Hardware Components
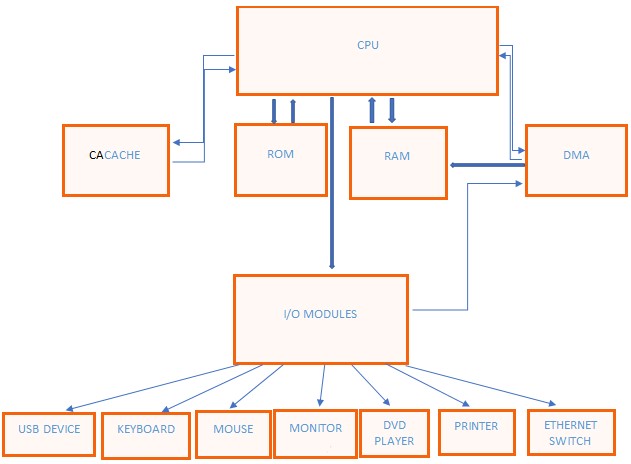
- Central Processing Unit (CPU)- The CPU is a component responsible for enabling a computer to function as it serves as the computer’s brain. The CPU is composed of sub-components such as the arithmetic logic unit (ALU), instruction pointers, cache, memory management unit, control unit and random-access unit.
- Memory/storage– this component involves space where data is processed and instructions for the commands are stored. The memory is divided into parts known as cells which have unique addresses varying from zero to minus one memory size (Amid et al., 2019). Memory is divided into three types such as cache, primary or main, and secondary memory.
- Cache memory- this is a high-speed semiconductor that speeds up the CPU and acts as the buffer between the computer’s main memory and the CPU (Chen, 2016). The cache holds parts of data and programs that are utilized by the CPU.
- Random access memory (RAM)- The RAM acts as the main storage and serves as a crucial part that stores programs and data, making them ready for use any moment the CPU requires the data and programs.
- Read-only memory (ROM)- this is electronic storage that is non-volatile thus, meaning it can store data and information permanently in the computer.
- Flash- flash memory is a non-volatile chip used for storage on a long-life basis and is useful in embedding systems. It keeps stored data even when the computer is switched off.
- Direct memory access (DMA) is a feature in a computer storage component that allows some hardware subsystems to have access to RAM independently of the CPU.
- Hard disk is a data storage device fixed in the computer motherboard with spinning disks used for storing data magnetically and can read or write data using in-built transducers.
- Keyboard- this is a peripheral component that contains alphanumeric keys, function keys, cursor movement keys, space bar, and special keys and it is used for typing characters on the computer screen or monitor.
- Monitor- This output device displays information from the storage systems and records characters being typed on the keyboard. It is also known as a video display unit (VDU). Other components include the mouse, adapter, motherboard, sound card and charger.
Computer Software Components
- Operating system (OS)- this is a collection of programs that are used to control the running commands and organize computer system resources such as the keyboard, monitors, printers, and disk drives (Chen, 2016). OS comes with commands and utilities that are used to maintain files, messages, and other elements.
- Application programs– these are software layers on top that perform specific tasks, for example, using Microsoft word processor for writing, spreadsheet for accounting and 3D access to drawing.
- Device drivers– These are specialized programs that support the application programs and the OS to perform commands in the computer (Kanner et al., 2021). The drivers do not interact with the user but rather with the hardware elements during computer usage.
- Root user processors– They are specialized programs that can be run by a computer user but under root authority, such as system administrator for the computer processes (Kanner et al., 2021). Root processes may include reading and writing objects, calling system functions, and performing control operations, among others.
- Utilities and system services– these are programs that add the capabilities of the OS. Examples may include antivirus, file management systems, and disk cleanup tools, among others.
Communication Components
- Layer 1– this is a physical networking layer that provides electrical and mechanical support in enabling or disabling transmission bits on physical connections. It involves electrical signals such as laser and optical fiber, electromagnetic waves such as wireless connections and sound (Kanner et al., 2021). Services performed by layer 1 include line coding, circuit switching, and modulation, among others. Examples include Ethernet physical layers, universal serial bus (USB) and Bluetooth physical layers.
- Layer 2– this is a network that uses hardware addresses to process and forwards information at the data link layer technology (Kanner et al., 2021). For example, layer 2 allows a switch to operate as a bridge to networks such as Wi-Fi, ethernet and cable data transmission and access.
- System devices- these are a set of integrated devices that are used for the input and output of data. They allow a computer user to manipulate and store data. For example, a router receives and sends data hence enabling the connection between devices in electromagnetic technology.
- Layer 3 is responsible for functional and procedural modes of data transfer in varying lengths and sequences from a source’s host to a given destination. The most notable layer in this case is the internet protocol (IP) that routes packets across interconnected networks.
- Layer 4 is the transport layer responsible for creating a virtual transfer control protocol (TSP) or user datagram protocol (UDP) interconnection between the hosts. Through TSP and UDP, layer 4 sends and receives data to and from the computer application programs running in a specific host.
- Application layer– this is an abstraction layer that distinguishes the shared communication protocols and interface modulation used by the host network. It is specified in TCP and IP in the OS model. Examples include hypertext transfer protocol secure (https), extensible markup language (XML) and real-time transport protocol (RTP).
Data Components
- File system– this is a method and data structure that OS controls on storage and retrieval.
- Data at rest- it means data that is not moving from one device to another or network to another.
- Data transition– it is the process of analyzing how current data is stored in a legacy practice management system and preparing the data for import into the required host.
- Types of media– it can be computer hard drives, removable drives, flash memory that are used to bring pictures into the display, or voice and video into a definition in output (Kanner et al., 2021). For example, fax involves the transmission of scanned printed materials connected to an output device.
- Encryption and compression– encryption is the shuffling of data that makes it hard to find the data without a key. Compression uses patterns to reduce the size at high levels.
- Data encoding converts data or a given character sequence, alphabets, or symbols into a specific format that is secure to transmit data (Kanner et al., 2021). It includes converting analog data to digital files that can be encrypted and compressed efficiently.
Apple’s M1 chip has a storage controller and flash technology that delivers double-speed solid state (SSD) performance when compared to intel design. According to the disks speed tested, the results showed that SSD in M1 MacBook Air is twice faster as the other generations recording a whooping 2190 megabytes per second and 2675 megabytes in terms of reading speed (Vorobets, et al., 2018). The intel results indicated the speed was about 1085 megabytes per second hence M1 having an advantage over the intel. In terms of data transfer, M1 chip beats Intel on that metric. The Apple mac takes only 27 seconds to transfer 40 gigabytes, while Intel takes 90 seconds for the same volume of transfer (Vorobets, et al., 2018). In terms of starting and shutting the computer, M1 mac is faster and gives a nice experience when tabbing multiple pages or opening simultaneous applications. Lastly, M1 chip has a neural network processing (NNP) technology that uses artificial intelligence to observe human traits and work on them.
References
Amid, A., Kwon, K., Gholami, A., Wu, B., Asanovic, K., & Keutzer, K. (2019). Co-design of deep neural nets and neural net accelerators for embedded vision applications. IBM Journal of Research and Development, 63(6), 6:1-6:14.
Chen, C. (2016). Computer-assisted consumer electronics in manufacturing and service industries: present status and future challenges (introduction). International Journal of Research Studies in Computer Science and Engineering, 3(2), 34.
Kanner, T., Kanner, A., & Epishkina, A. (2021). Algorithm for optimal and complete testing of software and hardware data security tools. Procedia Computer Science, 190(6), 408-413.
Vorobets,, G., Vorobets,, O., & Gorditsa, V. (2018). Application of the system approach for the synthesis of models of basic elements of reconfigurable structures at the information transmission systems. Electrical and computer systems, 28(104), 257-267. Web.