Introduction
In the world today there is a problem relating to information. This is because most companies have suffered a great deal due to the loss of information. Private and confidential information stored by companies has found themselves in the wrong hands that use them for personal gains. For the last five years, there are reports about information losses by companies from various parts of the world.
The United States of America and the United Kingdom have reported a loss of information. This loss of information is due to the way it is collected, made use of, and how it is shared out among the users. Hackers have found access to data and they have caused a lot of damage to business information. The banking sector that has engaged in banking online has been hit most by fraudsters who purport to be customers have had access to information meant for customers.
In the financial times of December 2007, it is reported that since the year 2005, there has been an increase in the number of information loss which has led to loss of profits1. The information lost in the United States was as follows:
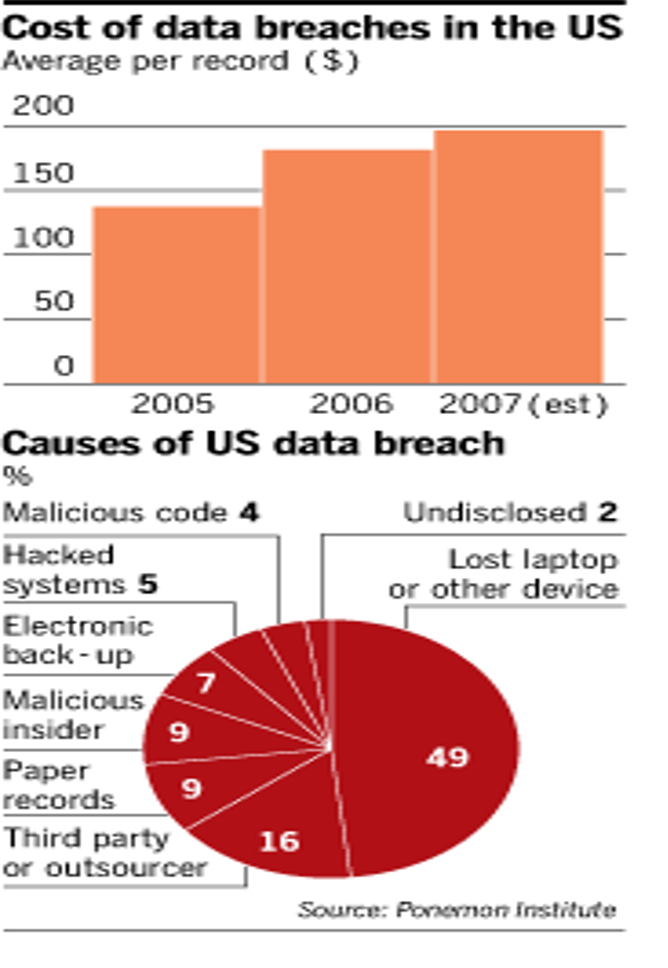
This loss of data as indicated by the data and graphs above shows how serious the problem of loss of data is omitted in society.
The trend
There is a trend that is bewildering the world, the loss of information. Loss of information or leakage is causing most companies to lose billions of dollars worldwide. The loss of information has increased over the recent years and it is said that in the United Kingdom and the United States, there is a lot of anxiety over the information lost. Some of the information lost has caused some organizations to make losses to a point of getting out of business. It is said that companies like yahoo are selling information to advertising companies a statement that is causing chilly among companies. Fraudsters are busy benefiting from these trends of loss of information.
Fraudsters have used information from well-known institutions to collect funds from members of the public. Recently, fraudsters used short messages (SMS) and internet messages to entice members of the public to services offered by various institutions. The best example is the lottery jackpot where a fraudster wrote messages to members of the public asking them to contribute something to facilitate the sending of the prize. This was imaginary and some members of the public had sent the fraudster’s money which led to a loss.
The trend in relation to insurance
Insurance will face a similar problem especially loss of confidential clients’ information which can be used by fraudsters to make false claims which will lead to loss of revenues. It is reported that in the month of November, a company reported the largest revenue loss due to loss of information. The report which led to the resignation of Paul Gray as revenue head of Symantec Global services is raising concern. This calls for proper knowledge management systems that will monitor the use of information technology in the organization and sharing.
For insurance businesses, data security can be both risky and confidential accompanied by strong financial attachments and their loss to fraudsters may be costly in the long run. If the information is lost against the backstroke of the customer, the reputation of the insurance will be in jeopardy as most customers will tend to avoid the insurance because of such kind of information leakage. The management of insurances has lost quite a substantial amount of money which has led to losses in revenue and reputation. Apart from insurances, other financial institutions have faced similar problems which have led to the loss of information.
To begin with, Knowledge management can be defined as the awareness and understanding of facts, truths, or information gained through reasoning in the form of experience or learning. Therefore Knowledge can be an appreciation of interconnected details that, in isolation, are of lesser value and Researchers use diverse expressions to define knowledge2 3. Commented that knowledge consists of justified true belief, Starbuck (1992) defined knowledge as a stock of expertise4 and Elliott and O’Dell (1999) as information in action.
Knowledge management is the implicit, explicit and systematic organization of important and shareable information within and with the external environment of an organization. It involves organizing information, finding and investigating, selecting necessary information, filtering, and presenting to groups, individuals, or to entities with an aim of improving understanding of specific areas of business interest. Therefore knowledge management involves the process of converting personal knowledge whether acquired in the learning process or obtained at any quarters into knowledge for others through the organization of information in the firm. Knowledge management focuses on two objectives that are enabling knowledge sharing within the organization and using knowledge to run communities and institutions5.
Some knowledge management activities that have been implemented by business organizations have helped them to focus on acquiring, storing, and utilizing knowledge for such things as problem-solving, dynamic learning, strategic planning, and decision making6 (Graduate School of Business, the University of Texas at Austin,2000 and Blue Ridge Academic Health Group. 2000).
From descriptions proved there is a need for the Allstate Insurance company to implement a good knowledge management system which ensures there is a proper use of information even data sharing will not be easily assessed. The system that the management of Allstate Insurance ought to implement needs to be user-friendly but free from hackers. Sharing of knowledge can be implicit or explicit within and without the organization.
Therefore, it is upon the management to ensure that there is data security for the information that is being shared out. The loss of data to the Allstate Insurance organization will be costly because there is an inherent risk in the information that is being used by the organization. The inherent risk with the information of the Allstate Insurance company’s industry is greater and its loss may result in huge profits which in turn may affect the company’s long-term survival.
Information is power and any information that runs into the hands of fraudsters will be very important for usage. The information stored in the Allstate Insurance organization needs to be protected especially personal information relating to the Allstate Insurance company’s clients. This kind of information should be stored in a convenient manner but free from hackers whose aim is to use the information for their own benefit. It has been noted that government departments and other organizations which use large forms of information face the problem of losing the information to hackers.
There are many ways that can be used to stop the trend of information loss within the organization. The ways recognize have been adapted by a few firms and they have ensured that their information is in safe custody, shared well, and is not easily accessible by fraudsters. Financial institutions like JP Morgan Chase Bank of America, commonwealth bank of Australia, and many large institutions have started banking online services but they have ensured that they have a strong data management system, which has had confidence from the bank. Although we do not fully prove, as they can also be hacked through the information black market which is growing.
The information can get to this market in case an employee leaves. However, in the case of the Allstate Insurance company, it is easy to keep information away from hackers, if the management of the Allstate Insurance company stops sharing vital information among departments which has high employee turnover.
Allstates insurance will benefit greatly/immensely if they try to understand the trend in information technology. The trend here is the loss of information to hackers whose main objective is to use the information to steal what is not theirs. The stealing of the information will be costly in the long run and short run. If information is stolen against the backdrop of the company, then there is a loss that will be experienced7.
Allstates insurance should try as much as possible to ensure all information that is provided within the company is free from being stolen by hackers. This is because at the moment they have not been affected by information hackers who steal information for purposes of use. Other insurance firms have been affected by the loss of information.
Recommendation
To enhance security further, the Allstate Insurance company needs to ensure that clients are informed and educated on the sensitivity of keeping private information away from unauthorized persons. This responsibility should be taken with seriousness because once information is lost within the organization; it is the company that carries the blame regardless of whether the clients had disclosed information that was not supposed to be disclosed to any other party. Information shared between employees should also be made not available to the members of the public.
This will ensure communications within the organization are kept private and confidential and do not leak outside the organization. To maintain this, the company needs to understand ways in which they can hire, motivate and retain employees to ensure low employee turnover. If there is high employee turnover, especially those involved in creating, collecting, storing, and distribution of information then the management of the Allstate Insurance expects a loss of information8.
Clients wishing to renew their services should provide full details including a password rather than giving only his name and address. This will ensure that the person who receives the economic value from the company’s services is the rightful owner of the service rather than any person who has anybody’s personal details and his address.
Lastly, the company should implement a knowledge management system that is fool prone to ensure there is proper information usage by both employees and the company. I propose the following system9.
To have a portal we need to understand and follow some steps and methodology which includes defining the site’s purpose, identify the site’s content, classify and organize the content, identify and codify knowledge objects, the definition of the site’s organizational and navigational schemes, create a maintenance plan, test the system for user friendly, provide feedback and have the plan for implementation10.
Knowledge goals ————> Knowledge identification ——-> Knowledge acquisition —->Knowledge development —–> Knowledge sharing—> Knowledge utilization—>Knowledge retention —–>Knowledge retention then feedback —-> Knowledge goals.
Conclusion
We have carried out trend analysis for Allstate Insurance.
In the trend, we have identified the problems facing companies relating to the private and confidential information of clients. Information in the business world has been in the past fallen into the hands of wrong people who used them for financial gain and it has been reported by many organizations on how they have lost great financial resources meant for customers. Allstate, fortunately, have not encountered the problem of information loss but it is a matter of time before they are faced with the same problem as other players in the industry.
We have carried out the trend analysis and made various recommendations that will ensure proper security for the information that is for the company. We have proposed the company have a well-defined knowledge management system which must have a portal that identifies a person when trying to access the company’s information. The information should be codified and any person trying to access the information is required to use a password which is necessary for the success of information management in the company.
For the security of the information, we have advised them to indicate and inform their clients of the need or necessity of keeping private and confidential information away from third parties. This will ensure that the information does not land in the hands of the wrong people who will, in turn, use the information for personal gains.
References
Ambrosini, V., and C. Bowman. 2001. Tacit knowledge: Some suggestions for operationalization.Journal of Management Studies 38: 811–829.
Blue Ridge Academic Health Group. 2000. Blue Ridge Academic Health Groups.
Report 3. Into the 21st Century: Academic Health Centers as Knowledge Leaders.
Graduate School of Business, the University of Texas at Austin. KM Answers to Frequently Asked Questions about Knowledge Management. Web.
Nonaka, I. 1991. The knowledge-creating company. Harvard Business Review 69: 96–104.
Polanyi, M. 1966. The Tacit Dimension. London, U.K.: Routledge and Kegan Paul.
Peel M. and Allison K. (2007); Devil in the details: Why personal data are ever more open to loss and abuse, Financial Times.
Salisbury, M. 2003. Putting theory into practice to build knowledge management systems. Journal of Knowledge Management 7: 128–141.
Sandra C. Vera-Mun˜ oz, Joanna L. Ho, and Chee W. Chow, (2006). Enhancing Knowledge Sharing in Public Accounting Firms Accounting Horizons Vol. 20, No. 2 pp. 133–155.
Sternberg, R. 1994. Tacit knowledge and job success. In Assessment and Selection in Organizations: Methods and Practice for Recruitment and Appraisal, edited by N. Anderson, and P. Herriot, 27–39. London, U.K.: John Wiley.
Stenmark, D. 2000. Leveraging tacit organizational knowledge. Journal of Management Information Systems 17: 9–24.
Szulanski, G. 2000. The process of knowledge transfer: A diachronic analysis of stickiness. Organizational Behavior and Human Decision Processes 82: 9–27.
Footnotes
- Peel M. and Allison K. (2007); Devil in the details: Why personal data are ever more open to lose and abuse, Financial Times.
- Sandra C. Vera-Mun˜ oz, Joanna L. Ho, and Chee W. Chow, (2006). Enhancing Knowledge Sharing in Public Accounting Firms Accounting Horizons Vol. 20, No. 2 pp. 133–155.
- Nonaka, I. 1991. The knowledge-creating company. Harvard Business Review 69: 96–104.
- Stenmark, D. 2000. Leveraging tacit organizational knowledge. Journal of Management Information Systems 17: 9–24.
- Ambrosini, V., and C. Bowman. 2001. Tacit knowledge: Some suggestions for operationalization.Journal of Management Studies 38: 811–829 and Blue Ridge Academic Health Group. 2000. Blue Ridge Academic Health Groups Report 3. Into the 21st Century: Academic Health Centers as Knowledge Leaders.
- Graduate School of Business, the University of Texas at Austin. KM Answers to Frequently Asked Questions about Knowledge Management. Web.
- Ambrosini, V., and C. Bowman. 2001. Tacit knowledge: Some suggestions for operationalization.Journal of Management Studies 38: 811–829.
- Szulanski, G. 2000. The process of knowledge transfer: A diachronic analysis of stickiness. Organizational Behavior and Human Decision Processes 82: 9–27.
- Sternberg, R. 1994. Tacit knowledge and job success. In Assessment and Selection in Organizations: Methods and Practice for Recruitment and Appraisal, edited by N. Anderson, and P. Herriot, 27–39. London, U.K.: John Wiley.
- Salisbury, M. 2003. Putting theory into practice to build knowledge management systems. Journal of Knowledge Management 7: 128–141.