Introduction
The security of computer system has been an issue of concern since early 1940s. During those eras security of computer was achieved by the use of heavy door lockers, which were not easy to master or break through. But due to the advancement of computer technology more sophisticated means of computer security were needed to ensure the safety and security of computer systems, since the prevailing methods could not curb the problem of data hacking through the networks.
This was made possible by the IBM, which realized the need to secure data from within by the use of password, which could not allow unauthorized users to have an access to the information in the computer system.
As time elapsed, the level of computer technology continued to advance and the problem of computer insecurity increased which led to the development more advanced technologies to minimize and step this problem.
With the advancement of IT and computer technology, most companies, organization and institutions have changed from the old method of record storage to the use of computers. This is because a computer can store a lot of information, which occupies a small space as compared to the old method where information was stored in bulky files that need a big space for storage (Hugh, 2001).
The retrieval of information from a computer is also faster and easier for an authorized user but very hard for unauthorized user which helps to protect the stored information.
Information stored in a computer system is safer because you can use a password so that unauthorized user cannot log in your computer system to access the information stored.
In some organization that deals with some very sensitive matters, for example, military & FIB have a very advanced security system, which helps to safeguard the access of sensitive files to other people who might alter their content, which can bring a very big problem (Hugh, 2001).
In some other places like institution of learning sensitive files should be well secured to avoid any unofficial alterations, for example, the files containing students results should be well protected to prevent students who might change their poor grades to better ones in case they access these files.
Therefore the security of computer system is very important issue to be considered in every organization because it helps solve some problem of risk that can occur when unauthorized user happen to access some sensitive information of the organization (Hugh, 2001).
These are some of the ways that a computer administrator can put into consideration to safe guard their information in a computer system.
Use of Password
A password prevents unauthorized user to have an access to the computer information, all unauthorized users are given a username and password to keep off unauthorized users.
For one to access the data or information contained in the computer system, one must use the right password to login into the computer. This ensures the safety of information found in the computer, as strangers cannot access the files in the computer system and altering the original information or deleting important files, which can pose a great danger to an organisation.
The password used by the user should be kept as a secret and should be changed after sometime interval. The passwords should also be well chosen and long to enhance it’s effectiveness such that it becomes very had for anybody with bad motives to trail it and login your system.
Limited Access to Users by Administrator
In case a network is involved, the network manager should let the authorized user have an access to a limited application programs, which they frequently use and deny them an access to files with sensitive information (Hugh, 2001).
This can be realized by, the administrator having his or her own account separate from the other users such that he is the only one who can login into that account. This will require him to ensure that he or she does not disclose their account password to the other users.
Some programs, files and folders should be protected using a password so that unauthorized users cannot change their content. Other documents apart from being protected by password should be made read only to enhance their safety (William, 1999).
Use of Back Up
Important files, folders and programs should be backed up to prevent their loss in case of an intruder infecting the computer with a virus that can crashes the system or which might delete the content of these files. These backed up information should then be kept away in a safe place. This makes sure that the original information found in a computer system remains such that in case of the loss of that information or altering of that information in the computer it can be accessed back from the back ups (William, 1999).
Screen Locking
This is important because it keeps off curious eyes to have an access to your information in a computer. For example, in case you happen to leave your computer on for a while, without logging out or shutting down your computer to attend to an urgent need the screen locks after sometime depending on your setting and for the screen to display you must enter the password to unlock it. This keeps away onlookers accessing your work when you have gone out. It also saves time because for you to access your work you only need to put your password, which is very faster unlike when you have to shutdown or log out your computer (William, 1999).
Encryption
Recently most people have adapted the use of Internet to shop customers collecting what they want inside an electronic basket and then pay using their credit card. This method worries majority of people because they fear their credits cards details can be tapped and then used for unauthorized purchases. The use of encryption reduces this risk because files that have been encrypted are scrambled such that if one comes across them they cannot be able to read them as they do not have the programs that should be needed to encode these files back to their original form as this program is only limited to the only right clients. Encryption encodes or scrambles files so that anyone who accesses such files full of data will need to access the encryption program which can be accessed only by the retailers ‘of website making that data useless to the unauthorized user.(Hugh,2001)
Use of Antivirus Programs
In some other computer system which is connected to the Internet hacking is a major problem and a lot of security measures should be observed to prevent the unauthorized users accessing the computer system information. This reduces the risk of data altering or implanting viruses in the system, which is also a problem to the computer system as viruses replicate, delete files and others can crash a system. This can result into a very big problem since important information can be lost. (Hugh, 2001)
Hawking Prevention Measures
Maritta (2004) defines hawking is the act of accessing the content of the computer system without been authorized. This can be done through some of the following means
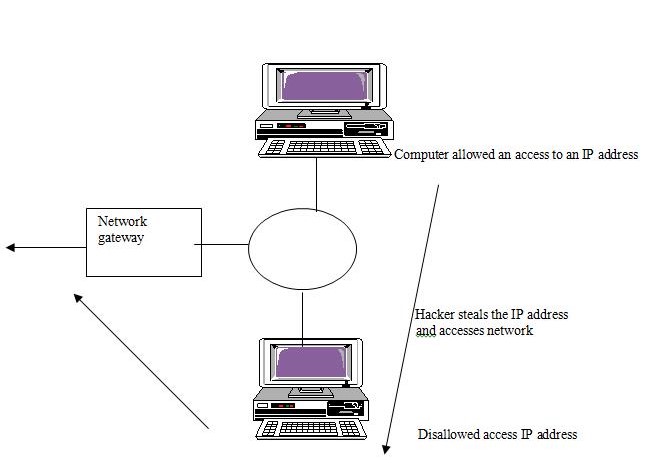
- IP spoofing attack
In this method the hawker determines the computer IP address that t he user is using and then steals it and accesses unauthorized materials when no one is using that computer.
- Password Attacks
According to Maritta (2004) a hacker finds the password of authorized user. This occurs when the password of the user is easy to guess for example those using a password that is similar to their login names. The hawker sometimes uses a special program that tries a number of passwords until it gets the gets the right one. The worst that can happen is when they succeed to get the Password of the system administrator, this is because they can change system set ups or password of the user which will deny the authorized users access to their files. Others can even delete very important files or plant a virus to a computer system.
Stern measures should be adapted to guard an access or damage of the files or programs of the computer system. This will be achieved by the use of password well chosen to minimize the chances of ID tracking and passwords, which are not in use, should also be deleted. (John, 2000)
In some cases hacking monitoring system should be installed to alert the system administrator when private materials are accessed unauthorized. This should also be
Incorporated with encryption of the content of secret files, folders or programs. The computer system should also have recovery programs, which can recover important files that might have been deleted by hackers by accident (John, 2000).
- The use of audit trail programs
The use of audit trail programs will help to keep update of all actions performed that is, all the read or alteration done by a user and by analyzing such history the system administrator can detect when the information in the system is been changed unauthorized by some users.
The computer system should also be installed with the latest computer virus, which helps to prevent computer being attacked by computer viruses that might damage their contents or crash the system (John, 2000).
Use of smart cards or biometric
A more effective method of securing a system is the use of smart where by users has to insert a smart card and enter their pin code to have an access to their system, also the use of biometric methods is more secure as the method requires the use of one’s physical features such as one’s retina images or fingerprints. Which are scanned and fed into the program and users will be allowed an access to the system once these parameters are verified (John, 2000).
Conclusion
The usage of a computer system determines the likelihood of the system expose to risk.
For example, a computer that has only one authorized user has minimal chances of the unauthorized user accessing or altering its contents, which is achieved, with an effective use of password and encryption of sensitive files. However, in a situation whereby a computer is connected to network or Internet the chances of information insecurity increase. This requires an advancement method to safeguard the content of the system by hawkers. It requires the system to be installed with a program that is able to monitor hacking. This helps to detect a heckler who might be tapping communication between the client and a server that might cause severe damage to the organization if the data was not well protected through encryption. This type of connection also calls for the need of the use of audit trail programmes which the computer administrator can use to establish whether sensitive materials in the computer system are accessed unauthorized done by analyzing the history of the actions performed by all the users. (John, 2000)
The usage of a computer system will determine the security measures to be taken. A computer that handles sensitive information in an organization, for example, the one used by the manager or the system administrator should have very efficient measures taken to protect the risk of that information been accessed without authority.
Installing many security programs in a computer system slows down the speed of execution of instructions. This is because the processor has got many instructions to process at a time, for instance, for every instruction given by the user there is another instruction sent by the security system installed but this takes place in the background. The more the security programs installed in a system the slower it will be in the performance, so for a very effective system in performance and safety very few but efficient security should be used. This will ensure that the information stored is safe and the speed of the system is not highly compromised (John, 2000).
Protected and their content encrypted. The system administrator did not consider this and that’s why the contractor was able to access the list of the company customers (Edward, 2006).
The computer system should also be fitted with audit trail software to help the administrator learn about the access of a sensitive material by an unauthorized user like this case so that the appropriate measures can be taken in time (Edward, 2006).
Every computer system should have a security measures taken into consideration to protect its materials from damage or access by unauthorized users. The security system used in a system varies with the use of computer system. Networks and Internet have the most advanced security system because they are highly prone to data hacking.
References
- Edward, W. (2006): Information Risk and Security, London, Gower publishing ltd.
- Hugh, A. (2001): Computer and Intellectual Crime, Cambridge, BNA books.
- John, P. (2000): Computer Security Management, London, Institute of career research.
- Maritta, H. (2004): Computer Safety, Reliability and Security, New York, Springer
- Matt, B. (2002): Computer Security, New York, Addison Wesley.
- William, E (1999): Computer Control and Security, New York, J. Wiley