Abstract
Geospatial intelligence has become an important concept in homeland security. As criminal gangs and terror groups continue to use sophisticated strategies to achieve their goals, the need to use emerging technologies in fighting their activities has become critical. The United States has taken lead in the use of geographic information system, geographic positioning system, and unmanned aerial vehicles (GEOINT) to collect intelligence. These new technological concepts have transformed the approach that security forces use to collect data. They make the process easy and less risky for the intelligence gathering officers. Other developed countries such as Russia, China, the United Kingdom, and Canada are also embracing the same technology to enhance their homeland security.
The focus of this thesis is to determine how the same GEOINT could be applied locally in the United Arab Emirates to enhance homeland security. In order to do so, it presents a literature review followed by a comprehensive analysis of questionnaires presented to a number of respondents, who all work in the UAE security sector. The findings reveal that the UAE needs to embrace the new technology to deal with the emerging security threats. The country has succeeded in creating a robust service industry, especially in tourism and air transport. The real estate industry and trade sector are also expanding rapidly as the government tries to reduce the country’s reliance on the petroleum sector. However, the sustainability of the growth depends on the ability of the government to ensure that residents and visitors are safe. The new technology will help the country to deal with the threat posed by regional extremists such as ISIL and Al Qaeda. The country’s security forces should use geospatial intelligence to gather intelligence and determine how to counter any terror attack or acts of crime. If necessary, drones can be used in armed combat when dealing with criminal gangs
Aknowledgment
I wish to express my deepest gratitude to my life coaches: my parents, and my life partner: my husband, many thanks, because I owe it all to you.
I am also grateful to my family who have provided me full support throughout my research. They were always keen to know what I was doing and how I was proceeding.
A very special gratitude goes out to my thesis advisor Dr. for her assistant. She consistently allowed this paper to be better by steering me in the right direction. I am indebted to her for her valuable comments on this thesis.
I would also like to thank the experts who participated in the questionnaire for this research. Without their passionate contribution and input, the research could not have been successfully conducted.
Finally, last but no means least, thanks to my manager Major and my work colleague Dr. for supporting me along the way.
Introduction
Background
The events of the September 11, 2001 Al Qaeda attack have had profound impact on the approach that countries take to counter various threats to security. Before then, the focus of many countries was to have a strong army capable of defending the country against external threats. Lowenthal and Clark (2016) explain that it never occurred to the United States that a small group of extremist could plan and execute a serious attack in the manner that the Al Qaeda did in 2001. The country was shaken as the attack focused on strategic places, including the Pentagon, which is the United States Department of Defense headquarters (Thomas, 2018). For a moment, the country was gripped with fear as it was not clear which other strategic building would be targeted by the attackers. It was a major surprise when it became evident that the attack had been planned, financed, and executed by an organization that had less than 1000 followers under the leadership of Osama bin Laden (Steiner, 2014). It was not the first act of terror planned and executed by Al Qaeda. In 1998, the same outfit had succeeded in planting explosives in American embassies in Kenya, Tanzania, and Uganda. Over 5,000 people were killed in these attacks (Chaliand & Blin, 2016). The United States realized that it had to redefine its approach of combating terrorism and other threats to homeland security.
The United States is not the only target of acts of terror. On April 3, 2017, Saint Petersburg metro station suffered a terror attack when an explosive device went off, killing many innocent civilians. In Western Europe, Germany, Britain, Spain, Belgium and France have suffered various incidences of terror attacks. A well-known example was the Charlie Hebdo attack, which took place on January 7, 2015, where an extremist group organized and executed one of the worst cases of terror attacks in the country (Suárez, 2017). A group of gunmen walked into the premises of this press firm and opened fire indiscriminately at everyone on their way, killing many people in the process. These incidences forces countries to be proactive when it comes to enhancing security. As Said (2015) notes, it is no longer tenable for countries to take a reactive approach of dealing with terror attacks and other acts that threaten national security.
Intelligence gathering has become core part of fighting acts of terror and threats to national security that may be sponsored by enemy states or extremist groups. The intelligence community has been playing a critical role in gathering information critical in enhancing security. Intelligence is collected in many ways – from human sources and agents, which is called Human Intelligence (HUMINT), openly available materials which is called Open Source Intelligence (OSINT) technical sources that include Measurement and Signature Intelligence (MASINT) which serves to detect, track and identify the signatures of target sources, Signals Intelligence (SIGINT) gathered from interception of signals, and Geospatial Intelligence (GEOINT) which uses remote sensing, geographic information system, unmanned aerial vehicle to capture image and utilize geospatial data as close to real-time as possible. Image data collection and analysis is the fastest way to get information to decision makers.
The concept of geospatial intelligence, popularly known as GEOINT, has gained massive popularity over the last decade as an effective proactive approach of dealing with threats. According to The United States National Geospatial Intelligence Agency (NGA), GEOINT which is considered the eyes of the intelligence community, refers to an “exploitation and analysis of imagery and geospatial information to describe, assess, and visually depict physical features and geographically referenced activities on the Earth” (Brown, 2015, p. 45). Geospatial Intelligence refers to everything on earth having a relational aspect in space and time. When you look at data and how they interact in the world in relation to specific places and specific times, its geospatial. Therefore geospatial information is the information that identifies a natural or constructive feature on earth by its geographic location and other characteristics. GEOINT allows to understand what is happening without having to be there.
Anyone who makes national policy decision, fights wars, and locates targets relies on GEOINT. Security services use GEOINT to detect the threat and know before they get there what they can expect, where these people are placed and what equipment are over there so they know exactly what to do and how to effectively get the job done. It has become critical for the intelligence agencies to go beyond using of spies to gather information critical in countering threats to homeland security. Geospatial intelligence makes it possible to monitor strategic geographical locations, especially places believed to be soft spots for terrorists and other criminals, with the goal of identifying any possible threat to peace and security. The emergence of unmanned aerial vehicles (drones) has made it possible for the military agencies and other law enforcement officers to monitor suspicious events and to plan effective counter attacks (Raman, 2013). Fitted with powerful cameras, a drone can help in collecting real-time information about a security breach and the pattern it is taking for effective planning of mitigation measures.
The United Arab Emirates is one of the fastest developing economies in the Middle East and North Africa (MENA) region. The city of Dubai is currently one of the top business hubs and tourists’ destination in the world. The emirate of Dubai has successfully managed to diversify its economy over the past decade. Tourism, air transport, hospitality, and trade are currently the main pillars of the economy. However, Miller (2013) warns that these economies are sensitive to the issue of insecurity. Any threat to security may have devastating impact on the growth of these sectors. The United Arab Emirates has remained a relatively peaceful and secure country despite the emergence of Arab Spring that affected the MENA region (Brown, 2015). It is worrying that some of the regional countries have remained volatile over the past seven years. Libya, Yemen, Iraq, and Syria are some of the most affected countries in the region. Many people fleeing these countries have to be accommodated in different peaceful countries, including the UAE. The problem is that the regional instability has led to the emergence of terror outfits such as ISIS.
Al Qaeda has also benefited a lot from the instability. Janmohamed (2017) notes, it is not easy to predict actions of these extremist groups. They have the potential of attacking any city in the region, and that is a major concern to regional leaders. Having an effective intelligence agency that can detect threat at the right time has never been more important to this country than it currently is (Rubin & Rubin, 2015). The military and law enforcement agencies need to know activities of these terror groups in the region and some of their possible targets. They also need to know if those who are admitted as tourists in the country are part of the terrorist planning to attack civilians in the country. Geospatial intelligence offers a good platform that can help the country’s security agencies to monitor activities of these groups and to plan effective ways of dealing with them, which will be explained in the next chapter. The aim of the study is to investigate the role and applications of geospatial intelligence in homeland security, and to explore how the concept can be applied to enhance the United Arab Emirates’ homeland security.
Problem Statement
The geopolitical position of countries in the Middle East puts them in a precarious position in terms of security. It is important to note that the focus of this paper is not political but security in nature. It might not be possible to separate politics from issues of security, as LaFree, Dugan, and Miller (2015) observe, but the focus of the paper is on security. Many countries in the MENA region are rich in oil reserves, one of the most important commodities in the international market for the last century. Studies have proven that powerful nations like United States and Russia keen on controlling the regional oil reserves often fuel the political instability in some of these countries (Udochukwu, Christian, & Adebayo, 2014).
Libya, Iraq and Syria are no longer stable and terror groups such as ISIS and Al Qaeda have infiltrated these territories as safe heavens to plan and execute their activities. Irrespective of the cause, insecurity is a major cause of concern in the region.
The infrastructure needed to facilitate exploitation, processing, and transportation of petroleum products are sensitive to any form of damage. Any major leak in the oil pipeline can have devastating environmental consequences on the area affected. Any form of attack on these pipelines cannot only have serious consequences on the environment but also safety of the people. Moreover, most of them are expensive and any destruction may cause serious negative consequences on the normal business operations of the affected firm. As explained above, the United Arab Emirates, especially the emirate of Dubai, has developed a robust service sector (Ganor, 2015). The service sector is just as delicate as the oil and gas sector when it comes to terror attack. It means that although the United Arab Emirates is enjoying years of economic prosperity, any major attack can cause a negative transformation, as major pillars of the economy will be affected. Geospatial intelligence is currently considered an important approach of ensuring that security is enhanced.
It is important to note that using GEOINT to manage security may not be easy. Other than the complex nature of the technology involved, there is the legal aspect that cannot be ignored. In the United States, law enforcement agencies are expected to get court order before conducting surveillance on a private property. The law protects citizen’s privacy, and any form of surveillance is considered a breach of that privacy (Hanhimäki & Blumenau, 2013). The complex nature of the legality of geospatial intelligence has been one of the major problems when using this approach of enhancing homeland security. Some of the criminals and extremists groups operating in the country would never give consent to the security officers to survey their premises. On the other hand, the law enforcement agencies need to conduct the regular surveillance to identify and deal with any threat. It is not possible to have court orders every time the security organs want to collect aerial data. In the United Arab Emirates, tourism is currently one of the main pillars of economy. Tourists want to be assured of their security while at the same time they want privacy. When they realize that their activities are under surveillance, they would become uncomfortable. Others may even consider visiting other regions. It means that when looking at the applicability of geospatial intelligence in enhancing homeland security, legal issues, and comfort of citizens and tourists should be considered.
Purpose of the Study
The primary objective of this study is to explore the significance and application of geospatial intelligence in homeland security. The special interest of this project is to determine how the United Arab Emirates (UAE) can enhance border and homeland security using the emerging technologies of gathering intelligence. It is a fact that in this region, security is a major challenge even to relatively peaceful countries such as the United Arab Emirates, and the other GCC countries. Protecting the borders becomes a major challenge, especially in countries that border regions, which are currently affected by the Arab Spring (Janmohamed, 2017). GCC countries bordering Yemen, Syria, and Iraq face a serious problem of ensuring that their borders remain safe. It should also be remembered that hostile nations such as Iran also pose a serious security threat. That makes it necessary to secure the borders. The activities of the enemy should be monitored to ensure that whenever they plan an attack, countermeasures could be put in place within the right time to protect residents of the country and their property.
Geospatial intelligence offers the solution needed to overcome the emerging challenges. The paper will look at who should be involved in managing border security using the new technology. As mentioned above, the responsibility of managing border and homeland security should not be left to the security service. The judiciary also has a role to play. Once the criminals or terrorists are arrested, they have to be taken to court to be sentenced based on the existing laws of the land (Law, 2015). It means that actions taken by the law enforcement agencies must be within the law to ensure that the suspected culprits are punished as appropriate. As such, the study will look at the role of the judiciary in the fight against threat to homeland security using geospatial intelligence. Locally in the United Arab Emirates, the study will look at how the intelligence can be gathered effectively without making citizens and tourists uncomfortable.
The significance of geospatial intelligence on homeland security is a relatively new area of study as the nature of security threats continue to change with the emerging trends in communication technology. When conducting the study, it is necessary to narrow the focus to avoid cases where irrelevant data is collected. Zarakol (2011) warns that when there is no proper guidance on which data is needed, it is possible that a researcher would end up gathering information that does not directly respond to research goals and objectives. As such, it is always advisable to develop research questions in line with the goal and objectives of the study. These questions dictate the kind of data that should be collected from primary and secondary sources. The primary research question is:
How can geospatial intelligence be applied to support homeland security in the UAE?
The primary research question directly responds to the research topic. Answering the questions makes it possible to meet the main goal of the study. Janmohamed (2017) argue that in many cases, it is often necessary to develop secondary research questions. They support the primary question by identifying smaller objectives that would lead to the realization of the primary goal of the study. The following secondary questions were developed:
- What is the role of geospatial intelligence in homeland security missions?
- How, when, and where can geospatial intelligence be an effective tool in supporting homeland security professionals and decision makers?
- Who should be involved in the use of geospatial intelligence to promote homeland security?
Data obtained from primary and secondary sources will help in answering each of these questions.
Theoretical Background
There are limited studies on geospatial intelligence in homeland security because the concept is relatively new in the UAE. However, it is necessary to appreciate that a few studies have looked at this topic from various angles. Looking at the findings made by these scholars will enhance understanding of the issue under investigation. When reviewing literature, one of the primary areas of interest will be to look at some of the theories relevant to this study. The theoretical background makes it possible to understand some of the concepts that have been developed by other scholars to help explain the issue at hand. One of the most important concepts that will be used is the Mosaic theory of intelligence gathering. The primary focus of this study is on how government agencies can collect necessary information in time to help deal with security threats. As such, this theory will be of critical importance. It will also be necessary to look at some of the theoretical concepts regarding managing security within a given area. Some of the concepts that will be critical include clash of civilization. Others include post-structuralism and realism. Each of these theories will be discussed in details in chapter 2 of the thesis.
National security is an issue that has attracted extensive research from various scholars for the past several decades. The nature of security threats keep changing. The theoretical background helps in identifying some of the notable concepts and beliefs that have been developed by scholars in the security sector in the past. It is necessary to look at some of these theories and concepts that have been developed, and determine their relevance in light of the issue being investigated in this paper. Some of the theories and concepts that were considered appropriate in this study include the mosaic theory of intelligence gathering, risk society, clash of civilization, post-structuralism, and realism.
Mosaic theory of intelligence gathering
The theory holds that it is necessary to gather small and separate pieces of intelligence and use them to construct a unified picture of an issue that is of interest (Briant, 2015). It is based on the belief that it may not always be possible for the government to gather all the needed information from one source to understand a given issue. As such, it is advisable to gather different bits of information from different sources, find a link between them, and then develop a complete picture of the problem under investigation. This theory is relevant to this study. The national government of the United Arab Emirates has a responsibility to protect its citizens. The responsibility can only be taken with success if data can be collected from various sources and processed appropriately to understand the nature of threat to national security. In many cases, it may not be possible to use one system to gather all the information needed. It may be necessary to use various platforms to collect such data. The use of intelligence officers, as has been traditionally the case, is still important. However, the security agencies stand a better chance of fighting crime is intelligence gathering also include the use of GEOINT. The information gathered by spies could make a greater sense if it is supported by data that is obtained using GIS and remote sensing machines (Heather, 2018). It will be easy to plan a counterattack against any threat to national security.
Risk society
The concept of risk society is defined by Briant (2015) as “a society that is increasingly preoccupied with the future (and also with safety), which generates the notion of risk” (p. 43). When the society constantly focuses in the current development to enhance sustainability and future success of the country, it is impossible to ignore the potential risks that it faces. The government and citizens will always focus on factors that may affect the ability to achieve goals meant to make the future better for the citizens. The concept is very relevant to this study, given that the focus is to determine how to apply GEOINT in enhancing security of the United Arab Emirates. The Vision 2021 of the UAE is a long-term plan, which aims at transforming the country into one of the best in the world in various respects (Heather, 2018).
The plan is meant to improve the health sector, employment opportunities, transport infrastructure, and most importantly to diversify the country’s economy and reduce its reliance on the oil and gas sector. In an attempt to achieve these goals, the country must be conscious of the risks that the society faces. One of the biggest threats to the country’s Vision 2021 is insecurity. The threat posed by terror organizations such as ISIS and Al Qaeda is real (Chaliand & Blin, 2016). The service sector that is currently booming in Dubai can be destroyed when there is insecurity. It means that managing homeland security must be the top of the government’s agenda as it focuses on achieving the vision. GEOINT promises to be an effective way of dealing with this threat. Using modern technology to gather intelligence and to plan attacks and counterattacks against security threats will enhance homeland security in the country.
The Study Scope
It is necessary to discuss the scope of the study for the benefit of those who may find this thesis relevant in their studies or policy-making. The primary goal of the study is to investigate the application of geospatial intelligence in missions of homeland security as a way to counter terrorism, Critical Infrastructure Protection (CIP), and enhance border security. Data collection will specifically focus on these areas of study. The information will be collected from published sources such as books, government reports, online platform, and other reliable sources. The methodology is discussed further in chapter 3.
It is important to note that this thesis focuses on how the GEOINT can be applied in the local context of the United Arab Emirates. It means that factors that are unique to this country were taken into consideration. It would be necessary for those applying the recommendations made in this thesis to consider these facts. For instance, the recommendations in this thesis can be applied in regional countries that share the same geopolitical environment such as the Kingdom of Saudi Arabia. The information may require some modification if it is to be applied in Europe, North America, Far East, and parts of Africa that do not share the same factors that the UAE faces when it comes to dealing with the issue of security.
Research limitations include confidential reports regarding GEOINT. Although there are several studies and researches about GEOINT, it is difficult to acquire data as the most significant data are confidential. Thus, this research will only investigate published material and publicly available data. The investigation of this study is limited and more empirical support is required.
Terminology Definition
It is necessary to define some of the technical terms and common abbreviations used in the study. Although some of them are defined within the text, it is necessary to list all of them here to make it easy to understand the document. The following are the terminologies and abbreviations:
CIP- Critical infrastructure protection: a strategy and mechanisms put in place by government agencies to protect important infrastructures such as oil pipelines, roads, rail, airports, and seaports (Thomas, 2010).
GCC- Gulf Cooperation Council: an intergovernmental political and economic union that brings together all Arab countries in the Persian Gulf with exemption of Iraq (Janmohamed, 2017).
GEOINT-Geospatial intelligence: refers to intelligence gathered about human activities on earth collected using aerial devices (Nacos, 2016).
GIS- Geographic information system; it refers to a system that is designed to capture, analyze, manage, store, and present geographic data (Deogawanka, 2015).
GPS- Global Position System: it is a radionavigation system used to provide geolocation of a given object anywhere on or near the earth at any given time (Conrado, Neville, Woodworth, & O’Riordan, 2016).
Homeland Security: it is a department within the United States responsible for maintaining security of Americans and their properties within the country. In a general context, it refers to the general security of people and properties within the national border (Biltgen, 2016).
ISIS- Islamic State of Iraq and Syria, sometimes known as ISIL- Islamic State of Iraq and the Levant: is an Islamic extremist group that is predominantly based in the politically unstable countries in the MENA region (Briant, 2015).
MENA- Middle East and North Africa: it has 22 member states from the Middle East and North Africa, which are predominantly Islamic states (Scott & Howlett, 2018).
RS- Remote Sensing: the process of scanning the earth using high-flying aircraft or satellite to obtain specific information (Asmat, 2012).
UAE- United Arab Emirates: It is the country of interest in this study within the GCC.
UAV- Unmanned Aerial Vehicle: it refers to an aircraft that is controlled remotely hence does not need to have a pilot on board (Deogawanka, 2015). It is mostly used for surveillance or in transporting explosive.
Organization of the Thesis
It was necessary to have a proper structure for this thesis to ensure that the set objectives are achieved. The first chapter is the introduction. It provided a detailed background of the topic, statement of the problem, and purpose of the study. It also outlines research questions, and scope of the study. The second chapter is the literature review. It explores studies that have been conducted regarding geospatial intelligence in various countries, especially in the United States. It looks at how GEOINT can contribute to achieving the mission of homeland security. Chapter 3 defines the method used to collect and analyze data. It defines the design, data collection method, treatment, and analysis procedure. Chapter 4 provides the findings made from the analysis of data. It explains how GEOINT can help in promoting homeland security. It also demonstrates how the concept can be applied in the GCC, specifically in the United Arab Emirates. Chapter 5 provides a summary of the paper and recommendations based on the findings made from the study.
Literature Review
In the previous chapter, background information about the topic has been provided. Goals and objectives that should be realized by the end of the study are also outlined. In this section, the aim is to provide a detailed review of literature in this field. According to Ahmad (2018), reviewing literature is important because it enables a researcher to understand what other scholars have found out in that field and the knowledge gaps that needs to be addressed. Conducting a review of literature also helps in avoiding cases where information that already exists is duplicated in a new study. Reproducing information that is in public domain does not help to improve knowledge in that field. This chapter starts by discussing the concept of homeland security. Major threats to lives of people and their property are discussed in this section. It then goes ahead to define the concept of geospatial intelligence and the way it has become critical in enhancing national security. The next section looks at the stages in the implementation of geospatial intelligence to counter terrorism and other criminal acts within the country. The chapter then discussed the growing popularity of GEOINT in various parts of the world. Looking at some of the theoretical concepts will also enhance understanding of the issue being investigated. The last section of this chapter is the identification of the research gap that needs to be addressed using primary data.
Homeland Security
The concept of homeland security emerged in 2002 when President George W. Bush created the Department for Homeland Security as a direct response to the September 11, 2001 terror attack. Since then, the concept of homeland security has gained massive popularity in the country and other parts of the world. The Department of Homeland Security defines the concept as “a national security, especially with regard to the threat of terrorism within a country’s borders” (January, 2018, p. 78). Scholars and experts in the security sector are yet to come up with a universally acceptable definition of the term homeland security. However, there is a universal belief that the concept is used in reference to safety of people and their property within the national borders of a country. It is important to look at the threats to homeland security, including the event that led to the creation of the concept.
September 11, 2001 Al Qaeda Attack
The United States has always been investing many resources in the security sector to ensure that its borders are secure and that its people are not subjected to any threat. According to Chaliand and Blin (2016), as one of the superpowers in the world, the country is constantly under threat of attack by hostile nations. For a long time, until the fall of the USSR in 1991, the focus of the country security organs has been on monitoring actions of Russia and its allies because of the belief that they have the potential to organize and execute devastating attack using nuclear weapons. It never occurred to the security forces that the country was in greater danger of serious attack from terrorists. That changed on September 11, 2001 when a terrorist group, Al Qaeda that was then headed by Osama bin Laded, organized and executed one of the worst attacks in the country’s modern history.
On September 11, 2001 at about 8:46 a.m., American Airline Flight 11 that was en route to Los Angeles with 92 people on board, including the five terrorists, was flown directly into the Northern Tower of the World Trade Center (Hanhimäki & Blumenau, 2013). After about 15 minutes, the second plane, United Airlines Flight 175, flown into the Southern Tower of the World Trade Center at 9:03 a.m. It had 51 passengers, 9 crewmembers, and 5 hijackers (Law, 2015). At this moment, it was apparent that the country was under attack. At 9:30 a.m., the third plane, American Airlines Flight 77, was flown into western part of pentagon, the headquarters of the United States Department of Defense (Nacos, 2016). The country was gripped with panic, as it was not clear when and where the next strike would be. The bold decision of attacking the headquarters of the country’s defense forces meant that the White House was no longer safe for the president. Indeed the hijackers had taken control of the fourth plane, United Airline Flight 93, and the target could have been the official residence of the United States president. The passengers on board this plane, upon learning the fate of other planes, wrestled with the hijackers and the plane crashed into a field in Pennsylvania at about 10:03 a.m.
The attack left 2,996 people dead and 6000 people suffered varying degree of injuries (Nacos, 2016). Majority of the casualties were within the buildings targeted by the attackers or close to them. The attack also had a devastating impact on property, especially the buildings that were directly hit. Most importantly, it became apparent that the United States was at a great risk of terror attack from terror groups. The country realized that although the threat posed by hostile states such as Russia and its allies could not be ignored, terrorists posed even greater threat. The fact that they are non-state actors and are not answerable to any government or international body makes them highly unpredictable. The fact that a small group of people, headed by Osama Bin Laden who was not even an army general, could organize, and execute one of the most devastating terror attacks in the United States modern history was shocking.
The investigation that was conducted soon after the attack revealed that one of the main weaknesses demonstrated by the country’s security organs and intelligence agencies was the inability to have the right information available within the right time for the right team of security organs within the country. The CIA and FBI had gathered intelligence that a small terror outfit, led by bin Laden, was planning an attack within the country (Hanhimäki & Blumenau, 2013). The investigations had revealed that the team was targeting planes, but it was not clear what exactly they were planning to do. The limited information that the security organs received delayed their ability to take appropriate precautionary steps, leading to one of the worst disasters in the country’s history. Security experts believe that this attack would have been avoided at various stages if the country’s law enforcement agencies and intelligence units could have coordinated their activities and conducted a thorough surveillance into the activities of these criminals. Since then, the United States has taken seriously the issue of intelligence gathering and sharing of information among different government departments.
The Emergence of ISIS
The threat to homeland security has become a major issue not only in the United States but also in different countries around the world. The emergence of extremists in the Middle East is a major concern not only to the regional countries but also to others in the world (Nacos, 2016). One of the terror groups, which have grown rapidly over the recent past, is the ISIS. When the government of Saddam Hussein was brought down in Iraq, it created a power vacuum that was filled by terrorists. The collapse of the government of Afghanistan following the War on Terror also made it easy for this group to expand. Unlike Al Qaeda that had a problem of recruiting a large army because of the limited financial resources, ISIL had a unique strategy of taking control of oil field, which enabled them to have a sustainable flow of income. It has been able to recruit people from North America, Europe, Africa, and other Asian countries. According to Law (2015), most of the attacks organized and executed by this terror group often target regional countries, especially Iraq, Afghanistan, Syria, Pakistan, Libya, Turkey, Yemen, and Saudi Arabia. European and North American countries have also suffered various attacks from this group.
In October 2015, a Metrojet Flight 9268 from Egypt en route to Saint Petersburg was bombed, killing all the 224 people on board, majority of whom were Russians travelling back home after a holiday in the North African country. ISIL claimed the responsibility (Suárez, 2017). In November 2015, a group of ISIL fighters opened fire in Paris, indiscriminately shooting at unarmed civilians in the city. Others took hostages while another groups used grenade. In the end, 130 lives were lost while another 368 people sustained serious injuries. On March 2016, suicide bombers who were members of ISIL attacked an airport and a metro station in Belgium, killing 32 people and wounding 340 others (Nacos, 2016). On July the same year, France was struck once again, this time a 31-year-old man drove a 19-tonne cargo truck into a crowd, killing 86 people and wounding 434 others (Suárez, 2017). In the same month, Germany was attacked when a young immigrant used a knife against innocent civilians. It was established that some of the immigrants who had come to the country as refugees were actually radicalized members of ISIL. In March 2017, the United Kingdom suffered an attack by this group when in Westminster that left six people dead and 49 others seriously wounded (Ahmad, 2018). The pattern shows that no country is safe from an attack by the emerging terror groups. The strategies used by ISIL and Al Qaeda shows that these terrorists often target unarmed citizens when it is least expected.
Homegrown Terrorism
One of the major issues emerging in homeland security is homegrown terrorism, also known as domestic terrorism. Soon after the 2001 Al Qaeda attack in the United States, the concept of terrorism was viewed by many as an attack planned and executed by Islamic extremists, especially those from the Middle East (Law, 2015). However, a new wave of terrorism is emerging in different parts of the world where attackers are locals other than the expected group of people from the MENA region. Some of these individuals have never even left their home country. Nonetheless, they get strong conviction to attack fellow citizens because of personal beliefs influenced by propaganda spread by terror groups and the events taking place in the MENA region.
The emergence of various online communication platforms makes it easy for them to understand events going on in other parts of the world. Ahmad (2018) notes that most of these local terrorists may not have the opportunity to get the military training those others within the MENA region have. Jenkins, Croitoru, Crooks, and Stefanidis (2016) explain that they can learn how to make dangerous explosive through the internet. These criminals are just as dangerous as those who are outside the borders of the country. In fact, the ease with which they can strike any part of the country and the inability of the security organs to predict their actions make them more dangerous than their counterparts who are out of the country. It is necessary to look at some of the major attacks that have been planned and executed by local extremists in various parts of the world.
European and North America are currently some of the worst affected regions by the problem of homegrown terrorism. In 2014, Canada suffered two attacks by individuals who were born and brought up in the country. These attackers targeted civilians as a way of expressing their frustration with some of the foreign policies that the country has adopted. In July 2011, Anders Behring Breivik planted a bomb in a car in Oslo, killing eight people when it went off (Hanhimäki & Blumenau, 2013). He also organized another attack on the island of Utøya, killing another 69 people. The Norwegian expressed his displeasure towards Islam and the countries immigration policies that allowed people from the Middle East to seek refuge in the country. The London underground bombing on July 2005 and the Madrid train bombing of 2004 were also planned and executed by the locals (Nacos, 2016). Other countries such as the Netherlands, Italy, France, Australia, and Nigeria have also suffered from acts of terrorism committed by their citizens.
The United States is the worst affected country by the problem of homegrown terrorism. Ahmad (2018) explains that domestic terrorism in the United States can be traced back several years before the September 11 incident. However, the term terrorism was not in use during that period. One of the most memorable acts of terror in the country was the Oklahoma City Bombing that took place on April 19, 1985 (Hanhimäki & Blumenau, 2013). Timothy McVeing and Terry Nichols took time to develop explosives then loaded them into a truck before packing it in front of the Alfred P. Murrah Federal Building. McVeing went ahead and detonated the explosive, which had disastrous outcome. One third of the building was wiped out by the explosion. The blast was so strong that it destroyed or damaged 324 other buildings, which were within a 16-block radius. Several cars and other structures were destroyed in the process. The incident left 168 people dead and 680 others injured (Hanhimäki & Blumenau, 2013). The terrorists claimed that their motive was to express their frustration with some of the policies made by the federal government.
The Boston marathon bombing of 2013 was one of the first major terror attacks in the country after the September 11 attack. Two brothers, Dzhokhar Tsarnaev and Tamerlan Tsarnaev improvised a simple explosive using a pressure cocker. They placed the two bombs 190 meters apart in crowded placed where city residents were following the events of the marathon. The two homemade bombs went off, killing three people and wounding over 264 others. Security forces were able to identify the attackers who later admitted to their crime, stating that they were not happy with the continued presence of American soldiers in Afghanistan and Iraq (Nacos, 2016). This incident was very important to the American security agents because for the first time after creation of the Department of Homeland Security, a major attack took place in an area that had a high number of security agents because of the sporting event. It was a major demonstration of the existing weaknesses in the country’s security system.
The Orlando nightclub shooting that happened on June 12, 2016 is a more recent example of the dangers posed by homegrown terrorists. The lone-wolf terrorist, Omar Mateen, was a 29-year-old American who was working as a security guard. He was born in the United States, although his parents had emigrated from Afghanistan. Omar embraced the Muslim faith and believed that he had to be more loyal to his people back in Afghanistan than to the United States (Nacos, 2016). He did not like the United States foreign policies, especially the presence of the United States troops in Afghanistan and other parts of the Middle East. He purchased some of the most effective semi-automatic rifles and thousands of ammunitions. He then targeted a local LGBT nightclub in Orlando. The mass shooting, which left 49 people dead and 53 others wounded.
A year after the Orlando nightclub shooting, there was another major terror attack in the country, the Las Vegas shooting of 2017. The Las Vegas shooting presents a unique case of insecurity to homeland security. On October 1, 2017, Stephen Paddock, a 64-year-old man from Mesquite, Nevada, opened fire on concertgoers at Route 91 Harvest music festival (Thomas, 2018). Strategically positioned on a 32nd floor of the Mandalay Bay hotel, he fired over 1,100 rounds, targeting those who were celebrating across the street. It is reported that 58 people died of gunshot wounds while 851 others were injured. He later committed suicide in his suite before the officers could arrest him. His case was unique because the investigations revealed that he had no links to ISIL or any other extremist groups. He was born and brought up in the United States and was not a Muslim. Before the incident, no one would have suspected that he would commit such a heinous crime. The analysis of his brain at Stanford University revealed that he had no serious mental disability. He left no evidence that could explain his motive.
Understanding the Concept of Geospatial Intelligence
The concept of geospatial intelligence is increasingly becoming popular in the field of security management. Ahmad (2018) defines GEOINT as “intelligence about the human activity on earth derived from the exploitation and analysis of images and geospatial information that describes, assesses, and visually depicts physical features and geographically referenced activities on the earth” (p. 32). It is a new form of gathering intelligence with the help of the emerging technologies. According to Janmohamed (2017), the traditional method of gathering intelligence was to use Human Intelligence who would investigate an issue and gather necessary information. The emergence of aerial photography was seen as being important to scientists keen on studying the earth for various reasons. It then became evident that this technology could be used in the security sector to understand activities of the enemy within a given region.
In homeland security, GEOINT is increasingly becoming a crucial aspect of monitoring and gathering relevant information needed to enhance safety of people and properties. As explained in the section above, homeland security is currently affected by both internal and external threats. Although terror organizations operating beyond the borders of a country still pose a serious threat to the national security, there is also the issue of citizens who have decided to join terror groups and help them achieve their goals locally. Predicting when and how these criminals would act may sometimes be a major challenge. With the help of GEOINT, security organs can monitor suspicious activities and take necessary actions before members of the public can be put in harm’s way. It is necessary to evaluate different aspects of GEOINT and the manner in which they facilitate intelligence gathering and security management within the country.
Geographic Information System
The geographic information system is one of the most important aspects of geospatial intelligence. January (2018) defines GIS as “a system designed to capture, store, manipulate, analyze, manage, and present all types of geographical data” (p. 78). It goes beyond collecting the physical data about a given geographical area. For instance, if it focuses on a school, it will provide the exact physical location of the institution, the number of students, teachers, and other non-teaching staff members, subjects taught in the institution, student capacity, and any other vital information that would be needed. As Janmohamed (2017) observes, GIS goes beyond the use of software to gather the physical factors of the issue under investigation. It also looks at other relevant information that may be needed. The comprehensive approach of investigation that that GIS embraces has made it one of the most popular tools in the security sector. It is often used to make critical decisions and to solve complex problems that would be challenging to address without such information. In homeland security, GIS is often used in the following ways:
- The first area of use is to map where things are, as January (2018) notes. The security forces can map the exact location of a security threat. It may not be within the borders of the country but close enough. Because of the various international laws that limit a country from making a military ambush when the target is outside the borders, the best that the border protection unit and other security organs can do is to monitor the activities of the enemy. With the help of this technology, it is possible to determine the exact location of the security threat and determine if they are making advances towards the country’s border.
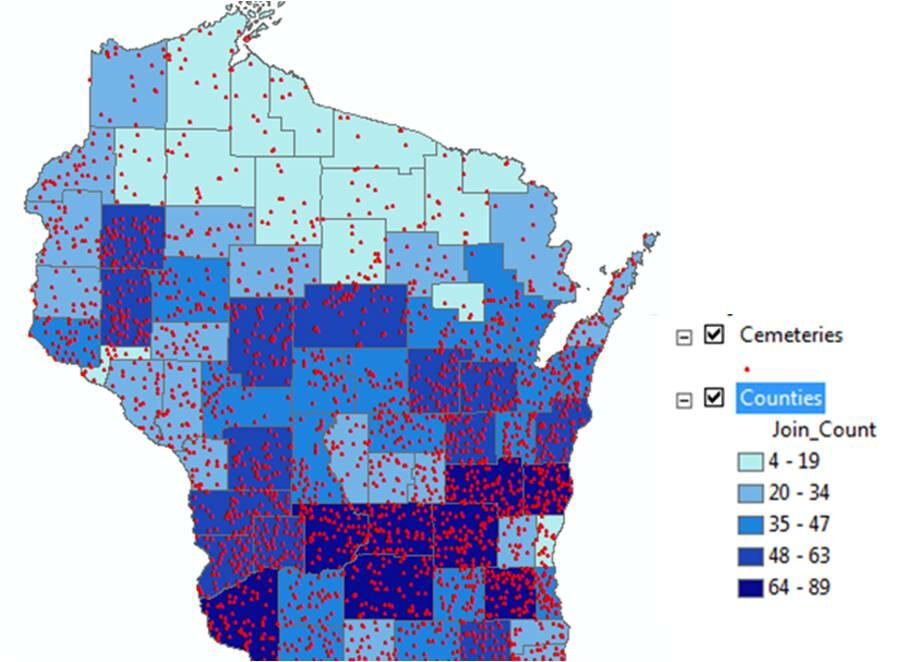
- GIS can also be used in mapping quantities. Nacos (2016) explains that one of the security nightmares that GCC member states have had to deal with over the recent past is the influx of refugees. The internal wars in Yemen, Syria, and Iraq have forced many people to flee their homes because of the fear of attack. The problem is that a country like the United Arab Emirates can only have a manageable number of refugees. Having an influx of undocumented immigrants can be a major security threat. The problem is that some of them may be part of extremist groups intending to launch an attack once they are within the borders. Using this technology, the border control forces can determine how to manage such a large number of immigrants in a way that will not pose any threat to homeland security. Figure 1 below shows how the system can be used to map quantities of things, which are of interest to security organs.
- GIS can be used to determine what happens inside a specific region. The threat to the national border security is one of the issues that national defense forces and other law enforcement organs must deal with effectively. Monitoring movement near the border is critical. Using this technology, the officers can have a clear view of every activity near or within the border. If a group of people is moving towards the border, this technology can be used to determine the composition in terms of gender, age, and items they are carrying. It is easy to identify potential threat that they pose to the country’s security. The information makes it possible to make the necessary decisions on how to counter the threat. Deogawanka (2015) also explains that GIS can help to determine any potential change within a given region. The security team will be able to determine if the threat is becoming more serious or not.
Global Positioning System
GPS is another information gathering system that has gained popularity both within the military and among civilians. According to Nacos (2016), GPS is “a global navigation satellite system, which provides the exact geo-location and time information to a receiver anywhere on earth” (p. 45). Originally, GPS was used exclusively by the United States military to identify the location of security threats, especially when on missions out of the country. It would help the commanders to identify the position of the targets, their movements, and other vital information that is needed to make the right decision. They would also make use of this system to launch an attack against the enemy at a time when they least expect it. January (2018) explains that this technology proved useful when the United States’ troops were fighting in Iraq and Afghanistan. It minimized the number of casualties by improving accuracy in attacks and reducing cases where the enemy would ambush the American soldiers. This technology has gained massive acceptance among the law enforcement agencies and civilians who may want to gather geographic information of a given location. It has become one of the effective tools used to monitor activities of those believed to pose significant security threat to homeland security in the United States. Its application has gained popularity in other parts of the world, especially in Europe where the problem of illegal immigration is becoming a major concern.
Remote Sensing
Remote sensing is another strategy of gathering intelligence about a phenomenon or an object without having to be physically present within that location (Deogawanka, 2015). One can use aircrafts or satellite to collect the needed information within a specific geographic location. This concept has gained popularity in various scientific disciplines such as ecology, oceanography, hydrology, meteorology, geology, glaciology, and military science (Nacos, 2016). It is important to note that in each discipline, a different approach of collecting data would be needed to achieve specific goals. In the military, unmanned aircrafts have become effective when it comes to collecting data. Biltgen (2016) says that remote sensing makes it possible for the security organs to gather intelligence without having to send troops to the field. In the past, intelligence officers had to be sent to a specific location to gather specific information, including geographic maps of a given area to help the forces in planning an attack or a counterattack. However, that is no longer necessary because of the emergence of remote sensing. A few experts in the field of technology can collect such data without having to move out of the office. It is not only cost-effective way of gathering intelligence but also safe for the officers involved.
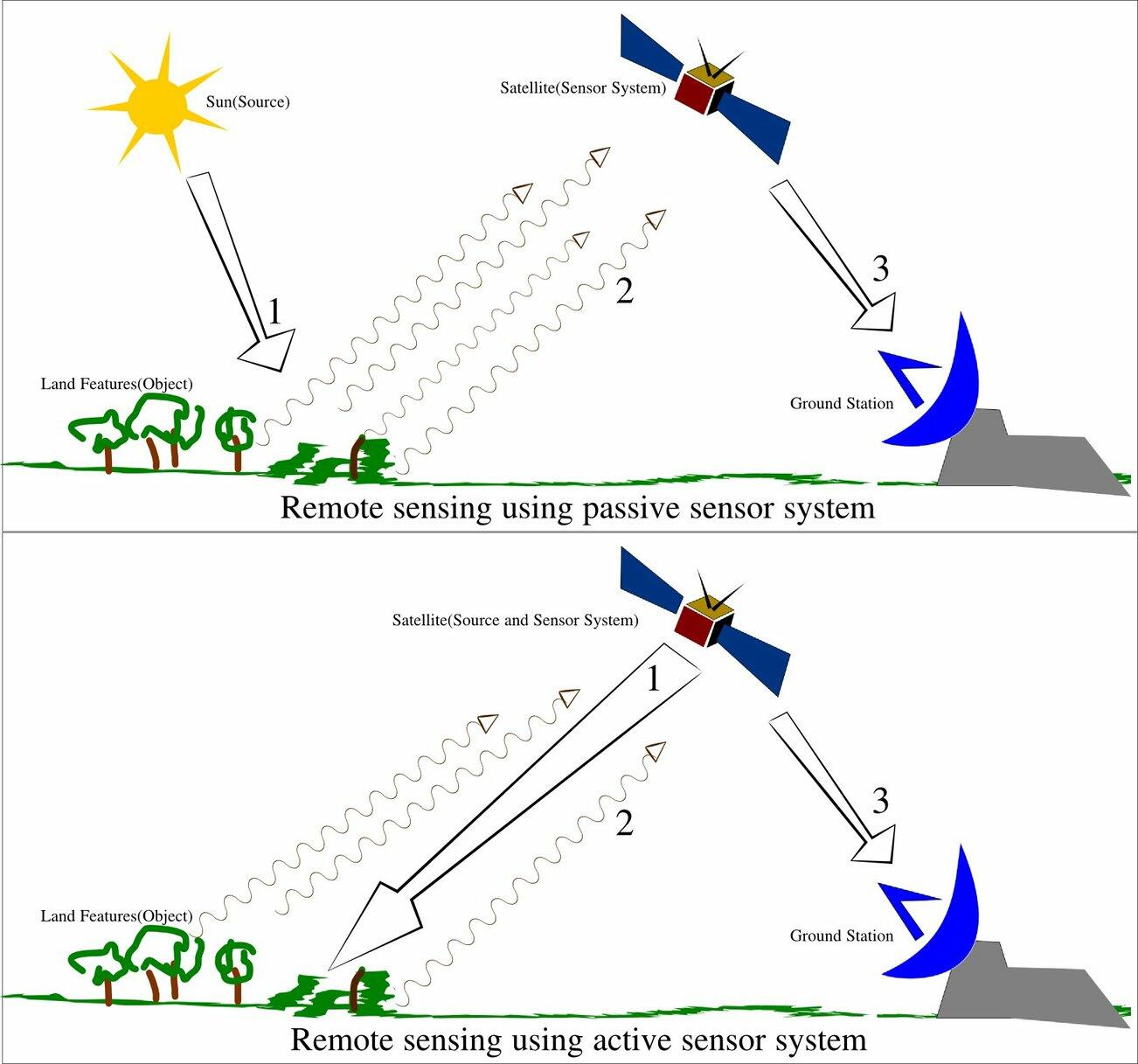
When using remote sensing, data can be gathered in two main strategies. The first strategy is passive sensing where sensors are used to gather radiation emitted by objects within a given area. In most of the cases, it uses the reflection of sunlight to gather information (Hanhimäki & Blumenau, 2013). The passive approach of gathering data is often used when there is need to monitor if there are movement of objects within a given location. Any abnormal changes in the reflections would indicate that a series of activities are taking place within the region of interest. The second strategy is the active collection where the satellite or sensor organ emits energy that scans objects within a given area to detect and measure radiations reflected in a given area. It is often used in cases where the detectors cannot rely on the sunlight, especially at night. Active collection of data, especially the use of LiDAR and RADAR, has gained popularity among the security personnel because of its ability to gather the needed data at any time and with greater efficiency. LiDAR stands for Light Detection and Ranging and it’s a remote sensing tool that uses ultraviolet, visible, or near infrared light to measure distance and create a 3D image of objects. It can tell the three-dimensional structure of an object even while moving. RADAR stands for Radio Detection Ranging which uses radio waves to scan the environment. Figure 2 below shows the two remote sensing strategies.
Unmanned Aerial Vehicles
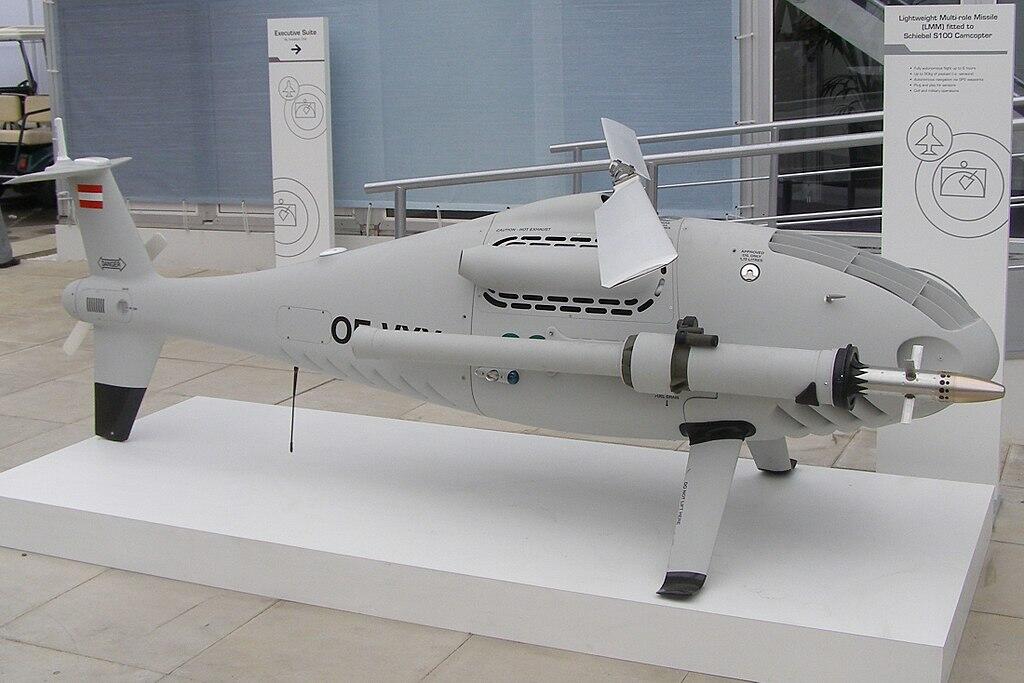
The use of UAV has become popular over the recent past. According to Nacos (2016), the United States intelligence agencies often found it challenging using manned airplanes to collect data, especially in volatile regions where the enemy had the capacity to bring such planes down using surface-to-air missiles. When that happened, the officer operating the plane would be taken captive or killed by the enemies. One of the biggest challenges of using these planes is that they were relatively large to accommodate the pilots. As such, they could be seen by the enemy, making them easy targets. The emergence of the unmanned aerial vehicles was considered a major solution to this challenge. Its small size meant that it could easily hover within a given region for a long time without being monitored. In case the enemy monitors it, there would be no casualty in case it is brought down. Others would be fitted with explosives to ensure that if they were brought down using surface-to-air missiles, they would turn into bombs. The enemy, knowing the danger of shooting such an explosive, may only launch complaint with the suspected agency instead of taking it down. The fact that the plane would explode before touching the surface of the earth means that the intelligence gathered will be destroyed before it could land in the hands of the enemy. The unmanned aerial vehicle is often used in two main ways.
- Intelligence gathering is one of the first and most important uses of UAV. January (2018) argues that the unmanned aerial vehicles have become the most useful tools in collecting information within a given area. These vehicles are fitted with powerful cameras and sensors to help monitor activities within a given area. Advanced technologies have made it possible to ensure that information collected using this instrument is relayed in real time without having to wait for it to land. It means that the vehicle can remain in the air for as long as it may be necessary to collect the needed information by the security agents. This technology also helps in case the enemy brings down the vehicle. The data collected will not be lost. Biltgen (2016) notes that most of these drones are currently fitted with explosives to ensure that if it is intercepted by the enemy, it explodes to avoid cases where enemies can use the collected information or the aircraft itself for their self-interest.
Figure 3 below shows a drone that is on a mission to gather intelligence.

- The drones are also used in active combat in regions where the enemy has the potential to bring down warplanes. Nacos (2016) explains that during the Vietnam War, many American planes were brought down by the enemy forces. Such incidences not only cause a massive destruction of military hardware but it also leads to loss of lives of the jet pilots and other officers in these planes. The emergence of drones was a major breakthrough in the United States’ military capacity. Instead of using the expensive aircrafts, soldiers can use these drones fitted with explosives to attack the enemy. Janmohamed (2017) says that using the drones in the battlefield is like playing a zero-sum game with the enemy. When the plane is brought down within the territories of the enemy, it will explode, and people within the area will be hurt. If the enemy decides not to bring it down, the bombs will be dropped, which is just as bad as downing the plane. This equipment has been used widely by the United States army in Syria, Iraq, and Somalia to fight extremist groups. In Libya, it was used by the west to attack Muammar Gaddafi’s convoy, making it easy for the rebels to abduct and kill him (Nacos, 2016). Figure 4 below is a drone fitted with a multirole missile, ready for an action.
Stages of Implementing GEOINT in Counterterrorism
Deogawanka (2015) explains that the threat to homeland security is an issue that does not just affect the United States of America but all other nations around the world. The study of the activities of terror groups and other terrorists show that both developed and developing nations are at risk. Europe, North America, Africa, and parts of Asia have all suffered from the activities of such criminal groups (Monaco, 2018). Using the emerging technologies can help enhance homeland security. The following are the stages in which the security organs should use geospatial intelligence to fight crime:
Monitoring/Surveillance
One of the first steps in fighting acts of terror is to gather intelligence about the activities of the terror groups to understand their plans. Biltgen (2016) says that the sophisticated nature of some of these terror groups makes it dangerous for the security agencies to take a reactionary tactic of dealing with them. Instead, the team must be proactive enough to know the plans of these individuals and take appropriate actions to protect lives of members of the public and their property. When using tools such as GIS and unmanned aerial vehicles, it is possible to identify the location of the threat, possible action that is being taken by the enemy, and the best way to organize a counter attack. The information gathered will make it possible for the team of security agents to determine if there are security threats that require urgent action by the officers or if the team can afford to wait just to ensure that its actions do not go against the law.
Preparedness
The next step is the preparedness. In this case, the team will need to be ready for the action that might be taken by the enemy. In the Middle East, the threat of attack by ISIS and similar terror outfits is real. The problem is that most activities of these terror groups are conducted in foreign countries, especially the unstable regional countries such as Iraq and Syria. The international law limits the ability of the military forces to take action against criminals in another country (Nacos, 2016). Even if the intelligence agencies have gathered intelligence about the plans by ISIS in Syria to attack a city within the United Arab Emirates, this law require the Emirati forces to work with the government of Syria to launch attack against the extremists to avoid having a situation where the Syrian government will consider it an inversion. Sometimes the best course of action is to prepare for a counterattack. With the help of information gathered using these tools, the team will know how to counter such an attack and to ensure that the targeted institutions or places are offered maximum protection.
Response
Dealing with common cases such as an attack by a terror group or local criminal gangs require the use of these emerging technologies. In the 2016, Dallas shooting that targeted white police officers, the team of law enforcement agencies tried to neutralize the attacker, Micah Johnson. The attacker succeeded in bringing down five police officers and wounding many others. The strategic location of the attacker and his military experience made it impossible for the police officers to go after him. A decision was made to use bomb disposal remote control vehicle (Janmohamed, 2017). This unmanned vehicle, fitted with bomb, was able to neutralize the threat without subjecting other officers to the threat of being shot at by the attacker. It was one of the best cases where GEOINT was used to respond to a threat to national security.
Mitigation
It is important to note that sometimes the team may fail to detect a threat until it may be too late to stop it. For instance, some of the homegrown terrorists can blend so well with members of the public that it may not be possible to detect they are planning an attack until the attack actually occurs. Geospatial intelligence can be used in mitigating such cases. With the help of the unmanned vehicles, it is possible to counter an attacker before he or she can cause more harm to innocent citizens. In other cases, these information-gathering tools can be used to identify the specific location of a threat so that the rescue team can help victims to move to safety.
The Growing Popularity of GEOINT in the World
The emerging technologies are becoming critical in managing the national security. Biltgen (2016) notes that not all the new technologies are effective enough to be embraced by the national security systems. Some of them are inventions that can be used in other fields and not on important matters as homeland security. Some of the issues that the law enforcement agencies and military have to deal with on a daily basis are so sensitive that trial and error can never be an option. Any mistake committed by the intelligence agencies, the police, and the department of defense can have devastating consequences. As such, it is advisable to ensure that proper care is taking when embracing new technologies. Before determining how GEOINT can be applied within a given country in the GCC, it is necessary to look at how it has been applied in other parts of the world.
Global application of GEOINT
At a global level, GEOINT has proven to be the tool that can help counter the constant security threats that different countries have to deal with on a regular basis. The United States have a unique security challenge, some of which have been discussed above. However, one area of interest that is yet to be reviewed is border management. According to January (2018), protecting the United States’ border is one of the biggest challenges that security organs in the country have to deal with. The statistics show that the country is still one of the preferred destinations for economic immigrants and asylum seekers (Heather, 2018). It has one of the largest economies in the world and the rate of unemployment in the country is one of the lowest. The minimum wage rate is also one of the highest globally (Nacos, 2016). The healthcare system, the transport sector, and standards of living are some of the best.
The socio-cultural diversity in the country that is brought about by decades of immigration of people from all over the world also make many immigrants comfortable knowing that it is easy to find people they can identify with in the country. Deogawanka (2015) notes that many illegal immigrants, especially from South and Central America often try to pass through the country’s borders to live the American dream. Their mass movement into the country poses a serious security threat to homeland security because it is not easy to determine the true aim intention of such immigrants. The border patrol officers are currently using GEOINT to monitor activities along the border of the country. Using remote sensing and GIS technologies, they can determine when there is a mass movement of people towards the country’s border. The information gathered can help in making the right decision about when to send officers to the border and how the illegal immigrants should be treated based on the potential threat they pose to the country and to the officers at the time of arrest.
Mexico is another North American country that is facing serious security challenges. Smuggling of drugs and weapons are some of the primary challenges that the security forces in the country have to deal with (Heather, 2018). Some of the world’s largest drug cartels operate within the country. These organized armed gangs are very ruthless because of the nature of their business. They resent law enforcement agencies because of the fear that they may be arrested for engaging in illegal trade. As such, they often do not hesitate to kill officers that they view as a threat to their activities.
They also resent fellow drug and weapon traffickers because of the competition in the market. These criminal gangs are also a serious threat to members of the public. Other than recruiting young innocent citizens to help them facilitate transportation of their drugs to the international market, especially in the United States, they also kill people they view as police informants. The government of Mexico has resorted to the use of GEOINT to help in combating these dangerous criminals. The technology helps to locate the area where these gangs organize their activities, their movement to and from their bases, and the kind of people they interact with on a regular basis (Heather, 2018). Using information gathered through GEOINT can help in planning an attack. The officers can know when it is safe to take down their forces and the pattern of attack that would yield the best outcome. The country’s law enforcement agencies believe that using this strategy will help overcome the security challenges in the country.
In Africa, Nigeria is facing a serious challenge of the emergence of a terror group known as Boko Haram. The terror group has been involved in numerous attacks, most of which target innocent citizens who lack the capacity to respond. Biltgen (2016) explains that on April 14, 2014, Boko Haram attacked a government secondary school located in Chibok and kidnapped 276 female students. These underage girls were married off to the Boko Haram soldiers. The group has also been responsible for numerous attacks, often targeting critical infrastructure in the country such as the oil pipelines and the transport sector (Janmohamed, 2017). The government of Nigeria, after conducting feasibility studies, considered it appropriate to use GEOINT to deal with the threat posed by Boko Haram and other similar terror outfits. Although the technology is yet to be rolled out in a large scale, the preliminary studies show that it has a potential of improving the country’s security by identifying the location of terror groups and determining their activities.
Application of GEOINT in MENA region
The use of GEOINT in the region has been motivated by the growing threat of a potential attack by extremist groups such as ISIS and Al Qaeda. Military forces in Afghanistan, Iraq, and Pakistan are known to be using this technology in their regular operations (Asmat, 2012). In Afghanistan and Iraq, the use of this technology has been promoted by the American soldiers working with the government forces (Deogawanka, 2015). They use GEOINT, especially the use of unmanned aerial vehicles to monitor activities of the rebels and terror groups. The information gathered help in planning attack or counterattacks. They are able to know the exact locations of these enemies and the kind of weapons they are using. The technology also helps in determining if the rebels are mingling with civilians to avoid cases where most of the casualties are innocent people who are not involved in the war. Sometimes these soldiers use drones to drop bombs to unsuspecting enemies. The strategy has helped reduce the number of deaths of American soldiers and forces allied to the government in the two countries (Alharith & Samak, 2018). In Pakistan, it has been the initiative of the government to introduce the use of GIS and other remote intelligence gathering techniques to help protect the country from various forms of threats. Data collected from primary sources will help in understanding the ability to apply this technology in dealing with the local security threats.
Clash of civilization
The clash of civilization is a theory, which holds that religious and cultural differences of people are systematically becoming the primary source of conflict in the world (Janmohamed, 2017). In the past, there was always the conflict between countries because of the desire to protect territories and important resources. The emergence of strong international laws limits the ability of foreign nations to invade other countries (Martin, 2015). The case of Russia annexing Crimea from Ukraine was a very rare occurrence that is unlikely to be witnessed in the future. The proponents of this belief argue that Islamic extremism is likely to become one of the major threats to national security (Heather, 2018). Unlike in the past when the main threat to national security was considered those outside the national borders, the current society faces a serious security threat posed by citizens within the country. As people continue to move from one country to another but sticking to their religion and cultural practices, the problem of cultural intolerance is set to become the leading security threat.
Cases where extremists open fire on fellow citizens because of the difference in religion or culture are worrying. Of the 9.2 million people currently living in the United Arab Emirates, 7.8 of them are economic immigrants (Nacos, 2016). It means that the country is just as culturally diversified as the United States. Attacks that target foreigners or people of different faiths have been witnessed in the country. Relevant examples include the women who stabbed an American teacher in Abu Dhabi in 2015 and the man who drove his car into an American runner in Abu Dhabi in 2017. The national security forces should be prepared to deal with this form of threat to the people in the country. Although the focus on border protection should not be ignored, there should be an increased focus on dealing with internal security threats.
Realism
The concept of realism emerged after the French Revolution. It opposed romanticism and instead emphasized the need to portray real situations and people with truth and accuracy without exaggeration, however sordid or unpleasant the reality may be (Janmohamed, 2017). It rejects attempts to make guesses, especially when it is based on stereotypes and personal feelings. Instead, one should be focused on getting the truth based on what is observed under a given setting. This concept is particularly important in the security sector. As the threat to national security continue to evolve over time, law enforcement agencies and the military need to have access to accurate information that can help plan and execute countermeasures in time (Corvaja, Jeraj, & Borghoff, 2016). Having a general assumption that Muslims in Europe and North America are extremists can be a dangerously misleading belief to the national security agencies. Instead, there should be clear measures that can facilitate intelligence gathering to understand the real sources of threat (Heather, 2018). GEOINT offers an important platform of knowing the truth. When used by security agents, accurate and unbiased information will be collected that can be used to enhance national security.
Main Findings of the Review Studies
The studies conducted reveal that GEOINT has great potential in managing national security. According to Landon-Murray (2015), managing security through geospatial intelligence should not ignore the relevance and power of social media. Facebook, WhatsApp, and Twitter have become some of the most powerful tools of communication in modern society. In the past, criminals and terrorists had to meet or make phone calls that could easily be tapped to plan their attacks. However, the emergence of social media has made it easy for criminals to plan and coordinate their activities. Facebook is one of their most preferred platforms of communication. The criminals can coordinate their activities without alerting the authorities. The problem is that security organs cannot intercept such private communication without obtaining a court order (Landon-Murray, 2015). It is not practical for the intelligence agencies to go to court every time they suspect two or more individuals are planning and discussing how to commit a crime through their social media platforms.
One of the strategies that intelligence agencies are currently using is to monitor public posts of individuals suspected to be radicalized. Landon-Murray (2015) argues that posts that show open hatred towards a given group or incitement against the government or a country are often one of the best ways of identifying terrorists. It is at this moment that the use of social media becomes intertwined with GEOINT when gathering intelligence. Once an individual is suspected to be an extremist, the government agencies can monitor their activities using remote sensing technologies to determine if they are planning an attack (Landon-Murray, 2015). Using both GEOINT and social media is motivated by the desire to thwart security threats at the planning stage. The threat posed by terrorists and criminals goes beyond physical activities such as using bombs and heavy weapons. Sometimes these criminals may intend to sabotage government operations by infiltrating some of the security officers trusted with protecting classified information. They may be interested in obtaining the information and passing it on to hostile countries or enemy states (Landon-Murray, 2015). One of the common means of communication that such individuals would prefer using is social media.
The views of the findings made by Landon-Murray (2015) compares with that of Franz, Kane, and Fair (2019), although there are also some differences. Franz et al (2019) focused on the Army and Joint Forces can go beyond the traditional practices to enhance national security and neutralize threats in the United States. The scholars argue that cyberspace is currently the most active, congested, and contested war domain in the world. It has become the main platform for spreading propaganda and selling extremist ideas. Unlike conventional media (newspapers, radio, and television), which have to follow ethical and legal guidelines when disseminating information, social media is unregulated (Franz et al., 2019). Individuals can post anything, and many governments are yet to come up with effective laws and regulations for managing this new threat. After selling negative ideas, especially to the adolescents who can be easily manipulated, these terrorists can convince them to join their criminal groups. The problem is that sometimes even the parents do not realize that their children have started engaging criminals. When they see them spending time on Facebook, they may think that they are chatting with their colleagues (Franz et al., 2019). ISIS used such strategies to recruit teenagers in the United Kingdom, United States, Germany, and other European nations to join them in the Middle East.
It is critical for security organs to understand this paradigm shift when managing national security. The cyberspace is the new frontier when planning to monitor and defeat activities of terrorists. Franz et al. (2019) believe that security agents should be keen on attacking extremist sentiments in social media before a section of the society can be radicalized. Ignoring Facebook posts that attack a given group of people or the state may be a reaffirmation that such arguments are true (Franz et al., 2019). Other than noting such individuals and following their activities closely, security agents should dispel rumors and negative sentiments by reminding members of society of the need to remain patriotic and committed to maintaining law and order. Franz et al. (2019) explain that such plans are lacking in many nations, including the United States. It is not yet clear to the government agencies how they should address numerous negativities in social media.
According to a study by Witt (2015), geospatial data is critical when conducting an investigation, interpretation, and communication of intelligence. However, geospatial resources needed by the intelligence community remain a major issue in many countries around the world. The United States and a few other developed nations have succeeded in developing an effective GEOINT infrastructure that can enable them to collect data from any part of the world. However, most of the countries in the developing world, including those in the Middle East, are yet to have such infrastructure (Witt, 2015). The scholar believes that one of the biggest challenges, why GEOINT is yet to become popular in the many parts of the world, is because of the level of sophistication of the equipment and skills needed. Even if a country is able to purchase the resources, it will still need the support of the United States or Russia to ensure that they can operate the spacecraft and other aerial vehicles used in data collection (Witt, 2015). The problem is that the countries that have this technology are not willing to share it with other countries as one of the ways of enhancing their national security. They believe that it is possible for the enemy to access the technology and use it against their allies. As such, Witt (2015) explains that many countries are yet to embrace the technology.
Knowledge Gap
The effect of geospatial intelligence on homeland security is a relatively new area of knowledge in the field of national security in the UAE. Some scholars have conducted studies to determine its application in North America and parts of Europe. The review of literature pointed out that there is a knowledge gap when it comes to the use of the new technology locally. The researcher noticed that most of these studies view the Middle East as a region where terror groups such as ISIS and Al Qaeda flourish. These scholars have not taken time to investigate the threat that some of the regional countries such as the United Arab Emirates and the Kingdom of Saudi Arabia face from the same group. It is important to note that the UAE has a different socio-political and economic environment from that of the United States. It means that when GEOINT is to be applied in the UAE, it may not be advisable to use the same model as that of the United States. This paper will address the existing research gap by determining how this new technology can be used to enhance security in the UAE and other GCC member states.
Methodology
In the previous chapter, the researcher provided a detailed review of existing literature on this topic. In this chapter, the focus is to discuss the methods used to collect and analyze data. The concept of homeland security is becoming increasingly important in modern society as terrorists embrace sophisticated approach of achieving their goals. In this study, data was collected from two sources. The first source was secondary data. The researcher collected data from books, journal articles, and other reliable online sources that have focused on the issue under investigation. Bernard (2013) notes that it is often necessary to appreciate the work that other scholars have done in a given field. Chapter 2 provided a detailed review of the information obtained from the secondary data sources. The second source of data came from primary sources. The concepts of geospatial intelligence and homeland security are relatively new. As such, collecting primary data is importance in enhancing knowledge about the topic. Moreover, given that the investigation focused on the application of this new technology in enhancing security in the United Arab Emirates, it was necessary to collect data locally within the country. In this chapter, the goal is to discuss how primary data was collected from sampled respondents and analyzed.
Research Philosophy
One of the first steps that a researcher should take is to define the appropriate research philosophy that should be used in the study. Research philosophy, according to Card (2016), refers to the basic beliefs and assumptions that must be embraced in the study. In natural science, it is possible for a researcher to manipulate specimen in a laboratory setting to suit specific conditions. However, that is not always the case when conducting a social sciences research where the primary focus is on people. A researcher cannot control the behavioral patterns of the people being investigated (Kersten, Blecker, & Ringle, 2014). As such, it is often necessary to make specific assumptions and hold certain beliefs to guide in the entire process of collecting and analyzing data. As shown in figure 5 below, one can choose to use positivism, realism, interpretivism, or pragmatism depending on the goal of the study. Each of these philosophies has basic principles, which made it appropriate to select only one of them to guide the study.
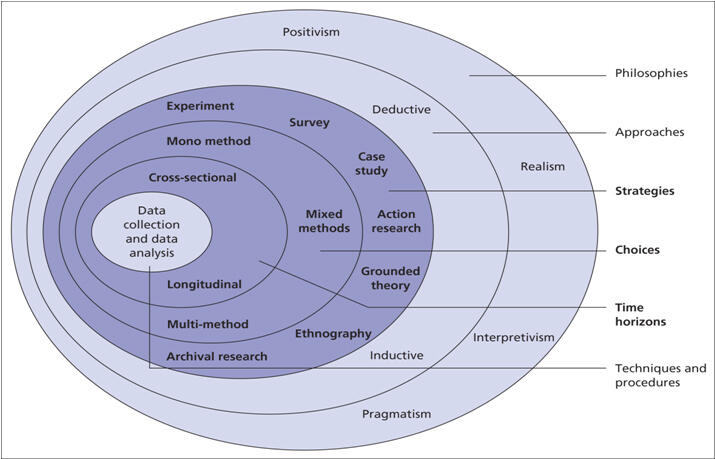
Pragmatism research philosophy
National security is a sensitive issue and any study that focuses on it should be based on facts. As discussed above, there are four different philosophies, each with its unique characteristics (Adams, Khan, & Raeside, 2014). The researcher considered pragmatism the most appropriate philosophy based on what was to be investigated in the study. It holds the view that a concept is true only if it supports action. “Pragmatism as a research philosophy recognizes that there are different ways of interpreting the world and undertaking research, and that no single point of view can give the entire picture” (Patten and Newhart, 2018: p. 56).
The scholar argues that in some cases an issue may be interpreted from various perspectives depending on the goal that needs to be realized. This philosophy allows a researcher to take different approach of investigating an issue as long as the outcome is realistic and supports an action. When using it, a researcher can opt to use qualitative, quantitative or both methods of study. When investigating the effect of geospatial intelligence on homeland security, it is necessary to use both qualitative and quantitative methods. The flexibility of this philosophy means that it allows a researcher to take different approaches of investigating the issue under consideration. It is important to note that just like positivism; this philosophy limits the work of a researcher to that of data collection, analysis, and interpretation. A researcher is not expected to be part of the subject as he or she may influence the outcome of the study.
The researcher believed that this was an appropriate philosophy in this study because it limits the role of the researcher to that of data collection, analysis, and interpretation. When investigating issues relating to national security, Mackey and Gass (2016),) warn that a researcher should avoid personal opinions that may have negative outcome on the study. Instead, the focus should be on facts gathered proactively from reliable sources.
Research Approach
When the appropriate research philosophy has been identified, the next step is to determine the approach that should be embraced in the study. Mackey and Gass (2016) argue that the selected approach should be in line with the philosophy selected. Research approach refers to “a plan and procedure that consists of the steps of broad assumptions to detailed method of data collection, analysis, and interpretation” (Patten and Newhart, 2018: p. 83). It is often defined by the nature of the research problem that a study seeks to address. One can use inductive, abductive, or deductive reasoning approach. The researcher considered inducting reasoning as the appropriate approach for the study.
Inductive reasoning
The researcher was interested in selecting the approach that was in line with the selected philosophy. Given that this was a qualitative research, inducting reasoning provided the best method of developing knowledge based on its principles. In this approach, a researcher is expected to start by making observations or conducting tests. It may not be necessary in this case to develop a hypothesis or to base the argument of the study on a specific theory. Instead, the researcher should be as open-minded as possible from the onset of the investigation. The observations or tests will make it possible for the researcher to develop a pattern. The pattern should not be based on a researcher’s personal opinion but real facts gathered from the study. The final stage is to develop a theory based on the pattern developed. According to Mackey and Gass (2016), sometimes this approach of reasoning is referred to as bottom-up approach because it is based on the use of observation to describe a given phenomenon. Figure 6 below shows the pattern of reasoning when using this research approach. It was not considered appropriate for the study because of the desire to developed hypotheses, which had to be confirmed or rejected as discussed in the previous chapter.
During the process of conducting this study, the researcher started by reviewing literature related to the use of geospatial intelligence in national security management (McNabb, 2015). The primary data were collected using open-ended questions as Mackey and Gass (2016). As shown in the figure above, observation is the initial stage of developing knowledge when using this approach. The researcher identified individuals who are knowledgeable and experienced enough to provide credible and reliable information relating to geospatial intelligence and its relevance in national security management. The use of unstructured questions was critical in allowing the participants to provide a detailed explanation to each of the questions (Brennen, 2017; Brennen, 2017). Instead of providing a rigid pattern of answering questions in the study, the respondents were allowed the opportunity of using their own words to explain their experience and views relating to the issue under investigation (Walter & Andersen, 2016). In exploratory studies, it is important to allow participants to provide a detailed explanation of their views over a given issue (Sappleton, 2013). The pattern was determined based on the responses provided by the participants.
Research Strategy
Research strategy is a systematic plan of action that defines how primary data will be collected from various sources (Mackey & Gass, 2016). After defining the philosophy and approach necessary for the paper, the next step is to determine the appropriate strategy. Research strategy that is chosen should be based on different factors such as availability of time, the ease with which the respondents can be reached, and their geographical distribution. McNabb (2015) states that the selected strategy should make it possible to collect the needed information within the time available for the study. The following strategies were used to collect primary data.
Questionnaire and Interviews
According to Patten and Newhart (2018), one of the best ways of collecting primary data is through interview. In this strategy, a researcher organizes a meeting with participants who are then engaged in a question-answer forum. The use of geospatial intelligence in enhancing homeland security is a relatively new strategy. The local law enforcement agencies and the defense forces find it critical to use these emerging technologies to ensure that local criminals and international terrorists do not compromise the country’s security. The interview will focus on two groups of people. The first group will be the local law-enforcement agencies who are responsible for maintaining law and order. These officers have to deal with local threats, especially the criminal gangs and homegrown terrorists who may want to harm people or destroy their properties. The researcher will also seek audience with local security experts, especially the scholars who specialize in national security and disaster management. They will all be asked the same questions in the same order. The interview will be conducted in two different ways as discussed below.
The researcher identified a team of respondents whose schedule can allow them to participate in a face-to-face interview. An arrangement was made to ensure that the meeting is convenient both to the researcher and to each of the participants. Most of the meetings were held in the offices of the respondents. They were informed about the date and be reminded a few hours before the interview to ensure that they are prepared. McNabb (2015) argues that face-to-face interview is one of the best ways of collecting primary data. The physical meeting between the interviewer and the interviewee reemphasizes the importance of the study. It increases the chances that all questions will be answered within the right time. An interviewer is able to use facial expression and body language to determine the validity of the response given. In most of the cases, people will avoid facial contact when trying to lie (Mackey & Gass, 2016). They will also take time before responding to a given question because they have to create the lie. On the other hand, truthful answers do not need thinking, especially when the question requires a simple response. The approach may be time-consuming, but it is a very effective method of collecting data from respondents.
The tight schedule of some of the respondents made it impossible to have a face-to-face interview. Nevertheless, their willingness to participate in the study made it necessary to organize phone interviews. Mackey and Gass (2016) argue that although phone interviews may not be as effective as face-to-face interviews when it comes to gathering additional information through facial expression and body language, it is also another good strategy of primary data collection. Using this strategy, the researcher identified these participants and identified a date when each would be available for the phone interviews. Most of the phone interviews were conducted in the evening, when the participants had completed their shift, based on their request. Both forms of interview were conducted with the help of a questionnaire that had been developed purposefully for this study.
Data Collection Approach
When using interviews or surveys as a method of collecting data, it is important to develop a clear action plan of the activities that should be taken. McNabb (2015) explains that the approach taken often determines if the process of collecting data is successful or not. One of the most important steps that should be taken is to develop an appropriate instrument of data collection. The instrument will ensure that data collection is standardized. It is necessary to discuss the structure of the instrument used to collect data in this study.
Instruments of data collection
It was necessary to have a standard format of answering the research questions in this study because of various reasons. First, given that one of the strategies used in data analysis required statistical methods, it was crucial to have a standardized approach of collecting data. It made it possible to code the answers for the purpose of analysis. Secondly, having a standard format of answering these questions made it possible to determine the varying opinions of the respondents on different issues relating to the research topic. As such, it was necessary to develop a questionnaire to help in the process of collecting primary data. The questionnaire had three sections as discussed below:
- The first section of the document focused on the background and demographic information of the respondents. The section focused on determining the age, gender, and nationality of the participants. Mackey and Gass (2016) argue that there are cases where demographical factors such as gender and age of an individual influence the pattern in which he or she answers specific questions, especially if the issue may elicit varied opinion. In other cases, may be possible to have a skewed data specifically influenced by a person’s age or other demographical factors. As such, generalization when answering some questions could be captured in the demographical space, as Brennen (2017) notes.
- The second part of the questionnaire dealt with academic qualifications and experiences of the participants. People with varying levels of academic background often reason differently, especially when the question asked allows them to use their own words. Similarly, experience that one gains affects their level of knowledge on a given field, and as such, one is likely to respond based on issues they have encountered in life. These factors made it necessary to capture these characteristics in this section. The last part of the questionnaire focused on specific questions the effect of geospatial intelligence on homeland security in the context of the United Arab Emirates. The questionnaire employed both closed and open-ended questions as a way of capturing data in the most comprehensive manner possible. It was necessary because the research used both qualitative and quantitative methods. The document was used to facilitate the interview. This document is attached at the appendix of this thesis.
Sampling and sample size
The issue of homeland security is in the domain of the country’s armed forces and the law enforcement agencies. It is possible to collect data from a wide number of participants. However, because of the sensitivity of the topic and the limited time available for data collection, it was necessary to develop a small manageable sample of people to participate in the data collection. Purposive sampling, which sometimes referred to as subjective, judgmental, or selective sampling, was considered the appropriate method of selecting participants for the study (Mackey & Gass, 2016). According to Patten and Newhart (2018), “purposive sample is a non-probability sample that is selected based on characteristics of a population and the objective of the study,” (p. 45). The sample must meet specific criteria to qualify for the study. In this context, participants had to be drawn from security experts who have knowledge about geospatial intelligence and its relevance in enhancing national security in the country. They must have worked in specific security agencies involved with intelligence and counterintelligence gathering for at least five years.
Random sampling would not be appropriate because it would lead to a selection of individuals who lack the needed knowledge. As explained above, matters relating to national security are very sensitive and as such, the information had to be as accurate as possible. When selecting individuals to participate in this study, the researcher asked them about their academic qualification and experience in various security dockets. Only those who met the set criteria were selected to be part of the study. As Patten and Newhart (2018) suggest, it is more advisable to have a small number of highly knowledgeable participants than a large group of individuals who have a limited understanding of the issue being investigated. The sample had to be classified into two groups. The first group included individuals working in law enforcement agencies and the country’s defense department. Those who were selected had been actively involved in intelligence gathering both domestically and at the international level. The second group was a team of experts who can help shed more light on this issue without the fear of revealing classified information. They include security experts who are in private practice and those who are working in institutions of higher learning. The researcher selected 40 individuals to participate in the process of primary data collection. Figures below show the demographic information and experience of the participants.
Data Analysis
When primary data has been collected from the field, the next important step is to conduct an analysis. Selecting an appropriate method of analyzing primary data is critical, as McNabb (2015) advises. The method should enable a researcher to achieve aim and objectives of the study. The primary goal of this research was to determine the effect of geospatial intelligence on homeland security in the United Arab Emirates. To achieve this goal, it was necessary to go beyond statistical analysis of data. As such, qualitative analysis was considered most appropriate for the project. Brennen (2017) defines qualitative data analysis as “the process of examining qualitative data to derive an explanation for a specific phenomenon” (p. 67). It focuses on the experiences of the participants to identify specific themes in a given study. When investigating the impact of geospatial intelligence on national security within the country, it was necessary to use open-ended questions that allowed participants to explain their views in their own words. It means that they were not restricted to specific choices when responding to specific questions. Phenomenology makes it possible to create themes that would help to understand the issue under investigation. The detailed explanation provided by the participants about various issues relating to geospatial intelligence and national security of the country made it possible to achieve aim and objective of the study.
Research Ethics
When conducting an academic research, it is important to observe various ethical considerations. One of the most important ethical requirements is to seek for permission when collecting data from employees of a given organization. In this case, it was necessary to engage a few officers from security organs. In the disciplined forces, respect for the authority is often unquestionable. Before a junior officer can offer to share information with a researcher, senior officers must grant proper permission. Moreover, the issue of security is so sensitive that the government may classify some information to ensure that intelligence meant to protect the country is not leaked to the targets. As such, the researcher had to make an official request to the officers commanding stations where the targeted officers work. Individual officers were contacted only after getting the approval of the senior officers.
It was the duty of the interviewer to explain the need for the study to the respondents. McNabb (2015) explains that before an individual can set aside some time to answer research questions, he or she should be convinced about the relevance of the study. The interviewer explained to them the goal of this study and the role they needed to play in ensuring that it was a success. Participation in the data collection process was voluntary. The respondents were reminded that they had the liberty to withdraw from the study at any time as long as they felt uncomfortable or had other pressing issues that could not wait. Withdrawal from the study would not be subject to any consequences.
Hiding the identity of the respondents was another critical issue that had to be observed in this study. According to Patten and Newhart (2018), intolerance is still a major issue in many societies across the world. Sometimes people are victimized because their views are not same as that of the majority. In some extreme cases, one may be subjected to physical attacks or economic sanctions because of their opinion. In the security sector, it is often expected that junior officers follow the instruction of their commanders. A junior officer having divergent views from that of the senior commanders may have serious consequences. As such, one of the most important ethical requirements was to hide the identity of the respondents. Instead of using their actual names, a unique identity based on numbers was used. It was impossible for one to trace a specific officer based on their names. The strategy was meant to shield the respondents from any form of victimization because of their divergent opinion.
It was also necessary to follow all the university rules and regulations when conducting this project. Mackey and Gass (2016) argue that institutions of higher learning have strict policies that must be observed by students when conducting research. One such rule is the need to avoid plagiarism. It is unethical for one to present the work of another person as his or her own. In this regard, the researcher was keen on avoiding any form of plagiarism. Information obtained from the works of other scholars was references accordingly using American Psychological Association (APA) format. A list of all the sources used was provided in the reference section of the paper. It was also an ethical requirement to ensure that the study is completed within time stipulated by the university.
Research Constraints
When conducting the study, a few constraints were encountered which are worth noting at this stage of the research. One of the major constraints encountered was the inability to have a large pool of participants to help in the collection of primary data. The sensitivity of the topic and the fact that members of the disciplined forces had to be involved complicated the process of data collection. Others would promise that they would take part in the investigations only to withdraw in the final hours of the interview. Despite the challenge, the researcher was able to identify enough people to be part of the study. Time was a minor issue that posed a challenge. Data had to be collected from both primary and secondary sources, processes, and the thesis written within the deadline. It was a challenge that the researcher was able to overcome.
Case Study
Sometimes it may be necessary to use case studies in a given project. Patten and Newhart (2018) explain that the use of case studies is particularly appropriate when trying to understand how a given concept can be applied in a specific setting. In this case, the focus was to determine how the concept of geospatial intelligence could be used to enhance homeland security in the United Arab Emirates. This concept has been applied in the United States and it is proving to be one of the most important inventions in the field of security setting. However, its application is yet to be fully embraced by most of the developing nations. It will be possible to understand how some nations have used this concept. It will then be possible to explain how it can be applied within the local setting. The difference in socio-economic and political environments in these countries may make it necessary to make some modification to this security concept to ensure that it suits the country.
Findings and Discussion
In the previous chapter, a detailed description of the method used to collect and analyze primary data was provided. In this chapter, the researcher presents the findings made from the primary data analysis. When reviewing literature, knowledge gaps were identified that needed to be addressed through collection and analysis of primary data. It was established that although the concept of geospatial intelligence and its relevance in homeland security is relatively new, scholars in North America and Europe have tried to explain its application in the western countries. Conversely, information about the same in the Middle East and especially in the United Arab Emirates is scanty. It is an indication that research is needed to explain how this concept can be used by the local intelligence forces to deal with the problem of insecurity in the region.
Research Questions
It was important to start the analysis of primary data by responding to questions presented to the respondents in the questionnaire. The questions focused on determining the level of security in the region, and the manner in which government agencies can use GEOINT to address security concerns, especially because of the increasing instability in the region.
Following the events of the Arab Spring, do you believe that security has become a major concern than before in the GCC region? Kindly explains.
This question focused on determining the impact of the Arab Spring on the security of the country and its neighbors in the region. Participants were requested to explain their views based on their knowledge and experience on issues relating to national security.
Participant 4 said, “Some of the countries within the MENA region such as Libya, Syria, and Yemen have completely been destroyed by the Arab Spring. Egypt and Sudan are struggling to maintain security because of political instability. For that matter, I believe that security has become a major concern in the GCC region than it was the case before.”
The concern was shared by many participants that the researcher interviewed who believe that the region has never witnessed such an extensive political instability in its modern history. They believe that the events of the Arab Spring have created a belief that the masses can easily dismiss a government if they feel unsatisfied.
Participant 11 said, “Even if the United Arab Emirates remains politically stable, the instability of some of its neighbors is a major security concern. The country has to receive refugees, some of which are criminal elements.
The security concern means that the region has to be adequately prepared to address the threat.
What is the level of threat that the United Arab Emirates is facing from terror groups within the region?
This question focused on determining the level of threat that the country faces from local and regional extremists. These security experts are in the best position to provide such information.
Respondent 3 said, “Although the country has not experienced a major terror attack in the recent past, extremists such as ISIS and al Qaeda have the potential to attack.”
Respondent 16 said, “I believe the threat is real, and that these extremists are waiting for a perfect opportunity to strike.”
Security organs in this country need to be alert because most of the respondents expressed their concern about the possibility of an attack.
What is the relationship between geospatial intelligence and homeland security? Provide a short explanation.
The question focused on determining whether the participants understood the relevance of geospatial intelligence in managing homeland security.
Participant 1 said, “Geospatial intelligence creates an opportunity for the security organs to collect aerial surveys and collect data relevant in enhancing homeland security.”
It is important to note that although the majority of these participants know about GEOINT, the majority of them have not had the opportunity to use it.
Participant 19 said, “I believe GEOINT is critical in managing homeland security, although I have not used it.
For the countries that have embraced the use of geospatial intelligence, do you believe they have improved security than was the case before its introduction? Kindly explain.
Some of the participants were security experts who have conducted studies about the application of GEOINT in various countries. It was necessary to know if this technology is working in other countries.
Respondent 6 said, “The United States has thwarted several attempts by criminals to cross its borders illegally because of data collected using GEOINT.”
The researcher determined that the majority of participants share the view that developed countries are using GEOINT to enhance their own security.
How effective is geospatial intelligence in fighting emerging threats to homeland security in the country?
The question focused directly on determining the relevance of this new technology in managing the country’s security.
Respondent 2 said, “GEOINT is rapidly becoming the most effective tools in managing homeland security. It makes it possible to collect information about the physical activities of criminal elements.”
The majority of the participants felt that GEOINT offers a perfect opportunity for various security agencies to deal with different threats.
How ready is GCC in terms of embracing GEOINT as a way of combatting the emerging threats to homeland security?
The question focused on determining how well regional governments have considered embracing this new technology as a means of enhancing national security.
Respondent 7 said, “The region is keen on embracing the new technology but they lack the capacity to do so.”
Respondent 11 said, “Regional security agents still lack the capacity to use advanced GEOINT technology although they appreciate its relevance in modern society.
As Landon-Murray (2016) observes, using GEOINT requires a team of highly skilled officers who knows how to interpret aerial information collected using remote sensing technology. Such skills are still lacking in many countries.
What is the level of investment that the country has made to promote the use of technology to gather intelligence?
The question focused on determining whether the country has made the necessary investment in this field.
Respondent 13 said, “The country has invested heavily on enhancing technology in intelligence gathering. However, enough is yet to be invested in GEOINT.”
Respondent 19 said, “The government has been relying on intelligence from the United Nation and its allies, and is yet to make a proper investment in GEOINT.”
The majority of those who were interviewed felt that the government has not made a significant investment in this sector because of its reliance on its allies when it comes to gathering geospatial intelligence.
How effective are the local law enforcement agencies in terms of using the technology to gather the intelligence necessary to keep the country safe?
The ability of the local security agencies to use modern technologies in collecting intelligence is critical at a time when the country is considering to embrace GEOINT.
Respondent 20 said, “The local security organs have been trained to use emerging technologies to collect, process, and share intelligence in an effort to enhance national security.”
A significant majority of the respondents shared the same view about the capacity of the local law enforcement agencies to use modern technology to fight crime. They have registered impressive success in fighting cybercrime and they can also use the same approach to fight terrorism.
Is there a will on the part of the government to create capacity within the armed forces to enhance the use of GEOINT in managing security?
The ability of the country to embrace GEOINT technologies in managing security depends on the will on the side of the government. The researcher wanted to know whether the government has expressed its genuine interest in this new concept.
Participant 24 said, “The government has made an effort to embrace this technology by working closely with the United States as a way of learning new intelligence management practices.
Participant 17 said, “It is not easy to determine if the government has a genuine will to embrace this new technology.”
Some respondents felt that the government has the will to embrace the new technology. However, others were skeptical, stating that sometimes it is almost impossible to know exactly what the government intends to do.
What are some of the issues that affect the effective application of emerging technologies, especially the use of GEOINT, in managing the country’s security?
The researcher was interested in determining the main impediments to the use of the new technology in the country.
Respondent 18 said, “Limited skills and experience among the local agents is the main impediment in the effort to introduce GEOINT in the country.”
The majority of the respondents shared the same view about the limited knowledge and experience of officers in the country.
Respondent 29 said, “One of the main issues facing the local authorities is that the technology is new and many people still do not understand how it should be applied.”
What are some of the challenges that the country is likely to face when using GEOINT to enhance the country’s homeland security?
In case the country introduces GEOINT in its security management system, it may face some challenges. The participants identified some of these challenges.
“Respondent 39 said, “The biggest challenge would be to train the local forces so that they can understand how to gather, interpret, and use geospatial intelligence. It may be necessary to send them to foreign schools.”
Respondent 21 said, “One of the main issues would be financing. The government would be forced to spend a significant amount of money to acquire new technology.”
What do you believe will be the reaction of other regional countries when the UAE starts to embrace GEOINT to enhance national security?
It would be expected that some of the neighboring countries would react when the country embraces the new technology. It was necessary to determine the view of the respondents on this issue.
Participant 13 said, “It is likely that some of the neighbors would be interested in embracing the same technology to bolster regional security.”
Respondent 8 said, “Some of the hostile nations in the region may feel threatened by the new technology and would want to upgrade their own systems.”
The respondents felt that regional countries would react in different ways when they realize that the UAE has embraced the new technology.
What is the danger to the country if other neighboring countries adopt this new method of managing homeland security?
The researcher was interested in determining if the UAE would be affected in case some of its neighbors embrace GEOINT.
Respondent 5 said, “Some hostile states may use the technology to spy on the country without the knowledge of the local intelligence agencies.”
Respondent 32 said, “When neighboring countries embrace the technology ahead of the UAE, they will have superior intelligence and counterintelligence power to that of the country.”
The respondents felt that the country’s intelligence agencies would become inferior to that of its neighbors if it fails to introduce this technology early enough.
What do you believe the government should do (that it is currently not doing) to ensure that it promotes the use of GEOINT as a way of enhancing homeland security?
The question focused on determining what the UAE government should do to promote the use of GEOINT in maintaining homeland security.
Respondent 2 said, “The government needs to spend more on training its security agents in this new technology.”
Respondent 10 said, “The government should work closely with the United States to enhance its technological capacity in security management.”
Training of the local forces and working closely with countries such as the United States were identified as some of the best ways of enhancing the use of GEOINT in the country.
Security Threats in GCC
One of the first issues that had to be determined from the sampled participants was their view about security in the region. The use of geospatial intelligence to deal with security concerns requires a significant investment. The investment would only be justifiable if the region faces unique security challenges that cannot be fought using traditional methods. Given that the participants involved in the study were security experts working within the region, they have first-hand experience about the real nature of security threat in the region. When asked whether the region is facing a more complex security problem than was the case a few decades ago, figure 8 below shows their response:
The participants stated that indeed the region is facing new security threats that did not exist in the past. Majority of the participants (12 out of 20) stated that they agree with the statement that the region is currently facing unique security challenges that may require sophisticated methods to manage. Six participants stated that they agree with the statement that the region is facing bigger security problems. One person was not sure about the issue while another disagrees with the idea that the region has to deal with greater security problem. Before determining how the region can use geospatial intelligence to enhance homeland security, it was necessary to identify security threats that regional states face. The respondents were asked to identify and explain some of the threats to regional security based on their security knowledge and experience.
Terrorist groups
When asked to explain the nature of threat that the region faces, Respondent 4 said, “Terrorist groups such as Al Qaeda and ISIL poses serious security threats in the region.”
This sentiment was shared by most of the participants interviewed in this study. They stated that the strength of ISIL and similar terror groups is a major security problem in the region. ISIL has taken a unique approach in its operations. Instead of operating as an underground terror outfit, it takes control of regions where weak governments cannot control. For instance, it is thriving in Syria, Iraq, and Yemen, which are affected by civil wars. It means that it is not possible for the affected country to lodge formal complaint with the host government about the terror activities of ISIL in the region. ISIL is also more sophisticated in its operations by integrating civilians in its operations. It is almost impossible to launch a successful military attack on this group of terrorists without putting lives of civilians, especially women and children, at risk. Another major challenge that the participants noted was that the group has sustained economic activities. In these unstable states, they have taken control of some of the oil fields. They allow corporates to exploit these resources and charge them tax before the products can be sold in the international markets. It means that they have the needed revenue flow to facilitate the terror activities. One of those interviewed (Respondent 6) stated:
“ISIL poses a serious security threat in the GCC region because it is not easy to determine when they will strike.”
On January 29, 2016, ISIL executed an attack on Al Ridha mosque in Mahasin District, Saudi Arabia (Biltgen, 2016). The attacker was a suicide bomber who targeted Shi’a mosque. Four people were killed while eighteen others sustained varying injuries. It was not the first attack that was planned and executed in the country. In most of the cases, they strike when it is least expected. The fact that they always target soft-spots (mostly the civilians unable to defend themselves) makes them very dangerous. ISIL has attacked several other countries in the GCC including Saudi Arabia and Bahrain. Its financial strength makes it easy to recruit fighters all over the world. The United Arab Emirates has not suffered a direct hit from this terror group. However, that does not mean the country is safe. In case its foreign policies go against the beliefs of ISIL, this terror group would not hesitate to strike. As such, the country must be ready to deal with such threats. Al Qaeda is another security challenge that the region cannot ignore. Although most of its top commanders have been killed and others imprisoned, the group is still active and poses potential threat to the country’s homeland security, especially with the rise of Hamza Bin Laden as his father’s successor and emerging leader of Al Qaeda.
The Arab Spring
The participants feel that the Arab Spring that started in North Africa and swept through to the Middle East has had serious repercussions on the regional security. Given that some of these individuals have the responsibility of maintaining law and order, the idea of dealing with a civilian revolution is a nightmare. Although the United Arab Emirates was not directly affected by the wave to the extent that the country needed to use its military forces to suppress the rebellion, it was a major security scare. In countries such as Tunisia, Egypt, and Libya where the leaders were toppled, there were devastating political and socio-economic consequences. Libya has never known peace since the military rule, Colonel Muammar Gaddafi, was killed in the revolution. The consequences of the Arab Spring have been felt in the entire region in different ways.
Refugees
Respondent 17 said, “The United Arab Emirates has been forced to host thousands of refugees fleeing countries like Yemen and Syria because of the Arab Spring.”
The problem is that handling such a large number of undocumented people strains security instruments. It is in the interest of the government to ensure that the refugees are offered shelter within a specific region before a decision can be made to integrate them into the country’s workforce, if that would be necessary. The security officers have to enforce the law when handling these immigrants. Another respondent noted that some of these immigrants are extremists disguised as refugees. Respondent 11 said, “The Arab Spring has led to serious security problems in the region because some extremists are posing as refugees to find easy entry into their targeted countries.”
Such terrorists find their way to the country with the primary goal of attacking the locals because of the doctrines they have come to embrace. According to Chaliand and Blin (2016), such incidents have been witnessed in Europe. Germany was one of the European nations that embraced the open-door policy when dealing with the problem of refugees. It made it possible for most of the refugees to seek asylum in the country. Unfortunately, some of them were part of the ISIL keen on exporting terrorism to Europe. The country has suffered several ISIL attacks since 2014, and most of the perpetrators were individuals who were taken in as refugees. This means that the United Arab Emirates may not be safe having such a large number of refugees into the country.
State-sponsored attacks
The United Arab Emirates has been involved in regional military activities to help restore peace and stability. Its army joined forces with the Saudi Arabian army to fight Houthi rebels who had taken over the leadership of Yemen militarily after overthrowing the democratically elected leader. In response, the Houthi rebels, backed by the Iranian government, issued a warning that it intended to retaliate against regional powers that had participated in the attack. One of their prime targets has always been the United Arab Emirates.
In July 2018, the Iranian government stated that it had enabled the Houthi rebels to launch a drone attack at Abu Dhabi International Airport as a way of fighting back against the country’s involvement in the local Yemeni political leadership (Ahmad, 2018). The group also made another claim that the Dubai International Airport, which is currently one of the busiest airports in the world, is a major target of attack. Although some of the claims are not true, especially the magnitude of the attack, the government of the UAE acknowledged that a minor incident was noted at the Abu Dhabi Airport and it was addressed without causing a scare. It is a clear demonstration that there is intent to attack. Respondents stated that the threat of state-sponsored attack is a real security concern.
Respondent 1 said, “The idea that another state can sponsor rebels such as Houthi to plan and execute an armed attack in the country is a major cause of concern to the security services.”
An attack by a state-sponsored terrorist group may have devastating consequences on this country. In fact, Brown (2015) notes that such attacks are often worse than acts of crime. Such rebels have the support of the government when planning and executing the attack. They can access all the materials needed at every stage of the plan, including intelligence. Iran is one of the countries in the region pursuing the development of nuclear weapons. If the government has openly supported an armed attack by the rebels against the United Arab Emirates, it means that it can facilitate the use of nuclear weapons. It is a major security concern for the security organs. The traditional approaches of managing the country’s security cannot be relied upon any more to ensure that the country is safe from any potential attack.
Crime
The region is also facing a problem of terrorists using various techniques to achieve their goals. The respondents noted that cybercriminals are currently targeting financial institutions and other corporations to damage the UAE. The statistics show that financial institutions in the region are losing millions of dollars every year to these techno-savvy criminals. Some of these criminals are now targeting government security organs to enable them to traffic drugs and other contraband goods. They tap into the security systems of the country to determine the security plans of the country and manner in which it can be manipulated to make it possible to evade the security system. There is a growing fear that the security at the country’s airport may be jeopardized if such criminals are allowed to operate in the region.
Respondent 3 said, “Some of the terrorists, especially the drug cartels and human trafficking syndicates, have developed unique ways of outsmarting the local security systems.”
Some of them use surgical methods and ingestion of hard drugs to evade security. The respondents explained that some of these cartels are ruthless and have a well-established military wing. They offer money to the security officials and airport employees responsible for conducting the search. If these officials fail to accept the financial benefits offered to them, then they become targets of these syndicates. Ganor (2015) argues that failing to deal with these drug and human trafficking cartels may put to risk the life of airport officials. Some of these criminals go an extra mile to target family members of such officials. Many officers often give in because of the fear of the consequences.
Using Geospatial Intelligence to Manage Security Threats
The sophistication of the modern-day crime makes it necessary to embrace new technologies to deal with them. Whether the security organs are dealing with state-sponsored terrorists, or organized criminal groups, using emerging technologies may be critical dealing with the problem. It also reduces the risk that security officials face when protecting lives and property in the country (Chaliand & Blin, 2016).
It was necessary to determine the views of the respondents over this issue. They were asked whether they believe there is a relationship between geospatial intelligence and homeland security. Figure 9 below shows the outcome of the analysis of their response.
The figure above shows that the majority of the participants believe there is a close relationship between the use of geospatial intelligence and increased homeland security. The statistics show that 18 out of 20 respondents stated that there is a relationship between the two. Only two of the participants stated that the relationship does not exist. The two argued that emerging technologies have complicated the ability of the country to manage homeland security. Answering the primary research question about the manner in which geospatial intelligence can be applied to support homeland security needed the respondents to determine if there is a relationship between the two. Therefore, an open question was asked.
How can geospatial intelligence be applied to support homeland security in the GCC?
The participants strongly believe that geospatial intelligence offers a proper solution to the growing problem of insecurity in the GCC region, especially in the United Arab Emirates. The next step was to identify specific areas that geospatial intelligence can be applied within the security system to ensure that various threats are neutralized as soon as they are detected. The respondents identified three main areas where this new technology can be of great importance in managing various security threats identified above. They are the following:
Intelligence gathering
The law enforcement agencies and the country’s military need to gather intelligence with regard to attack planning and to prepare counter attack. When dealing with state-sponsored terror group, it may not be easy to predict when they are planning to strike and the magnitude of a possible attack. The Iranian government recently announced that it had facilitated Houthi rebels to attack local Emirati airports using drones because of the country’s foreign policies. The country’s armed forces have the responsibility of protecting citizens and property from death and destruction arising from such an attack. When dealing with such a powerful enemy, the country cannot afford to be reactive in response to the threat. It has to take proactive measures to ensure that the threat is neutralized before it can affect the people. In this case, it will be necessary to gather intelligence ahead of time that is relevant to the nature of the threat. Respondent 9 said, “The country’s intelligence agencies need to know about activities of the enemy and be able to predict when they are planning an attack.”
The current sources of information used by the country’s intelligence agency ma not allow for collecting all intelligence needed. Geospatial intelligence could be a very valuable addition. Respondent 12 said, “Using drones or GIS, it is possible to monitor ground activities of the enemy to determine if it is planning an attack.”
Without risking lives of the officers or agents in the field, drones can be used to collect the needed information, especially when dealing with terror groups such as Houthi and ISIL. Drones, fitted with powerful cameras, can help monitor the movement of the members. The technology will inform the agency about the size of the terror group in terms of active soldiers, the type of weapons they are using, the means of transport, and the specific geographic location where they are concentrated. One of the emerging trends that these terrorists use is suicide bombing. Some of them go as far as planting bombs on women and children who many do not view as a source of threat. Using this technology, security officers are able to determine when a person from such a terror outfit is mingling when the public. An immediate action can be taken to arrest such an individual before he or she can walk into populated areas with explosives. Respondent 4 said, “Geospatial intelligence is particularly important when managing strategic economic zones such as the international airports.”
The UAE General Civil Aviation Authority has come up with various measures that help in ensuring that no one can smuggle explosives into local airports. However, such measures cannot protect the country from aerial attacks such as the one that Iran and its allies may be planning to use against the country. It is necessary to use the new technologies to deal with this new threat. GEOINT will make it possible for the aviation authority, working closely with relevant security agencies, to monitor the airspace for any aerial threat. If it is established that a rocket has been launched or a drone is being used to deliver a bomb, proactive measures should be taken to deal with the threat before it reaches its target. The technology can also help in gathering intelligence about drug cartels and other criminal groups operating within the region.
Planning
GEOINT can play a critical role in security planning. According to Janmohamed (2017), when faced with a serious security threat, the local law enforcement agencies and the defense department may need to come up with a plan of dealing with the threat. Houthi, ISIL, Al Qaeda and Iran are some of the leading security threats in the region. The United Nations Charter Chapter VII, Article 51 gives every country an express permission to use force against any armed attack (Said, 2015). Unfortunately, that power is only granted if the country attacked has a clear proof of the armed aggression. Using GEOINT, the UAE, working closely with regional allies such as Saudi Arabia, can monitor the activities of the enemy and come up with a proactive plan on how to respond to a threat proactively. When the intelligence gathered confirmed a plan or an attempt by the enemy to launch an attack, the country’s armed forces will have a clear plan on how to respond to protect lives and property. Respondent 13 said, “The country needs to collect the most recent information of the activities and plans of the enemy to come up with its own counterplan to deal with the regional threat.”
In combat
Technologies in geospatial intelligence can be used in combat when necessary. The open admission of Iranian government and Houthi rebels that they launched an armed attack against the United Arab Emirates is a proper justification for the country to fight back to protect its territory. Instead of sending fighter jets to the rebel-held regions in Yemen, the country can use drones. These unmanned aerial vehicles are cheaper than the fighter jets. They can fly to the targeted zones undetected and drop explosives that target the enemy. The fact that these vehicles are controlled remotely means that there will be no human casualty in the assault. Even if the enemy brings down the drone, the Emirati soldiers will not be captured or killed in the process. Respondent 7 said, “The country needs to increase its capacity to use drones and other modern technologies to deal with the emerging threats to enhance efficiency and reduce human casualty.”
Continuous training of the officers
The officers responsible for maintaining security in the country require regular training to ensure that they understand the nature of threats they have to deal with in their normal operations. GEOINT can help in identifying the latest threats to the country. Constant use of this technology will help them understand the changing nature of security threat. The commanders in the military training academies will know when and how to revise the course content in respect to the changing security threats. Officers will need to know how to operate drones just as well as flying fighter jets. Such trainings will equip the local law enforcement agencies and military officers with skills needed to fight modern-day security threats.
Case Study: Using GEOINT to Enhance Homeland Security in the United Kingdom
The United Kingdom is one of the countries, which have suffered terror attacks over the recent past. The Manchester Arena bombing, which occurred on May 22, 2017, is one such attack that puts to question the ability of the country’s security organs to deal with the threat of terrorism. It was followed by another attack in less than two weeks, the London Bridge attack that occurred on June 3, 2017. Such occurrences cause panic among citizens, especially in a stable country such as the United Kingdom where many people often feel safe both at home and in the workplace. Most of these attacks are planned and executed by members or sympathizers of extremist groups such as ISIL and Al Qaeda. In 2015, the Ministry of Defense decided to embrace GEOINT as a way of enhancing its capacity to deal with the emerging security threats. Hewlett-Packard was paid £8.5 million to transform the country’s intelligence agencies (Janmohamed, 2017). The technology firm was tasked with the responsibility of introducing geospatial intelligence to the country’s security organs.
The government of the United Kingdom was concerned that the growing regional and global insecurity was posing a serious threat to the country socio-political and economic environment. It was creating fear among members of the public as it became clear that actions of the terrorists were becoming unpredictable. The introduction of the technology-based approach of collecting intelligence was a major milestone in the war against terror and other organized crimes. The United Kingdom is currently one of the countries actively using GEOINT to enhance homeland security (January, 2018). Various intelligence and counterintelligence agencies in the country such as the National Domestic Extremism and Disorder Unit, the National Crime Agency, the Security Service, Secret Intelligence Service, and Defense Intelligence have all embraced the use of geospatial intelligence. It enables them to collect relevant security-related data and develop plans on how to respond adequately to protect lives and property. The strategy has helped improve homeland security in the country. It is expected to be applied locally in the United Arab Emirates to address the growing security concerns. It could greatly contribute to the current work of the intelligence and security services.
Conclusion and Future Reccomendations
The United Arab Emirates has one of the fastest developing economies in the MENA region. The country has made impressive steps to reduce its reliance on the export of petroleum products. The tourism and air transport sections have become some of the most important pillars of the economy. Dubai International Airport is currently one of the busiest in the world. The real estate market and the trade sector have also registered impressive growth over the past decade. However, the impressive record that most of the economic sectors have registered may be affected by the growing security concerns. The service sector, especially tourism and air transport, is very sensitive to the issue of insecurity. When tourists and business travelers realize that the region is no longer safe, they will opt to visit other parts of the world, a move that may have devastating consequences for the UAE. The emergence of ISIL, Al Qaeda and other terrorists in the region is a major threat to the country’s security. Although the United Arab Emirates has not experienced a major armed attack committed by these terrorists, some neighboring countries such as Saudi Arabia have been affected.
The use of geospatial intelligence offers a solution to this growing security threat. The United States, the United Kingdom, China, Russia, and many other nations are currently using this technology to ensure that they can fight terrorism and other acts of aggression that target citizens and their property. Geographic information system, remote sensing, geographic positioning system, and unmanned aerial vehicles have emerged as the effective tools that can help gather information without having to send intelligence officers to do the job. Currently, the United States is using GEOINT to ensure that its borders are secure from any form of attack. The same technology can be used by the United Arab Emirates and its neighbors within the GCC to ensure that the region is protected from any form of security threat. It will ensure that the security agents in the country can collect data about the existing threats and coordinate a counteroffensive to protect the country. The following are the recommendation on how United Arab Emirates can benefit from GEOINT in supporting homeland security:
- The United Arab Emirates Military Intelligence Security Services (military) and National Electronic Security Authority (civilian) should create special dedicated units that will use GEOINT to collect data.
- The government should ensure that the two units have state-of-the-art technologies needed to collect data remotely within the country and its borders. The Military Intelligence Security Service should have the capacity to collect data beyond the borders, especially in rebel-controlled regions of Yemen and Iraq.
- The officers in these two units should be taken through proper training to equip them with skills necessary for the task ahead. The government can request support from countries with established GEOINT systems such as the United States and United Kingdom.
- The intelligence gathered by the two agencies should be shared with the relevant agencies to ensure that the security agencies can respond to any threat within the shortest time possible.
- The United Arab Emirates should invest in GEOINT technologies and collaborate with coalition countries on geospatial R&D.
Finally, it is recommended to extended this study for further research on areas that could improve geospatial intelligence with an emphasis on geospatial intelligence fusion as well as geospatial intelligence forecasting. Geospatial intelligence fusion covers the linkage between geolocation, social media, crowdsourcing, and spatial analysis. Fusion is significant for the reason that asessing a phenomenon from several sources of information is better than assessment from a single source. Additionally, forecast is important as it can help predict how terrorist groups behave and how that behavior can be changed. Therefore, it can play a key role in informing security services to take decisions for security operations. These areas are part of several means that could improve the quality and timeliness of geospatial intelligence and ensure its effectiveness.
References
Adams, J., Khan, H. T., & Raeside, R. (2014). Research methods for business and social science students. New Delhi, India: SAGE Response.
Ahmad, J. (Ed.). (2018). The BBC, the ‘war on terror’ and the discursive construction of terrorism: Representing al-Qaeda. Cham, Switzerland: Palgrave Macmillan.
Alharith, A. S., & Samak, Y. A. (2018). Fighting terrorism more effectively with the aid of GIS: Kingdom of Saudi Arabia case study. American Journal of Geographic Information System, 7(1), 15-31.
Ambinder, M. (2011). The little-known agency that helped kill bin Laden. Web.
Asmat, A. (2012). War against terror (Pakistan): Fighting terrorism with remote sensing. Web.
Bernard, H. (2013). Social research methods: Dualitative and quantitative approaches. Los Angeles, CA: SAGE Publications.
Biltgen, P. (2016). Activity-based intelligence: Principles and applications. Boston, MA: Artech House.
Brennen, B. (2017). Qualitative research methods for media studies (2nd ed.). New York, NY: Routledge.
Briant, E. (2015). Propaganda and counter-terrorism: Strategies for global change. Manchester, UK: Manchester University Press.
Brown, S. (2015). Faces of power: Constancy and change in United States foreign policy from Truman to Obama (3rd ed.). New York, NY: Columbia University Press.
Card, A. (2016). Applied meta-analysis for social science research. New York, NY: The Guilford Press.
Chaliand, G., & Blin, A. (2016). The history of terrorism: From antiquity to ISIS. Oakland, CA: University of California Press.
Conrado, S. P., Neville, K., Woodworth, S., & O’Riordan, S. (2016). Managing social media uncertainty to support the decision making process during emergencies. Journal of Decision Systems, 25(1), 171-181.
Corvaja, A. S., Jeraj, B., & Borghoff, U.M. (2016). The Rise of intelligence studies: A model for Germany. Connections, 15(1), 79-106.
Deogawanka, S. (2015). Charlie Hebdo attack: Three days of terror. Web.
Deogawanka, S. (2015). How GIS supports the fight against terrorism. Web.
Franz, G., Kane, G., & Fair, J. (2019). Reshaping intelligence operations in the cyberspace domain. The Cyber Defense Review, 4(1), 33-40.
Ganor, B. (2015). Global alert: The rationality of modern Islamist terrorism and the challenge to the liberal democratic world. New York, NY: Columbia University Press.
Hanhimäki, J. M., & Blumenau, B. (Ed.). (2013). An international history of terrorism: Western and non-western experiences. New York, NY: Taylor & Francis.
Heather, M. (2018). The effects of geospatial-intelligence on United States-Mexico border security. Web.
Janmohamed, S. Z. (2017). Generation M: Young Muslims changing the world. London, UK: I.B. Tauris & Co. Ltd.
January, B. (2018). ISIS: The global face of terrorism. Minneapolis, MN: Twenty-First Century Books.
Jenkins, A., Croitoru, A., Crooks, A. T., & Stefanidis, A. (2016). Crowdsourcing a collective sense of place. PLOS, 1(4), 1-20.
Kersten, W., Blecker, T., & Ringle, C. (2014). Innovative methods in logistics and supply chain management: Current issues and emerging practices. Berlin, Germany: Epubli GmbH.
LaFree, G., Dugan, L., & Miller, E. (2015). Putting terrorism in context: Lessons from the global terrorism database. New York, NY: Routledge.
Landon-Murray, M. (2015). Social media and U.S. intelligence agencies: Just trending or a real tool to engage and educate. Journal of Strategic Security, 8(3), 67-79.
Landon-Murray, M. (2016). Big data and intelligence: Applications, human capital, and education.” Journal of Strategic Security, 9(2), 92-121.
Law, R. D. (Ed.). (2015). The Routledge history of terrorism. New York, NY: Routledge.
Lowenthal, M. M., & Clark, R. M. (2016). The five disciplines of intelligence collection. Thousand Oaks, CA: CQ Press.
Mackey, A., & Gass, S. M. (2016). Second language research: Methodology and design. New York, NY: Routledge.
Martin, A. J. (2015). America’s evolution of women and their roles in the intelligence community. Journal of Strategic Security, 8(3), 99-109.
McNabb, D. (2015). Research methods for political science: Quantitative and qualitative methods. New York, NY: M.E. Sharpe.
Miller, M. A. (2013). The foundations of modern terrorism. Cambridge, UK: Cambridge University Press.
Monaco, C. (2018). The mandate to innovate. PRISM, 7(4), 18-29.
Nacos, B. L. (2016). Terrorism and counterterrorism (5th ed.). New York, NY: Taylor & Francis.
Patten, M. L., & Newhart, M. (2018). Understanding research methods: An overview of the essentials (10th ed.). New York, NY: Routledge.
Raman, R. (2013). Everyman’s war: Strategy, security and terrorism in India. London, UK: Random House Publishers.
Rubin, B., & Rubin, J. C. (2015). Chronologies of modern terrorism. New York, NY: Taylor & Francis.
Said, W. E. (2015). Crimes of terror: The legal and political implications of federal terrorism prosecutions. New York, NY: Oxford University Press.
Sappleton, N. (2013). Advancing research methods with new technologies. Derry Township, PA: Hershey Company.
Scott, R., & Howlett, S. (Eds.). (2018). The changing face of volunteering in hospice and palliative care: An international perspective. Oxford, UK: Oxford University Press.
Steiner, J. E. (2014). Homeland security intelligence. Washington, DC : CQ Press.
Suárez, T. (2017). State of terror: How terrorism created modern Israel. Northampton, MA: Olive Branch Press.
Thomas, J. L. (2010). Developing geospatial intelligence stewardship for multinational operations. Web.
Thomas, T. S. (2018). Beneath the surface: Intelligence preparation of the battlespace for counterterrorism. New York, NY: William S. Hein & Company.
Udochukwu, E. S., Christian, U. E., & Adebayo, A. (2014). The application of geospatial intelligence in national security for sustainable development to combat terrorism insurgence in Nigeria. Journal of Environmental Science, Toxicology and Food Technology, 8(9), 11-16.
Walter, M., & Andersen, C. (2016). Indigenous statistics: A quantitative research methodology. New York, NY: Routledge.
Witt, E. C. (2015). Geospatial resources for the geology community: The USGS national map. The Journal of Geology, 123(3), 283-294.
Zarakol, A. (2011). What makes terrorism modern? Terrorism, legitimacy, and the international system. Review of International Studies, 37(5), 2311-2336.
Appendices
Questionnaire
[The primary goal of this research is to conduct an analytical study of the impact geospatial intelligence on homeland security, with a specific focus on how the new technology can be used to enhance security in the United Arab Emirates. The paper will determine how the security forces in the country, both the military and law enforcement agencies; can use this emerging technology in the field of intelligence gathering to fight threats to security in the country. Your participation is important, as it will help in the collection of information relevant to the study. Kindly provide answers to each of the questions below to the best of your knowledge. Your participation is on a voluntary basis]
Part A: Respondents’ Demographic Information
- In which age group do you belong? Tick as appropriate
- 18-25
- 26-33
- 34-40
- 41-55
- Over 55 Years
- What is your gender: Tick as appropriate
- Male
- Female
- What is your Nationality? Tick as appropriate
- Emirati national
- Non-Emirati national
Part B: Respondents’ Academic Qualifications and Experience
- What is the highest academic qualification you have besides your training in the security sector?
- High school graduate
- College diploma
- Bachelor’s degree
- Master’s degree
- Doctorate degree
- Are you assigned to a high-ranking position where you have to make critical decisions?
- Yes
- No
- How long have you been working in the security sector?
- Less than 2 Years
- 2-5 Years
- 6-9 Years
- 10-16 Years
- Over 16 Years
Part C: Impact of Geospatial Intelligence on Homeland Security
- Following the events of the Arab Spring, do you believe that security has become a major concern than before in the GCC region? Kindly explains.
- What is the level of threat that the United Arab Emirates is facing from terror groups within the region?
- What is the relationship between geospatial intelligence and homeland security? Provide a short explanation.
- For the countries that have embraced the use of geospatial intelligence, do you believe they have improved security than was the case before its introduction? Kindly explain.
- How effective is geospatial intelligence in fighting emerging threats to homeland security in the country?
- How ready is GCC in terms of embracing GEOINT as a way of combatting the emerging threats to homeland security?
- How well do the local security forces understand the significance of geospatial intelligence in the fight against insecurity?
- What is the level of investment that the country has made to promote the use of technology to gather intelligence?
- How effective are the local law enforcement agencies in terms of using the technology to gather the intelligence necessary to keep the country safe?
- Is there a will on the part of the government to create capacity within the armed forces to enhance the use of GEOINT in managing security?
- What are some of the issues that affect effective application of emerging technologies, especially the use of GEOINT, in managing the country’s security?
- What are some of the challenges that the country is likely to face when using GEOINT to enhance the country’s homeland security?
- What do you believe will be the reaction of other regional countries when the UAE starts to embrace GEOINT to enhance national security?
- What is the danger to the country if other neighboring countries adopt this new method of managing homeland security?
- What do you believe the government should do (that it is currently not doing) to ensure that it promotes the use of GEOINT as a way of enhancing homeland security?
Thank you for being part of this study. Information that is obtained from you is meant for academic purposes. Your identity will remain confidential as was initially promised.