Abstract
SR 168 billion or US$45 billion of the Saudi Arabian Government’s budget for 2012 was allotted to education and training. Furthermore, the Saudi e-learning market is predicted to be worth US$ 670 Million by 2014. Despite this expansion, rates of failure in e-learning project remain high, pointing to the importance of adopting risk assessment procedures in implementing e-learning programmes successfully in Saudi universities. Detailed interviews were conducted with experts from the National Centre for e-learning and Distance Education (NCELDE) to assess how e-learning projects were analysed for learning risks and how such risks were managed.
Through interview and questionnaire, participants were asked to rank the likelihood of 15 e-learning risks occurring, along with their potential impact, to determine which risks were most significant. Unrealistic expectations formed the most significant risk, followed by unreasonable schedule and budget for a project, lack of completeness in requirements, no agreed-to user acceptance testing and sign off criteria, and software which was no longer necessary. Most participants suggested project management approaches rather than technical processes as strategies through which such risks could be dealt with, thus providing support for the concept of project management as a risk management strategy. Communications management, for example, was among solutions suggested within this approach.
Introduction
E-Learning in Saudi Arabia
Recently, the Saudi Arabian government has given more attention to the development of higher education infrastructure and increased the budget of the education sector. This, in turn, has resulted in the growth of e-learning programmes in Saudi universities.
The expansion has also been motivated by the wide acceptance of e-learning programmes by students as well as employees. Other factors, including advancements in the e-learning industry, government initiatives, availability of broadband connectivity, the cost-effectiveness of e-learning, increasing need for soft skills and new IT and business systems, continue to encourage many educational institutions and students in Saudi Arabia to engage in e-learning programs (Papanikolaou & Boubouka 2010). The demand and need for e-learning education facilities in Saudi Arabia have increased rapidly. The latest research in Saudi Arabia’s education system forecasts increased demand for e-learning modules driven by the rise of investment in e-learning, which is seen as promising as an alternative to distance education. The Saudi e-learning market’s size is likely to grow by 33% during the next two years, to reach US$ 670 Million by 2014. At the beginning of 2012, the Saudi Government announced a $40 billion (SR 150 billion) budget for education and training.
The Saudi government has declared its aim to create new universities across the country, which are expected to demonstrate a considerably increased focus on e-learning. Therefore, the Ministry of Higher Education (MOHE) has set up a National Centre for E-Learning and Distance Education (NCELDE) to promote e-learning and distance education programs across Saudi Arabia. The NCELDE anticipates offering e-learning programs to over 100,000 students in 50 colleges. Furthermore, it forecasts that around 300 colleges and more than 400,000 students will be engaged in e-learning programmes in 2 years’ time.
Risks Associated with Adoption of E-Learning in Saudi Arabia
In reference to e-learning delivery, there are several risks which touch on different areas, such as investment, operation, security, and technical elements of IT. As observed by Ganga & Ricketts (2007), investment risks are broken down to accommodate risks such as technological and environmental risks, market risks, competition risks, and firm-specific risks. All these risks are interrelated, and assessment during the introduction of e-learning is essential. Prior to the adoption of e-learning in Saudi Arabia’s universities, risk analysis is important as it will prepare the project management team to deal with the risks that arise during the execution stages, and when the project is in progress and fully accomplished. Wallace (2006) highlights some of the risks experienced in e-learning, including poor leadership, intellectual property rights, unrealistic expectations, sustainability issues, poor partnership working, insufficient human resources, and technical limitations, among many others.
Before the adoption of e-learning in a Saudi university, different stakeholders should be aware of the risk of project failure. According to Joubert & Wishart (2012), in the US, the introduction of e-learning was associated with program failures of poor business approach. In addition, more than 50% of students dropped out of the courses that were offered. However, this was considered a necessary step in online learning and teaching. Indeed, e-learning has become a success in the US, with a survey carried out in 2009 showing that over 4.6 million students were enrolled on online courses. Therefore, Saudi Arabia is in a position to borrow a leaf from the book of established e-learning programs in the US and UK.
Historically, even government-sponsored e-learning programs such as Alllearn of Yale, Stanford, Oxford, United Kingdom e-University, New York University Online, and Arizona Learning Systems, among others, have failed (Panda & Mishra 2007). Therefore, there is the risk of adopting e-learning programs and later failing to succeed. Some of the reasons why the programs failed include a poor business approach, low student levels, high costs in sustaining top-quality courses, high costs in building learning management systems, and poor focus of students’ related services. Risk analysis on these issues would help in mitigating or reducing the associated risks while delivering e-learning programs in Saudi Arabia’s universities.
Government involvement and policy that supports e-learning are necessary for ensuring that the delivery of e-learning emerges as a success. As illustrated by Panda & Mishra (2007), a policy should be developed that prepares the public for e-learning since the project will undergo experimentation as well as failures before it is fully implemented. In addition, the government can offer financial support in public universities which are prone to financial difficulties.
Risk Analysis in E-Learning
E-learning is a relatively new area: therefore, risk management experience in e-learning is still limited. However, e-learning can be classified as a part of information technology projects, and thus risk management practice in IT project could be applied in e-learning projects. The IT industry has been plagued by project failures which result from project risk factors. E-learning, which is a part of the IT industry, is also prone to project risks.
Risk can be described as the measure of project uncertainty or the difference anticipated between expectation and reality (Adams 1995; Ma & Doug 2000). Generally, the risk is regarded as a negative factor in the introduction of new technology because of its associated downside exposure to unrealised benefits, technical; performance shortfalls, time slippage, cost overruns, and withdrawal by sponsors from the projects (Yellen 2000). The implication is that before carrying out a project, it is imperative to have a good strategy to manage the risks associated with the adoption of new concepts such as e-learning.
Risk management’s key elements are risk assessment and risk mitigation. Risk assessment allows the project management team to evaluate the likely risks as well as the sources of those risks before a project has commenced (Blass & Davis 2003; Ma & Doug 2000) and is carried out to identify, estimate and evaluate risks associated with undertaking a particular project (Panda & Mishra 2007; Cassel 2002; Dobrowski 2006). Risk mitigation is about deciding the best way to deal with a specified risk: whether to tolerate it or reduce it by taking direct action, by transferring it to someone else or even by terminating the activity which is considered the source of the risk.
Risk analysis is generally divided into three essential activities: risk identification, risk estimation and risk evaluation. Risk identification is the most important process of risk management, as there is no way to deal with risk without identifying it. Most of the time, using past experience of types of risks that have been recognised within the area or any other similar areas is considered the general strategy for risk identification. Identifying new risks necessitates greater thought about things that have not been tried before, which is difficult, particularly in a new area such as e-learning.
Underlying the estimation and evaluation of risk is the assumption that it is possible to draw logical conclusions regarding the chance of a risk occurring, as well as the possible effect of that risk. Risks can also be categorised as a short-term or a long term risk. Determination of short term risks assists in mitigating long term effects which may result from neglected short-term risks. In most past studies, risks identified have been related to the technical aspect of e-learning, forgetting cultural and human issues as possible risk factors, especially when e-learning programmes take place in complex human-centred organisations such as Saudi universities, and often involve collaboration between several partners.
Aim and Objectives of the Study
The emphasis in this research is on the assessment of potential areas of risk on delivery of e-learning projects in Saudi Arabia’s universities. Therefore, this thesis could be considered as a guidance study, providing annotated links to the risks in e-learning projects in Saudi Arabia, which enables e-learning project managers in Saudi Arabia to improve their understanding of the major risks involved in their projects, and to become more aware of suitable strategies for the management of such risks. The outcomes of this research project are not subject to any specific predictions. While the research was conducted in Saudi Arabia, it is possible that the outcomes will be broadly relevant to other locations, especially in Gulf countries.
The study seeks to explore the following objectives:
- To identify risks associated with e-learning projects through analysing available literature on the topic;
- To report on the assessment of these risks by the employees of the National Centre for E-Learning and Distance Education (NCELDE) in Saudi Arabia;
- To identify possible ways to treat these risks according to the points of view expressed, and;
- To make recommendations based on conclusions drawn from interviewees and questionnaire respondents.
Research Scope & Structure
This research begins with an outline of the most recent literature on risk assessment and mitigation in e-learning projects and risks analysis theories, highlighting the most frequently applied model of qualitative risk analysis, which is Risk Factor Analysis, which is a systematic qualitative risk analysis technique developed by the Los Alamos National Laboratory. There is then a focus on risks associated with e-learning projects, and a list of risks applicable in the e-learning area is provided, including technical risks, schedule risks, cost and funding risks. Risk treatment solutions are provided along with the risk areas identified (see Chapter 2).
Chapter 3 outlines the methodological procedures undertaken to conduct this research. The research approach is a general qualitative research design, depending on interviews and questionnaire to develop grounded theory. The methodology chapter further explains how qualitative content analysis of interview and questionnaire results is used to achieve this goal of grounded theory development. The sampling process is accordingly explained in detail, along with methods of data analysis. The fourth chapter focuses on the results of the interviews and questionnaire, discussing the data gathered and critically summarising the results in such a way as to support the initial research aims and objectives. A final conclusion is then drawn in Chapter 5, identifying both outcomes and limitations of the research, with suggestions for possible further research.
Literature Review
Introduction
This section of the paper attempts to explore the delivery of e-learning programs in Saudi Arabian universities. In addition, it aligns past research materials with the aim of the study and the research objectives formulated. The different theories adopted by e-learning programs and the risks associated with these are also discussed in detail. According to Al-Shehri (2010) and, e-learning is a subset of distance learning and can be defined as the process of delivering content through electronic media. Examples of electronic media adopted in e-learning include CD-ROM, interactive TV, audio and videotape, satellite broadcast, extranets, intranets, and the internet (Joubert & Wishart 2012; Al-Shehri 2010; Wallace 2006). E-learning can either be asynchronous and synchronous. The asynchronous approach is a mode of e-learning that facilitates learning to be carried out in real-time (Aboulfaraj, Jomoah & Hassan 2009, p.3) because it is largely interactive. Some of the real-life applications with regard to e-learning include discussion groups, online chats, question and answer, mentoring, video and audio web-streamed web presentation, videotaped classes, and self-paced classes (Aboulfaraj, Jomoah & Hassan 2009, p.3).
On the other hand, synchronous learning uses a real-time platform, which is usually an instructor-led exercise. All the participants are “logged in” at the same time in such a way that they can communicate simultaneously. Examples of synchronous learning as noted by Aboulfaraj, Jomoah and Hassan (2009, p.3) include virtual classrooms, internet telephony, video and audio conferencing, and two-way live satellite broadcasts whereby lecturers can communicate with students in a classroom. Over the past decade, e-learning has emerged as a new learning method. This has been made possible by the emergence and advancement of information communication and technology.
In determining the risks associated with the adoption of e-learning and its delivery, theories related to e-learning and risk analysis will be adopted. The theories and their application are discussed below.
Qualitative Risk Analysis Theory
Risks are uncertain happenings which have an impact on projects being undertaken. As a result, risk analysis is deployed to assess the degree of risk uncertainty as well as its impact on a project. One of the major approaches applied in project risk analysis is structural risk analysis, which is used to determine some of the problems related to technical implementation (Ganga & Ricketts 2007). E-learning is operated through multiple systems which are prone to uncertainty, hence the need to carry out a risk analysis process.
Qualitative risk analysis entails the analysis of risk factors via a qualitative rather than quantitative approach. One of the systematic qualitative project analysis techniques applied in assessing risks in project management is Risk Factor Analysis (RFA). As noted by Ma & Doug (2000), the RFA method explores the risk factors that arise during the pre-conceptual and immediate levels of project development. The tool, which was designed and developed by Los Alamos National Laboratory, uses flow charts which entail different variables. As with e-learning, the major risk factors analysed under the RFA model are technical risks, schedule risks, cost risks and funding risks. All these risks are intrinsically intertwined in such a way that the presence of one risk creates room for the other. For instance, funding risk, which may result from underfunding, leads to increase in cost overheads, which is an example of cost risk. The technical/operational risks are associated with the systems, adoption of new technology, training employees, satisfying all clients, among others.
As noted by Kindinger and Darby (2000), technical risks expose the whole system to risks, which may affect the whole project, to performance and operational risks which may jeopardise the whole mission of a project. Schedule risks are concerned with time allocated, design, research and development and start-up operations. Cost risks are related to the risk of not meeting technical risks, cost overruns and cost performance (Kindinger & Darby, 2000). Lastly, funding risks are associated with underfunding or increase in costs as a result of a delay in project completion. By determining the risk factors, it becomes easy for the management team to undertake their project and control both unanticipated and anticipated uncertainties. Examples of risks are represented in Figure 1 below, as adopted from Kindinger and Darby (2000).
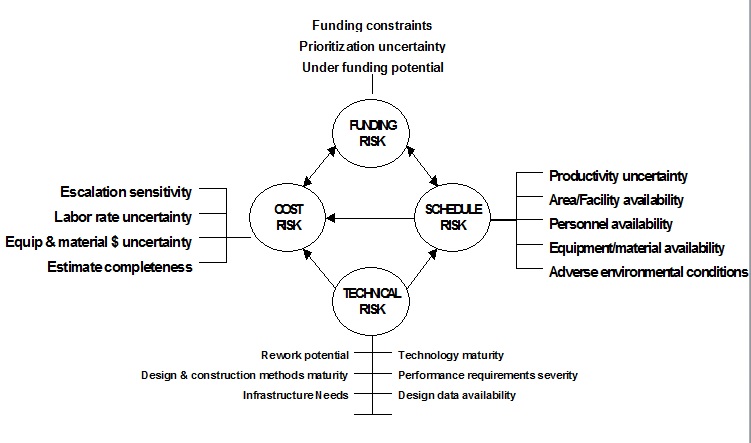
From Figure 1 above, there are different risks associated with project risk analysis. All these risks are applicable in the e-learning implementation as well during its delivery in Saudi universities. The application of these risks in reference to the context of Saudi Arabia is discussed in the sections that follow below.
Risks Associated with Adoption of E-Learning
Operational risk is regarded as the main risk in e-learning (Patomviriyavong, Samphanwattanachai & Suwannoi 2006, p.2). Operational risks involve risks associated with processes, people, technological elements, and content. This is supported by Alwi and Fan (2010, 143) and Dabrowski (2006). They add that despite e-learning being exposed to operational risks, it is also exposed to content risks as a result of security breaches or issues. Content risks are those risks which occur during the preparation of coursework. This includes the risk of having low content, which may not be enough to cater for the increased number of students in Saudi Arabia.
In most cases, the internet is relied upon to enhance communication. According to Patomviriyavong, Samphanwattanachai and Suwannoi (2006, p.442), internet speed is necessary, and a decline in internet broadband places connectivity at risk. In some cases, a decrease in internet connectivity may cause loss of content, damage of program reputation, and monetary losses. Human beings are employed to run e-learning facilities. Humans are also prone to mistakes, not to mention that different people have different levels of knowledge and skills. Therefore, it may be hard for an instructor who is not well trained to conveniently address over 40 students if by any chance, they ‘log in’ simultaneously. Lack of skills can jeopardise full execution and implementation of e-learning in Saudi universities.
Although e-learning has been regarded as a major breakthrough in learning, and especially in higher education (Kapp n.d), there are however numerous costs which may hinder its full implementation, use, application, and delivery, not only in Saudi Arabian universities but on a global level (Ganga & Ricketts 2007; Joubert & Wishart 2012; Alghamdi 2012). Cost is one of the major barriers associated with the implementation of e-learning. Aboulfaraj, Jomoah and Hassan (2009, p.8) note that e-learning is perceived as costly because high upfront outlay is required to maintain the system and purchase the learning management system. High costs increase the risk which comes with its implementation, and the management staff at most universities see it as a waste of financial resources (Ma & Doug 2000). Therefore, universities may go ahead and implement e-learning services without the guarantee that full support with the costs required will be given (Panda & Mishra 2007). In a study that was carried out in Saudi universities on the perceptions of students and faculty members found that some of the major constraints to implementation and delivery were a high cost of internet connection in Saudi Arabia compared to other Arab nations (Hussein 2011, p.51).
According to the Centre for Education Research and Innovation (2001), universities are faced with risks such as offering state-of-the-art technology in order to compete favourably. While implementing these new technologies for e-learning programs, numerous risks and large sums of money are usually involved. This can be reduced by hiring a team of technicians that is well versed technologically. Hussein (2011, p.51) notes that there is a risk associated with the lack of a support team that is well trained for students and faculty staff before, during, and after the use of e-learning services. These risks are necessary for the e-learning process. Lost competitive advantage, lost opportunities to deliver training at low cost, and challenges faced while training employees and students have been considered as possible risks experienced while delivering e-learning (Yellen 2000). In addition, there are other risks associated with the effectiveness of e-learning with regard to delivery. According to Aboulfaraj et al. (2009, p.9), the expectations of the management determine the effectiveness of e-learning through the measurement of learning outcomes.
The high cultural values and beliefs among Saudi nationals have hindered the full implementation of e-learning in Saudi Arabia. In reference to the delivery of e-learning, culture is seen as a major risk which jeopardises the adoption of e-learning in Saudi Arabia. Aljabre (2012, p.133) notes that there has been an increase in the number of students who are dropping out of distance learning classes in Saudi Arabia. Most of the students have withdrawn from distance learning as well as e-learning courses in favour of the traditional classroom setting. Although there is no profound and well-founded reason why students are withdrawing from online and distance learning classes, it has been suggested that culture has played an integral role. Societies characterised by close social relationships prefer a collective learning style which is based on a holistic approach.
The absence of an instructor with physical touch in e-learning has been suggested as another reason for students’ trepidation towards this new form of learning (Aljabre 2012, p.133). In this line of thought, the above statements can be viewed as risks since the implementation of e-learning will be shunned by students because of their culture and its nature. The government of Saudi Arabia may be willing to invest in e-learning programs, but there is the challenge of its adoption, thereby risking the implementation and delivery of the services. Hussein (2011, p.51) is in support of the above argument and has noted that there is the risk of community resistance on e-learning programs in Saudi Arabia since most of the community members consider it as a facet of western culture as opposed to a mode of learning. In addition, a study carried out by Blass & Davis (2003) showed that online-based degrees were less preferred by most employers, and as a result, students preferred traditional learning methods.
Security is a major risk involved in the implementation and delivery of e-learning programs in universities (Panda & Mishra, 2007; Cassel, 2002; Wallace, 2006). According to Kritzinger (n.d, p.3), ICT opens major doors for security which have thus far compromised the whole e-learning environment. This is because e-learning depends strongly on the internet as a platform for communication, thus contributing to high-security risks. The presence of hackers, malicious software and viruses pose a threat to the implementation of e-learning at universities (Ganga & Ricketts 2007). This problem is evident in Saudi Arabian universities since they also use the internet to offer e-learning services. Kritzinger (n.d, p.3) adds that students can access examination marks from the main database and have them changed. In addition, some students may also intercept the assignments and coursework of other students while they are being delivered and resubmit before the owner has done so. However, this is a matter of proper implementation of security measures in information systems. Because of the security threats posed, issues of integrity and confidentiality become compromised (Dabrowski 2006; Alwi & Fan 2010; Wallace 2006). Human errors like accidents or mistakes made by employees could also jeopardise the implementation of e-learning.
In delivering e-learning, there exists a risk referred to as student’s risk. According to Brik and Ma & Doug (2000), this risk is related to the maximum number of student users in the e-learning system required to share knowledge from that particular system. There exists the problem of a student knowing the materials delivered by the instructors, which may affect the student’s performance. In addition, too many students under a system program may be hard to teach and require additional effort to attend to each of their academic needs. Storing the student’s password and user ID has also been categorised as a student related risk. Blass & Davis (2003) note that the misuse of login information by a student jeopardises access to the system, leaving it open to unauthorised learners who may access the system. As a result, infiltration of the system has the probability of altering the security systems. There exists the risk of communication between the students and the teachers given that teachers are not always available online. In this situation, the student-teacher feedback may be affected if the students are not able to interpret the message sent.
For the e-learning system in existence, there is the risk involved in the improvisation of the entire system, which is referred to as a system developer’s risk (Yellen 2000). Changing a system is not only expensive but also extensive. This is because of different models in the market which can accommodate different models and course programs. In addition, developing, designing, and delivering e-learning depends on a high-quality database and high-end web server, quality LMS, high internet bandwidth, and robust technological infrastructure which has the capability of sustaining networked applications and multiple users without interruptions. During the installation phase, the system delivery team should be able to give an accurate cost, taking these risks into consideration so as to limit double costs. The system developer is also faced with the risk of storing students’ and teachers’ passwords safely (Blass & Davis 2003). In this time of technological advancement, the number of hackers has increased, which jeopardises the risks associated with security. Therefore, universities in Saudi Arabia should be prepared for the security risks that may jeopardise the delivery of e-learning.
E-learning comes with the risk of damaging the reputation of an institution of higher learning. This can be attributed to the fact that every university is on the verge of installing programs to offer e-learning services, not on the basis of offering education, but as a strategy of attracting students and competition. This argument is supported by Ma & Doug (2000) who note that increases in the number of students who take online courses with a particular institution can damage its reputation given that the students do not receive appropriate teaching. Bad reputation not only damages the institution but also renders the students’ degree worthless.
Learning institutions planning to adopt and deliver e-learning are faced with the risk of damaging the system process that offers vital support to the students (Ma & Doug 2000). Furthermore, standardising informal processes of learning may lead to competitive winning. According to Panda & Mishra (2007), the delivery of e-learning has been faced with a risk to quality assurance as a result of mushrooming non-accredited institutions offering university degrees. Most of the virtual programs have thrown up quality concerns, which consequently imply that the quality of online degrees has become open to doubt. Blass & Davis (2003) add that the credibility of online degrees has become questionable, given that the number of non-accredited institutions is on the verge of increasing further. Investment risk has been regarded as a major risk in delivering e-learning (Dabrowski 2006). This has been attributed to the increase in competition among different institutions of higher learning.
Countermeasures to Associated Risks
The risk associated with security can be countered through technical countermeasures which would also prevent students and instructors from falling victim to potential security accidents. Some of these measures include proper authorisation so that only approved users have access to the facilities (Kritzinger n.d, p.5). This can be achieved through the use of passwords. In addition, identification and authentication tools could be adopted for the same purpose. These tools include the use of message authentication codes, access control lists and encryption codes. In other words, having control over the e-learning environment is very important. However, Alwi and Fan (2010, p. 153) note that technical measures are limited since information systems are not designed to be fully secure. Therefore, proper management and application procedures are necessary to ensure security levels are boosted. Some technical researchers have advised that to reduce security risks, controlling access is very important.
Operation-related risks can be managed through building expertise among individuals so that they are able to tackle any unforeseeable events (Patomviriyavong et al. 2006, p.4). Other solutions include changing the number of students enrolled per semester under the same program. In addition, management could classify any problems brought about by students in order to categorise them as content, internet, and speed risks. Instructors should be fully equipped with the latest technology and knowledge of the newly implemented information systems. Furthermore, this could be improved by allowing employees to specialise in certain fields (Patomviriyavong et al. 2006, p.4). In order to avoid risks associated with malicious software and viruses, an institution of higher learning can adopt desktop virtualisation. This allows the technical team to carry out diagnostic measures as well as protect the databases from any malicious software or virus.
The issue of cultural risk could be solved by creating awareness among Saudi Arabian students. This would ensure that high turnover is realised, thus reducing cost-related risks. University members, according to Ghee (2005), can adopt the latest technology to minimise the risks associated with e-learning. This would allow the university staff and students to run e-learning programs easily and smoothly without the risks associated with technology and content. Proper strategic risks management should be developed at the university level to address any form of risk associated with e-learning (Wills & Bowles 2009).
Cost as a result of connectivity has been identified as a major risk which may hinder the delivery of e-learning in some Saudi Arabian universities. This can be solved by having subsidised internet broadband and connectivity to allow connection in universities and even in homes. The government, through collaboration with mobile service providers, could create more affordable internet connections. Most of the major risks can be solved through the use of a learning management system (LMS). According to Hussein (2011, p.44), LMS facilitates the effective delivery of e-learning as it enables students to be well attended to, and allows their performance to be recorded as well. In addition, the implementation of the Learning Content Management System (LCMS) has the potential to reduce content loss and increase content availability (Willis & Bowles, 2009; Abouzahra, 2011). LCMS implementation has the capacity of enhancing consistency in e-learning programs and courses. For instance, a well connected LMS and LCMS facilitates the availability of content and the integration of other programs which support the sustenance and availability of learning materials over the internet.
Summary of Literature Review
E-learning is a new concept in education that allows students and teachers to interact via the web or the internet. The students are able to access their assignments, course work materials, and feedback from their instructors. Based on the literature review, the concept of e-learning is very new, and there exists limited literature on the risks associated with its adoption and delivery in higher institutions of learning. Qualitative risk analysis is applied in project management to analyse risks factors qualitatively with the objective of reducing uncertainty. The most often-applied model of qualitative risk analysis is Risk Factor Analysis, which is a systematic qualitative risk analysis technique developed by the Los Alamos National Laboratory. Under RFA, four broad categories of risks applicable to e-learning are mentioned, namely: technical risks, schedule risks, cost and funding risks. All these risks are interrelated, and the presence of one leads to the rise of another. Despite the numerous benefits associated with the adoption of e-learning in institutions of higher learning, such as flexibility, easy access to education, and reduced costs in delivering education, there are some risks which are associated with the practice.
Costs, security, cultural beliefs and operation risks have been found to be some of the major risks associated with either implementation or delivery of e-learning programs. Security risk jeopardises the students’ and teachers’ passwords and login information. Other risks include investment risks, high probability of failure in the implementation of e-learning systems, systems developer risks, high costs in building learning management systems, high costs and students’ risks. Based on past studies, the failure of e-learning programs is attributed to a poor business approach, high costs in sustaining top-quality courses, and poor focus on students’ services. These can be countered through the use of technical countermeasures and proper management, awareness creation, as well as by subsidising internet broadband charges.
Research Methodology
Introduction
The methodology has been described by Collis and Hussey (2007, p.78) as the approach used in research to organise and plan the general approach in which the research goals and questions are addressed. In addition, different tasks are carried out to ensure that the research is successful since the findings and analysis depend heavily on the methodology applied. In other words, the methodology is the core of a research. According to Goddard and Melville (2001, p.1), research methodology as a process helps in answering the researcher’s unanswered questions and creating questions which did not exist in the first place. In respect to the research study, different research variables, which include risk analysis theory, shall be applied. To achieve the research aim and objectives, the mixed methods approach and an exploratory research design will be used. The collected data is relevant and related to risk assessment in e-learning in Saudi Arabian universities.
Research Design
The present study uses a mixed-methods research design, which is essentially a method for gathering, analysing and “incorporating” both quantitative and qualitative primary data at some point of the research process in an ongoing study, with the view to achieving a broad and holistic comprehension of a research phenomenon under examination (Newman & Benz, 1998). As postulated by Creswell (2002), the rationalisation for adopting a mixed-methods design for this study arises from the acknowledgement that neither quantitative nor qualitative research designs are adequate by themselves to capture the trajectories and details of the scenario, such as a compound and multifaceted issue of performing a risk analysis on the delivery of e-learning programs in universities of Saudi Arabia. Additionally, existing literature shows that both qualitative and qualitative research approaches complement each other when employed in combination (Newman & Benz 1998), hence provides a framework for more comprehensive analysis of the risk factors that influence the delivery of e-learning programs in Saudi Arabian universities.
In quantitative research, the researcher not only relies on empirical field data as the primary source of information but also employs postpositivist philosophical assertions for developing knowledge, such as the cause-and-effect paradigm, reduction to clear-cut variables or phenomena of interest, hypothesis testing, utilisation of measurements and observations, and the evaluation of existing theories (Bryman & Bell 2007). Indeed, not only does the researcher segregates variables/phenomena of interest and causally relates them to ascertain the extent and frequency of relationships (Sekaran 2006), but he/she possess discretion to establish which variables/phenomena of interest to investigate and which instruments to employ in finding answers to key research questions and objectives, resulting in extremely reliable and valid scores (Creswell 2002).
In the same vein, qualitative research involves “…an inquiry process of understanding where the researcher develops a complex, holistic picture, analyses words, reports detailed views of informants, and conducts the study in a natural setting” (Creswell 1998, p. 15). It is reported in the literature that in qualitative research method, not only does the researcher makes knowledge allegations based on the constructivist or advocacy/participatory standpoint, but he/she collects critical primary data from those immersed in everyday life of the setting or problem environment in which the study is framed (in this study, the National Centre for E-Learning and Distance Education), not mentioning that data analysis is to a large degree based on the values that these respondents perceive for the world (Mertens 2003). Ultimately, the qualitative research approach generates an adequate understanding of the problem environment based on multiple contextual factors (Creswell 2002).
A strand of existing literature (e.g., Newman & Benz 1998; Creswell 2002; Sekaran 2006) shows that the most justifiable benefit of the mixed methods research approach is that it provides the researcher with the capability to generate new knowledge based on pragmatic standpoints by establishing truth is ‘what works.’ Subsequently, the researcher has the competence to select strategies, along with variables/phenomena and units of analysis, which are most appropriate for generating a holistic response to the topic of interest. A principal precept of pragmatism is reinforced by the fact that quantitative and qualitative research approaches are compatible and, as such, both numerical and textual data, collected successfully or concomitantly in any research study, can help to comprehensively understand the main area of interest under examination (Bryman & Bell 2007; Creswell 2002). Hence, the mixed methods research approach assists the investigator to effectively conduct a risk analysis on the delivery of e-learning programs in universities of Saudi Arabia.
The present study utilises one of the most used and admired mixed methods designs known as the sequential explanatory mixed methods research design. Developed by Tashakkori & Teddlie (2003) and cited in Ivankova et al. (2006, p. 3), this research design consists of two disparate phases – quantitative and qualitative – and essentially entails “…collecting and analysing quantitative and then qualitative data in two consecutive phases within one study.”
In the quantitative section, which is the first, quantitative, numeric data was collected by means of an online-based survey/questionnaire technique. The fundamental purpose of this section was to explore and identify potential risks that directly or indirectly affect the delivery of e-learning programs in Saudi Arabian universities. Available methodology literature reveals that a survey/questionnaire technique is mostly employed when the researcher is principally concerned with descriptive, explanatory or exploratory evaluation/appraisal of the variables or phenomena under investigation (Sekaran 2006). The justification behind selecting a survey technique to gather primary quantitative data from the field was based on:
- the study was largely descriptive in nature as the respondents from NCELDE were only measured once, and
- respondents had the capacity to respond to the questionnaire instrument by way of self-report using the email medium (Sekaran 2006; Phillips & Starwaski 2008).
In the qualitative section, it is important to note that a qualitative multiple action research approach was employed by the researcher to collect text from the sampled NCELDE participants through interviews. Available literature demonstrates that “…action research is a form of applied research where the researcher attempts to develop results or a solution that is of practical value to the people with whom the research is working, and at the same time developing theoretical knowledge” (Research Methodology n.d., p. 3-6). Action research lends itself to utilisation in organisational contexts or community settings to initiate change efforts (Bryman & Bell, 2007) and, therefore, it is justifiable to use this approach in the present study as the investigator goes beyond the exploration and identification of risks that influence the delivery of e-learning programs in Saudi universities to finding alternatives and solutions and demonstrating ways to apply them with the view to reverse the trend. As noted by Meho (2006), interviews are critical in assisting the investigator in enhancing his/her comprehension of social, cultural and environmental variables and processes rather than merely produce empirical facts about the phenomena of interest and then make generalisations based on these facts.
Target Population & Sample
The target population in the present study comprises employees of the Ministry of Higher Education in the National Centre for E-Learning and Distance Learning (NCELDE) in Saudi Arabia. Additionally, it is imperative to note that part of the target population comprised personnel in the management/supervisory cadre at NCELDE. The justification behind selecting NCELDE employees is anchored on the understanding that this group of the population is well endowed with knowledge regarding the risks associated with e-learning initiatives because NCELDE acts as an oversight body for the programs in Saudi Arabia. The justification for selecting the second category of the population (managers and supervisory staff) is oriented towards the comprehension that this category of professionals possesses an in-depth understanding of the risks involved in implementing e-learning initiatives by virtue of their close proximity to communication, authority and policy-oriented structures at NCELDE.
Moving on to the sample size, it is important to note that both convenience and purposive sampling techniques were employed to select the required sample of participants. The convenience sampling procedure was employed to select a total of 65 employees of NCELDE from a pool of 350 employees of the government body. In this sampling technique, NCELDE employees were selected to take part in the study based on their convenience of accessibility and proximity to the contact person that was being used by the research for purposes of data collection within the organisation. Available literature demonstrates that convenience sampling is easy to employ, requires less time and is less costly, thus the justification for using it in this particular study. Equally, purposive sampling technique was used to select a sample of 15 managers/supervisory staff of NCELDE for purposes of data collection. Purposive sampling technique, according to Balnoves & Caputi (2001), targets a particular group of the population that appears to have a unique understanding and knowledge of the research issue under examination, thus the justification to use this approach.
The Sampling Criteria
The criteria for selecting NCELDE employees included:
- Being in active service to the Ministry of Higher Education in NCELDE for a period not less than two years;
- Must be between 21 and 45 years of age to demonstrate the dynamism of e-learning initiatives;
- Be of either sex and any racial/ethnic/religious orientation
- Must exhibit sufficient understanding of the issue under examination, and;
- Mist be ready and willing to participate in the online survey
The criteria for selecting managerial/supervisory staff of NCELDE included
- Be of either sex and any racial/ethnic/religious orientation;
- May be of any nationality, but must have worked in a managerial/supervisory capacity in NCELDE for a period not less than three years;
- Must exhibit sufficient understanding of the research issue under examination, and;
- Must demonstrate readiness and willingness to participate in the interviews.
Data Gathering Instruments
Quantitative Data
The questionnaire tool was the main instrument that was used to collect quantitative data from NCELDE employees. The questionnaire tool, which was administered online, contained a multiplicity of items of diverse layouts which included: multiple-choice items, asking either for a single response or all that applied; dichotomous responses such as “Yes” or “No”; self-evaluation and attitudinal questions, measured on the 5-point Likert-type scale, and; open-ended items projected to elicit responses that could not be captured by closed-ended items. It is imperative to mention that in the development of the questionnaire items, the investigator holistically relied on the identification of the conceptual domain and the review of related literature for the sole intention of guaranteeing the content validity of the questionnaire tool (Philips & Starwaski, 2008).
The rationales for employing the questionnaire schedule to gather quantitative data from NCELDE employees are many and varied. Existing literature shows that questionnaire schedules are effective where primary data are gathered online, as was the case in this particular study, in large part because of their ease of application and adaptability (Adams & Cox, 2008). Other advantages of using these data collection tools, as postulated by Sekaran (2006), include:
- They are cost-effective when administered to participants via online protocols;
- Most questionnaire tools consist of closed-ended questions, making it easier for the investigator to undertake a comparative analysis on each of the questions;
- The investigator is at liberty to include unstructured questions to facilitate in enquiring new information which may be previously unknown to them, or to merely explore new areas of research;
- They provide the capacity to guarantee anonymity as names/physical identities of the sampled participants are of no significance to the study, and;
- They possess the ability to attain high response rates.
Qualitative Data
The online interview tool will be the main technique employed to collect primary qualitative data from managerial/supervisory personnel at NCELDE. Extant literature demonstrates that the interview guide has traditionally been perceived as “…a qualitative research technique that involves conducting intensive individual interviews with a small number of respondents to explore their perspectives on a particular idea, program, or situation” (Boyce & Neale 2006, p. 3). With the adoption and use of technology applications, however, it is currently possible to conduct online, asynchronous, interviewing schedules – a process that entails manifold email exchanges between the investigator and study respondents over a sustained period of time (Meho 2006).
The investigator included six structured items in the interview guide for purposes of eliciting detailed and comprehensive feedback about the managers/supervisors thoughts, attitudes and perceptions, especially with regard to the risks involved in implementing e-learning initiatives in Saudi universities. The rationale for employing the interview guide to collect primary qualitative data for this study arises from the fact it is not only convenient and cost-effective when done using online protocols, but also uses less time and facilitates the investigator to have more access to the study respondents (Meho 2006).
Secondary Data
Secondary data for this particular study was gathered by undertaking a critical review of relevant literature in the field of e-learning. The review was resourcefully significant not only in identifying the current risks to the successful implementation of e-learning initiatives but also for comparative purposes aimed at developing benchmarks, strategies and policies, as well as alternatives that could be used to remedy the risks and guarantee the successful implementation of these initiatives. Available literature reveals that a comprehensive review of relevant literature is important in any research process as it represents a reflection of reality (Balnoves & Caputi, 2001).
Ethical issues
Before data collection was carried out, consent to take part in the study was sought from 80 participants from the Ministry of Higher Education in the National Centre for E-learning and Distance Learning in Saudi Arabia. Moreover, the participants were informed of the nature of the study, its goals, objectives, and why the research was being carried out. In addition, a letter from the university and a cover letter outlining the purposes of the research study was made available to the participants and to the relevant authorities.
The research Endeavour was to carry out a risk assessment on the delivery of e-learning programs in the universities of Saudi Arabia. To ensure professionalism in the research study, the researcher ensured an ethical code of conduct was followed. Ethical considerations were paramount to the study, being fully reflected in the manner in which the study was conducted: these also contributed to the reliability and credibility of the study through the provision of a debriefing process.
Prior to undertaking the research, the researcher sought consent from the participants and the Ministry of Higher Education in National Centre for E-learning and Distance Learning. The participants were given a surety that the information recorded during the data collection process was to be kept confidential and that it was not to be made available to a third party (Jackson 2008). In addition, the researcher provided a surety that privacy and anonymity were to be observed and maintained throughout the research study. Given that the information being collected from participants was original and the content not copied from any source, it was necessary to seek consent from the participants.
Explanatory letters were also sent to each of the 80 participants prior to the interviews and questionnaires. The letters were signed by the university faculty. In addition to the explanatory letters, cover letters outlining the purpose of the research, its aim and giving a surety that the research is for academic purposes were also sent. It should be noted that no participant was coerced or made to act under duress during the sample selection and interviewing process, or during the completion of the questionnaires. The participants voluntarily agreed to be part of the research and were part of the debriefing process. Before the interviews were audiotaped, the researcher sought consent to record all responses. Furthermore, the participants were assured of the possibility of having the results back to authenticate whether they conform to what was said during the interviewing process.
In terms of the secondary data used in the study, the researcher made sure that literary works making up the secondary materials were acknowledged. Academic requirements in relation to copyrighted materials were also taken into consideration to avoid plagiarism. All these ethical considerations were carried out to ensure that originality, validity, and reliability are achieved. The study sought to verify the information presented from various sources and took a methodical approach to its presentation. Lastly, the information used in the literature review and adopted during the discussion process was used to provide literal support and provide references to the information included in the dissertation paper.
Reliability and Validity of the Study
The concepts of validity and reliability are very important in a study. Threats from these two elements, as noted by Cohen et al. (2009, p.133), “…can never be erased completely; rather the effects of these threats can be attenuated by attention to validity and reliability throughout a piece of research.” Different instruments of data collection are used to address both validity and reliability. Although reliability is important in a research study, it acts as a precondition for ensuring the validity of the methodology. To begin with, validity is used to mean the extent to which an instrument used in a study measures what it was intended to measure (Miller n.d, p.3; Stemler 2001, p.7; Kirk & Miller 1986). Furthermore, it is applied in qualitative research to determine the authenticity of the collected data. Cohen et al. (2009, p.134) note that the validity of qualitative research is not concentrated in the collected data but on the meaning which attaches to the collected data. With this in mind, the researcher must be honest while self-reporting the collected data and information.
There are some principles which need to be observed for validity to exist. For example, the source of the collected qualitative data should be from a natural setting. In addition, the collected data should be descriptive and be represented in terms of the participants rather than of the researcher (Cohen et al. 2009, 134; Connaway & Powell 2010, p.61). To ensure that face validity is achieved, the researcher will ensure that the instruments used in the research, namely structured interview and questionnaire schedules, measure what they are designed to measure, which is e-learning in Saudi Arabia’s universities. Another kind of validity that will be tested in the research is content validity, which according to Miller (n.d p.3), measures the degree to which the designed instrument fully measures the domain of interest. For example, in the study, the researcher will carry out research to explore risk assessment analysis of the implementation of e-learning in Saudi Arabia. In this context and drawing on the interview research schedule, the researcher shall ensure that all the questions are fully representative of the domain under which the study was being carried out.
Reliability has been defined as the degree to which a measurement procedure is able to produce similar results if the research is repeated (Miller n.d, p.1; Thanasegaran 2009, p.35). To ensure that the collected data is reliable, the researcher shall develop openness and trustworthiness. This shall ensure that the researcher obtains the intended results from the participants. As a result, duplicability could easily be achieved. Furthermore, the sampling technique adopted will ensure the reliability, since random sampling gives an equal chance to each individual in a population. The data to be collected is believed to be sufficient to facilitate adequate data analysis, thus enhancing the reliability of the research findings.
Data Analysis
Quantitative data arising from the questionnaire schedules were first cleaned and coded before being entered into a statistical package known as SPSS for Windows for analysis and interpretation of the results. The researcher used the statistical package to run univariate analyses (descriptive statistics of mean, median, mode, and standard deviation) aimed at exploring and identifying the risks involved in the delivery of e-learning programs in universities across Saudi Arabia. Frequency distributions and cross-tabulations were also used to identify the occurrence of the risks. The resultant data were further harnessed, analysed and presented using frequency polygons, bar charts, pie charts and text to make them easily understandable to the reader. Qualitative data received from the open-ended items in the questionnaire schedules were categorised, coded, and entered into the statistical program using the exhibiting themes (Sekaran 2006).
Qualitative data arising from the structured interview guides were analysed using content analysis – a process that reduces qualitative information to numerical terms and lends it to quantitative analysis by virtue of the fact that the researcher employed structured interview guides (Smith & Firth 2011). Consequently, the researcher developed some coding units to categorise the qualitative data in the questionnaire, along with some predominant themes that could be used to provide responses to the main research objectives for this study.
Data Analysis
Introduction
The present study is focused on the urgent need for educational institutions operating in Saudi Arabia to identify risk assessment procedures that influence the successful implementation of e-learning programmes. Towards the actualisation of this broad objective, an online survey was conducted on a sample of 65 employees of the National Centre for E-Learning and Distance Education (NCELDE). An online interview was also conducted targeting 15 managerial/supervisory staff of NCELDE with the view to developing a comprehensive understanding of what of the various risks that influence the successful implementation of programmes in e-learning environments. This section purposes to detail the findings of the two exercises. To adopt the normal tradition of the mixed-methods research approach, the quantitative findings derived from the questionnaire schedules will be presented separately from the qualitative findings derived from the structured interviews. It is important to note that the investigator received 52 completed questionnaires from NCELDE, representing 80% response rate. Equally, the investigator was able to conduct 13 interviews to their logical conclusion, representing 86.7% response rate.
Statement of Results (Questionnaire)
The main highlights of the study findings are not only interesting but informative too, especially with regard to identifying and understanding the various risks that are associated with the delivery of e-learning initiatives in universities of Saudi Arabia. A critical analysis of demographic data demonstrates that many of the employees sampled (68.5%) were yet to celebrate their 40th birthday, and only a handful of the employees (8.2%) were past 50 years of age. Two in every three NCELDE employees sampled for the study (65.5%) had been in active employment at the Ministry of Higher Education agency for a period not less than four years, implying that they were well versed with issues affecting e-learning programmes in Saudi Arabia. A major research finding is that many participants felt that e-learning initiatives must be perceived as useful by participants (42.3%), and that e-learning initiatives must provide opportunities for success – not failure or uncertainty (38.8%) when asked what could be done to make e-learning initiatives compelling to both educational institutions and students. The rest of the distribution is demonstrated in Fig 2 below.
Importance of Perceived Risks
When asked to identify the most common source of risks that may affect the delivery of successful e-learning activities in universities across Saudi Arabia, the three most common causes identified by the participants were technical issues (58.2%), human issues (52.4%), and cultural issues (47.3%). The researcher employed a 5-point Likert-type scale to evaluate some critical issues that had been highlighted in the literature as forming the top-most risks on the delivery of e-learning programs in Saudi universities. These issues are directly related to the slow uptake of e-learning initiatives in Saudi Arabia and include insufficient human resources; unrealistic schedule and budget; unrealistic expectations; incomplete requirements, and; diminished window of opportunity owing to late delivery of software, among others. Descriptive means were used to demonstrate how NCELDE employees rated the perceived risks in terms of their importance. As suggested above, a 5-point Likert-type scale was employed to rank the responses, with one representing “highly disagree” and five representing “highly agree.” Table 1 below summarises the results.
Table 1: Descriptive Means of Top-Most Risks on the Delivery of E-Learning.
This descriptive analysis clearly demonstrates that the five most influential risks to the successful implementation of e-learning initiatives in universities of Saudi Arabia, in decreasing order of importance, are: 1) poor leadership from the project manager or steering committee, 2) poor quality of staff at the university to roll out e-learning programs, 3) insufficient human resources, 4) unrealistic schedule and budget, and 5) incomplete requirements. An interesting observation from this analysis is the fact that very few participants think that redundant software in the market, as well as poor production system performance, contributes significantly to the delivery of e-learning programs in Saudi universities despite extant literature demonstrating to the contrary. Interestingly, eight in every ten participants (81.7%) felt that good project management was the most appropriate approach that can be used by universities to deal with risks in e-learning programs because many risks emanate from poor leadership approach.
Ranking Risks in terms of Likelihood, Impact and Onset
The participants were then asked to rank several predetermined risks in terms of likelihood, impact and onset. The researcher believed that this information was critical in the risk preparedness and the adoption of risk mitigation strategies. It is important to note that an estimated two-thirds (65.2%) of the sampled population thought that insufficient or uncertain human resources to run the e-learning initiatives represented a high likelihood, high impact risk with a fast-paced offset, while two-fifths (41.2%) felt that technical representation or solutions reached or exceeded represented a high likelihood, high impact risk but with a slow onset. Equally, 40.2% of the population felt that poor partnership working in e-learning projects represented a high likelihood, high impact risk for universities across Saudi Arabia, but with a slow onset, while unrealistic expectations and programme sustainability issues were found to represent high likelihood, high impact risks with slow onset by 38.6% and 35.2% of the participants, respectively. The rest of the distribution is shown in figure 3 next page.
From the above figure, it is clear that the three most high-likelihood, high-impact risks associated with the delivery of e-learning programs in universities of Saudi Arabia, in decreasing order of intensity include: poor/inadequate leadership (70.5%), insufficient/uncertain human resources (65.2%), and technical limitations (41.2%). Equally, it is important to note that failure to meet technical standards adequately is considered a low likelihood risk but with a high impact on e-learning initiatives by almost two in every three (65.4%) respondents. Lastly, from the analysis, it is evident that most institutions of higher learning in Saudi Arabia have put in place adequate mechanisms to deal with resistance to change as only 15.3% of the participants felt that lack of formal change management processes in universities constituted a low-likelihood, low-impact risk to the delivery of e-learning programs at the universities.
For comparative reasons, respondents were asked to name and rate other risks that they thought affected the delivery of e-learning programmes in universities across Saudi Arabia. About seven in every ten respondents (72.3%) said unreasonable project schedule and budget was a high likelihood risk in Saudi Arabian universities, but the risk had a low impact and slow onset. Equally, harmful competitive practices were selected as a high likelihood risk but with low impact and slow onset by an estimated two-thirds (64.2%) of the respondents. The rest of the distribution is demonstrated in figure 4 below.
It appears from the above presentation that although the twin risks of poor quality assurance and poor evaluation can still present in the delivery of e-learning programs in universities across Saudi Arabia, there is a low likelihood for these risks to appear, not mentioning that they have a low impact on e-learning programs. However, the other four risks (failure to satisfy set regulatory standards; contract negotiation and management; unreasonable project schedule and budget, and; harmful competitive actions) have a high likelihood of happening in Saudi universities though with varied impacts on e-learning initiatives.
Managing the Risks and Management Processes
The study participants were asked to select the most appropriate actions that could be used to manage the listed risks once they present. They were provided with three predetermined options, namely: Treat the risk; transfer the risk, and; terminate the activity. Figure 5 below presents the responses.
The figure above clearly demonstrates that many respondents thought that it was important to treat the risks related to unrealistic schedule and budget (90.2%); poor quality of staff (82.4%); unrealistic expectations (82.4%); poor leadership (80.2%); poor production system performance (75.2%): incomplete requirements (76.3%); friction between clients and contractors (70%); continuous changes to requirements by clients (62.6%), and; lack of agreed-to user acceptance testing or signoff (62.4%). Equally, many participants felt that it was important to terminate the activity in the event that e-learning programs were faced with redundant software (70.2%) and inadequate third party performance (62.3%). Lastly, a majority of the respondents felt that it was important to transfer the risk to the delivery of e-learning initiatives if the universities were faced with the reduced window of opportunity due to late delivery of software (82.4%) and inadequate user documentation (56.2%).
Lastly, the researcher used a 5-point Likert-type scale to evaluate the most appropriate project management process that could be used to manage the listed risks. The processes had been drawn from extant literature and include scope/quality management; communication management, and; human resource management. Descriptive means were used to demonstrate how NCELDE participants ranked the most appropriate project management processes to manage the listed risks. As indicated above, a 5-point Likert-type scale was used to rank the responses provided by the participants, with one representing “highly disagree and five representing “highly agree.” Table 2 next page summarises the results.
Table 2: Descriptive Means of Most Appropriate Project Management Processes to Manage Listed Risks.
From the descriptive means above, it is evident from the responses that some risks can be managed well by only one process while others can be managed comfortably by two or all the three processes. For instance, while respondents strongly agree with the fact that insufficient/inadequate human resources can only be managed well by the human resource component of the educational institution providing e-learning initiatives, the same respondents strongly agree that the risks of poor leadership and poor quality staff can be best managed by the employment of all the three processes – quality management, communication management, and human resource management. Equally, most respondents either “agree” or “strongly agree” that some risks such as friction between clients can be managed by two processes – communication management and human resource management.
Statement of Results (Interview Guide)
A number of themes were generated when the 13 interviewees (management personnel and supervisory staff at NCELDE) were asked to elucidate their viewpoints and perspectives regarding the risks facing the delivery of e-learning programs in universities across Saudi Arabia. All the 13 interviews understood well what e-learning entails, with the majority of them saying that e-learning entails using electronic media in the process of transferring and delivering information between the teacher and the learner through the use of computers, networks and multimedia. A small section of the interviewees described e-learning as a subset of distance learning that entails the delivery of content through electronic media. Indeed, one interviewee said that e-learning entailed “teaching by using modern communication mechanisms of the internet, as well as other internet-based portals and the adoption of the principle of self-learning or teacher-assisted learning” Overall, the interviewees demonstrated a comprehensive understanding of e-learning initiatives in Saudi Arabia.
Various responses were received when the interviewees were requested to state their thoughts about a probability of a risk occurring in an e-learning context, and the researcher took time to group the themes around two thematic predispositions – long-term and long-term risks. The risks that were grouped under the long-term thematic orientation included: Personnel shortfalls (insufficient human resources); unrealistic expectations; diminished window of opportunity due to late delivery of software; continuous changes to requirements by the client; poor production system performance, and inadequate third party performance (contractor not fit for purpose). Equally, the risks that were grouped under the short–term thematic orientation included: inadequate user documentation, lack of agreed-to user acceptance and signoff criteria; application (software) not for the purpose; friction between clients and contractors; poor quality of staff; software no longer needed; incomplete requirements; unreasonable project schedule and budget, and poor leadership (project manager or steering committee).
A number of themes also generated when interviewees were requested to name some of the most used risk treatment strategies for the risks that they had already identified. Table 3 demonstrates the themes.
Table 3: E-Learning Risk Treatment Strategies.
Lastly, the interviews were requested to detail how they manage the risks that affect or influence e-learning programmes in universities across Saudi Arabia. Again, the responses were grouped into underlying themes, with most of the most prevalent themes being summarised below.
- The full development of rehabilitative programs to help employees to understand the risks.
- Direct support and guidance from the government for e-learning projects.
- Search for resources and off-campus laboratories such as self-study computer areas, and articles on the internet.
- Establishment of a centre to support staff and young professionals in the field of computers and take advantage of their skills.
- Continued support and translation of software that is in English. It is necessary to maintain purchase programs and the learning management system, which usually are supported in English to minimise the costs of procurement.
- Ask Direct supervision and support from Saudi Network Information Centre (SaudiNIC) to support network of e-learning, which is responsible for the administration of the domain name in Saudi Arabia, and operation of the Saudi DNS root servers and the registry services under Saudi TLDs to reduce the operational risks, which come as a result of security breaches or issues.
- Support the speed of the internet and its activation in all parts of Saudi Arabia.
- Training in academic skills and research methods.
- Commitment to the timetable set for the completion of the implementation of the project according to specifications and at a reasonable cost in order to achieve a reasonable return on e-learning away from risk
Interpretation of Results
Introduction
The initial objective of the present study was to critically undertake a risk analysis on the delivery of e-learning programs in universities of Saudi Arabia. A strand of existing literature (Dabrowski 2006; Ganga & Ricketts 2007; Joubert & Wishart 2012) have already been done to look into the risks associated with the delivery of e-learning programs in western countries, but only a few have been interested in establishing the scope of the problem in Saudi Arabia. Below, the researcher attempts to discuss and interpret the results of this study based on the initial objectives.
Identifying Risks to E-Learning Initiatives through Analysing Available Literature
Extant literature analysed in this study has identified numerous risks that influence or affect the effective delivery of e-learning initiatives. Overall, the risks identified include insufficient or uncertain human resources; technical limitations of solutions reached or exceeded; poor partnership working; project sustainability issues; unrealistic expectations, poor leadership; litigation in protecting intellectual property rights; application (software) not fit for the intended purpose; failure of the e-learning initiatives to meet the intended technical standards; lack of formal change management process; unrealistic schedule and budget; diminished window of opportunity owing to late delivery of software; poor production system performance, and; continuous changes to requirements by the client (Joubert & Wishart 2012; Wallace 2006; Blass & Davis 2003). As noted by Mo & Doug (2000), all these risks are intrinsically intertwined in such a way that the presence of one risk creates room for the other. Cassel (2002) highlights some of the risks experienced in e-learning, such as poor leadership, intellectual property rights, unrealistic expectations, sustainability issues, poor partnership working, insufficient human resources, and technical limitations, among many others
Extant literature, as demonstrated by Cassel (2002), shows that these risks are mostly caused by technical, human, economic, as well as cultural causes. For instance, funding risk (economic), which may result from underfunding, leads to increase in cost overheads, which is an example of cost risk. The technical/operational risks are associated with the systems, adoption of new technology, training employees, satisfying all clients, among others. As noted by Blass & Davis (2003), technical risks expose the whole system to risks, which may affect the whole project, to performance and operational risks which may jeopardise the whole mission of a project. Extant literature also demonstrates that operational risks are associated with processes, people, technological elements, and content. It is imperative to note that Content risks are those which occur during the preparation of coursework. This includes the risk of having low content, which may not be enough to cater for the increased number of students in Saudi Arabia [Yellen 2000)
Equally, Ma & Doug (2000) note that Human beings are employed to run e-learning facilities. Humans are also prone to mistakes, not to mention that different people have different levels of knowledge and skills. Therefore, it may be hard for an instructor who is not well trained to conveniently address over 40 students if by any chance, they ‘log in’ simultaneously. Lack of skills can jeopardise full execution and implementation of e-learning in Saudi universities.
Assessment of E-Learning Risks by NCELDE Employees & Managers
The study findings have availed comprehensive data on how employees and managers of NCELDE assess the risks as they affect the delivery of e-learning programmes in Universities across Saudi Arabia. For instance, it has been demonstrated that risks such as insufficient/uncertain human resources to learn the e-learning initiatives in universities of Saudi Arabia, along with poor partnerships and unrealistic expectations, represents high-likelihood and high-impact risks that have the capacity to jeopardise the provision of e-learning initiatives in the country. Available literature demonstrates that risk assessment allows the project management team to evaluate the likely risks as well as the sources of those risks before a project has commenced (Blass & Davis 2003), and is carried out to identify, estimate and evaluate risks associated with undertaking a particular project (Ma & Doug 2000; Panda & Mishra 2007; Ganga & Ricketts 2007).
The findings from NCELDE employees are categorical that the top high-likelihood, high-impact risks associated with the delivery of e-learning programs in universities of Saudi Arabia, in decreasing order of intensity include: poor/inadequate leadership, insufficient/uncertain human resources, and technical limitations. Equally, it is important to note that failure to meet technical standards sufficiently is considered a low likelihood risk but with a high impact on e-learning initiatives conducted by universities in Saudi Arabia. It is also important to note that most institutions of higher learning in Saudi Arabia have put in place adequate mechanisms to deal with resistance to change as very few participants felt that lack of formal change management processes in universities constituted a low-likelihood, low-impact risk to the delivery of e-learning programs at the universities. These findings can collaborate in other studies (e.g., Ganga & Ricketts 2007; Joubert & Wishart 2012; Wallace 2006), which suggests that insufficient/uncertain human resources, technical limitations, poor partnerships among collaborators, project sustainability issues, as well as poor project leadership, constitute high likelihood risks with high impacts on the effective delivery of e-learning programmes.
The findings from NCELDE managerial/supervisory staff demonstrates that long-term risks in the delivery of e-learning initiatives in Saudi Arabian universities include: Personnel shortfalls (insufficient human resources); unrealistic expectations; diminished window of opportunity due to late delivery of software; continuous changes to requirements by the client; poor production system performance, and inadequate third party performance (contractor not fit for purpose). On the other hand, short-term risks, as revealed by the managers and supervisors during the interview, include inadequate user documentation, lack of agreed-to user acceptance and signoff criteria; application (software) not for the purpose; friction between clients and contractors; poor quality of staff; software no longer needed; incomplete requirements; unreasonable project schedule and budget, and poor leadership (project manager or steering committee). These observations are reinforced by Joubert & Wishart (2012), who suggest that it is important to categorise the risks as long-term or short-term not only to initiate early warning signs of the risks involved but also in devising evasive manoeuvres and preparation of recovery plans.
Identification of Possible ways to Treat Risks
The findings brought to the fore critical knowledge that it is indeed possible to manage some risks, such as insufficient/inadequate human resources, by employing the human resource component of the educational institution providing e-learning initiatives. Equally, some risks such as poor leadership and poor quality staff can be best managed by the employment of all the three processes – quality management, communication management, and human resource management. The present study came up with very many risk treatment strategies for the various risks that affect the delivery of e-learning programs in Saudi Arabia. For instance, the high likelihood, high-impact risks of poor project leadership can be treated using the established communication and escalation hierarchy, as well as by establishing a steering committee selection process and operational guidelines.
Equally, the high likelihood high-impact risks of poor quality staff and personnel shortfalls, according to the interviewees, can be treated by changing project management objectives, procuring external parties, planning for available resources, planning contingency options, and assessing project staff capability. This view is reinforced in the literature by Ma & Doug (2000), who suggests that risks involving human resources and shortage of staff are best-ameliorated planning available resources, training of personnel, and outsourcing to qualified external parties. A strand of existing literature (e.g., Blass & Davis 2003; Panda & Mishra 2007; Dabrowski 2006) also demonstrates that e-learning risks such as insufficient human resources, poor leadership, sustainability issues, unrealistic expectations, and poor quality of staff should be treated rather than terminated or diverted to other avenues. This view has been well represented in the study findings.
Conclusions & Recommendations
Conclusions
The present paper illuminated some prominent findings within the broad area of risks associated with the delivery of e-learning programs in universities of Saudi Arabia. First, it has been demonstrated that the identification of potential risks and adopting appropriate actions is a critical challenge facing e-learning project managers, not only in Saudi Arabia but also globally. The comprehensive review of extant literature identified numerous risks associated with the delivery of e-learning programmes. However, it would be plausible to mention that some risks were mentioned repeatedly by the study participants, and hence the investigator perceived these risks to be most critical to the delivery of e-learning initiatives in universities across Saudi Arabia. These risks include unrealistic expectations; unreasonable project schedule and budget; insufficient human resources, and; poor leadership. Three other risks viewed as of paramount significance in the Saudi Arabian context included incomplete requirements, lack of agreed-to user acceptance testing and signoff criteria, and software which was no longer needed. The need for awareness of these risks among e-learning managers should, therefore, be emphasised.
Second, it can be concluded that the common project management processes for highly ranked risks in universities across Saudi Arabia include quality management, communications management and human resource management. While some risks could be effectively managed by one management process, other risks, including poor leadership and poor quality staff, demanded the intervention of two or all the three management processes. Of importance here is the fact that the study results demonstrated that project management strategies could be applied to the management of risks. Therefore, e-learning project managers should give more attention to project management as a strategy for managing the most risks. The results reported can be used as guidance to significant risks and the different treatment strategies that e-learning project managers should consider for effective risk management.
Lastly, the present study has contributed immeasurable knowledge in categorising and ranking the risks affecting the delivery of e-learning initiatives in universities across Saudi Arabia. Through the study, it is now known that some risks, such as insufficient/uncertain human resources and technical limitations, have a high likelihood of happening in the Saudi context, leading to devastating effects due to their high impact and speedy onset. Such knowledge is fundamental not only to allow project managers to institute remedial measures but also to be adequately prepared with alternatives.
Recommendations
Several recommendations arise from the study findings. First, Saudi universities need to start educational and awareness campaigns to assist employees in understanding the risks associated with e-learning programmes. Educational programmes will go a long way in dealing with the risk of poor quality staff. Additionally, it is recommended that the Saudi government should start supporting and guiding e-learning initiatives in the country through direct funding and the provision of highly trained professionals to move the e-learning agenda forward. The government also need to subsidise internet costs and other mechanisms that will lead to an increase in the adoption of technology in institutions of higher learning. The establishment of a centre and support staff for e-learning activities in Saudi Arabia may also serve as an important milestone in the pursuit of furthering the delivery of e-learning activities in the country and beyond. Lastly, educational institutions need to be on the forefront in developing technical and support teams that will identify risks and address them before they can become a liability to the delivery of e-learning programs in universities of Saudi Arabia.
Reference List
Aboulfaraj, WH, Jomoah, IM & Hassan, MH 2009, Corporate e-learning practices: Opportunities for university administration, Web.
Abouzahra, MM 2011, Building the e-learning system in King Saud University – A system perspective, Proceedings of the World Congress on Engineering and Computer Science 2011, vol. 2, Web.
Adams, JGU 1995, Risk, UCL Press. London.
Adams, A & Cox, AL 2008, Questionnaires, in-depth interviews and focus groups, Open Research Online, Web.
Alghamdi, A 2012, Transforming learning systems through e-learning, Web.
Aljabre, A 2012, ‘An exploration of distance learning in Saudi Arabian universities: Current practices and future possibilities’, International Journal of Business. Humanities and Technology, vol. 2 no. 2, pp. 132-136.
Al-Shehri, A.M 2010, ‘E-learning in Saudi Arabia: To E or not to E, that is the question’, Journal of Family & Community Medicine, vol. 17 no. 3, pp. 147-150.
Alwi, NHM & Fan, I 2010, ‘E-learning and information security management’, International Journal of Digital Society, vol. 1 no. 2, pp. 148-156.
Balnoves, M & Caputi, P 2001, Introduction to quantitative research methods: An investigative approach, Sage Publications Ltd, Thousand Oaks, CA.
Blass, E & Davis, A 2003, ‘Building on solid foundations: Establishing criteria for e-learning development’, Journal of Further & Higher Education, vol. 27 no. 3, pp. 227-231.
Boyce, C & Neale, P 2006, Conducting in-depth interviews: A guide for designing in-depth interviews for evaluation input, Path Finder International Tool Series, Web.
Bryman, A & Bell, E 2007, Business research methods (2nd ed.), Oxford University Press, Oxford.
Cassel, R.N 2002, ‘Faulty accreditation of distant learning programs threatens to destroy our present education systems’, Education, vol. 122, no. 4, pp. 680-691.
Cohen, L, Manion, L, Morrison, K & Morrison, KRB 2009, Research methods in Education, Routledge, New York.
Collis, J & Hussey, R 2003, Business research: A practical guide for undergraduate and postgraduate students, Palgrave Macmillan, Hampshire.
Connaway, LS & Powell, RR 2010, Basic research methods for librarians, Libraries Unlimited, Santa Barbara.
Creswell, J.W 2002, Educational research: Planning, conducting, and evaluating quantitative and qualitative approaches to research, Merrill/Pearson, Upper Saddle River, NJ.
Dabrowski, M 2006, ‘E-learning initiatives in an academic environment – Case study of Warsaw School of Economics (WSE), Dialogue & Universalism, vol. 16 no. 3/4, pp. 73-80.
Ganga, SO & Ricketts, IW 2007, ‘Facing the challenges of e-learning initiatives in African universities’, British Journal of Educational Technology, vol. 38 no. 5, pp. 896-906.
Ghee, P 2005, The academic quality handbook: Enhancing higher education in universities and further education colleges, Routledge, London.
Goddard, W & Melville, S 2001, Research methodology: An introduction, Lansdowne, Juta.
Hussein, HB 2011, ‘Attitudes of Saudi universities faculty members towards using learning management system’, The Turkish Online Journal of Educational Technology, vol. 10 no. 2, pp. 43-53.
Ivankova, NV, Creswell, JW & Stick, SL 2006, ‘Using mixed-methods sequential explanatory design: From theory to practice’, Field Methods, vol. 18 no. 1, pp. 3-20.
Jackson, S.L 2008, Research methods: A modular approach, Cengage Learning, London.
Joubert, M & Wishart, J 2012, ‘Participatory practices: Lessons learnt from tow initiatives using online digital technologies to build knowledge’, Computers & Education, vol. 59 no. 1, pp. 110-119.
Kapp, MK n.d., Advantages of e-learning, Web.
Kirk, J & Miller, ML 1986, Reliability and validity in qualitative research, Sage Publications, Beverly Hills.
Kritzinger, E n.d., Information security in an e-learning environment, School of Computing, University of South Africa.
Ma, LV & Doug, WG 2000, ‘Will virtual education initiatives succeed?’ Information Technology & Management, vol. 1 no. 4, pp. 209-227.
Meho, LI 2006, ‘E-mail interviewing in qualitative research: A methodological discussion’, Journal of the American Society for Information Science and Technology, vol. 57 no. 10, pp. 1284-1295.
Mertens, DM 2003, Mixed methods and the politics of human research: The transformative-emancipatory perspectives. In: A. Tashakkori & C. Teddlie (eds.), Handbook on mixed methods in behavioral and social sciences, Sage Publications, Thosand Oaks, CA.
Miller, MJ n.d., Reliability and validity: Graduate research methods, Western International University.
Newman, I & Benz, CR 1998, Qualitative-quantitative research methodology: Exploring the interactive continuum, Southern Illinois University, USA.
Panda, S & Mishra, S 2007, ‘E-learning in a mega open university: Faculty attitude, barriers and motivations’, Educational Media International, vol. 44 no. 4, pp. 323-338.
Papanikolaou, K & Boubouka, M 2010, ‘Promoting collaboration in a project-based e-learning context’, Journal of Research on Technology in Education, vol. 43 no. 2, pp. 135-155.
Patomviriyavong, S, Samphanwattanachai, B & Suwannoi, T 2006, ‘E-learning operational risk assessment and management: A case study of the MSC in management program’, International Journal of the Computer, vol. 15 no. 1, pp. 34-57.
Phillips, PP & Starwaski, CA 2008, Data collection: Planning for and collecting all types of data, John Wiley & Sons, London.
Research methodology n.d., Web.
Sekaran, U 2006, Research methods for business: A skill building approach (4th ed.), Wiley-India, Mumbai.
Smith, J & Firth, J 2011, ‘Qualitative data analysis: The framework approach’, The Nurse Researcher, vol. 18 no. 2, pp. 52-62.
Stemler, S 2001, ‘An overview of content analysis’, Practical assessment, Research & Evaluation, vol. 7 no. 17, p. 7-14.
Thanasegaran, G 2009, Reliability and validity issues in research, Web.
Wallace, M 2006, ‘An investigation into copyright concerns as a barrier to the widespread development of e-learning practice within Scottish further education colleges’, Information & Communications Technology Law, vol. 15 no. 1, pp. 79-119.
Wills, S & Bowles, K 2009, An evolutionary approach to strategic planning for e-learning, First International Conference of e-Learning and Distance Learning, Web.
Yellen, RE 2000, ‘Reaching the future information systems worker with distant learning’, Journal of End User Computing, vol. 12 no. 4, pp. 29-36.
Appendices
Appendix 1: Introductory/Explanatory letter
Name of the University (………………)
Address (……..)
Date (……………)
Name of the student/researcher (……………)
Address (………..)
RE: Consent for research
My name is (…………..), and I hereby seek your consent to conduct research on including risk assessment related to delivery of e-learning in Saudi Arabia’s universities. The findings will be used for academic reasons and for ethical reasons confidentiality and anonymity will be observed. Your participation will be highly appreciated
With Regards
Appendix 2: Authorization cover letter
Institution
Address
Date
RE: Research Approval
This is to confirm that (name of the student) has been approved by the (name of university/college) research board to carry out research. Your assistance to the student will be highly appreciated.
Name of the Faculty Advisor: ………………….
Faculty Advisor’s e-mail address: ………………….
Department, School, or Programme: ………………….
______________________________
Student’s Signature
Date_________________________________
Signature of Faculty Advisory
Date
Appendix 3: Questionnaire Schedule
Hello, my name is
, from
University. This data gathering exercise is in response to the fulfillment of my academic requirements in
University. I kindly want to request for your engagement in completing this survey to assist the researcher have a better understanding on the risks that affect or influence the delivery of e-learning programs in universities of Saudi Arabia. Specifically, the researcher is seeking to understand how the risks are assessed and ranked, and how they are treated to facilitate the smooth delivery of e-learning programs.
N.B: The survey will take between 20 and 35 minutes to complete, and is exclusively voluntary. The researcher would like to take this opportunity to assure all participants that information provided will be kept and treated in strictest confidence
Section A: General Demographic Information
- Age………………………………
- Which section/department of the company do you work in…………………..
- How many years have you been in active employment
- Less than one year
- 1-<3
- >3-<5 >5-<7
- 7+
- In your view, what could be done to make e-learning initiatives compelling to both educational institutions in Saudi Arabia as well as students (You can tick more than one)
Section B: Risks to E-Learning
- What is trhe most common sources of risks associated with e-learning initiatives? (Please select one).
- Economic factors
- Cultural factors
- Technical factors
- Human issues
- Other (please specify)………………………………………………………………………………….
- Please indicate the level to which you agree or disagree with the following risks in terms of their importance in affecting the delivery of e-learning initiatives in universities across Saudi Arabia
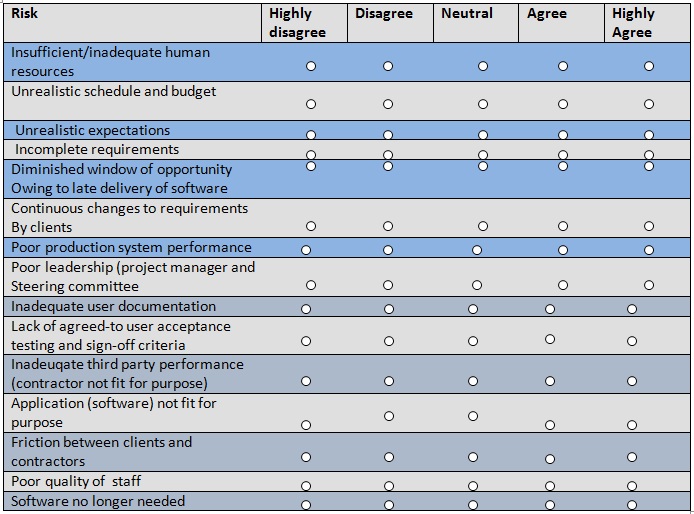
-
- Please rank the risks stated below in terms of likelihood, impact and onset (H=High; L=Low)
Please tick which is the most appropriate treatment strategy for the listed risks (Please tick one treatment strategy per risk)
-
- By ticking the appropriate checkbox, please indicate the level to which you agree or disagree with the usefulness of the stated project management processes in managing the listed risks (1= Highly disagree; 5= Highly agree)
Appendix 4: Interview Guide
Hello, my name is … , from … University. This data gathering exercise is in response to the fulfillment of my academic requirements in
University. I kindly want to request for your engagement in undertaking this interview to assist the researcher have a better understanding on the risks that affect or influence the delivery of e-learning programs in universities of Saudi Arabia. Specifically, the researcher is seeking to understand how the risks are assessed and ranked, and how they are treated to facilitate the smooth delivery of e-learning programs.
N.B: The interview will take between 20 and 35 minutes to complete, and is exclusively voluntary. The researcher would like to take this opportunity to assure all participants that information provided will be kept and treated in strictest confidence