Abstract
As soon as digital artifacts have become a part and parcel of everyday life, the need for digital media archives with the capacity of preserving the given metadata has risen impressively. The process of converting the digital metadata to archives, however, is fraught with several difficulties, the key one concerning the methodology for embedding high payload capacity information into digital multimedia and at the same time retaining the high quality of the image. The given paper will consider steganography as a possible solution to the aforementioned issue. Allowing for detecting the genetic algorithm for boosting the PSNR value with the information of high capacity will help solve the issue regarding digital multimedia archiving.
Keywords: Steganography; LSB; Genetic Algorithm; Block mapping, message segmentation
Introduction
The present-day world of media and communication is dominated by digital multimedia content. More to the point, the use of digital content has finally become an available option for most people. However, apart from the everyday use of digital media, its significance in the research and academic life of several students must be mentioned. Media allows for accessing important resources, training essential skills, and managing time more efficiently. The information processing that such media performs, however, still needs major improvement.
Using an embedding process to connect two types of data and enhance the capacity of metadata, steganography can be used to handle the aforementioned issue. By encompassing the spatial domain of steganography in the given research, the author of the given research is going to analyze the use of digital multimedia and its effect on various spheres of people’s life. For the given purpose, the technique of the least significant bit subscription scheme (LSB) is going to be utilized. The choice of the research technique was predetermined by its high rates of uncomplicatedness [1] and impressively big hiding capacity, as well as the fact that it hinges on such specifics of a human eye as the insensibility of low bit images [2].
For the stereo-image not to be blocked by the SDDS system, it is required that messages should be embedded in a particular spot, therefore, providing the maintenance of the cover image statistical features. Seeing how the spatial-domain embedding approach, which does not allow for choosing the given position due to the regularity of message distribution, embedding the message in a certain location will be fraught with several difficulties, such as the definition of changes in the spatial project.
In the project in question, the mapping technique is going to be used to split the cover image under consideration into several major blocks and, thus, perform an analysis, since the aforementioned approach will help place every single element of the message in its place. The abovementioned operation will contribute to defining the most reasonable frequency domain position and, thus, drive the number of static feature disturbances on the chosen spatial domain slot to a minimum, which can be attained by using the Genetic Algorithm (GA).
Therefore, the goal of the given paper is to research GA usage for concealing metadata. Chapter Two reviews the stenography methods. Chapter Three shows how to utilize GA for data hiding. Chapter Four evaluates the matrix method, while Chapter Five offers an analysis of the proposed algorithm. Chapter Six provides a list of results and concluding remarks. Block substitution is going to be used in the given paper as opposed to the bit-based one because of the inferior properties of the latter [3, 4].
Steganography Methods Review
Steganography is traditionally defined as the skill of concealing specific data in traditional messages for users to make it harder to decipher these implications. Some of the steganography techniques have been used so widely that they have turned into widely accepted and, therefore, frequently used formats [5].
As a rule, steganography methods are split into two major categories, i.e., Transform Domain and Spatial Design approach [6]. The former approach presupposes that images should be converted before the message is implanted into them [7]. Speaking of the former method, one must mention that it allows for hiding the key message of the image in its essential parts, which is why the Transform Domain requires differentiating between high, middle, and low-frequency elements of the image. The fact that the signal energy rates are especially high in the lower frequencies, explains why the visibility of the image is of especially high quality.
Judging by the above-mentioned specifics of the Transform Domain, it is reasonable to assume that planting secret data in higher frequencies will suffice to prevent image distortion. In addition, Transformation Domain methods win by comparison with the rest of the methods because the TD does not depend on the format of the image; quite on the contrary, because of the message embedded into the image, TD can withstand both a lossy and a lossless compression [8].
In contrast to the TD, the Spatial Domain, these are the pixels that the key messages are embedded into. It offers such methods of planting messages into the image as the LSB plane direct manipulation and the replacement of the cover image with the bits to be concealed. [9, 10]. The given method, however, is rather easy to spot [11]. Instead of it, LSB matching based on planting the data into a cover image has been suggested recently. Due to the matching process that it involves, high similarity rates and, therefore, low detectability are exercised [12].
The given study is not the first instance of using GA as the means to address the LSB issues. GA has also been used in several studies to conceal the data in the rightmost k LSBs of the host image [13], Mielikainen’s method [14] being one of the most recent updates of the technique in question.
GA Approach
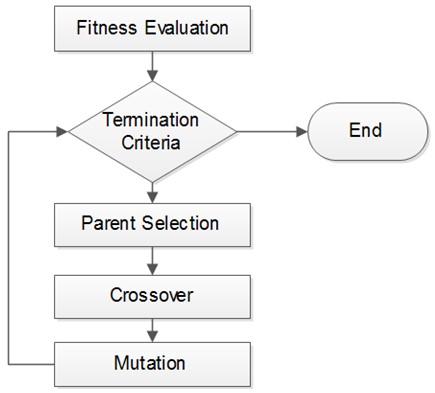
The genetic algorithm (GA) is an optimization and search technique based on the principles of genetics and natural selection. A GA allows a population composed of many individuals to evolve under specified selection rules to a state that maximizes the “fitness” (i.e., minimizes the cost function). The method was developed by John Holland (1975) [15]. The genetic algorithm starts with no knowledge of the correct solution and depends entirely on responses from its environment and evolution operators such as reproduction, crossover, and mutation to arrive at the best solution.
By starting at several independent points and searching in parallel, the algorithm avoids local minima and converges to sub-optimal solutions. In this way, GAs are capable of locating high-performance areas in complex domains without experiencing the difficulties associated with high dimensionality, as may occur with gradient descent techniques or methods that rely on derivative information [15,16]. Figure 1 shows the basic process of the Genetic Algorithm.
Process of Concealing the Metadata: GA Stages
- Creating a random population of chromosomes;
- Assessing the objective (fitness) function;
The evaluation of the given function hinges on the PSRN criterion, which is supposed to reach its minimum value for the process to have any meaningful results.
PSRN, or Peak Signal to Noise Ratio, being the criterion as the foundation for the fitness function, is traditionally defined with the help of the following functions:
![]()
![]()
- Repeating the steps a–c until the new population is made:
- Choosing a pair of chromosomes (probability increasing together with the function of fitness);
- Forming two new strings with a crossover of chromosomes;
- Mutating the newly obtained chromosomes and planting the new strings into the population.
- Swapping the new and the previous population;
- As long as the optimum solution can be provided by correcting the value of error with the number of generations or the maximum amount of generations is attained before it ceased to grow at the point where it serves as the location of the best chromosome, the experiment can be considered successful.
Hiding Process Using Score Matrix
The combination of the secret image and cover image is assessed with the help of the so-called matrix M [18]. Ti, also known as a double state scoring, works in the following way:
- T1 is scored when the cover and stego image pixels are similar or identical;
- T2 is scored when the stego image data is dependent on the cover image.
To demonstrate the significance of maintaining the cover pixel values at the same level, fewer alterations must be made to the cover image. Supposing, T1 is greater than T2 (T1 > T2). Thus, it becomes obvious that the pixels, which do not demand the LSB alterations are a better option than the ones that do.
Supposing that S and H represent the matrix of the hidden data and the cover image correspondingly, the stream value of T1 , which allows for providing the formula for teh score matrix M:
![]()
- m (i, j) equals i – the row (M, L2);
- the column (M, L2) equals the length of the hidden stream groups;
- L2 equals the length of the cover stream groups).
By choosing the M and L element from each row and column, one will be able to define the order that ha the best matching potential [8]. The given formula is used for adjustment list calculation:
J = [j1,j2,…,jk ,…, jL3]
Proposed Method
Supposing, the hidden message in the image is split into N similar parts, the mapping function connecting the hidden and cover image blocks can be technically defined as the N permutation. The best mapping function selection being P*T in the given case, N increases exponentially; for instance, a 512*512 image will consist of 4096 elements, computational complexity being equal to O(4096!)*T. Therefore, it will take too much time to calculate the N – in fact, the number that will be obtained in the course of the multiplication will verge towards infinity.
The given issue, however, can be resolved efficiently, as the research results show; by using a score matrix as the method for carrying out the mapping function procedure, one is capable of assessing the performance of any matching order of both the secret image and the cover image. In its turn, the normalized total score of J is calculated with the help of the following formulas:
f(J)= 1 ∑m(i,j)|J (3) fm
fm =L.T (4) s1,
f m being the maximum possible value used in the adjustment list.
Embedding Procedure
According to the system, in accordance with which the secret image, or message, is split into N blocks, the following step must be taken in order to create the pseudo-code for a stego image:
- Splitting the cover image into several blocks (e.g., 8*8 blocks);
- Assessing the score matrix represented in each block;
- Calculating the adjustment list value by locating and stating the fitness function;
- Locating the most efficient and reasonable adjustment list with the help of the GA strategy;
- Planting the cover data into the image in question by following the adjustment list provided.
Extracting Procedure
Logically, to obtain the secret message, it will be necessary to carry out the steps listed above in inverse order. Thus, the receiver will be able to obtain the stego-image together with the key and then analyze the information that the given key offers to consider. Delivered in an encrypted way to the receiver, the given information will be later on interpreted and used accordingly.
Experiment Results
According to the results acquired in the course of the research, the introduction of the Graphical User and Matlab R2013a improves the efficacy of the code a few notches. As the table provided below shows, the average value of the PSNR reaches 72.15533 dp and the related capacity of the 152*512 peter.jpg images increases, as Figure 2 shows. Thus, the proposed method turns out to be more efficient than the traditional LSB method for increasing the capacity of stego images.
Table 1. The Embedded capacity in KiloByte (KB) for the proposed method and its related PSNR in pepper.jpg
Conclusion
The task of preserving digital media is extremely important, since it allows for its more efficient use. However, retaining the capacity of images, as well as their imperceptibility, is rather difficult. With the help of steganography, however, the process of conserving digital media can be upgraded a few notches and made times easier. Moreover, the quality of the images remains just as high.
Footnotes
- A. D. Ker, “Steganalysis of LSB matching in grayscale images,” Signal Processing Letters, IEEE, vol. 12, pp. 441-444, 2005
- L. Shao-Hui, C. Tian-Hang, Y. Hong-Xun, and G. Wen, “A variable depth LSB data hiding technique in images,” in Machine Learning and Cybernetics, 2004. Proceedings of 2004 International Conference on, 2004, pp. 3990-3994 vol.7
- W. Yi-Ta and F. Y. Shih, “Genetic algorithm based methodology for breaking the steganalytic systems,” Systems, Man, and Cybernetics, Part B: Cybernetics, IEEE Transactions on, vol. 36, pp. 24-31, 2006.
- E. Kawaguchi and R. O. Eason, “Principles and applications of BPCS steganography,” 1999, pp. 464-473.
- Fabien A. P., Ross J. Anderson and Markus G., “Information Hiding – A Survey”, Proceedings of the IEEE, special issue on Protection of Multimedia Content, pp. 1062-1078, 1999.
- Silman J., “Steganography and Steganalysis: An Overview”, SANS Institute, 2001.
- Lee Y. K. and Chen L. H., “High capacity image steganographic model”, IEE Proceedings of Visual Image Signal Processing, Vol. 147, No. 3, pp. 288-294, 2000.
- Shi Y. Q. and Sun H., Image and Video Compression for Multimedia Engineering, CRC Press, Boca Raton London New York Washing, D.C., 2001.
- Ker A., “Improved detection of LSB steganography in grayscale image”, Lecture Notes in Computer Science, pp. 97-115, 2005.
- Mahdavi M., Samavi Sh., Zaker N. and Modarres-Hashemi M., “Steganalysis Method for LSB Replacement Based on Local Gradient of Image Histogram”, Iranian Journal of Electrical & Electronic Engineering, Vol. 4, No. 3, pp. 59- 70, 2008.
- Chan C. K. and Chan L. M., “Hiding data in image by simple LSB substitution”, Pattern Recognition, Vol. 37, pp. 469-467, 2004.
- Chang C. C., Hsiao J. Y. and Chan C. S., “Finding optimal least-signification-bit substitution in image hiding by dynamic programming strategy”, Pattern Recognition, Vol. 36, pp. 1583-1595, 2003.
- Wang, R.Z., Lin, C.F., Lin, J.C.: Image hiding by optimal LSB substitution and genetic algorithm’, Pattern Recognit., 2001, 34, (3), p. 671-683.
- Mielikainen J., “LSB matching revisited”, IEEE Sigal Processing Letters, Vol. 13, No. 5, pp. 285- 287, 2006.
- H Holland. “Adaptation in Natural and Artificial Systems: An Introductory Analysis with Applications to Biology”. Control and Artificial Intelligence. second edition. Cambridge, MA: MIT Press, 1992.
- Yi-Ta Wu, Frank Y Shih. Genetic Algorithm Based Methodology for Breaking the Steganalytic Systems. IEEE Transactions on systems, man, and cybernetics Part B: cybernetics, February 2006, vol 36, no 1.
- J. Fridrich, M. Goljan, and D. Rui, “Detecting LSB steganography in color, and gray-scale images,” MultiMedia, IEEE, vol. 8, pp. 22-28, 2001.
- Soleimanpour M., Talebi S. and Azadi-Motlagh H., “A Novel Technique for Steganography Method Based on Improved Genetic Algorithm Optimization in Spatial Domain”, Iranian Journal of Electrical & Electronic Engineering, Vol. 9, No. 2, pp. 67-75, 2013.