Background
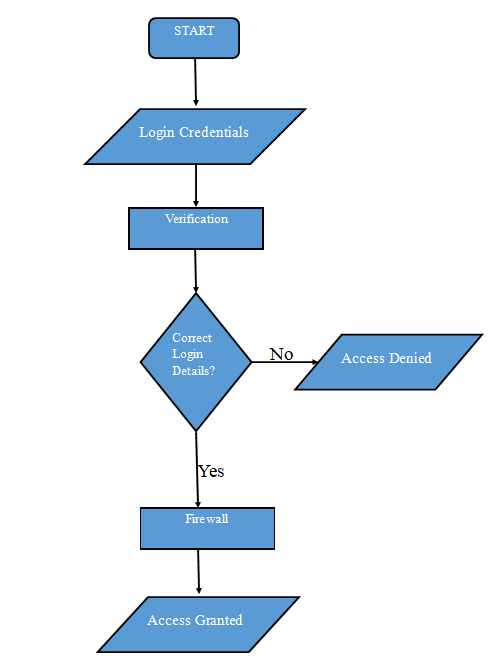
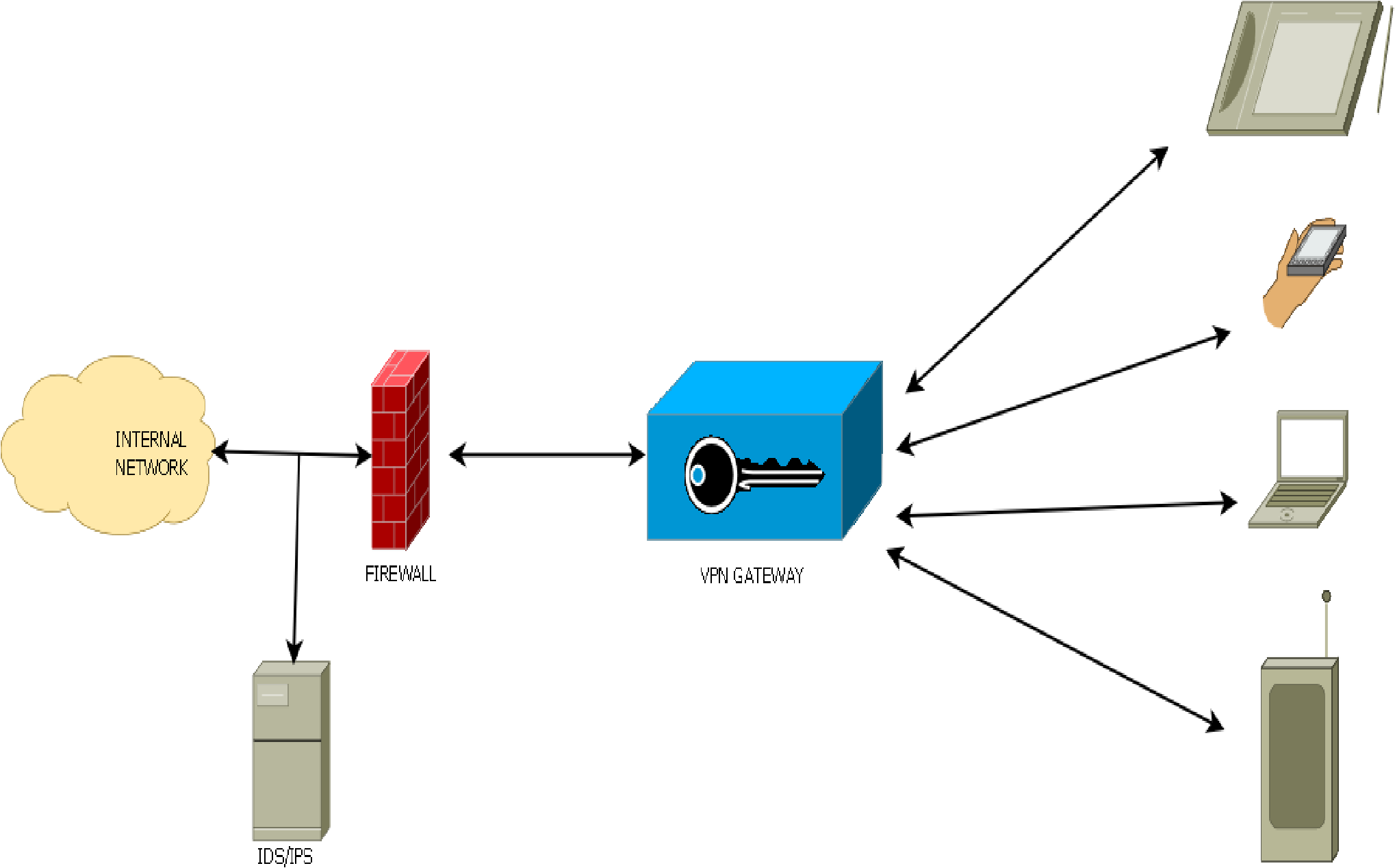
Data is accessed every day by several persons, each with different needs. Numerous factors contribute to the security of data and networks. By establishing a well-conceived security strategy that addresses the most vital parts of the danger, it will be possible to minimize data loss and corruption. Hardware safety measures like firewall protection for the network must be established at the outset. People who need to access the government agency network securely must be assigned a secure password and identification. When citizens rely on the government’s networks every day, the government agencies must implement protocols for identification and create rules for each communication link. All communications must be encrypted, so the relevant authority can detect inappropriate usage and take appropriate action. The figures below demonstrate how clients will connect to the agency’s systems.
Equipment List of Network Security Devices
Vendor Brands per Each Device and the Associate Costs
Anti-Malware, mobile device management, intrusion detection, and prevention systems are just a few examples of network security devices that can be used to protect the integrity and sensitivity of private information. Powerful weapons are required to battle and eliminate cyber threats, and the cyberweapons outlined here need to be used to monitor the network management systems (Hassija et al., 2019). The start price for Cisco’s equipment is approximately $8,000, whereas the starting price for Internet Security Systems, Inc. is approximately $8,995 per permanent license (Cisco Firewalls, 2020). McAfee’s Anti-malware plan starts at $24.99 and increases to $69.99 (McAfee, 2021). Microsoft’s Intune Enterprise Mobility + Security provides a combination of administrative capabilities and security for mobile devices going from $10.60 to $16.40 per user for each month (Enterprise Mobility and Security Pricing Options, 2021). These prevention security systems might be slightly expensive, but they provide services that are worth their prices.
The Functionality of Each Device and Their Expected Benefits
Installing Cisco’s IDS/IPS system will give a multi-pronged defense for a company’s network, including outside and inside network security because Cisco’s security system is networked and controlled. The agency would detect and respond to data-center attacks, providing a stable defense against any cyberattacks. Protection from data encryption on devices used by company staff ensures the avoidance of a company data breach caused by data accidentally leaked into a company’s system. However, Intune MDM can keep field agents safe by implementing encryption and pin security controls with no requirement for a complete device-level takeover (Kemper, 2019). This will ensure employees do not feel insecure about any cyber-attack while handling any government information
Maintenance Plan
It is necessary to create security controls during the different stages of an information system’s lifecycle. This includes the creation of those controls during both the development and maintenance processes. It is vital to create security strategies and documentation for every data framework, as they have varying security needs and dangers because of the risk of having data access unpermitted. Secondly, simulations of real information must be used to test the systems thoroughly. However, tests must be performed with caution since it’s critical not to compromise data integrity and security. For testing that utilizes existing information or personal data, adequate security measures should be in place. Processes that use data should undergo vulnerability assessments on an occasional basis. If vulnerability warnings come from manufacturers or other parties, those reports should be evaluated to determine the appropriate level of network security.
On the other hand, to clarify what makes the system compliant with the regulations, the document should describe any exemptions or exceptions and the policy of the product’s functionality. It’s important to check the information system constantly to make sure everything is working properly. The continual control method must include the processes for the information design and its main parts and the continuous safety examinable assessment to recognize the network system’s weaknesses to attacks. In addition, companies should devise plans that accommodate their overall purpose should data get compromised. System updates should be executed more often to keep everything running smoothly.
Risks Associated with Maintenance Activities and Specific Activities and Resources Required
The recommendations listed above are intended to help system administrators improve the overall security of their systems. As a result, failure to carry out the actions outlined in the maintenance plan may result in the loss of or unauthorized access to private information. The abuse of such information, inadequate execution of security measures, and the creation of new risks can also result from system modification. To ensure that data is safeguarded through encryption, the maintenance plan must be followed.
Physical Security Measures
When working with data, one critical thing to consider is how crucial it is to keep data accurate and avoid leaking sensitive information. In this regard, it is necessary to deploy security equipment that provides privacy protection and the integrity of personal information. This will keep sensitive information protected and make sure anyone who changes it is permitted to do so. It also detects any data corruption on the way through, and therefore the legitimacy of the data will be ensured. The following physical security measures ensure security to the electronic assets:
- Electronic Access Controls: This is the department responsible for putting in place and publishing procedural documentation about organizational controls and technological and procedural means of managing access to any electronic security perimeters that may be in place.
- Monitoring Electronic Access: Implementing and documenting electronic and manual processes for tracking and logging access to Electronic Security Perimeters that run continuously.
- Cyber Vulnerability Assessment: cyber vulnerability assessment (scanning for potential weaknesses) of the access points into the security perimeter should be performed at least once per year.
- Documentation Review and Maintenance includes revising, updating, and supporting compliance with information security policies through document management.
Physical Security Vendors
Quantum Secure and the RBtech Perimeter security system are two examples of physical security providers that can help you achieve the security requirements described above. Quantum Secure is one of the industry’s leading physical security vendors, specializing in identity management and access control to physical security systems (Wallden & Kashefi, 2019). RBtech, a major technological firm that focuses on designing, developing, and producing excellent outdoor perimeter security systems, offers an exclusive and sophisticated design on all its devices (Perimeter Security Systems, 2021). A perimeter protection system is required since they are a relatively affordable and effective option.
Human Resource Activities
The human resources department is critical to data breach prevention, as it oversees information security efforts. The HR department should improve this position by writing and publishing policies that are easy to access by the employees. When working for the organization, employees must be aware of the consequences of any failure to safeguard data. If a breach occurs, the employee is liable to be penalized. The HR department must ensure that employees receive security awareness training (He et al., 2019). This gives staff knowledge about what a data breach is and who to contact when it happens. Employees will see and learn about real-world data breaches and their measures to avoid these incidents. To address this concern, whenever an employee leaves the company, they should return any sensitive materials, change their network access credentials, and give up their email and social media accounts.
References
Cisco Firewalls. (2020). Router-Switch.com.
Enterprise Mobility and Security Pricing Options. (2021). Microsoft.com.
Hassija, V., Chamola, V., Saxena, V., Jain, D., Goyal, P., & Sikdar, B. (2019). A survey on IoT security: application areas, security threats, and solution architectures. IEEE Access, 7, 82721-82743.
He, W., Ash, I., Anwar, M., Li, L., Yuan, X., Xu, L., & Tian, X. (2019). Improving employees’ intellectual capacity for cybersecurity through evidence-based malware training. Journal of Intellectual Capital.
Kemper, G. (2019). Improving employees’ cyber security awareness. Computer Fraud & Security, 2019(8), 11–14.
McAfee. (2021). McAfee Total Protection. McAfee.
Perimeter Security Systems. (2021). RBtec Perimeter Security Systems.
Wallden, P., & Kashefi, E. (2019). Cyber security in the quantum era. Communications of the ACM, 62(4), 120-120.