Introduction
In the recent past, a rise in the use of the internet by both primary and secondary users has experienced a rise in different forms of attacks. These attacks range from worms and viruses to thefts of personal information. In addition to that, new and emerging forms of attacks have been reported and the situation has been getting worse each new day of internet usage. Among these new forms of attacks are Distributed Denial of Service (DDoS) attacks. Typically, these attacks rely on the concept of causing processes to generate other processes which disable any response from the resources and eventually disabling the functionality of internet resources. To launch attacks on the internet, the DDoS attack employs four main techniques. The Denial of Service Attacks (n.d.) confirms these attacks to be attained by:
- Attempts to flood or overwhelm the target network’s resources denying the legitimate user access to the network
- Attempts to delink all communication between connected and communicating computers
- Attempting to disable any access to the internet by legitimate users
- Attempts to disrupt the functionality of system resources such as the CPU of the server
Ideally, these attacks exploit the vulnerability of a network by seizing upon flaws and logical limitations inherent in any application. On the other hand, internet protocols and other related resources are exploited in the process to implement these attacks.
According to Sen (2011), the relative ease with which DDoS attacks can be effected and the low cost associated with DDoS attacks makes the technique potentially dangerous. The situation is further compounded by the inadequacy of available defense mechanisms which are integrated into Internet systems to prevent or minimize DDoS attacks. That has made DDoS attacks more serious and a great threat to the community of Internet users (Sen, 2011).
Ollmann (2010) views these attacks as basically targeting bandwidth consumption by overwhelming the target victim with a payload beyond one’s level of data or information consumption. Ollmann (2010) further asserts that if a primary victim’s target resources are exhausted, the possibility of successfully implementing a DDoS attack is high. Another approach identified by Ollmann (2010) includes exploiting applications by targeting inherent system weaknesses as detailed later in the study.
Considering the fact that “the Internet nowadays has become a basic necessity rather than a luxury as compared to years ago” (Sen, 2011), Sen (2011) reinforces the concern that the insecurity of the internet has made clients using the network figure out the enormity and danger associated with DDoS attacks. One recent experience was the use of DDoS by some countries to wage cyberwar against each other (Dubendorfer & Wagner, 2003). This kind of cyberwar is referred to as “intention to blackmail or smirch a country’s image” (Dubendorfer & Wagner, 2003).
Furthermore, the emergence of DDoS attacks as a cyber weapon to wage war has led to a multitude of problems. Not only are Internet users the only targets affected by this kind of attacks, virtual corporations thriving in the Internet have experienced serious disruptions on their operations. One typical example is a 2009 internet attack that targeted big website service providers including yahoo.com, amazon.com and eBay. The attack caused a loss of millions of dollars (CSI, 2003). A survey conducted to estimate the loss due to these attacks estimated the attacks to cost victim organizations $65 million (CSI, 2003). On the other hand, DDoS attacks have been evolving as a tool of “war” in which countries attack other countries. In this case, the internet is used as a platform to launch the cyber-attacks. Other examples include Government websites which have been hacked into with new cases registered each new day. Nowadays, hackers from different countries attempt to initiate and sustain conflicts between different countries through the internet using DDoS attacks. Cases of these attacks have been reported in different countries including Israel and Palestine, US and China, and many others (Allen & Demchack, 2003).
It is important to note that DDoS attacks are an emerging and persistent problem for the corporate world and governmental organizations operating in the Internet. That is because DDoS attacks affects the delivery of basic and important web services to Internet users making website organization lose large sums of money. These attacks have also demonstrated the potential to paralyze service rendering through the internet.
Many website owners and system administrators have tried to combat this problem by using different techniques. One such approach is to upgrade the network security policy to keep DDoS attacks at bay. On the other hand, general system techniques that website administrators apply include counteracting and guarding the Internet territory through different packet filtering techniques. This is attained by procuring expensive and complex software tools available in the market today.
Inspite of these precautionary measures, the occurrences of DDoS attacks are still on the rise. On the other hand, DDoS attacks dynamically evolve with new internet technologies, and seem to become more complex with the growth of the internet.
In order to determine the true extent of the problem and the extent to which website owners and website security administrators are coping with the problem, a survey was carried to capture valuable information which provided a glimpse of the possible ways to strengthen one’s defense against DDoS attacks.
However, conducting a survey of the kind was difficulty as new and difficulty challenges were experienced. Asking every websites organizations that have been attacked before by DDoS is a herculean task. The reason being that website organizations usually want to make DDoS attacks to be of low-profile to avoid loss of confidence from the users of the website that has experienced such attacks. In addition to that, users may express loss of confidence on the ability of the target website to afford security for the data and transactions conducted on the website translating into catastrophic losses.
To surmount that obstacle, the researcher treated information from the respondents with a high degree of anonymity. Respondents were assured of the confidentiality of information they provided. In addition to that, the aim of the research was stated in explicit terms to the respondents to encourage their participation and increase the number of responses. Not only did the survey employ questionnaires based on a question and answer technique, but also incorporated sections that allowed elicitation of detailed and in-depth information from the participants.
In the end, results generated from the project will help members of the Internet community get an idea on techniques to combat and strengthen their security defenses against DDoS attacks.
Problem Statement
The project aims to establish the technological characteristics of common DDoS attacks and enable the researcher acquire in-depth knowledge of the technologies used to minimize or prevent DDoS attacks. The knowledge acquired will play a critical role in the discussion and analysis of approaches to strengthen defenses against network attacks and help system administrators from organizations vulnerable to DDoS attacks to be able to overcome the problem. The researcher also seeks to crystallize the importance of exploring various methods of defending organizations and the Internet community against DDoS attacks.
The school of thought was to explore different avenues of technologies used to prevent or minimize DDoS attacks on the Internet and identify agile technologies that provide strong technological defenses against DDoS attacks. The discussion on the nature of DDoS attacks and currently available defense technologies will help system administrators formulate a better solution to DDoS attacks.
In addition to that, various cases where DDoS attacks have been launched with political backing will be a subject of scrutiny. Such will be a helpful case study on the extent and rampant nature of DDoS technology by different countries.
Given the aforementioned discussion, the researcher identified DDoS attacks on legitimate players in the Internet community. The nature of DDoS attacks pose great risks for both internet service providers and users with a 24/7 connectivity to the internet. Furthermore, each DDoS attack presents a dose of serious problems and challenges to system administrators for both the corporate sector and government sector websites. Once these attacks occur, system administrators spend a lot of time salvaging and minimizing the effects of DDoS attacks on their systems. Typically, that time should have been used to optimize their systems for better service delivery to their clients. On the other hand, parrying of any DDoS attacks will free more resources for more and effective web service provision and ease of Internet usage.
The intended outcome of this study is to come up with a good understanding of DDoS attack technology. In order to address the problem of DDoS attacks, the researcher deemed it necessary to identify different methods used in DDoS attacks. Emphasis will be on common and prevalent DDoS modes of attack. Patterns on how a DDoS attack exploit the different Internet protocols will be documented and scrutinize for better understanding. This will greatly help system administrators come up with proper network solutions and the state of network vulnerability. Moreover, different modes of DDoS attacks prevention mechanisms will be enumerated including the modern technology and network technique that have been designed and formulated during the past years.
The offshoot of these two-way analysis and discussion on DDoS attacks including the nature and technological defense approaches will be helpful to any organization that wish to eradicate the looming possibility of such attacks if launched against them. DDoS elimination or minimization will enable corporate and governmental websites focus and use their limited resources in providing a more reliable and optimal web services to their users.
Distributed Denial of Service (DDoS) attacks can be likened to an ordinary thief. The two share a common denominator. Both can attack someone, or in the case of DDoS attacks website entity at any given moment. They are robbers of peace of mind and the ease and comfort of having a transaction in the Internet community. Any attack which is DDoS in nature is expected to bring great disruption on the daily routine of every Internet user and every website service company. Much has been and will be loss when this kind of network attack targeted a specific website entity. It is expected that what comes along with the denial of service to the Internet users will come financial loss to the website corporation or say even a governmental website. Furthermore, more will be wasted through time dealing with the effects of the DDoS attack on the network. Productivity is sure to suffer next to the service to a website’s users.
Given the scenario of an aftermath of a DDoS attack, the unhampered and unbridled use of it by hackers can bring the whole Internet community in havoc and chaos brought about by the inconsistency and repeated disruption of internet web service. If this happens – if it has not yet reached that proportion now – then the Internet that has changed how the world works will be in great peril of being unreliable.
The result of are a loss of business gain and opportunity for all legitimate Internet players. In the fast paced 24/7 nature of internet connectivity, it is seen that virtual and traditional corporate organizations are spending time and money to grab the financial benefits that are derived from the use of the network. With the presence of network attacks, more can be said about the possibility of financial and business loss to all Internet players.
Strengthening the defense against DDoS attacks by every website corporation and government sites is deemed to be the sole solution to the problem. But the level of security that can be afforded by these defense technologies is an inquiry to be done by every organization involved in the usage of the Internet.
The researcher then aims to answer the research questions related to the project:
- What is the current technology of DDoS attacks?
- What can an organization do to protect themselves from DDoS attacks:
-
- What methods have been developed that provide existing DDoS attack detection systems?
- How can the defense and detection strategy be improved against DDoS attacks?
- What kind of as information campaign should be used to help organizations avoid DDos attacks?
The conclusion that can be drawn from this study will offer good insights on the prospect of free-DDoS attacks. Additionally, websites organizations will be better placed to identify strategies to embrace the battle against DDoS attacks. The discussion is on the nature as well as on modern defense mechanisms and technologies available to the Internet community to look for a more intelligent solution to the pressing problem.
Aim
The main aim of this study is to arrive at a possible solution to the problem caused by DDoS attacks against any website entity. Many DDoS attacks have been launched in recent years. Many more have been experienced in the recent past and continue to occur in each passing day. The study aims to presents the history and technological evolution of DDoS attacks and present protection modes that are available and which most network engineers have suggested can give an organization a positive outlook of being free from any form of DDoS.
Objectives
Study objectives:
- In-depth history of DDoS attacks.
- The effects of DDoS attacks on network system and the damage caused on the Internet community.
- Deterrent countermeasure defense technology to parry this kind of network attacks.
- How DDoS has been and can be used by countries to attack other countries.
These objtives are directed towards helping online organizations on ways to handle this modern Internet scourge.
Chapter Summary
This chapter has carefully detailed on the aims and objectives of the study. In addition to that, the chapter has also given emphasis on the havoc and disruption caused by DDoS attacks on targeted websites. The next chapter will discuss related literature review on DDoS attacks and the results will be used to justify and explain the importance of this study.
Review of Related Literature
The main purpose of this chapter is to elucidate and discuss available literature on DDoS attacks, DDoS technologies, and ways to prevent or minimize these attacks. In addition to that, a deeper insight into the working and nature of Distributed Denial Service attacks will be crystallized. Time and space will also be allocated for the discussion on the modern ways and tools of defending a network against DDoS attacks. To give broader implications of DDoS attacks, a review of old and recent DDoS attacks with political backing will be considered in this study. The attacks are referred to as “cyberwar” which is conducted against different countries.
DDoS an Introduction
The increasing number of Distributed Denial of Service (DDoS) attacks in recent years and months does not fail to alert the attention of all legitimate Internet players. DDoS attacks are already considered by IT expert as a major threat to the web community (Mirkovic et al. n.d.).
There is no doubt that with the spate of attacks experienced on the web community include monetary loss and compromise on financial gains. In part, that account for the fact that many web services fail to reach their targeted audience. In a survey conducted by CSI (2003), the estimated financial loss due to such attacks reached $65M in the entire United States alone.
It must be clear though that DDoS attacks are initiated with the intention of compromising “security or steal data or money” like any other Internet threat. Yet, the consequence of such an attack indirectly leads to losses to the web service corporations like “loss of business, revenue, customers, market confidence, etc.”
For the past few years now, DDoS attacks have repeatedly crippled a large number of commercial and government owned websites. It therefore cannot be denied that DDoS attacks are a great menace to Internet users. Comparing the severity and prevalence of DDoS attacks in the Internet, the CSI/FBI in 2003 charted the statistics of the different threats prevalent in the web as shown in Table 2.1 below.
Table 2.1. Types of Internet Attacks According to 2003 CSI/FBI Survey (Cashell et al, 2004).
Basing on the survey done by CSI/FBI, Distributed Denial of Service attacks occupy the third position from the top and is one of the major prevalent threats against the Internet with a 41% response rate (Cashell et al, 2004).
According to Sen (2011) the risk of a DDoS attack happening against a network is partly due to two factors. The first factor is the “ease and cheap costs of launching an attack,” (Sen, 2011). Even a teenager armed with a simple tool of DDoS attacks can initiate a spate of DDoS attack as happened in 2002 when many major e-commerce websites were crippled and hacked into (“Computer Crime,” 2002). The second factor is, according to Sen (2011) is “compounded”, the prevalence of such an attack and “the inadequate state of any viable defense mechanism” Sen (2011) present in the Internet network.
If this is the case, there it is not surprising that DDoS attacks are growing and proving to be a potentially dangerous threat to the stability and reliability of the Internet. Increase in financial loss as well as business gain for e-commerce corporations as well as governmental web services will continue to endure a repeated spate of onslaughts of the Internet plague.
In a 2010 survey, modern application layer DDoS attacks were charted and the result is the steady growth of bandwidth capacity of such attacks (“Anatomy of Botnet,” 2011). These modern DDoS attacks target and exploit the vulnerabilities of the characteristics of the most widely used application in the Internet, namely: HTTP, VoIP, DNS, and SMTP (“Anatomy of Botnet,” 2011). What adds to this alarming volumetric growth in DDoS attacks is the fact that these attacks “consume less bandwidth than volumetric attacks and are more difficult to detect” (“Anatomy of Botnet,” 2011).
Figure 2.1 presents the rapid increasing bandwidth capacity of DDoS attacks through the span of a decade, starting from 2002 to 2010:
DDoS: Technical Overview
One of the most pronounced DDoS attacks launched by hackers was the coordinated attack that happened in February 7, 2000. Prominent websites such as Yahoo, eBay and Amazon failed to operate for up to 24 hours. Incidents of websites being hacked and thus igniting or sustaining conflicts between countries like Palestine and Israel called Palestinian-Israel cyberwar, and United States and China happens have been reported from time to time (Allen & Demchack, 2003).
The general DDoS attack techniques that was used during these incidents was the generic strategies of sending hundreds of computers by bombarding the target victim with nonsense and senseless data sufficient to deplete the site with its memory (Chau, n.d.; Douligeris & Serpanos, 2007). Peng et al (2007) have identified two kinds of DDoS attacks. The first attack attempts to consume the resources for the target victim (Zwicky et al, 2001). The second type of attack targets the victim’s network bandwidth. The latter attack has more serious implications on the functionality of a website at times leading a website crashing and ultimately closing down (Sen, 2011).
The packet types used in these type of DDoS attacks have varied throughout the years. Three common packets that are still in use to effect DdoS attacks today. These include TCP floods, ICMP echo requests and UDP floods.
According to Kumar et al. (2006) a rise and spread of these form of internet attacks has been brought about by nine key reasons which include:
- A large population of unwitting users
- DDoS attacks do not display similar attack patterns or characteristics.
- DDoS attackers use legitimate methods to access and attack internet resources
- Lack of a coordinated administrative system for cooperation against the attacks
- Use of available automated software tools (botnets)
- Logical security flaws and other loopholes in the Internet;
- A deficiency of information on DDoS attack techniques
- the absence of “standardized evaluation and testing approaches.” (Kumar et al., 2006).
TCP Floods
This is where stream of TCP packets with a variety of flags are sent to the victim’s IP address. Here the SYN, RST, and ACK flags are commonly used. An example is where “SYN attacks exploit the vulnerability of TCP three-way handshakes thus depleting the server of its memory” (Leiwo, 2000). That happens when the attacker tries a connection request sent to the victim’s server with packets characterized by unreachable source addresses (Noureldien, n.d.). Since the server cannot complete the request for connection, the victim’s server results in a waste all of its resources leading to the crash of the server (Noureldien, n.d.).
Under IP spoofing, attackers attempt to enhance DDoS attacks by using spoofed sources that cannot be reached under normal cases. The approach denies the TCP protocol from establishing any new round of attacks (Chen & Yeung, n.d).
ICMP Echo Requests
One type of this attack is the smurf attacks where “ICMP echo request packets sent to IP broadcast addresses to generate denial of service attacks” (Forristal, n.d.).
UDP Floods
The most common of this is the cousin of smurf attacks, the fraggle attacks.
Types of DDoS Attacks
Throughout the years there have been old and modern DDoS attacks that are discussed below.
SYN Attack
The “SYN flood attack exploits the defenselessness of the TCP three-way handshake based on the way it allocates large data structures for incoming SYN packets regardless of their authenticity” (Leiwo, 2000). When the server puts the requests in the memory stack, it remains there until it is confirmed. That leads to an overflow in the memory of the server. Thus in the end there will be a denial of request even if the request is a legitimate one (Leiwo, 2000).
Smurf/Fraggle Attack
The smurf or fraggle attack is a ICMP flood. In this type of attack. This is where attackers use ICMP echo request packets that are sent to IP broadcast addresses to generate denial of service attacks (Forristal, n.d). Smurf basically uses TCP while fraggle takes an en route through UDP. Smurf attack is more effective than fraggle which is less popular to hackers.
HHTP Flood
This refers to an “ with the aim of bombarding web servers with HTTP requests” (Forristal, n.d). This type of DdoS attacks are most common with the botnet software. “HTTP request can be done by using a valid TCP connection which is a genuine IP address” (Forristal, n.d). An attacker has the ability to use bot’s IP address.
SIP Flood Attack
“SIP is a widely open standard for call setup in the voice over IP (VoIP)” (Rosenberg et al, 2002). In an attack scenario, the “attacker flood the SIP proxy with many SIP Invite packets which have false IP addresses” (Chen, n.d.). The first victims in this attack are proxy servers. Not only are the “server’s resources depleted, but can also be consumed by the SIP invite flood” (Jackobson & Jules, 1999).
DNS Amplification Attacks
The role of the DNS or domain name system is to provide a distributed infrastructure to associate and store different types of resource records (RR) with internet domain names (Mockapetris, n.d.). In this type of attack, one query response can contain multiple types of RR and some of these RR are very large.
DDoS: Network, Tools and Mode of Attack
According to Dietrich et al (2000), Distributed Denial of Service (DDoS) Network is defined and follows a hierarchy. One or two attackers stands at the top of the hierarchy and it is them that controls the immediate lower segment so-called “handler.” The handlers meanwhile control the agents that “execute the commands relayed to them” (Dietrich et al, 2000). Dietrich and his group further elaborated that the communication that is going on in the network between the attacker, handler and agents is called the control traffic. When the attacker signals the attack to a certain targeted network, then that is called “flood traffic” which will eventually choke the resources of victim and make his site crash as a result.
Figure 2.2 shows the typical DDoS Network hierarchy. All of DDoS attacks one way or another function according to this hierarchal mode:
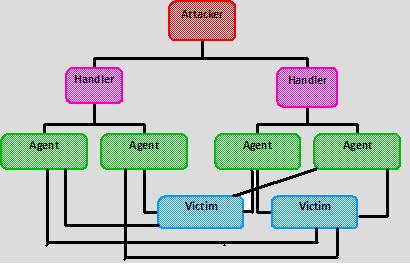
The use of this kind of network hierarchy, as explained by Dietrich et al (2000) is to remove the “attacker” from view. The attacker uses the handler as his first line of defense to hide his identity (Dietrich et al, 2000). Dietrich et al further explained that the attacker communicated with the handler via a “variety of mechanisms:” through simple telnet, a more advance techniques like encrypted TCP connections. Dietrich et al further adds that ssh is a used in DDoS tools and mode of attacks such as Tribe Flood Network (TFN); while blowfish-encrypted proprietary is used in Stacheldraht.
Moreover, Noureldien (n.d.) stated that even if the study of DDoS attack is directed towards the defense against such attack, the importance of discussing the elements (such as network) and tools and the mode of such attack is needed (Kessler, 2000). For the most DDoS attacks, common tools and mode of attacks can be enumerated to give a good idea of how a DDoS attack is launched. Moreover, these DDoS tools and mode of attacks do not just give how such an attack functions, but also give a look on the characteristics of network vulnerabilities by which DDoS attacks tries to exploit to reach its goal of disrupting a website’s service.
There are basically not less than ten important and popular tools that have launched a successful DDoS attack and are still in used as a kind of technology by attackers (hackers). These tool can be enumerated as Trinoo, Tribe Flood Network (TFN) Stacheldraht, Trinity, Shaft and Tribe Flood Network 2K.
Trinoo is the first and probably the most common tool in DDoS attacks. It is considered to be the first and the oldest DDoS tool that was designed. What this DDoS tool does is launched a distributed SYN DoS attack. Here the masters and daemons needed for the launching of a DDoS attack communicate with each other using selected ports. According to Dittrich (1999) study of Trinoo, the tool suggests that it is being set up in hundreds if not thousands of systems in the Internet. This is accomplished as stated by Dittrich (1999) when these vulnerable systems are being compromised by “remote buffer overrun exploitation.” Dittrich (1999) further adds that access to this Internet systems are made possible by the installation of multiple “back doors.”
A sample of Trinoo attack was reported in August 17, 1999 (Dittrich, 1999). In this case, a Trinoo network of an estimated 227 systems flooded a single system in the University of Minnesota; the attack swamped the system resulting to a two-day crash. What is more surprising in this attack is that there were traces that there are at least “16 systems” that participated in the attack and some of them originating outside the United States (Dittrich, 1999).
Meanwhile, another tool known as Tribe Flood Network or TFN is the most used tool in initiating attacks that consists of ICMP flood, UDP flood, SYN flood and SMURF attacks. The difference of TFN from Trinoo is that all the communication in launching an attack that happens between the attacker, agents and handlers is done through the use of ICMP ECHO and ECHO reply packets (Dittrich, 1999). The communication for example between the TFN client and daemons is facilitated via ICMP ECHO REPLY packets (Dittrich, 1999). The success of this DDoS tool in getting the attacker’s target to successful crashed is accomplished through the exploitation of the vulnerability in the network system. TFN usually use the absence of any TCP and UDP monitoring by which the packets that are sent by TFN becomes difficult to detect. Noureldien (n.d.) states that this happens because many “protocol monitoring tools” are not designed and configured to display and capture the ICMP traffic.
TFN later on upgraded to a higher version called Tribe Flood 2K. This software according to (CERT/CC, 1999) is a complex version of the first TFN. Keeping abreast with the challenges of launching a DDoS assault, this new version is designed with the intention of to make it unrecognizable and difficult to filter (CERT/CC, 1999). Through this software, it can remotely execute assault orders; moreover it can also hide the real source of the attack by spoofing the original IP address.
Another well-known DDoS tool is the Stacheldraht which means “barbed wire” in German language. Stacheldraht is considered a greater threat as a DDoS tool considering that it possesses both the characteristics of Trinoo and TFN being the offshoot of these former tools. Dittrich (n.d.; 1999b) in his analysis of Stacheldraht found out that this tool has the “full control features” and the capacity to forge sources address that is a characteristics of TFN. Dittrich (n.d.; 199b) added that the twist in this kind of tool is it has “Blowfish-encrypted control channel for the attacker.” This DDoS software through years has mutated and evolved in different more potent version. In 2000 StacheldrahtV4 appeared early in the said year and succeeded by another higher version called Stacheldraht vl.666 (CERT/CC, 2000). This new version now has the capacity to launched TCP ACK and TCP NUL packets assault and “pre-configured Smurf attacks” (CERT/CC, 2000).
A DDoS tool that attacks a victim’s site through Internet Relay Chat is Trinity. This modern software makes the communication between the attacker, handler and agent through IRC or AOL’s ICQ. This tool can be used to initiate flooding assault. Dittrich (1999a) explained that the characteristic of this software is that it has a favorite port for its activity specifically port 6667; moreover the software is armed with a backdoor program with the ability to listen on TCP port 33270 (Dittrich, 1999a).
Another DDoS software is the Shaft. This software looks like Trinoo in its ability to launch an attack. Dittrich et al (2000c) explained the characteristics of this software tool as having the capacity to initiate a packet flooding attack. Dittrich et al (2000c) adds that it also gives the client (attacker) the control on the size of the packets that will flood the target network and even the duration of this assault.
DDoS tools are listed on Table 2.2 below:
Table 2.2 Summary of DDoS Tools (Gupta et al., 2010).
The Emergence of BotNets DDoS Attacks
Sometime back, DDoS attacks were identified as amplification attacks. Sisalem et al (2009) explained this mode of DDoS assault to be a situation where the attacker manually assaults target victims by “targeting the misuse of protocol or service features to amplify the amount of data sent.” Yet, as the Internet age progresses, Vacca (2010) stated that bot and botnets are the latest innovation in the proliferation of malware, which are tools for DDoS attacks. Vacca (2010) further elucidated that a single bot program installed in the victim computer had numerous possibilities of using the target computer for endless malicious activities such as launching a DDoS attacks. According to Greenberg (2007), by January 2007, Google’s Vinton Cef had run an estimate number of computers being infected by botnets into 150 million. That was about 25% of all internet hosts.
In a report by Damballa system called Top 10 Botnet Threat Report 2010 (“Top 10,’ 2010), the system reported an increase in the number of botnet since the last several years. The list of botnets shown below is made of up of a list of 20 victims in the year 2010. Damballa reported that most of these botnets are created using DIY botnets that are available in the Internet as shown in Table 2.3 below:
Table 2.3 2010 Top 10 BotNet (“Top 10,” 2010).
Venter et al. (2007) and Gu et al. (2008) stated that the evolution of botnet into such a sophisticated software has resulted into a subject of predominant and latest prevalent threat on the Internet. According to Venter et al. (2007) this has prompted a thorough and significant research into the network security community to give “early detection and response techniques” solutions (Venter et al, 2007; Vrizlynn et al, n.d.; Wang & Reiter (2003).
Defense Against DDoS Attacks
It is well understood that DDoS attacks can wreak havoc and can create chaos in business according to findings reported by (IBM BladeCenter, n.d.) The report further added that the increasingly sophisticated and complex botnets plus other malicious methods have the ability to cripple transactions in computer networks and websites. Handley & Greenghalgh (2004) and Aries Institute of Technologies (2007) elucidated the obvious goals of these DDoS internet attacks by targeting a specific server and other critical mission-critical components of the network and bombard it with tremendous amounts of external request rendering e-commerce transactions, digital media traffic and network services disrupted. Based on these findings, Holz (2005) concluded that the emergence of DDoS attacks are the number one threats to the Internet community today. That is in addition to the fact that, many solutions have been crafted and formulated based on DDoS attacks (Sterne, 2001; Kargl et al, 2001).
The main focus is the solution that these digital mechanisms provide to targets that are defined by the vulnerabilities inherent in most internet protocols (Lu et al., 2007). The only problem that stand between these new solutions is that the packets sent by DDoS attackers target are difficult to detect as an attack since these packets cannot be easily distinguished from legitimate, normal packets that are sent by legitimate users and computers. It is argued that “The difficulty with these attacks is that each request in isolation looks benign. A bogus request is very difficult to distinguish from a legitimate one” (TippingPoint Technologies, n.d.)
Nevertheless, some of these suggestions include protocol reordering and protocol enhancement, methods which make security protocols less vulnerable and more robust to resource consumption attacks (Matsure & Imai, 1998; Leiwo et al, 2000).
Other suggestions and solutions that have been designed by network computer engineers are network ingress filtering technique, a mechanism designed to prevent attacks that use spoof source addresses (Ferguson & Senie, 2000). This process involves the configuration of the router to drop packets that have suspicious source IP addresses. One problem with this solution is the inability to control the flood coming from its own network.
Other known solution to the problem of DDoS attacks that are used by many software applications to support protection from DDoS attacks are: the ICMP traceback which is useful to ascertain the path used by the packets through the Internet (Belovin et al, 2001); Deterministic packet marking (DPM); Probabilistic packet marking (PPM); Pushback approaches, path identifier (Pi); and route-based packet filtering (Cai et al, 2004; Yau et al, 2002; Park & Lee, 2001; Burch & Cheswick, 2000). Most of these enumerated strategies target the checking of IP address, IP header, IP packet, and even header size to eliminate IP spoofing and other crafty maneuvers by DDoS attackers.
Given the above mentioned suggestions as protection and defense mechanisms against DDoS attacks, Gupta et al. (2010) narrows these mechanisms into two categories, general techniques and filtering techniques.
General Techniques
General techniques are identified as common preventive measures for protecting a network against DDoS attacks. These techniques include system protection or replication of resources that individual servers and their Internet Provider Service (ISP) use so not to be part of any DDoS attack.
The tandem of Geng and Whinston (2000) suggested two general techniques by which DDoS attack can be avoided. The first one is by disabling unused services. The reason for this suggestion as stated by Geng and Whinston (2000) is that the “less there are applications and open ports in hosts, the less there are chance to exploit vulnerabilities by attackers.” The tandem further elucidated that if a specific network is unused or not needed, that network’s services should be disabled to prevent DDoS attacks like UDP echo and character generation services (American Bar Association, 2008; Tipton & Krause, 2007).
Geng and Whinston (2000) also supported technique of installing new and latest security patches. The duo explained that given the technology of DDoS attacks these days are focused on the vulnerabilities of the targeted target system. Installing new patches can avoid such DDoS attacks. Kim & Solomon (2012) further added that safety general measures to avert and avoid DDoS attack can be done through global defense infrastructure. The design for global deployment infrastructure is an effective general preemptive measure to stop a DDoS attack since this can install filtering rules for the most important routers in the network (Geng & Whinston, 2000). Yet, Gupta et al (2010) explained that this kind of general measure to avert and shun DDoS attack is only possible in theory considering that the Internet is a vast network administered by different autonomous system and act according to their own set of local security policies.
In this case, the tandem of Geng & Whinston (2000) suggested another mechanismof general measures to protect a network from DDoS attacks. The two suggested the IP hopping technique. The two elaborated that DDoS attack can be prevented by altering or changing the network location of the server, meaning changing the network’s IP addresses. It is known that DDoS attacks are based on the technique of flooding a server located in a specific IP address, an ingenious mechanism is deemed effective. This can be done, as explained by the duo of GEng & Whinston by “changing the IP address of an active server proactively with a pool of homogeneous servers”….or this can be done “with a pre-specified set of IP address ranges.”
Gupta et al (2010) elaborated on the use of IP hooping as still vulnerable against DDoS attack. However, the approach hasThere are still some loopholes (Gupta et al, 2010). While changing the IP address drop the target server from the stream of DDoS attacks, this method for averting and avoiding such attacks is only applicable on DDoS attacks that are designed to work on IP addresses. Gupta et al (2010) added that this method has no use or function for DDoS attacks that are designed and loaded with a tool like domain service name tracing function.
Lau et al (2000) in their studies suggested disabling of IP broadcasts as a general defense mechanism against DDoS attacks. According to Lau et al (2000), disabling IP broadcasts means crippling DDoS attacks. One typical example is Smurf and ICMP floods where DDoS attacks used intermediate broadcasting nodes (Lau et al, 2000).
According to Oppliger (1997), “firewalls can effectively prevent Internet users from launching DDoS attacks characterized by simple flooding which comes from machines behind the firewall” (Oppliger, 1997). The reason for this effectiveness is based on the “simple rule that characterizes firewalls to deny or allow protocols, ports, or IP addresses” (McAfee, n.d.). The only downside to this technique is the inability of firewalls to keep abreast with complex DDoS attacks. An example is an attack on a web service, port 80 where the firewall is not capable of distinguishing good traffic from an actual DDos attack (Oppliger, 1997).
Summary and comparison of these general techniques is shown in Table 2.4 below:
Table 2.4 Summary and Comparison of General Techniques.
Filtering Techniques
With the relative shortcomings inherent in the general techniques designed to avert and avoid DDoS attacks, IT professionals and experts are trying to sort out other effective ways of averting attacks. Filtering techniques are one of the techniques networks and servers use to protect burgeoning DDoS attacks. Currently, there are six major filtering techniques tested and known to work effectively.
Ingress/Engress filtering was one of the filtering techniques suggested by Ferguson & Senie (1998) to protect networks or servers from DDoS attacks. This filtering technique uses the domain prefix connected to the ingress router to determine if the domain prefix and the server match else the connection is dropped ( Apolloni, 2007). According to the tandem of Ferguson & Senie (1998) the only requirement for this kind of filtering technique is the knowledge of IP addresses connected with the network. However, this requirement is difficulty to achieve as the knowledge of complex network topologies are difficulty to capture. To counter that problem, the technique uses reverse path filtering according to (Baker, n.d.).
The downside to this kind of technique according to Gupta et al (2010) is that it cannot effectively work in real world Internet network where asymmetric Internet routes are common. Gupta et al. (2010) added that an attack using spoof IP address can still penetrate the network if there is no ingress/engress installed in the network. The group also elucidated that an attack is still possible if the attacker got the subnet IP address and uses it as the route for the attack (Mirkovic et al, 2004).
Another kind of filtering technique to defend against DDoS attacks is referred to as history based filtering according to (Peng et al., 2003). Peng et al. (2003) knowledge of the workings in the network during normal operations indicates that when IP addresses and DDoS attacks are stable, the sources of IP addresses are compromised. Peng et al. (2003) suggested the use of the IP address database (IAD) to keep records of the frequency of IP addresses that have been compromised. Peng et al. (2003) explained that using IAD during a DDoS attack was critical from the moment all IP address attacks not in IAD are dropped. The group of Peng et al. (2003) also identified the importance to use Hash based/Bloom filter technique for quick and faster searching of IP addresses in IAD.
The good news about history based IP filtering technique is that it does not need each member of the internet community to cooperate. That is because each member can have or not have this kind of filtering technique (Gupta et al. 2010). The only downside to this kind of filtering technique is its ineffectiveness to prevent DDoS attacks when the IP source of the attack is genuine or real.
A variant to the bloom filtering technique is the counting bloom filter (Chen & Yeung, n.d). According to Chen and Yeung (n.d) the counting bloom filter employs a technique which keeps a table of counters showing the number of hits a target has experienced from DDoS attacks. For each attack, the value corresponding to the IP address of the victim under DDoS attack is decrement or increased. Thus, if a counter, i is identified at a location such as h, then, the corresponding counters at location hi (b), where 1<i<k are greater than zero (Chen & Yeung, n.d).
Third on the list of filtering techniques is the router based packet filtering according to (Park & Lee, 2001). In Park & Lee’s (2001) views, the technique extends the capability or workings of the ingress filtering technique. The technique uses the “route information to filter out spoofed IP packets” (Gupta et al., 2010). According to Park & Lee (2001) the principle behind this technique is that the core link in the Internet network are limited sources of IP addresses from which the link to legitimate traffic comes from. A spoofed address can be detected once an unexpected source of IP address appears on the IP address. This packet can then be filtered (Park & Lee, 2001).
Park & Lee (2001) further elaborated that the router-based based filtering technique uses the BGP routing topology to filter spoofed source addresses. A simulation carried on the router-based filtering technique showed that a fraction of spoofed addressed being filtered indicated an 18% implementation level of the Internet community.
Another filtering technique by Anderson et al. (2004) called capability-based method is where the destination takes control of the traffic directed towards it. On the other hand, the request packets sent to the destination are marked by the router it with the above mentioned capabilities. The destination then will have a choice to decide whether to permit the packet to go on or be dropped (Anderson et al., 2004). The data or packets already marked with capabilities are sent to their destinations via the router. The advantage with this filtering technique is the ability to control the part of the destination to drop or get hold of the packet. The destination can easily drop packets without marked capabilities in times when there is a DDoS attack therefore saving the network from congestion.
Meanwhile, Keromytis et al (2002) suggested a filtering technique called Secure Overlay Service (SOS). The mechanism for this method is that all traffic coming to the network will be verified by secure overlay access point (SOAP). After traffic is authenticated it is then routed to a special overlay node (Keromytis et al., 2002). The overlay node is called beacon “in an anonymous manner by consistent hash mapping” (Keromytis et al, 2002).
Another kind of filtering technique known as validity enforcement (SAVE) protocol was suggested by (Li et al., 2002) and (Giladi & Serpanos, 2006). The “Internet protocol can enable routers to alter or update information from expected source IP addresses and then block packets with unexpected IP addresses” (Li et al., 2002). According to Li et al. (2002) and Vimercati et al (2005), “the goal and aim of the new protocol is to give routers specific information regarding the range of source IP addresses that are expected at each interface” (Li et al., 2002) and (Vimercati et al., 2005).
A summary and comparison of different filtering techniques are shown in Table 2.5 below:
Table 2.5. Summary and Comparison of Filtering Techniques (Gupta et al. 2010).
Application Layer DDoS Attacks and Defense Against It
A report by Arbor Network (2010) indicates a surge in the number of DDoS attacks in the recent recent years to the 100 Gbps barrier. This barrier is described as “staggering” with 1,000 percent increase equivalent to 10 Gbps. Furthermore, Arbor Network (2010) reports that increasing attacks are becoming more sophisticated and target specific applications like DNS, VOip, and HTTP. In addition to that, Arbor Network (2010) reports that the application layer DDoS consumes less bandwidth while being characteristically stealthier to detect. Chee & Brennan (2010) attributes the effectiveness of layer 7 DDoS attacks to legitimate TCP or UDP connections which demand a smaller number of connections and are able to optimize available resources to their limit. This kind of DDoS attacks have a paralyzing effect on e-commerce considering that its effects run from loss revenue or profit, lower productivity, penalties and tarnished reputation or brand. Layer 7 DDoS attacks can be categorized in four types, namely: request flooding attacks; asymmetric attacks; repeated one-shot attack; and application-exploit attacks (Arbor Network, 2010). Figure 2.3 table below shows this increase in this so called application layer (layer 7) DDoS attacks:

Since layer 7 type of attacks are an emerging trend in DDoS attacks, Chee & Brennan (2010) suggested general countermeasures to these attacks to include limiting the size of requests requirements made to each form, identifying 95% to 99% of the normal access speed range for the network with speed limits and maximum allowable sizes of request forms, and enabling the network to establish a request timeout for each form.
How DDoS is/was Used to Attack Another Country
DDoS attacks are fast becoming the alternative for physical war or nuclear war as been witnessed in recent years. There used to be a time when bullets and missiles were used to attack another country, but now it is worth concluding that cyber war is a new and evolving means to wage war. Programs and codes are now the weapon of destruction. Cyber war is evolving as the terrain where countries can attack each other. Incidents of government and state websites being hacked are continually added to a growing list. However, most of these attacks, which use DDoS hacking technology, have helped ignite and sustain conflicts between countries like Palestine and Israel called Palestinian-Israel cyberwar, and United States and China which happens from time to time (Allen & Demchack, 2003).
One most recent cyber war attack using DDoS hacking technology was one done against Estonia on April 2007 (Kirk, 2007). Estonia’s prime minister’s website, along with banks and other sites mostly run by schools were put to a halt due to an overwhelming distributed denial of service (DDoS) attacks. On another part of the globe, series of DDoS attacks against countries like United States and South Korea happened in 2009. The White House and Pentagon’s websites were crashed and South Korea’s government agencies’ websites were targeted victims. North Korea was suspected to be the main perpetrator of these undesirable acts (Nazario, n.d.)
In 2011, a major DDoS attack on Turkish government websites was launched by the group of Hackers called “Anonymous” (“Cyber-attack Group,” n.d.; “Anonymous Hackers,” 2004). The said attack was launched a day before the national election in Turkey. According to the statement by the Anonymous attackers indicated the attack to have been a reaction to the plan by the Turkish government to implement filtering system in their Internet services. One of the Turkish government websites that suffered disruption to its service provisions included the telecom authority, the one government department that hackers thought was responsible for the filtering system intended for deployment into the Internet system in Turkey.
Methodology
The main goal of this research was to gain insights and in-depth perspectives regarding the trend and technology of DDoS attacks and possible methods and mechanisms which e-commerce and organization can adopt as countermeasures to protect websites from the threat of DDoS internet attacks. In order to come up with a possible insights and good understanding of the issue and its resolution, the researcher identified the need to conducti a survey on a number of web sites. Names of surveyed websites were made confidential for the sake of security.
The researcher believes that doing a survey in this research is more feasible and can accurately crystallize the entire picture and rationale of strengthening a network/site against DDoS attacks. Furthermore, it is less laborious and can be carried out easily. Herr & Anderson (2005) support this statement by arguing that the traditional five-chapter survey research dissertation method using inferential statistics to analyze data is less labor intensive and can be done without leaving one’s office, a situation that can be modified to fit into the researcher’s working environment, in this case the Campus. Case study in this case is not feasible and dropped from the plan. Case studies in recent years have been criticized for their inability to generate feasible answers to specific issues and problems which may be variably different from one case study to the other (Feagin et al, 1991; Jakobsson & Zhou, 2004).
Collection protocols
During the planning stage, the researcher identified a purposive or judgment sampling technique to collect data from the target population. Simply defined, judgment sampling is the “process in which the researcher readily decides on which part of the population can be best used in the study” (Kalton, 1983).
In this particular case, using individual internet owners as samples is time consuming yet the researcher realized that it did not affect the timeframe allotted for the project. That was achieved by balancing time allotted for data collection the task. In addition to that, measures were put in place to ensure all scheduled tasks were accomplished within the specific time and date. Measures were also instituted to immediately counter any problems experienced during the research.
The methodology used by the researcher exposed him to a variety of respondents, an extremely essential feature in this project. The more diverse the samples were, the higher the probability of finding better solutions on strengthening systems against DDoS attacks. However, to make this research more functional, focus was given to answers provided by respondents who had had prior experience with DDoS attacks and solved the problem in their systems.
The actual research begun with the researcher asking for permission from websites sampled into the study as respondents. This was true especially for cases where a site had had a history of DDoS attacks. The researcher coordinated with their IT supervisors and expounded in clear and explicit terms the purpose of this project. When the requests were granted, consent from respondents was done next. The researcher found some of them hesitant. However, the researcher explained their answers would be strictly used for academic purposes only with a lot confidentiality. This set-up gave the researcher the opportunity to personally monitor the process. It also gives a way for a high response turn out. A total of 20 respondents were subjected to the study. The number may be small compared with other surveys. That was partly due to the fact that the process of looking for website owners and administrators was challenging.
Research Design and Processing
The survey results were used as the main method of strengthening defense against DDoS attacks. The information produced was tabulated and analyzed. A content analysis technique was applied in the processing of the survey results. Furthermore, additional research was conducted through the use of literature a review in order to identify possible methods of strengthening defenses against DDoS attacks. Moreover, the result was examined to determine different methods in defending a system or site against DDoS attacks. The results were examined to form the basis for making recommendations to organizations which are part of the internet community and other stakeholders on techniques to defend or minimize attacks from DDoS threats.
Design for Processing
When it comes to data evaluation and analysis, this thesis is basically qualitative in nature. It intends to explain and describe the occurrence of DDoS attack against websites and the methods of defense against it. This ensured that the project will give insights on how DDoS attack happens and dealt with by websites administrators. In addition to that, the damaging effects of DDoS attacks to websites were given emphasis. For the researcher to identify the strategic IT value of this project, the researcher is aware of the need of discussing the technical aspects that are part of DDoS attacks and defense against it. Discussions of these two aspects cannot be avoided, especially in the aim to have a better grasp on the essential strategic strengthening of defense against DDoS attacks.
Design for Project Outcome
It has been mentioned that the main goal of this study is to disseminate ways corporations or entities that are part of the Internet community can strengthen their defenses against DDoS attacks. Thus, the rationale to analyze different techniques, measures, and technologies to controls or avert DDoS attacks. It is therefore important to determine the extent to which these measures can defend systems against DDoS. Moreover, the signs of progress and growth are evaluated based on the expenses that are spent in expanding site bandwidth and other equipment. From this point of view, the researcher is guaranteed that the devised answers are found on praxis and go beyond theoretical assumptions.
Implementation and Analysis
To further establish the nature and prevalence of DDoS internet attacks, the researcher conducted a survey on many website owners and corporations. A total of 20 respondents were included in the study. As has been mentioned, the number may not be high compared with respondents in similar surveys. But due to the difficulty of physically identifying and locating web owners and administrators, the process had experienced great challenges. For the research, the number was sufficient to stand the scrutiny of establishing ways to strengthen defenses against DDoS attacks. On the other hand, the respondents were informed and briefed beforehand about the aim of the survey and purpose to avoid unnecessary disagreement.
One of the critical and basic foundations for this project is to answer the inquiry concerning website administrators’ level of awareness about DDoS attacks. As been mentioned, DDoS attacks have been registering an upward trend as one of the most dangerous threats in the Internet. According to the data gathered, 90% of the respondents have heard about it. Meanwhile 10% stated that they have never heard of this kind of Internet attack before. This result, as shown in Table 4.1, can be understood, considering that not all web administrators are abreast with Internet trends given the factor of competency in the job.
Table 4.1. Respodents who have heard about DDoS attacks.
There may be 10% who have never heard of DDoS attacks and 90% knowing about this technology, but on the question of whether who among the respondents have experienced DDoS attacks against their sites, it yielded to a high percentage of 75%, as shown in Table 4.2. Analyzing this data, it can be said that those who have never heard of DDoS attacks are those who have not experienced it, so for their ignorance about the attack. Meanwhile, the high percentage of respondents who said they have suffered from such attack leads to the conclusion that this hacking technology is rampant and already in the knowledge of competent and experienced website owners and administrators.
Table 4.2. Respondents who have experienced DDoS attacks.
From the above table, it is already established that 18 respondents have experienced DDoS attacks. The researcher endeavored to use the number from the findings to determine the average time an attack lasts before a remedy is applied. It is not surprise, based on gathered data that 6 hours to 12 hours to be the duration of an attack resulting to a 0% functionality of the victim site. An attack usually paralyzes the site and if there is no strong defense against the attack, the site may remain inoperable for a long period. 24 hour duration before a remedy takes effect registered 55.5%. Implying that the usual duration of an attack before it can be remedied averaged a speed of 24 hours, as shown in Table 4.3. On the other hand, respondents who have experienced longer periods of time before providing a solution to a DDoS attack registered small percentages of 33.3% and 11.1% respectively.
Table 4.3 Duration of DDoS Attacks.
Those who have information and experience on the effects of DDoS attacks on one’s site reveals an interesting result according to the data gathered. Using general techniques such as firewall and filtering techniques both garnered 3% number of respondents for each defense against DDoS attack. Meanwhile, there is a high percentage on those web owners and administrators who use both general and filtering techniques to protect their sites from such attacks; 65% as shown in Table 4.4. This is a revelation to the researcher since it is known that there is no foolproof one technique defense against DDoS attack and using all the available technology to parry such attack, like general technique and filtering, is good preventive measure being taken already by those who have information and experience of DDoS attacks.
Table 4.4. Response to DDoS Attacks as Taken by Web Administrators.
The survey result contributed to deeper, insight and first-hand information regarding the nature of DDoS attacks and defense measures being applied to deter it from disrupting web services. It is beneficial to this project since a more comprehensive analysis was performed and shed light to some of the common practice web site owners apply in strengthening their networks against possible DDoS attacks. Through the straightforward and intelligent answers by respondents, the researcher had identified a case where everyday workings of a site trying to defend itself from Internet attacks such as Distributed Denial of Service (DDoS) was done.
Conclusions and Recommendations
The rising trend of distributed denial of service (DDoS) internet attacks has raised a red flag from IT professionals and members of the Internet community. The disruption and devastating effects of DDoS attacks on website services can not only be measured by financial and business opportunity losses, but also by other factors that can be said to be the main reasons why a website owner or administrator will try to defend their sites against attack. But the devastating effect of DDoS attacks is the reliability and accessibility of any Internet access to the net users at large. This is the reason why the upsurge of cases and prevalence of DDoS attacks in recent years has predicted the near dooms-day scenario to the growth of the Internet.
Yet, something can be done to curb the Internet surge as users with previous experience and detailed knowledge are aware. The amount and time spent to remedy the first hours of a DDoS attacks plus the eventual expenditure to recover one’s online reputation and image is minimal compared with the basic measures and precautions one can apply on one’s site to protect it from DDoS attacks. These can be done through general security measures like setting up firewalls, using IP hopping techniques, etc. To some extent, spending on software and technology that can enhance filtering techniques to remove malicious traffic or packets by dropping them soon as they manifest is feasible.
Users who have experienced disruptions on their online operations showed owners to be already aware of the remedy for the online plague. However, the solution to the problem of strengthening one’s defense against DDoS attacks already practiced by website owners and administrators who have experienced previous attacks by hackers using DDoS technology.
They, unknowingly, have somehow validated the first thesis of this project. If one plans to strengthen one’s website defense from disrupting DDoS attacks, the result and data gather from this project present a silver lining to the doom scenario that the DDoS problem has brought to the whole Internet community. The counter-measure done and being applied by website owners and administrators to their own sites is close to a foolproof protection from DDoS attacks. There may be still some percentage of DDoS attacks penetrating their sites, but their way of defending themselves against it is already far behind what seasoned hacker using DDoS technology can do disrupt their site’s operation.
One can strengthen one’s network defense from DDoS internet attacks by adapting security measures offered by general security measures and filtering software. It is in the domain of general knowledge that neither use of these security measures is enough to contain DDoS attack. But positive results can be attained by integrating these security measures. Though suggested remedies are still not a perfect solution to the problem of DDoS attacks, considering DDoS technology, the possibility of effectively parrying DDoS attacks is high. This conclusion was reached by the researcher by analyzing responses to a survey given by these respondents.
It is recommended that website owners, organizations connected to the Internet and IT professionals use a “one-two punch” to disrupt Distributed Denial of Service (DDoS) hacking technologies. The one-two punch method is an adaptation of general techniques such as firewalls, IP hopping, and installation of security patches working with filtering techniques provided by many software developers and vendors. In addition to that, a simple establishment of request timeout for each form can proof helpful for any site intending to parry DDoS attacks.
Attacks such as spoofed flooding attacks which include random spoofed attacks and subnet attacks can be prevented or minimized by use of a reliable and efficient data storage mechanism to documenting relevant data traffic information.
Future Works
In this project, the history and growth of distributed denial of service (DDoS) attacks have been mapped out. The trend growing trend of morphing complexity of the technology applied in such Internet attack is well discussed and covered.
Known traditional general security measures and methods to combat these online plagues are discussed and explained for the benefit of the reader. The general measures are should be taken seriously though they are basic approaches to minimizing or preventing DDoS attacks. In addition to that, advances in major filtering techniques, as provided for by many software developers and vendors are discussed.
The main contribution of this work is to successfully evaluate the strength of one’s network against DDoS attacks. The objective was fulfilled by conducting a survey using a sampling technique on online users and website owners who have experienced catastrophic attacks from DDoS attacks. Results from the research indicated that combinations of general security measures and packet filtering techniques available today are the best solution in combating DDoS attacks. These security measures, of course, are not ideal or 100% foolproof against the surge of DDoS attacks. That is partly changing due to ever changing methods that are getting sophisticated each new day. However, the above mentioned measure can yield a high possibility of parrying DDoS attacks.
Several approaches have been suggested on ways to improve future works based on findings from this project as enumerated below:
- Further study on the emerging level 7 DDoS attacks and the kind of filtering techniques that can be applied to it
- A review and redesigning of network protocols that DDoS attacks usually use as backdoors to its attacks
References
Albitz, P. & Liu, C. (2006). DNS and BIND. California: O’Reilly Media, Inc.
Allen, P. & Demchak, C. (2003). The Palestinian-Israel: Cyberwar. Web.
American Bar Association. (2008). Data Security Handbook. Chicago: ABA Publishing.
Anderson, T., Roscoe, T., and Wetherall, C. (2004). Preventing Internet Denial-of-Service with Capabilities. ACM SIGCOMM Computer Communications Review. 34 (1), pp. 39-44.
“Anonymous Hackers,” (2004). Anonymous Hackers Take Down a Government Website in Turkey. National Turk. Web.
Apolloni, B. (2007). Knowledge-based Intelligent Information and Engineering Systems. 11th International Conference, KES 2007 XVII Italian Workshop on Neutral Networks.
Arbor Network (2010). The Growing Threat of Application-Layer DDoS Attacks: How Peakflow SP and Peakflow SP TMS can Stop Them. Web.
Baker, F. (n.d.). Requirements for IP version 4 routers. RFC 1812, Internet Engineering Task Force (IETF).
Belovin, S., Leech, M., & Taylor, T. (2001). ICMP Traceback Messages. Internet draft, October. Web.
Burch, H., & Cheswick, B. (2000). Tracing Anonymous Packets to Their Approximate Source. In Proceedings of the 14th Systems Administration Conference, USENIX LISA, December 2000, pp. 319-327.
Cai, M., Chen, Y., Kwok, Y.K.,and Hwang, K.(2004). A Scalable Set-Union Counting Approach to Pushing Back DDoS Attacks. USC GridSec Technical Report TR-2004-21.
Cashell, B. et al. (2004). The Economic Impact of Cyber-Attacks. CRS Report for Congress. Web.
CERT/CC, (1999). ‘Results of the Distributed-Systems Intruder Tools Workshop.’ Web.
CERT/CC (2000). ‘CERT Advisory CA-1999-17 Denial of Service Tools.’’ Web.
Chau, H. (n.d.). Network Security – Defense Against DoS/DDoS Attacks. Web.
Chen, W. & Yeung, D. (n.d).Defending Against TCP SYN Flooding Attacks Under Different Types of IP Spoofing.
Chee, W.O. & Brennan, T. (2010). H…..t…..t…..p…..p…..o…..s…..t. OWASP AppSec. Web.
Chen, E.Y. (n.d.) Detecting DoS Attacks on SIP Systems. In: Proceedings of the 1st IEEE Workshop on VoIP Management and Security, pp 53 – 58.
“Computer Crime,” (2002) Computer Crime and Intellectual Property Section (CCIPS) of the U.S. Department of Justice. Web.
CSI (2003). CSI/FBI Computer Crime and Security Survey. Web.
“Cyber-attack Group,” (n.d.) Cyber-attack Group Launches DDoS Attacks on Turkish Government Websites. Web.
“Denial of Service Attacks,” (n.d.). Denial for Service Attacks. Web.
Dietrich, S., Long, N. and Dittrich, D. (2000). Analyzing Distributed Denial Of Service Tools: The Shaft Case. Proceedings of the 14th Systems Administration Conference (LISA 2000). Web.
“Distributed Denial of Service,” (2007). Distributed Denial of Service (DDoS) Attacks: The Big Threat in the War on Downtime. CAI Networks, Inc. 2007.
Dittrich,D. (n.d.). The ‘‘Stacheldraht’’ distributed denial of service attack tool, Web.
Dittrich, S. D. Dittrich, and N. Long. (2000b)‘ An analysis of the ‘Shaft’ Distributed denial of Service Tool’. Web.
Dittrich, D. (1999a). The DoS Project’s “trinoo” distributed denial of service attack tool. University of Washington. Web.
Dittrich, D. (1999b). ‘ The stacheldraht’ distributed denial of service attack tool’. 1999. Web. Web.
Dittrich, D. (1999c). ‘ The Tribe Flood Network’ distributed denial of service attack tool’. 1999.
Douligeris, C. & Serpanos, D. (2007). Network Security: Current Status and Future directions. Canada: John Wiley and Sons.
Dubendorfer, T. & Wagner, A. (2003). Past and Future Internet Disasters: DDos Attacks. Web.
Feagin, J, Orum, A and Sjoeberg, G. (1991). A Case for the Case Study. University of North Carolina Press: Chapel Hill, NC.
Ferguson, P. and Senie, D. (1998). Network Ingress Filtering: Defeating denial of ser-vice attacks which employ IP source spoofing. RFC 2267, the Internet Engineering Task Force (IETF).
Ferguson, P., Senie, D. (2000) Network Ingress Filtering: Defending Denial of Service Attack which Employ IP Source Address Spoofing. RFC 2827.
Forristal, J.(n.d.) Fireproofing against DoS Attacks. Web.
Geng, X. and Whinston, A.B. (2000). Defeating Distributed Denial of Service Attacks. IEEE IT Professional, 2(4), 36-42.
Giladi, R. & Serpanos, D. (2006). Security Embedded Systems. Proceedings of the NATO Advanced Research Workshop on Security and Embedded Systems. Patras, Greece.
Greenberg, A. (2007). Spam Crackdown ‘a drop in the bucket.’ Forbes.Web.
Gu, G., Perdisci, R., Zhang, J. and Lee, W. (2008). BotMiner: clustering analysis of network traffic for protocol- and structure-independent botnet detection. SS ’08 Proceedings of the 17th Conference on Security Symposium. Berkeley, USA.
Gupta, B.B. et al. (2010). Distributed Denial of Service Prevention Techniques. International Journal of Computer Electrical Engineering, 2(2), pp. 1793-8163.
Handley, M., & Greenhalgh, A. (2004). Steps Towards a DoS-Resistant Internet Architecture. FDNA ’04 Proceedings of the ACM SIGCOMM Workshop on Future Directions in Network Architecture. New York, USA.
Herr, K. and Anderson, G. (2005). The Action Research Dissertation: A Guide for Students and Faculty. Sage Publication: California.
Holz, T. (2005). A Short Visit to the Bot Zoo. IEEE Security and Privacy. 3 (3), 76-9.
“IBM BladeCenter,” (n.d.) RioRey, DataTrend Technologies and IBM provide automated Distributed Denial of Service (DDoS) Solution. IBM Systems and Technology Group. Solution Brief.
Jackobson, M., Jules, H.(1999) Proof of Work and Bread Pudding Protocols. In Proceedings of the IFIP TCI and TCII Joint Working Conference on Communications and Multimedia Security (CMS’99), pp. 258 – 272, Leuven, Belgium, 1999, Kluwer.
Jakobsson, M. & Zhou, J. (2004). Applied Crytography and Network Security. Second International Conference, ACNS 2004. Yellow Mountain, China.
Kalton, G. (1983). Introduction to Survey Sampling. Sage Publications: California.
Kargl, F., Maier, J., and Weber, M. (2001). Protecting Web Servers from Distributed Denial of Service Attacks. WWW ’01 Proceedings of the 10th International Conference on World Wide Web, New York, USA.
Keromytis, A.D., Misra, V. and Rubenstein, D. (2002). SOS: Secure Overlay Services. Proceeding of ACM SIGCOMM , pp. 61-67.
Kessler, G. (2000). “Defenses against Distributed Denial of Service Attacks”. Web.
Kim, D. & Solomon, M. (2012). Intro to IT Security. London: Jones & Bartlett Learning.
Kirk, J. (2007). Estonia recovers from massive DDoS attack. ComputerWorld. Web.
Kumar, K., Joshi, R.C., and Singh, K. (2006). An Integrated Approach for Defending Against Distributed Denial-Service (DDoS) Attacks. IRISS, IIT Madras. Web.
Lau, F., Stuart, R. Michael, S. et al. (2000). Distributed Denial of Service Attacks,” in the Proceedings of 2000 IEEE International Conference on Systems, Man, and Cybernetics. Nashville. TN. 3, pp. 2275-2280.
Leiwo, J., Aura, T., Nikandar, P. (2000) Towards Network Denial of Service Resistant Protocols. In Proceedings of IFIP SEC 2000, Beijing, China, pp. 301 – 310.
Li, J., Mirkovic, Wang, M. and Reither, P. (2002). SAVE: Source Address Validity Enforcement Protocol. Proceedings of IEEE INFOCOM. Pp. 1557-1566.
Lu, K., Wu, D., Fan, J., Todorovic, S., and Nucci, A. (2007). Robust and efficient detection of DDoS attacks for large-scale internet. Computer Networks, 51, pp. 5036-5056.
McAfee (n.d.). Personal Firewall. Web.
Matsure, K., Imai, H. (1998) Protection of Authenticated Key-Agreement Protocol against a Denial-of-Service Attack. In Proceedings of 1998 International Symposium on Information Theory and its Applications (ISITA’98), pp. 466 – 470.
Mirkovic, J., Martin, J. and Reiher, P. (n.d.) A Taxonomy of DDoS Attacks and DDoS Defense Mechanisms. Web.
Mirkovic, J., Dietrich, S., Dittrich, D., and Reiher, P. (2004). Internet Denial of Service: Attack and Defense Mechanisms. New York, USA: Prentice Hall PTR
Mockapetris, P.(n.d.) Domain Names – Implementation and Specification. RFC 1035, Internet Engineering Task Force (IETF). Web.
Nazario, J. (n.d.). Politically Motivated Denial of Service Attacks. Web.
Noureldien, N. (n.d.) Protecting Web Servers from DoS/DDoS Flooding Attacks. A Technical Overview. Web.
Ollmann, G. (2010). Understanding the Modern DDoS Threat. Web.
Oppliger, R. (1997). Internet Security: firewall and beyond. Communication of the ACM, 40(5),pp. 92-102.
Park, K. and Lee, H. (2001). “On the Effectiveness of Route-Based Packet Filtering for Distributed DoS Attack Prevention in Power-Law Internet. In Proceedings of ACM SIGCOMM’01, San Diego, CA, 2001, pp. 15 – 26.
Peng, T., Leckie, C., and Ramamohanarao, K. (2003). Protection from Distributed Denial of Service Attack Using History-based IP Filtering. Proceedings of IEEE International Conference on Communication (ICC). Anchorage, AL, USA, 1, pp. 482-486.
Peng, T., Leckie, C., Ramamohanarao, K. (2007). Survey of Network-Based Defense Mechanisms Countering the DoS and DDoS Problems. ACM Computing Surveys, 39 (1).
Sisalem, D., Floroiu, J. Kuthan, Abend, U., and Schulzrinne (2009). SIP Security. United Kingdom: John Wiley and Sons.
Sen, J. (2011). A Robust Mechanism for Defending Distributed Denial of Service Attacks on Web Servers. International Journal of Network Security & Its Application, 3 (2), 162-179.
Sterne, D., Djahandari, K., Wilson, B., Babson, B.,Schnackenber, D., Holliday, H. & Reid, T. (2001). Autonomic Response to Distributed Denial of Service Attacks. Lecture Notes on Computer Science. 2212/2001, pp. 134-149.
TippingPoint Technologies (n.d.). Modern Denial of Service Protection. TippingPoint Technologies.
Tipton, H. & Krause, M. (2007). Information Security Management Handbook 6th Ed. Boca Raton: Auerbach Publications.
“Top 10,” (2010). Top 10 Botnet Threat Report 2010. Damballa.
Vacca, J. (2010). Network and System Security. Massachusetts: Syngress.
Venter, H., Labuschagne, L., and Eloff, M. (2007). New Approaches for Security, Privacy and Trust in the Complex Environment: proceedings of the IFIP TC-11 22nd International Information Security Conference (SEC 2007), Sandton, South Africa. Springer: New York.
Vimercati, S., Syverson, P. and Gollman, D. (2005). Computer Security – ESORICS 2005. 10th European Symposium on Research in Computer Security. Milan, Italy.
Vrizlynn, L., Thing, L. Slowman, M., and Dulay (n.d.). A Survey of Bots Used for Distributed Denial of Service Attacks. Department of Computing, Imperial College London.
Wang, X. & Reiter, M. (2003). Defending Against Denial-of-Service Attacks with Puzzle Auctions. IEEE Symposium on Security and Privacy. Berkeley, CA.
Yau, D.K.Y., Lui, J.C.S. and Liang, F.(2002). Defending against Distributed Denial-of-Service Attacks with Max-Min Fair Sever-Centric Router Throttles. In Proceedings of the 10th International Workshop on Quality of Service.
Zwicky, E., Cooper, S. & Chapman, B. (2001). Building Internet Networks. USA, O’Reilly.