Outline
In this document, we would be addressing various policies and security issues that an enterprise web service may have to face in a real environment. This would give an insight on how to develop security policies and strategies. We will also be seeing security risk management approaches and various levels of security that need to be taken care of. In the later part of this document, we would be seeing the various attacks and threats and also how identity management, authentication, authorization, access control, etc are maintained to protect messages and transactions.
Introduction
“Web services security quality is the ability to determinate the legality of access to the system and service, to cut off any illegal approach, fabrication and authority exercise, to control any legal access and to provide integrated security service for the use of stable, reliable and appropriate authority to reduce or eliminate all potential threats, which may occur while using Web services. In the Web services environment, the method for applying security service MAY be redefined in that for existing security standards because of access method and service interface shared by WSDL, SOAP message communication through XML, and the indigenous features implemented on various platforms” (Quality model for web services: security quality 2005, p.34).
Web services for Business-to-Business (B2B) and Business-to-Consumer (B2C) transactions have always been under threat from external intruders. Web service security has, therefore, become a part of the agenda for the business system. We will be seeing the various security levels and models that would help the security professionals; application architects and information developers develop suitable policies and authentication protocols to protect critical components like servers, workstations, networks, and so on. To maintain the interoperability between organizations and also between the organization and the customers, care needs to be taken to ensure that the security policies have a common architecture. (Chanliau & Mishra 2004).
Elements of web service security
“Web Services Security (WS-Security) was first introduced in 2002 as part of the overall Web Services Roadmap [Roadmap02, WSSecurity02]. It has since been approved as an Organization for the Advancement of Structured Information Systems (OASIS) standard [WSSecurity04]. WS-Security specifies an abstract security model for protecting messages.” (Communicating security credential 2009).
Since web applications and services are under various threats and vulnerabilities we need to understand the elements of security before any further approach. (Singhal, Winograd & Scarfone 2007, p.23).
Identification and authentication
This involves the verification of user details (the identity of the user), process, or devices, and then further authenticates the user so that he could make use of the available service.
Authorization
Once the user is identified as a valid user, he or the device is granted, directly or indirectly, access by the application or the system owner.
Integrity
This is a property of the data that needs to be ensured with the highest importance. It should be seen that the data is not manipulated in an unauthorized manner during processing or any transactions.
Non-repudiation
Indicates integrity of the data and maintains uniqueness by genuine high-quality authentication. In a different sense, it refers to achieving genuine authentication through cryptographic methods thereby denying access to data and hence can avoiding data being manipulated.
Confidentiality
It refers to maintaining only authorized access to a user’s information. Unauthorized disclosure of data has to be checked. This would also include protecting personal privacy and proprietary information.
Privacy
Privacy refers to the process of maintaining one’s personal information from being exposed without suitable permission. It involves the usage of service without disclosure of personal or critical information to outside sources.
Audit Trail
“In computing, the term is also used for an electronic or paper log used to track computer activity” (Audit trail: definition 2009).
Security policies
“A policy is defined as a broad statement of principle that presents management’s position for a defined control area.” (Tipton & Krause 2007, p.378)
The key elements of a security policy are:
- Understandability: The material presented should be for the intended audience.
- Applicability: When writing the policy, care should be taken that it meets the company’s standards and requirements. (Peltier 2002).
Security service level
The grid security infrastructure allows two kinds of securities –transport level and message-level security.
Transport level
At the transport level of security, the entire communication is encrypted. i.e. all the client-server information.
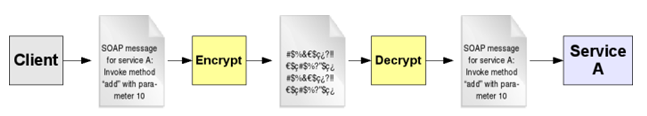
Message level
In the message-level security, only the contents of the SOAP message are encrypted; the rest is all in the unencrypted format. SOAP is a protocol that is used for exchanging structured information within the web service in computer networks. It relies on formats such as XML, HTTP, RPC (Remote Procedure Call), etc to set up the frame format. Transport level security vs. message-level security
(Transport level security vs. message-level security 2008).
Quality Sub-factors
Transport Level
Transport Level Data Confidentiality
As data is transferred from one service node to another, an efficient network protocol such as TLS or IPSEC provides a good level of confidentiality services nodes.
Transport Level Data Integrity
Comparison of the data packets or message that is transmitted between the networks is done by TLS or IPSEC to ensure the integrity of the data. This demands the protocol to be secure enough to do a good comparison.
Transport Level User Authentication
The authentication done by the communication channel of the message transmission layer could be unidirectional or bidirectional. It is checked that both the sender and the recipient are authenticated either according to electronic signature matching or some cryptographic technique.
Transport Level Access Control
The protocol decides the accessibility of a particular resource in a transmission channel by the user to prevent intrusion by unauthorized users.
Transport Level Accessibility
With the aid of services such as firewalls, IDS, IPS, etc the transport level accessibility could be established. This gives out a message indicating that there is no permission to access the service.
Transport Level Audit Trail
It refers to the creation of a data structure according to certain policies which contain logging information of all the transactions lately done. This would help in debugging and also to check unwanted changes in the data.
Message Level
Message Level Data Confidentiality
For ensuring the data (SOAP message) confidentiality encryption based on standards XML could be used. The available XML standards are that of W3C and OASIS. Other similar encryption techniques available are S/MIME and PG/MIME.
They exhibit higher efficiency compared to transport-level security because they provide encryption of parts of the messages. Encryption at the message level is better than at the transport level.
Message Level Data Integrity
Message level data integrity of SOAP messages can be obtained through XML-DSIG (Data signature) or OASIS WS–security. The XKMS (XML Key Management Specification) extends the concept of Public Key Infrastructure using XML standards thereby providing an easy and interoperable key management service.
Message Level User Authentication
It is an email-based authentication system in which the user is in full control of the process. This helps in avoiding any kind of phishing attacks and ensures 1005 authentication. This is enabled with the support of the XML-DSIG standard adopted by W3C wherein it appends a head and tail to the SOAP message that could be decoded by the authorized user. (Quality model for web services: message level user authentication 2005, p.37).
Web-based security audit tools
Some of the web-based security auditing tools are Shields UP, Security metrics and DataScope, Leak Test, etc. Shields UP is more focused on its mission and easy to implement than others mentioned above. For its successful operation, it demands the system’s IP address allocated by the network. These services scan the network and report any harmful programs that are capable of making changes to the data or the application itself.
They also keep track of the various changes that occur within their network in a database. System metrics require the user to provide all the necessary information such as the system name, URL, firewall address, etc depending on what you need to scan. It performs a more thorough scan than the Shields UP. It judges the state of the system depending on the number of vulnerabilities. A system with more than four is indicated as FAIL. The result would be sent by mail. DataScope is very much similar to the System metrics; the only difference being that it displays the exact areas of vulnerability. Apart from these tools, lots more are available with better features. (Geroski 2002).
Risk Management approaches
“Risk is defined as the possibility of an unsatisfactory outcome.” (Borysowich 2006). They have a great influence on the success of a project. Even if it cannot be eliminated, a good risk management system should be able to control the effects of that risk. The methodologies involved in risk management would be identifying the risk, prioritizing it, and then, after well-defined planning and monitoring, executing the necessary actions to reduce/eliminate the risk.
The role played by XML [Extensible Markup Language] in web security
It was developed by the security standards namely W3C and OASIS. Several XML security protocols coordinate to form the XML firewall. Its main aim is to provide integrity and authentication to data by wrapping the data within an XML format. XML is built to carry data and not to display it. One of the major advantages of using XML compared to other markup languages is that they are interoperable with other heterogeneous hardware and software platforms. (Ryan 2004).
Risks and threats faced by the web-based services
Applications such as ActiveX, Java, and other plug-ins improvise the web page by providing it with a new life and dimension. Some of them also monitor the system performance and check for any updates required by the system. They gain access to the system memory for this purpose especially when the external memory or bandwidth is low. But this isn’t always safe. Intruders gain access to our files and are capable of deleting or even corrupting our files.
The best way to defend against these applications would be by disabling the updates of these applications within the system security settings. They are sometimes referred to as the next-generation virus carriers. (ActiveX and Java: the next virus carriers? n.d.). The plug-ins are software applications that interact with the host system applications such as web browsers, emails, and other services promising several advanced features. They are also referred to as add-ons or snap-ins. Adware and malware pretend to be plug-ins and steal valuable information including login details such as passwords. They become a major threat when it comes to financial transfers where the developer of the malware gets to know about all the details.
CGI Flaws
CGI stands for Common Gateway Interface and it defines how the user data is sent to the webserver, how it is processed, and then how it is outputted back to the user. The following shows a diagrammatic representation of the flow of data between the CGI.
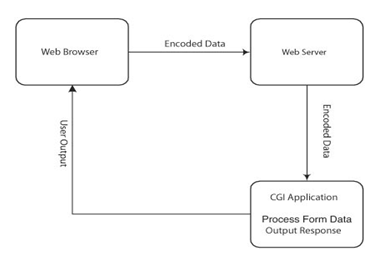
One of the major flaws in CGI is that it fails to identify the format of the data that is inputted. This becomes a serious issue when dealing with a structured query language. Since the integrity and security of web services are important factors, regulating or controlling the flaws in the common gateway interface becomes a major concern for the application developers. The security breach due to these flaws can occur because of the fault of either of the two people-The programmer and the manager or team leader.
If the team leader fails to explain or communicate the security policies of the company, then the programmer might not include the necessary features, resulting in the breach of their official site. Similarly, if the developer fails to consider the understands the policies and he is unaware of the programming technique, these flaws can occur So care must be taken from both sides to prevent such attacks.
Trust Relationship
The trust relationship is an integral part of any web service security service. The policy and ontology are set by these relationships to determine how well they could be used to bring about interoperability between different organizations. These trust standards would request the web service to perform the necessary authentication
i.e. an incoming message should satisfy a set of requirements specified by the policies within the trust. Messages that fail to provide proof for their claim will be rejected. The steps carried by the trust engine of the web service security application are as follows:
- Verifying the claim in the token to see if it complies with the required policy.
- Verifying whether the attributes of the message match with the required signatures. In case the signature doesn’t match, the message is discarded immediately with the corresponding message display.
- The next step is verifying whether the issuers of security token are themselves valid to issue the claims. This process has to be externally verified by sending a security token to the service and then evaluating the other security token obtained in exchange.
Reference List
ActiveX and Java: the next virus carriers? n.d. Web.
Audit trail: definition 2009, SearchCIO.com: Technology Management Strategies for the Enterprise CIO. Web.
Borysowich, C 2006, An approach to risk management: risk defined, Toolbox for IT. Web.
Chanliau, M, & Mishra, P 2004, Enterprise web services security: a reference architecture. Sys-Con Media. Web.
Communicating security credential 2009, Safari Books Online. Web.
Geroski, R 2002, Web-based security audit tools offer useful feedback, Tech Republic. Web.
Peltier, TR 2002, Information security policies, procedures, and standards: guidelines for effective information security management, CRC Press.
Quality model for web services: message level user authentication 2005, Oasis. Web.
Quality model for web services: security quality: definition 2005, Oasis. Web.
Ryan, J 2004, The role of XML in agile enterprise architecture (is XML really boring?), Developer. Web.
Singhal, A, Winograd, T, & Scarfone, K 2007, Guide to secure web services: recommendations of the national institute of standards and technology, National Institute of Standards and Technology. Web.
Tipton, HF & Krause, M 2007, Information security management handbook: policy definition, 6th edn, CRC Press.
Transport level security vs. message-level security 2008, Dimuthu’s Blog: Waiting for your Comments. Web.
Web server vulnerabilities: CGI flaws 2009, Safari Books Online. Web.