Summary
This paper takes us through computer systems architecture and the constituent components that make up a computer. It introduces us to the functions of the hardware parts of a computer and how each part of a computer system work. Ideally, computer architecture constitutes hardware that acts as a platform for systems software and network components. In addition to that, it details the internal working of hardware components spanning the central processing unit (CPU) and their processing capabilities (Patterson, 1996).
Computers and their capabilities
A computer is an electronic device that accepts numerical data inputs computes the data and communicates the output into the console unit. Computers execute these tasks electronically or mechanically. This is achieved by combining electrical and mechanical techniques in executing assigned tasks. Computations can either be electronic or mechanical.
The mechanical approach of performing computations is limited in terms of the complexity that is urged upon their construction. The wear and tear of mechanical components and associated maintenance requirements and the slow computational speeds that are achieved are some of the drawbacks of this method. On the other hand, computations can be executed electronically. Electronic signals replace the complex system of gears and wheels in mechanical systems. Electronic computations outdo mechanical computations in terms of speed, efficiency, cost, and implementation.
Besides mechanical and electronic computations, optical computations can be used to perform computations on data. This is based on the concept of the particle nature of light. Data exists in the form of light and it has been projected that optical computing will in the end overtake electronic computing (Patterson, 1996). This is due partly to the way different areas of application have experienced exponential growth in the use of light in different devices with much success.
The capability of Computers
Having compared different computational models, an in-depth look into the abilities of modern computers is inevitable. Computers are classified depending on the key characteristics of the processing hardware. The processing hardware, referred to as the processor manipulates data by performing mathematical computations such as additions, subtractions, comparisons, and moves data from memory to input storage and output devices. The processor achieves these through instructions that it fetches and executes. These instructions are commonly referred to as computer programs. Processors accept instructions that direct them to perform specific tasks in the form of programs.
Processors are computer hardware classified into special-purpose and general-purpose processors. Special-purpose processors perform special tasks while general-purpose processors perform a variety of tasks. These hardware technologies are based on the principles of classical physics. These principles have their basis on the behavior of matter at atomic and sub-atomic levels. Patterson (1996) argues that with advances in physics, data can now be represented in bits and bytes in modern computers. In addition to that modern computers have huge information and data storage capacities. In modern computers information is stored in the form of data, programs.
Computer Hardware
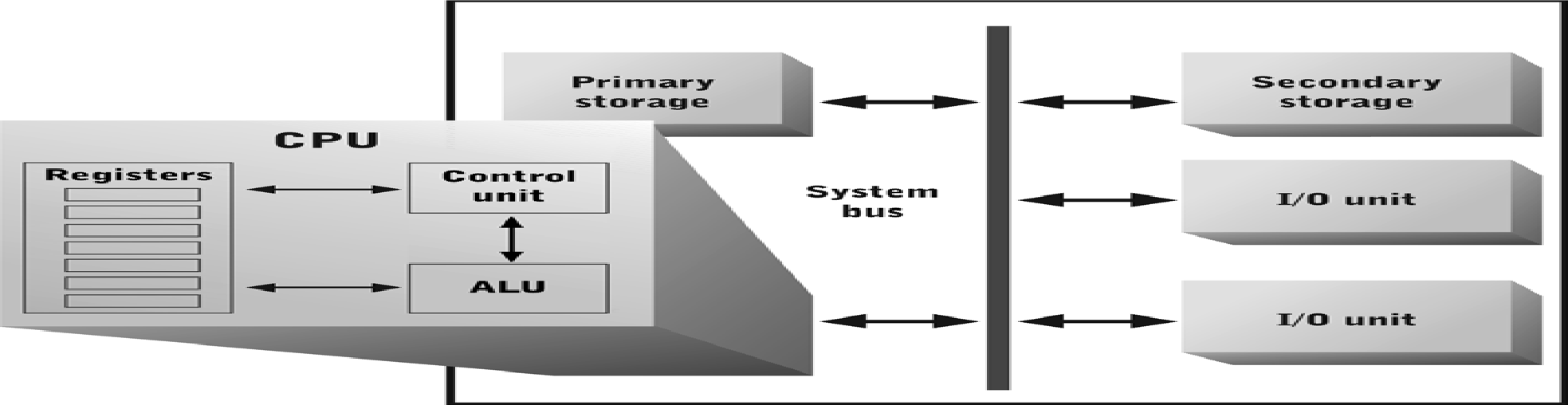
Hardware in a computer acts as a platform for data and information processing. Computer hardware provides computational capabilities for processing data and information by accepting inputs and computationally transforming these inputs into outputs. These outputs are meaningful and can influence an action (Patterson, 1996). In addition to that, hardware provides a platform for short term and long terms data storages. Besides that, these computers act as communication channels from and to the outside world. In addition to that, computers enable data and information transfer between different hardware devices and coordinate all communication that occurs between a computer and its peripheral devices. The major hardware parts of a computer constitute the central processing unit which manipulates data and programs by accessing information and data from temporary storage devices or permanent storage devices. The CPU works by coordinating the arithmetic logic unit, the control unit, and the memory registers functionalities (Comer, 1986).
The architecture of the arithmetic logic unit is primarily composed of electronic circuits which provide the path through which data flows. This data is basically stored in registers whose capacity is characterized by a single bit of data. On the other hand, the control unit coordinates data communication between different hardware storage devices and the CPU and identifies program instructions, fetches them and issues relevant commands to the ALU to execute them(Patterson, 1996). Other hardware devices include the system bus that provides a path through which data flow to different destinations. In addition to that, other hardware devices include primary storage devices that hold data for temporary data and information commonly referred to as random access memory (RAM).
Data can also be stored in secondary storage devices for long term storage of programs and data. This makes secondary storage devices slower and less expensive than primary storages devices. A computer system becomes complete when input and output devices referred to as I/O devices are integrated into the whole architecture of the computer system. These provide a good interface for computers to communicate with peripheral devices by accessing or transferring data and information from and into these devices.
System software
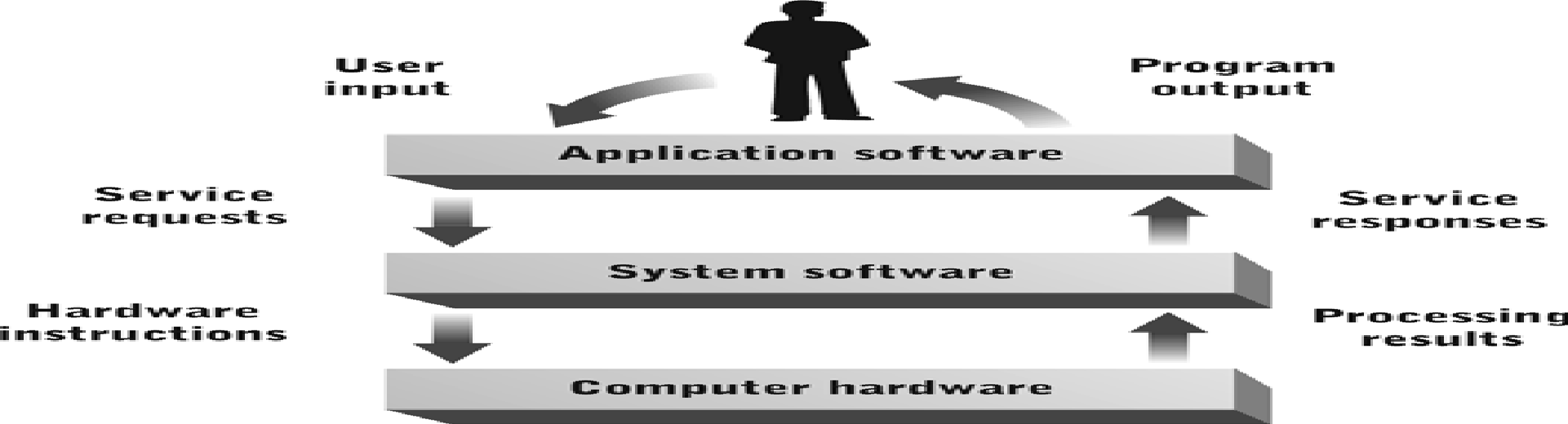
System software is used to capture the user’s instructions and translate them to be executed in the CPU. These instructions are usually translated from human-readable and understandable languages to machine-readable instructions that are represented in the computer as bits and bytes. Patterson (1996) argues that high level abstractions are translated into low level details through system software. System software manages and allocates computer resources and performs tasks needed by various applications to run efficiently (Patterson, 1996).
System software typically provides services requested by the user. These may include supporting end users, controlling user interactions, system security, detecting and throwing error conditions, and controlling input and outputs operations. These services optimize a variety of system software layers. These include the hardware interface layer, resource allocation layer, system management layer, and system services layer. One of the system software that provides system services is the Operating system. It is a platform upon which other programs run.
The Beginning of Technical Knowledge
Processors
Processors are architecturally characterized by interconnections of millions of circuits that are burned into single chips. Different processors manipulate data differently. Among these are multicore processors that are embedded into a single chip based on the concept of a multicore architecture. These processors consist of different compartments that are divided into different cache areas with different functionalities and capabilities. However, this also depends on the manufacture of the processor (Patterson, 1996).
Integration and Performance
A focus on how computer devices coordinate their operations affords this discussion. One of the coordinating mechanisms is the system bus. This component has an established protocol with other computer devices and provides a link for different system components to communicate in transferring data through electrical or optical signals. The data bus translates data from and to target memory addresses by reading and identifying status information of all transmitted data, memory registers, commands, and responses (Patterson, 1996). The constituency of the system bus is composed of the data bus, control bus, and address us. The system bus is uniquely characterized by circuitry that has evolved from wired to data communication lines. The system bus hosts a number of devices as discussed below.
Devices ported to the system bus coordinate their activities by a bus clock with bit rates of the magnitude of 2.5 nanosecond and a data transfer rate of 3200,000,000 byte per second. Coordination of data and respective devices is done through a bus protocol. This protocol governs data formatting and representation, controls system usages and messages sent through the bus. It identifies data and its contents and requisite memory addresses. Bus cycles and device controls based on system bus protocols adversely impact on system optimization in data transfer rates. However efficient protocols optimize system capacity and provide faster data transfer rates between different devices (Patterson, 1996).
The performance of each bus protocol depends on the strategy used to access data, transfer data, and store temporary data files. Such control devices include direct memory accesses (DMA) and the DMA controller. The DMA controller is the master of the data bus. In addition to that, various types of data buses exist. Among them are video buses, I/O bus among others. Information on various types of devices and buses can be accessed from the device manager.
The data bus provides access to information through logical and physical access mechanisms. Various devices are ported to the data bus to provide data conduits for information flow and storage when being accessed (Patterson, 1996). In addition to that, device controllers implement interface and access protocols, control system access by different components, and provide mechanisms of physical data translations. Other devices of vital importance are interrupt handlers that listens and handles interrupts and calls for services. These handlers report error conditions, service requests, and I/O tasks.
Other protocols handle performance mismatches, buffering and caching, sand tack processing.
I/O
The computer system bus architecture hosts input-output devices that are largely categorized into human and computer devices. These can be modems, keyboards or printers. Data transfer between the system bus and these devices is governed by system bus protocols. Input and output devices optimize basic display concepts that range from image compositions that are matrix oriented which are characterized by excellent display resolutions (Patterson, 1996). These include fonts and their sizes, color, image storage and communication, video displays, image description technologies. Other output devices include barcode readers and scanners. These devices detect specific data patterns in an item for a large number of items in a short span of time. In addition to that, an optical scanner generates a map typical of a printed page. These scanners rely on photoelectric sensitivity to different frequencies of light. They integrate pattern searching abilities with special purpose software to read and print a block of data. On the other hand, data capture devices integrate capabilities of input output devices and computer enabled communication channels. The diagram below illustrates typical components of the CPU.
Data and Networks
Data is stored in a variety of ways and communicated through network devices. Data representation and processing is logical and mathematically manipulated. Data storage and representation in a computer optimizes binary rules. Binary data is well mapped into Boolean logic. Besides that, data storage and processing can be in hexadecimal and octal form. This ensures data compactness and range, accuracy, flexibility in manipulating the data, and complete standardizations. Data is stored in different data type forms. Data types can be integers, Booleans, among others. In addition to that, data communication though networks follows standards that have been established by various international organizations (Patterson, 1996). To sum it all, data in all computing devices is represented in 0s and 1s. The CPU recognizes and processes these primitive data types that are categorized into characters, Boolean values, integers and real numbers. These representations of data follow standard protocols established by the IEEE.
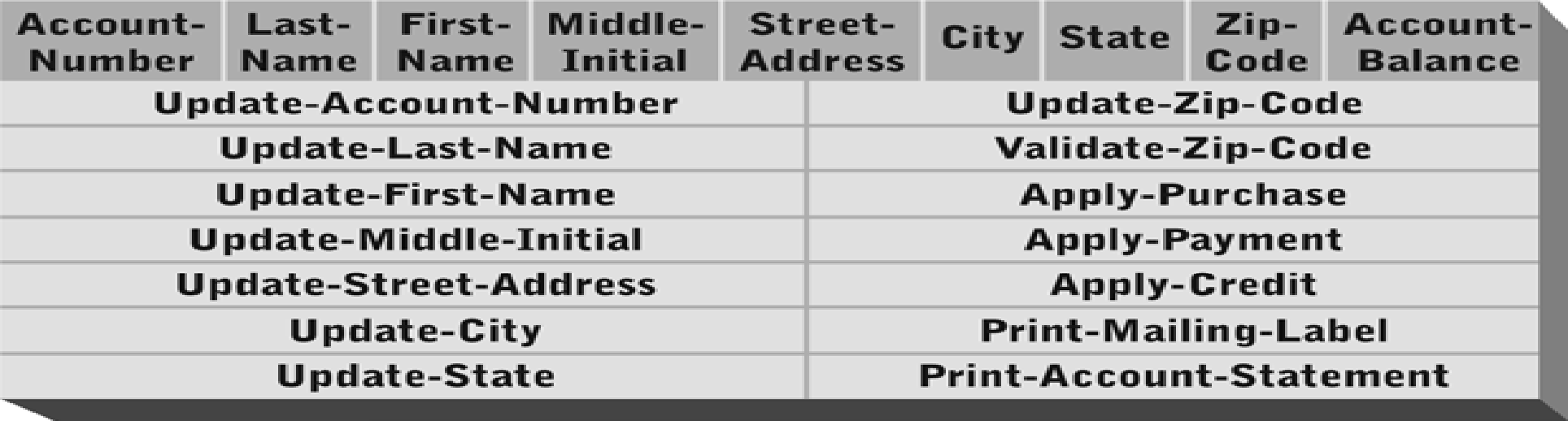
Data structures define data storage formats. Different algorithmic approaches are used to optimize access to data stored different data structures. Among the data structures are pointers and arrays. Software developers make extensive use of pointers and arrays and lists to access data stores. Data stores can be formatted as files that are defined by primitive data elements that are organized and accessed through a specified sequence of steps. However, the sequential access methods suffer from inefficient time optimization in accessing data elements. A linked list is a data structure that optimizes search for a data element in a more efficient way and is less time consuming.
Data storage and presentation and access are defined by data structures such as pointers and addresses, arrays and lists, and records and files. Other data structures include classes and objects. An example of a customer class is illustrated below.
Network Architecture
Computer Network
Basically, a computer network is an interconnection of two or more computers through a communication medium such as a fiber optic cable for the purpose of sharing data and other resources (Comer, 1986).
Computer Network Architecture
Computer architectures vary from one design to another and share common attributes such as network topologies and communication protocols. However, it is important to note that computer architectures are classified into three basic designs. These categories include the local area network, the wide-area network, and the metropolitan area network. Each of these network designs are uniquely characterized by features that distinguish one network design from the other. Noticeably, a local area network is characterized by its scope of operation. It consists of a small number of computers that are connected to each and operate within a small area such as a building (Comer, 1986). These computers can also be connected within an office or a home. On the other hand, a metropolitan area network is characterized by an interconnection of communicating computers which are geographically separated but located within the same city. This network design uses either cables or wireless communication to link the computers within the network for the purpose of sharing data and other resources. In addition to that, the wide-area network architecture is characterized by an interconnection of computers that are geographical separated spanning wide areas of coverage such as different cities for the purpose of sharing data and other resources through cables or wireless by means.
Network Architecture Topologies
It is important to identify and discuss network topologies to completely understand network architectures. These topologies are classified into star, bus, and ring topologies (Comer, 1986).
The hub or switch in a star topology forms the central point to which all nodes in a star topology are connected. On the other hand, the bus topology is characterized by network elements that are connected to a single cable. All data transfer occurs between the computers and the backbone cable (Hayes, 2002).
The last topology is the ring topology. This architecture is characterized by a ring framework in which all the computers in this topology are connected to each other in a ring. One computer communicates to the next computer in the ring through a mechanism known as token passing. Each computer in the ring accepts the token from the ring, if the token is meant for the host computer, the computer empties the token and releases it to proceed to the next computer to be used to carry other tokens around the ring. It is important to note that communicating computers in a network do so through a number of rules known as protocols.
Protocols are communication standards or rules with underlying definitions on how communication between different nodes and electronic devices in a network occur. These protocols are characterized by schemes that are typically used for error checking when transmitting data from one node to another. The scheme defines how data is formatted during transmission from source to destination. It also defines the different methods networked computers use to communicate between each other. One of these protocols is Internetwork Packet Exchange (IPX). This protocol is designed for a specific operating system commonly referred to as Novel Netware. Another protocol is the Asynchronous Transfer Mode (ATM). The ATM protocol optimizes data transfer in fixed-sized packets. One of the benefits with this protocol is that it provides high speed data transfer rates in a reliable and secure environment. In addition to that, ATM provides voice and video data transfer within one network and another (Comer, 1986).
Theoretically, these protocols transfer data through the seven OSI (Open Systems Interconnection) layers. The OSI model is defined by seven layers with each layer performing a specific function. In addition to that, the protocol is cross-platform as it is accommodates communication from different hardware and software platforms. It is interoperable.
The first layer among the seven layers is the application layer. This layer defines data and other communication interfaces and provides standardized services for communicating partners. The next is the presentation layer whose functions are to make data communication across different platforms compatible and provide data encryption and other security functions. The session layer is another critical component of the layered protocol. It is next after the presentation layer. Specific to this layer are session and dialogue management between communicating and talking parties. In addition to that, the layer identifies, establishes and terminates links between parties engaged in a communication and identifies and reports errors that occur in each of the upper layers of the model (Patterson & Hennessy, 2003).
The next layer is the transport layer which follows after the session layer. The transport layer ensures that data and information are correctly delivered to the target destination. The layer ensures that reliable data deliveries are made and any loss of data is appropriately recovered. The network layer ensures, which is the next layer in the series uniquely formats and delivers data packets between different networks and ensures that the flow of data within each network is controlled to avoid data congestion and other performance hitches (Hayes, 2002). The second last layer, the data link layer frames packets for transmission, and ensures that data and packets for transmission are error-free. The last is the physical layer. This layer specifies specific data formats to be sent across different networks. These protocols and network topologies enable data communication to be possible through different networks.
References
Comer, D. J., 1986. Microprocessor-Based System Design. New York: CBC College Publishing
Hayes, J. P., 2002. Computer Architecture and Organization. 3rd ed. New York McGraw-Hill
Patterson, David A. 1996. Computer Architecture: A Quantitative Approach. 2nd ed. San Francisco, CA: Morgan Kaufmann Publishers.
Patterson, David. A. & Hennessy, John. L., 2003. Computer Architecture: A Quantitative Approach. 3rd ed. San Francisco, CA: Morgan Kaufmann Publishers.