Abstract
In the present age of globalisation, close proximity of different nationalities often raises security issues in all countries. To combat the situation almost all countries have now resorted to biometrics security to identify and ward off the elements that can harm the security of the nation and its socio-industrial establishments. Biometrics recognition technology has achieved a covetable position in the industrial field and is on the path of tremendous success. But the increase in biometric applications has resulted in the rise of privacy infringement and identity threats including unauthenticated access to the data bases.
This poses great risk in the performance of the systems and the present crisis has initiated the system engineers to design new biometric devices by combining iris recognition technology with its biometric counterparts so that any possibility of frauds could be eliminated. Since the industry is exhibiting progress, it requires that the applications of biometric systems should reach the laymen without lowering the security services delivered to the existing government organisations and corporate bodies, and with this motive the manufacturers are trying their level best to make every biometric recognition system cost effective and user friendly. The lack of ethics exhibited by the employees who are handling the biometric devices can be overcome by stringent surveillance and proper legislation.
Introduction
Biometrics Security: The present scenario
In the present age of globalisation, the advanced information and travel facilities have made it possible to bring different nationalities of the world to close proximity which often raises security issues in all countries. To combat the situation almost all countries have now resorted to biometrics security to identify and ward off the elements that can harm the security of the nation and its socio-industrial establishments. Many researches are going on in this field to assess the performance and adaptability of biometric system and its devices. The sensors have now become small in size, more reliable and cheaper with the inclusion of advanced ergonomic attributes.
They are integrated into the security systems in the form of encryption to elicit flawless environment, thereby making them cost effective to corporations and organizations (Patrick, n.d.). Therefore, many governments are installing state of the art biometric security systems like the one installed at Manchester which scans the body of passengers for identification (Manchester Airport, 2010).
However, the accuracy of some of the biometric systems at airports and defence, generate some concerns about its adaptabilities. The negative relationships are more seen in systems like DNA, Retina and Iris based identification modes while analyzing the physical characteristics of dim fingerprints that produce unbelievable rates of enrolling failures. The latest field trial to assess the outcome of fingerprint readers using radio frequency at ATM machines like Coventry, projected an alarming failure to enroll rate to the extent of 13% because of the faded fingerprint images of elderly women (Patrick, n.d.).
In spite of these negations, the biometric applications are deployed in many strategic areas, especially in the identification of individuals in civil and criminal procedures, health care, surveillance, screening, e-Governance, e-Commerce and logical accesses. More than ever, its need is increasing day by day, and is very critical in dealing terrorist activities and checking at border crossing (Ethical and Social Implications of Biometric Identification Technology Workshop, 2005).
Scope of Biometrics
Standing on the achievements we had now in this 21st century, it is a matter of pride to see that the mere identification of eyes, countenances and fingers have led to the real identity of criminals and terrorists, and no more will it remain shadowed to make them thrive in their acts against a nation or nations or the people of the world. The developments we see in the biometrics are not a single day advent; rather it is a process of continual improvements and transitions derived from yester years (Zalman, n.d.).
This unique method of identifying a person according to the physiological and behavioural characteristics (Wildes, 1997) has undergone several dramatic changes through the years and now it has become an extensive and reliable form of security identification and personal verification solution (Arvacheh, 2006). It has added much to the IT sector and homeland security system of all countries and is applied in airports, border securities, travel documents, passports, visas, IDs etc.
It safeguards most of the governmental functions and protects national assets as well as individual identities. Services like Network security, electronic banking, investment modes and others forms of financial transactions, retail and wholesales, marketing, law enforcement, health services, insurance, social services, credit transactions, governmental networks, passport processing, driving licensing, college and school admissions and physical access to multiple utilities and innumerable day to day functions are all monitored by applying these technologies (Biometrics, 2007).
Aims and objectives
Biometrics has grown much since the September 11 attack, and the developed countries are pumping money into the industry with little hesitation. It is flourishing more than many other technological counterparts and is unbeaten with its raging $1 billion potential market. The present study is:
Would biometric security be of a real value to organizations which require high security system?
This is to highlight benefits and advantages of using the biometric security in detecting the criminal and protecting the society from them.
Aims
- To understand the different types of biometric security and its applications
- To ascertain whether biometric security will become cost effective to organizations which require higher level of security systems
- To assess the effectiveness and accuracy of iris recognition biometrics when compared with its counterparts
- To analyze the ethical issues arising from use of biometrics
The main objectives are
- To conduct secondary research to establish the types, scope and limitations of biometrics
- To examine organizations that has implemented biometric security.
- To identify where possible solutions to potential problems exist and to recommend a series of steps that could be taken into consideration to improve biometric security technologies.
In order to find out answers to the research questions and objectives the constituents relating to Biometrics security are placed under different chapters, viz.
- Introduction: It gives a brief account of background, problems and lead to the research approach.
- Literature Review: The entire data collected is reviewed here.
- Methodology: The data collection methods and analysis are done under this head
- Results (Analysis): Findings derived out of the study is elaborated in this chapter.
- Discussion: The findings are analysed and discussed here.
- Conclusion & Recommendation: The outcome of the research and recommendation for furtherance of the study are given under this chapter.
Literature Review
Introduction to Biometrics Security: The present scenario
In the present age of globalisation, the advanced information and travel facilities have made it possible to bring different nationalities of the world to close proximity which often raises security issues in all countries. To combat the situation most of the countries have resorted to biometrics security now to identify and ward off the anti elements that can harm the security of the nation and its sensitive establishments. Therefore, biometric security technologies demand more attention on account of its reliability and accuracy in identifying and authenticating the individuals in border crossing, defence, and socio-industrial establishments.
More and more research is going on in this field to assess the feasibilities and performances of biometric systems, and to know the adaptability of certain biometric devices. The sensors have already become small in size, more reliable and cheaper with most advanced ergonomic attributes. These devices are integrated mainly into the security systems in the form of encryption making them cost effective to corporations, organizations and airports (Patrick, n.d.). Many governments are moving toward installing biometric security systems similar to the one installed at Manchester that scans the body of passengers for identification to reduce problems of illegal entrants (Manchester Airport, 2010).
The Achilles’ heel in Biometrics
However, the accuracy of the biometric systems and their applications at airports and defence, invite concerns about their adaptabilities. These negative elements prevail in the maintenance of accuracy in DNA, Retina and Iris based identification modes, and especially in fingerprints identification, where the dim fingerprints produce unbelievable rates of enrolling failures. The latest field trial to assess the outcome of fingerprint readers using radio frequency at ATM machines like Coventry, projected an alarming failure to enrol rate to the extent of 13% because of the faded fingerprint images of elderly women (Patrick, n.d.).
While the identification technology acquires more involvement in our everyday life, the misuse of latent data and surveillance will bring forth problems innumerable as the potential information and surveillance are controlled by individuals or enterprises, making the whole system unproductive. This situation warrants international initiatives in regulating the norms and procedures of biometric security applications considering the ethical and social paradigm and other related implications.
The biometric stalwarts opine that education together with innovative policy making can very well reduce the negative interjections about the technology applications, though they know not what sort of policies will support the system, for any gesture towards this will invoke global issues, and any such move will become ineffective sans the submission of global community (European Commission, 2005).
The past four years have seen the public demanding a high tech and result oriented universally feasible identification technology, and their outbursts have forced Mr. Tony Blair to declare that priority would be given to develop a sophisticated and potential biometric system that could make the borders of Europe secure. Nevertheless, the very biometrics evokes limitless social and other legal concerns like monopolizing the custody of information and the misuse of potential data.
Apart from these, there is the presence of cultural difference in approach between the USA and Britain towards the data protection issues. The United States cherish a consumer perspective, whereas Europe, especially the UK, considers it as the fundamental human rights, which projects biometrics as basically a bio-politics issue in the present socio-ethical environment rather than adopting affordable technical means (European Commission, 2005).
History of Biometrics
Standing on the achievements we had now in this 21st century, it can be seen that the mere identification of the body parts such as eyes, countenances and fingers have developed into the revelation of the real identity of criminals and terrorists, and the biometric information will not remain concealed now restricting the aliens from unleashing their inhuman activities against a nation or nations or the people of the world. The developments we see in the biometrics are not a single day advent, but it is the outcome of a process of continual improvements and transitions gifted by the yester years.
Though the history of biometrics has its origin from 14th century in China (Zalman, n.d.) it remained obscure till the 19th century. The only mode of identification was totally dependent on the memory and knowledge of persons by others (Holmes & Walmsley, 2005). But in 1882, Alphonse Bertillon introduced a new idea called anthropometry where he resorted to scars, birth marks, and tattoos for personal identification. This method was called Bertillonage, and it remained the basic criminal identification method during the entire past century (Homeland Security, 2009).
Considering the pains in gathering the measurements and the inaccuracies, the Bertillonage method was quickly replaced by Fingerprinting which proved accurate and more reliable. Willian Herschel accepted fingerprints as a valid form of signature in the 1870’s and Sir Francis Galton made sufficient modifications to this method later on.
He established that there existed no similar fingerprints among the human beings, and that the difference in characteristics could be collected from the fingerprints as it would not change throughout the life span of an individual. Yet, their theories were not recognized till 1897 when Edward Henry introduced the Henry Classification system in India. The system was subsequently introduced in Britain with necessary alteration in 1901, and then in America in the year 1902 (Homeland security, 2009a).
Biometric technologies have now become the main application for extensive and reliable form of security identification and person verification solutions (Arvacheh, 2006) and they follow certain norms, which are given below:
- Universality: Every human has some characteristics of his or her own.
- Uniqueness: There will not be identical characteristics
- Permanence: The characteristics shall not vary with time
- Collectability: These attributes will be measurable and collectible
- Performance: It should bring out accuracy irrespective of environment
- Acceptability: The sample collection methods must be acceptable and reliable
- Circumvention: No fraudulent measures shall creep into the methods applied and shall be beyond any deception (Biometrics, 2007).
Importance of Biometrics after 9/11
After the attacks in September 11, 2001, Europe and the USA were obsessed with the call of war on terrorism. Though the USA was the main party to this war, the United Kingdom joined them being their staunch ally. Britain has precedents in dealing with domestic terrorism like IRA in North Ireland, and the 9/11 shook the administration that it introduced several bills in succession followed by the Prevention of Terrorism Act 2006 (Sim, 2010). Madrid bombings of 2004 have actually catalysed the anti-terrorist activities of UK, and much before 9/11 the EU had enhanced the internal security of the member nations by designating the Europol to deal with anti terrorism tasks (The EU and the Fight against Terrorism, 2006).
The European Union adopted biometrics in 1997 by instituting a database called Eurodac to regulate the flow of asylum seekers. It contains the digitalized form of fingerprints of the persons who seek entry in any one of the countries of the EU consequent on political oppression. Subsequent to 9/11 incident, the USA has implemented a unique biometric visa programme in accordance with the Enhanced Border Security and Visa Entry Reform Act of 2002. The data collected by the consulate at the time of visa application has to be cleared by undergoing DHS Automated Biometric Identification System before the issue of a visa to the applicant (Ceyhan, 2008).
During this period the US was struggling with administrative setbacks in combining the different border agencies to form the Bureau of Customs and Border Protection (CBP) under the DHS, which was a new concept for US departments. However, the problems were not that much severe when compared to the EU scenario, which was known to be a “limitless political, legal and bureaucratic nuances of institutions, rules, national cultures and, not least, reigning personalities” as stated by Meyers et al. (2007).
The 2007 VWP reforms permitted the DHS to process applications from countries having refusal rates that ranged from 3 to 10% if they were “actively cooperating with the US to prevent terrorist travel including sharing counterterrorism and law enforcement information” (Implementing Recommendations of the 9/11 Commission Act of 2007) & (Hobbing & Koslowski, 2009). BMS was then expected to serve the VIS while anticipating the new biometry-based systems like Eudora and SIS II (Paul, 2007).
Thereafter, the Schengen Information System II (SISII) was implemented in the EU to keep away the unwanted third country elements (Ceyhan, 2008). Passenger controls in airdromes, border control, access to databases etc., are only a few examples of biometric security applications. Presently, iris recognition based technologies are applied heavily to improve border controlling facilities and travel assistance at UK airports (New passport design unveiled, 2010).
Types of Biometric security applications and problems faced by them:
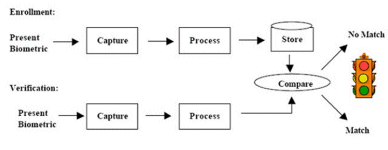
Authentication of biometric security identification demands the tallying of the enrolled biometric template with the current biometric sample captured at the point of the required identification time. This is done by searching the entire database for the required match that is available in the network. This process is called one to many options matching, and in verification mode, when the system confirms the identity of a person from the previous one; it is termed as one to one mode of matching. Suppose that a user tries to an account and inserts the token of identification in the form of a smart card, without entering the password, a simple touch or look at the camera will take the person directly to his account after authenticating the user as shown in Figure-1 below (Biometrics, 2007).
The biometric techniques aforesaid do not consider the local environment relating to the systems. Here, the local elements mean the elements like software, equipments, tools, people, status, statutes etc. When these are altered it will affect the performance of the system generating uncertainties. Therefore, when a biometric solution is identified factors like vulnerability, uniqueness, strength of the supporting system and its longevity, scope of re-enrolment and error reporting etc. are taken into account.
The information system that is attached to it will present an analysis of every stage beginning from the subjection of the individual into the system for identification till the display of the match result that appears on the information window. The information and the ergonomics of the user, the working environment, liveliness, mental state, cultural traits etc., are also deciding factors on par with the technical data that are fed into the system design (Dale et al., 2006). The following are the biometric methods adopted for person identification.
- Fingerprints: The ridges and valleys seen on the fingertips of an individual are unique. No other person will have the same characteristics. This physical trait is hence adopted by all countries for identifying a person.
- Face recognition: An individual can be identified with his or her facial images captured in different angles. The facial images are captured either by a camera or through the subjection to the infrared heat emission.
- Speaker recognition: The acoustic characteristic of speech is used here as the method of identifying a person.
- Iris recognition: The patterns of iris are captured using an image collecting system and the same is analysed for identification.
- Retina: Here, the biometric template is created by enrolling the patterns of capillaries at the back of eyes.
- Hand and finger geometry: The unique characteristics of hand and fingers are the basis of identification in this method.
- Signature Verification: By analyzing the signature, the identification of a person can be done in this mode (Homeland Security, 2009).
- DNA Fingerprint: In DNA fingerprint the specimen tissue of the person is sequenced and the tiny DNA segments are compared to find out the match.
- Deep Tissue Illumination: The tissues of the body are illuminated and the data collected are compared with the variables related to light reflection.
- Keystroke Pattern: This system compares the keyboard typing patterns of the individual against the data relating to the previously recorded patterns for identity recognition (Questbiometrics).
Since there is no end to the applications of biometrics, new devices are flooding in the current market. The latest applications are
- Biometric Time Clocks used in companies and offices to regulate the timekeeping of the employees,
- Biometric safes, biometric locks and biometric access control devices that are meant mainly for home and office securities,
- Biometric systems that control access to personal computers, and
- Wireless biometrics that offers high end security through PDA etc. (Questbiometrics).
But these applications have problems relating to acquisition and transmission. Also they have limitations in storing templates in the systems (Encyclopedia.jrank.org).
It is widely accepted that authentication is based on the three fundamentals such as password, token and biometric of the person (Nanavati et al. 2002). Currently, password and PINs are the most relied on authentication mode which is not dependable due to thefts and hacking (Pointsec, 2005; Clarke et al. 2002). Though surveillance based security technologies (SOSTs) offer enhanced security they are prone to infringing the privacies of individuals. Moreover, people are concerned about the purpose of the government to adopt such surveillance methods, and therefore, they consider SOSTs as privacy infringement applications (Pavone, 2010).
Cost effectiveness of Biometrics security applications
The emergence of Biometric technology as a major industrial wing is significant if seen against the other security alternatives that enjoyed monopoly in the field. Biometrics is conquering all fields at a time when online identification and verification processing are shadowed by the frequent frauds in the payment technology. Whatever it is, unequivocally it could be said that biometric technology which has reliability, accountability and cost effectiveness will experience tremendous success in the days to come.
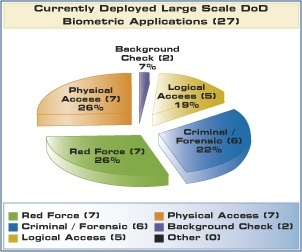
It has already created a new saga in taking organizations, large and small, in its confidence, and security agencies, governmental institutions, financial services and the laymen are all attracted to biometric security systems. The Figure-2 given below will give an idea about the mass appeal the biometric applications enjoy (Evaluating the Capability of Biometric Technology, 2009).
Biometrics has established its firm presence in fingerprint analysis and authentication in networks, PCs & laptops, and handgun safes. The security parameters of biometrics are:
- False Accept Rate (FAR) which is the number of false inputs matched with the previous templates (Evaluating the Capability of Biometric Technology, 2009).
- False Reject Rate (FRR) which is the number of true inputs matched with previous templates (Evaluating the Capability of Biometric Technology, 2009).
The manufactures of biometric devices are bent upon making improvements in the accuracy level by bringing down FAR and FRR factors (Evaluating the Capability of Biometric Technology, 2009). The biometrics techniques, being very complex, keep the power consumption low to make it cost effective which is essential for embedded systems. At present, the dynamic reconfiguration techniques are adopted in software-driven radio and cryptography. It is also heavily used in aerospace missions.
Biometrics needs strict image or signal processing with viable but flexible computations in real time, to cope with the advancing person identification algorithms that improve error rates. Because of this improvement, the consumers are becoming more satisfied and confident in accepting biometric devices which calls for frequent upgrading of the existing biometric products in the market. Cost effectiveness acts as the main guiding factor for using partial configurability by the biometrics and that counts much in a competitive market filled with myriad of products from consumer electronic sector. Security and accountability can be improved through enhancing the computational biometric verification algorithm which in turn will make the cost become proportional to the algorithm variations (Fons & Fons, 2010).
Till recently, the manufacturers of biometric technology based products have concentrated their business only around governmental buildings and prisons. The public never dared to imagine a fingerprint scanner or digital imaging equipment will become true before their eyes, but now the advanced biometric technology has proved that such products are no more dreams. The 2004 survey made among 840 corporate chiefs in Europe, Africa and the Middle East (Kevin, 2003) & (The Solutions: Cost-Effectiveness, n.d.) has revealed that:
- 68% – believed that biometrics is a reliable and justifiable security measure
- 39% – anticipated staff or customer resistance to the system
- 37% – believed that the companies could misuse biometric technology provisions
- 51% – believed that biometrics is prone with identity-theft
- 55% – are considering to adopt fingerprint or iris verification security systems
- 47% – believed that technical malfunctions could create problems in biometrics
- 80% – agreed that biometrics is useful for border control & government security
- 89% – agreed that biometrics is adaptable for the various activities of FBI and CIA
- 74% – admitted that biometrics is the best tool for the validation of credit cards
- 70% – welcomed adoption of biometrics for processing personal ID cards
- 53% – agreed that biometrics is effective in handling welfare payment s (Kevin, 2003) & (The Solutions: Cost-Effectiveness, n.d.).
According to the Gartner Group a password oriented call to a help desk consumes 30% of the real time and the password resetting cost ranges from $30 to $150. The Marriot hotel chain having 30000 associates needed their passwords changed after each 90 days to enable corporation information security. The cost borne by the hotel chain is at the rate of $30 per password change. So, $30 x 30,000 associates x 4 changes per year will cost around $10.8 million per year. Just imagine how much money the Marriot hotel can gain on installing biometric security. For, in biometric security there exists no password (Elizabeth, 2005).
Accuracy of Irish recognition as a major method of biometrics security
Iris recognition system is the most viable and leading biometric security application compatible to sensitive areas such as defence, aviation and border control. The e-commerce and banking sector has already adopted this system massively due to its accuracy, reliability and cost effectiveness (Hudson, 2010). This recognition system works effectively for all, and even a blind person’s iris can be subjected to the recognition process. The accuracy rate is higher than other biometrics identification system and an error is limited to one in 1.2 million chances. Iris recognition does not need any body contact with the camera and is compatible to other security systems.
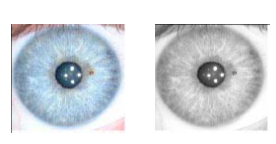
The problems connected with iris recognition equipments are very less, that is to say as only 1% (The Solution: Cost effectiveness, n.d.). Iris recognition Biometric system is the easiest when compared with its counterparts as the pattern comparison is limited to the annular area between the pupil and white sclera. Irises exhibit (Figure-3) complex and rich characteristics and they differ from one person to another (Sirvan et al., 2005).
Biometrics-Emergence of new industries
The industries in the modern times have discovered that security is the prime issue for their smooth functioning and that information is the most valuable asset which cannot be compromised at all. It is because information is essential to increase productivity and quality in terms of profit margin (Inman, 2000). When businesses become more dependent on information they need to protect it from unwanted physical access, fraud or theft. The relevance is convincing as there were only 10000 biometric devices in 1996 with annual growth rate of 7.5% each year (Randall, 1999). The cost of the biometric devises is coming down sharply which will boost the prospects of biometrics industry (Arnese, 2000).
In order to evaluate the emerging biometrics industry, it needs to be segmented first as technology, vertical markets and the applications (Eric, 2000). Figure-4 depicts the typology.
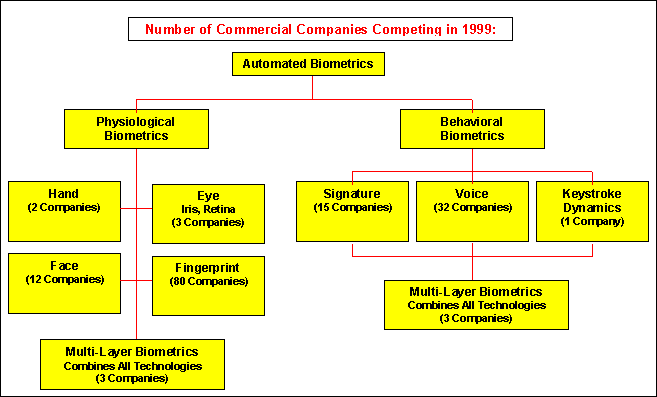
The automated biometrics industry can be put into two categories namely, physiological and behavioural biometrics as shown in the above figure. Physiological biometrics does not change, according to Eric (2000), whereas behavioural biometrics concentrates on signature and voice of a person and keystroke dynamics for person identification. Biometrics centred industrialists are currently on the move to make devices depending on body odour, ear shape and veins. Irrespective of the segmentation, these technologies analyze the information adopting the same process consisting of capture and extraction and then comparison and matching, wherein extraction denotes taking out the data from the capture for creating the template, whereas comparison pertains to the matching of the new sample with one in the template (Inman, 2000).
Ethical and Social Implications of Biometric Identification Technology
While the identification technology acquires more involvement in our everyday life, the misuse of latent data and surveillance will bring forth problems innumerable as the potential information and surveillance are controlled by individuals or enterprises, making the whole system unproductive. This situation warrants international initiatives in regulating the norms and procedures of biometric security applications considering the ethical and social paradigm and other related implications.
The biometric stalwarts opine that education together with making of innovative policies can very well reduce the negative interjections about the technology applications, though they know not what sort of policies will support the system, for any gesture towards this will invoke global issues, and any such move will become ineffective sans the submission of global community (Ethical and Social Implications of Biometric Identification Technology Workshop, 2005).
A recent investigation conducted by the Gizmodo team dug out 100 photographs from the storage of the Gen 2 millimeter wave scanner belonging to the Brijot Imaging Systems. These photographs were obtained after getting information that the U.S. Marshals who were handling the machine in the Orlando courthouse had saved some images of the scans. The leaking of the images reveals the unethical handling of machines by the employees in the courthouses and airports in the country.
The incident is a clear cut violation of privacy and shows the unethical attitudes of the federal employees in handling such biometric equipments. It was reported that the images were removed by the Marshals in Orlando and were delivered to FOIA before returning the machine to the manufacturing company (Johnson, 2010). A fellow citizen has discovered that these images if placed inverted in the Photoshop a real vivid picture could be gained out of it (Frucci, 2010).
The scientists hold that during the scan, the X-rays will penetrate the dress of the passengers to bring certain physical hazards to them. It is assumed that though the radiation due to the x-rays is only about 0.02 microsieverts, it would be alarming that around 700 million passengers are affected adversely due to this, when one person among 20 are prone to radiation which causes BRCA-1 and BRCA-2 mutations related to breast and ovarian cancers (Knox, 2010).
Many have pointed out that biometrics is directly proportional to the privacy (Rosenzweig, 2004) and that it would not make any sense in discussing biometrics without assessing the infringement of the privacy. Concerns are abundant like misuse of the permission, illegal tacking for surveillance to perform social control, harming the status of anonymity, identity theft, cultural and religious problems etc. Therefore, adoption of biometrics technology needs evaluation (Liu, 2008). According to Fleming (2010), it is essential that a biometric security application should adhere to the principle of authentication without the involvement of identification as authentication without the insistence of identification safeguard the privacy of the user.
Limitations
The research was focused on the evaluation of performance of different biometric security systems and its prospects as a cost effective technology that provide solutions to the problems of security at all sensitive and business areas while authenticating different individual transactions in varied sectors of modern societal life. In pursuit of information to materialize this project, the researcher has to encounter some problems in gathering relevant data.
Many institutions were not willing to transfer information regarding their companies and some individuals who received the questionnaire were reluctant to answer the questions. Nevertheless, somehow the researcher managed to overcome these problems. Sufficient books were not available to answer the research questions and hence the next option of collecting information from authentic web sites was adopted. The time constraint and the limited budget also posed certain setback in the study.
Methodology
Introduction to Methodology
Research in generic means search for knowledge. Therefore, research methodology can be identified as a systematic approach adopted for solving a research problem scientifically, wherein the various steps are applied and analysed through logic means. The research methods are classified into 4 groups viz., (i) Descriptive vs. Analytical, (ii) Applied vs. Fundamental, (iii) Conceptual vs. Empirical and (iv) Quantitative vs. Qualitative. Here, quantitative research is applied with respect to the quantity of the data whereas, qualitative research, more or less, involves the quality or kind (Research Methodology, 2010).
According to Habermas (1972), every research made shall be in accordance with motivation which is guided by interests and values. The social and personal notions of the researcher will naturally find a place in such researches. Therefore, the value problems that may come up while the researcher traverses to fulfil the task will naturally become the guiding principles for the study. This research paper, as such, engages in values and interests, ethical codes, practices and societal welfare. To complete the task the researcher has investigated the available literature and learning procedures which put insights to formulate ideas to achieve the objectives. Qualitative analysis and cross studies were incorporated to streamline the research.
The useable literature on biometric technologies was re-examined and a questionnaire was contrived and utilized to gather applicable data for this research. Further, to find the required answer to the research question, one to one interview was also held. The sampling population was selected in a purposeful way and qualitatively examined. There were some useful sources over the Internet about research methods which were put to study (Cronje, 2005; Trochim, 1996-2004).
Yin (1994) and STORRE (2002-2006) state that:
Every type of empirical research has implicit, if not explicit, research design. In the most elementary sense, the design is a logical sequence that connects empirical data to a study’s initial research questions and ultimately, to its conclusions. In a sense the research design is a blueprint of research, dealing with at least four problems: what questions to study, what data are relevant, what data to collect, and how to analyze the results (Yin, 1994 & STORRE, 2002-2006).
Selection of research technique
There are many elements to be considered before selecting a method as there are benefits as well as drawbacks with every method chosen, and the researchers have to discover the most appropriate for them. According to Jarvinen (1999) it is more effective to separate research into approaches rather than methods. In addition, the research techniques utilized in the theory-testing approach are field studies, reviews, and field tries out.
The features of such study are the hypothesis, form or structure which is gathered from literature, formulated or polished to conform to that specific study. The purpose of this research was to find answers to the question: Would biometric security be of a real value to organizations which require high security system? This was to highlight benefits and advantages of using the biometric security in detecting the criminal and protecting the society from them.
Other aims were:
- To understand different types of biometric security.
- To understand how biometrics is applied and used by organisations.
- To assess the effectiveness and accuracy of iris recognition biometrics when compared with its counterparts
When an investigator wants to construe an incident the study is expected to serve an understanding purpose. Firstly, the understanding should support the researcher to augment the knowledge of the studied incident. Secondly, it should build up new thoughts and theoretical views, and eventually the purpose permits disclosing of on hand problems inside the phenomenon. The present research is fulfilled by examining the views of individuals on various biometrics applications and cross studies of the acquired literature. The opinions of the individuals were analysed to ascertain the feasibility and adaptability of the devices and to know how far such systems infringe the privacy of the individuals.
The market trend and the conviction of the public on the advancement of this technology as an emerging industrial sector were collected systematically. While gathering data from these samples maximum effort was put in to avoid any embarrassment to the respondents and interviewees (Roberts & Patel, n.d.).
A set of nine predetermined questions was drafted for the questionnaire and another set of 5 questions was prepared for placing before the interviewees. These questions were drawn to assess the public’s opinions about the biometric technology, the violation of ethical standard in handling the devices, the advancement of the technology as a major industrial sector, and how far it could convenience the people.
Also it was intended to evaluate the effectiveness of the technology in person identification while safeguarding the interests of the people as well as the security of the nation. The in depth one to one interview and the questionnaire helped the researcher much in exploring the topic in detail, though the interviews were short and objective, and were limited to duration of 15 minutes. The time of the interview was limited to 15 minutes to maintain the focusing on the questions and to avoid their unnecessary harangue. Such a limitation enabled the interviewees to maintain more interest in answering the questions with enthusiasm. Moreover, it helped the interviewees to save their much valued time.
The main purpose of these interviews and questionnaire was to extract the current trends of the homogeneous segments of the various respondents. Most respondents expressed concern over the manipulation of the biometric information by the authorities and at the same time they were optimistic and admitted that the technology is fast developing and that it would change the style of modern living. Biometrics has now entered the wider range of business world where at times the consumer interests are jeopardized though every device is designed to advance the consumer convenience (Roberts & Patel, n.d.).
Population and Sample
The researcher decides and describes the population based on the types of data that are collected with reference to time, territory and other appropriate component such as individuals and age. Furthermore, the region of the population has to be defined, and according to Miller, the territory is government limits e.g. a city or a region (Miller, 1998). Non-probability sample distribution is undertaken when the investigator has some control over the chosen sample.
The investigator can select the sample established on judgment or repute, expediency, share, and/or offers (Miller, 1998). The questionnaire was therefore, given to the general public whose age was between 17 and 68 years old. I found that the people of this age group were more prudent in assessing a situation and were capable of answering the problems effectively.
The questionnaire was also given to the company staff after obtaining permission from their management, so that the answers would be very authentic and free from prejudices. The researcher was under the impression that they would interact with each other to share their thoughts about biometrics. The organizations which were selected for participating in the survey had more than 100 employees. Around 9 companies were contacted and they told the researcher that they were interested to invest in biometric systems, but they wanted to remain anonymous in this research. Also, thirty five odd individuals were interviewed and their details were held back due to the researcher’s commitment to them that every detail they provided would be held confidential.
Data collection
The primary data collection was based on literature, interviews and questionnaire. The details provided by the informants were considered as supplementary data and therefore, the processes and documents review related to organizations and communities were included in the study, Electronic archival research comprised of information from the webs and hard and soft copies of newspapers and other related sources. The interviews have become conducive to comprehensive analysis to which 35 individuals of varied ages were interrogated on the issues related to biometric technologies and their use, the role of the stake holders, advantages and disadvantages of the systems (Roberts & Patel, n.d.).
Results (Analysis)
According to Daymon (2002) “there are no general set of laws and stages of qualitative data analysis; nevertheless the qualitative analysis is about reduction and interpretation”. The collected data were detailed, therefore it was important to make it more manageable. A questionnaire was used to collect parts of the data for this dissertation to analyse the results in a qualitative way. The results were examined and then a meaningful conclusion was drawn out of it. The analysis of the data which were collected through interview and questionnaire was done by means of inductive approach, wherein inductive analysis denotes the origination of information inherent in the data itself.
The data thus collected were condensed and evaluated by adhering to the thematic codes. The themes were the resultant elements of the data, interview questions, questionnaire, and the learning of the available literature (Roberts & Patel, n.d.). The following pie-chart (Figure-9) depicts which biometric techniques the respondents are conversant with. The three main techniques recognized are finger scan, voice-scan and eye-scan. The result is as follows:
26 out of 41 respondents recognized finger-scan, 19 out of 41 are aware of eye-scan and 13 out of 41 were able to tell about voice-scan. Finally 11 people did not recognize anything about biometric systems.
Most of the respondents do not have any knowledge or experience at all of biometric systems as depicted in this graph. It indicates that out of 41 respondents 33 lack knowledge or experience of biometric-systems and 8 out of 41 have some experience of biometric-systems. Majority who experienced biometrics were when they entered the borders of USA.
The above graph depicts the attitudes towards using biometric as a safety means for getting at the workplace or signing-in on the computer. This graph shows us a clear view that the respondents had a positive outlook for using biometrics. Out of the 41 respondents questioned 28 showed positive attitude whereas 7 of them had a negative attitude while 6 were uncertain. Some of them feel that even though biometrics increases the security but they have to do with too many passwords and some of them feel that it may not be worth the cost involved.
The above figure depicts the respondents’ belief as to whether biometrics increases the security or it does not do so. The graph also shows how many respondents were uncertain about it. Out of 41 respondents only 34 were positive while 4 were on the negative side and 5 of them were not certain at all about the security features of biometric. Majority of the respondents feel that a combination of biometrics as well as the traditional system would work better.
The following graph displays the attitude of the people towards the usage of eye-scan, facial-scan, signature-scan, keystroke-scan, voice-scan, hand-scan, and Finger-scan. Most of them believe that hand-scan and finger-scan are the easiest and best techniques of biometric systems. 32 respondents out of 41 felt that hand-scan was very easy and it was good while 34 felt that finger-scan was better and easier to apply. 21 respondents felt that eye-scan was the easiest and a better system. This came as a surprise and that 10 respondents felt that eye-scan was uncomfortable. 20 respondents had a negative feeling towards signature-scan and 19 were doubtful of voice-scan.
This graph shows 23 out of 41 respondents preferred finger-scan and 10 of them liked hand-scan. Since these two techniques, are very easy to follow, and trustable they are preferred by majority of the respondents. 6 out of 41 respondents believed that eye-scan was easier and they felt that this technique was most natural.
The figure below shows that 22 respondents out of 41 felt that they had worries about their personal data stored for biometric purpose may be used for other purposes as well. 3 respondents were uncertain while 16 of them remarked that they were not worried at all. The majority of the respondents felt that criminals might use their personal data so stored and may use it for purposes which might bring in great troubles.

Finally, when the respondents were questioned about the future of biometrics as a secured system for security purposes they said that the suppliers of such systems must first of all create awareness among the public so that such techniques can be adopted by the organizations. They must market their products in a way which would bring automatic awareness among the buyers of such products. In fact most of them felt that such techniques should also be viewed from the point of costs involved in their adoption. Reliability on such techniques must also be increased. Some respondents stated that regrettably the system was used by most countries and organizations only when terrorism and company surveillance increases to a defenceless situation.
Questionnaire
This survey is strictly academic and anonymous.
- Gender:
- Age:
- Which biometric solutions do you know of?
- Do you have any knowledge of biometric-systems either in your organization or somewhere else?
- What would you say about using biometrics, for example why, and why not?
- Do you feel biometric security solution is more secured than the traditional ones used or do you feel a combination would be better?
- What is your thought about using these unusual techniques?
- Finger-scan?
- Facial-scan?
- Eye-scan?
- Voice-scan?
- Hand-scan?
- Signature-scan?
- Keystroke-scan?
- Which one of the techniques mentioned above is your preference and ease to use?
- What do you feel about biometric data being stored in a database?
- Are you worried that the personal data about you that is stored may be used for a diverse purpose?
- How do you think biometrics can become successful?
One-on-One Interview sample Questions (35) interviewees.
- Do you know what biometric technologies are?
- As a manager, what would you consider to adopt biometrics in your company?
- Do you feel that all biometrics systems are error proof?
- Do you feel that the interfaces used by your company are accessible to everyone?
- Do you feel that biometric technologies could assist to breakdown barriers? (Chu & Rajendran, 2009)
Aggregated Results
The data was derived by aggregating the responses of all participants.
Do you know what biometric technologies are?
Results: 24 out of 35 knew well about biometric systems of security. 10 out of 35 do not know much about it but they have heard of it. 1 out of 35 has no response and confused the term with biotechnology. (Chu & Rajendran, 2009)
As a manager, what would you consider to adopt biometrics in your company?
Results: 10 out of the 35 like to have biometric systems in their companies to check the attendance of the employees and to get access to the company data. 25 out of 35 had no practical knowledge of implementing the systems. (Chu & Rajendran, 2009)
Do you feel that all biometrics are error proof?
Results: 20 out of the 35 believe that many biometrics devices are error proof though they admit there are some challenges to it. 5 out of the 35 believed that there are errors and wants rectification. 9 out of the 35 held the view that the technology is still far away from the reach of laymen and are not user friendly and cost effective. 1 out of 35 had no opinion at all. (Chu & Rajendran, 2009)
Have you heard of the ADA?
Results: 17 out of 35 agree that they know what ADA is, but only 12 were able to distinguish its purpose. (Chu & Rajendran, 2009)
Do you feel that the interfaces are accessible to everyone?
Results: 31 out of 35 replied: Yes. 3 out of 35 said: No. 1out of 35 expressed ignorance. (Chu & Rajendran, 2009)
Do you feel that biometric technologies lead to breakdown barriers?
Results: 5 out of 35 were affirmative. But 1 out of 35 was negative. 29 out of the 35 admitted their ignorance in the matter. (Chu & Rajendran, 2009)
The questionnaire and the interviews revealed the following information with regard to the favourability to the different biometrics devices:
Out of the 35 respondents, 77 percent agreed that biometric technologies are very useful as a tool for authentication of identifying people. 16 percent of them were in favour of the scalability, accountability, security and ethics of biometrics. But 7 percent of the respondents disliked the use of biometrics. According to Chu & Rajendran (2009) “The technology that respondents most widely accepted was fingerprint recognition
(rated 8.15/10), followed by iris recognition (7.9/10). Signature recognition received the lowest acceptance rate (5.72/10). When asked to rate the places it should be used, respondents favoured using biometrics for office building security, travel, air transportation screening, medical procedures, banking and other financial transactions, and government functions. However, many did not feel that the technologies would be useful in an educational setting.”
Role of Stakeholders
Most of the respondents are of the opinion that the government plays the key role in biometric systems as it has got the responsibility to ensure the privacy of the people as well as security. A standard is necessary and the government should implement it. With regard to businesses security has prime importance. Other main responsibilities include protection against fraud, assistance to stakeholders, and improvement of efficiency of the biometric systems. There should be stringent action on the part of the users to protect the biometric information of the citizens. The respondents expressed firm stress on the need to maximise the training programmes and to minimise the use of the technologies towards protection and security of the citizens (Chu & Rajendran, 2009).
Advantages and Disadvantages of Biometrics
The main advantage of biometrics is the enhanced security that the systems provide while ensuring maximum accuracy. It reduces paper work, and offers the unique feature of protection from duplicating or copying or loss of information. The most dreaded disadvantage of biometric technology is the possible infringement of privacy of the individual. The capital investment to install the devices is also very high (Chu & Rajendran, 2009).
From the above studies it can be concluded that there exist certain amount of concern among the public towards the use of biometric systems due to the possible invasion of person’s privacy, irrespective of the benefits the systems offer. Therefore, the public insist that the government and the business sector should build up the trust and safeguard the interest of the people. As an industry the future of biometrics devices are very bright as the demand for them is increasing rapidly. The TechCast (2009) reports show that the need for biometrics is growing rapidly, that is to say at a rate of 35 percent per year.
Educational institutions, governments, private organisations etc. have major roles to play in this field by enhancing and promoting the technology through knowledge dissemination and implementation of strict usability and reliability standards. According to TechCast (2009), “biometrics is expected to enter the mainstream (at a 30% adoption level) in 2015 with a $380 billion U.S. market size, a $1368 billion world market, predicted at a 73% expert confidence level.”
Discussion
The term Biometrics has been in use since the 19th century to denote the statistical analysis of data in biological science and now it refers to the automated identification of individuals by applying their biological traits with the help of information technology. The biological traits are analyzed through scanning the iris, face, signatures, fingerprints and hands, and also by deciphering the voice patterns of an individual.
Biometrics is thus defined as the system of analyzing the available statistics of biological data which is measured in terms of physical as well as behavioural characteristics of an individual for identification purpose. In other words, it is the science of measuring a person’s physical or behavioral characteristics for verification and identification. Biometric techniques play an important role in verifying the real identity of any individual in highly classified security applications (Ewg.iee.org, n.d.).
Biometrics in the current scenario
Therefore, identification of a person is a necessity in order to carry out the myriads of business transactions and functions in our every day life including health care, finance, law enforcement, communication, border security, aviation, industries and organisations, governmental as well as private managerial functions, and the like. It acts as the most effective tool against terrorism, which enables a country to ward off the alien people entering its dominion.
Further, the human society has progressed much with the use of electronics and automated machines, and the conventional application of passwords and electronic cards have become obsolete and useless as they can be fabricated or manipulated by any one that comes across it or these can be lost irrecoverably. In biometrics, such things will not happen as identifying a person is facilitated through deciphering the physiological and behavioural characteristic of every individual. This person identification is achieved through Positive Identification method which denotes the verification of the identity or authentication based on the enrolled identity particulars of that particular person.
Commercial applications like electronic data conversion, logins, internet access, e-commerce, credit card, ATM, mobile phones, medical records, web security etc. are examples of authentication applications. Integrating the technologies in the processing of smart cards, digital signatures, encryption keys etc., biometrics performs a vital role. Thus the identification of a person from the biometric details in the database having millions of enrolled identities has much significance in this context (Jain, 2004), (UK Passport Service, n.d.) & (Biometrics, 2007).
The rapid developments in the field of science and technology have made it convenient to use biometrics devices effectively. Now a user can enter an account with a proper user name or a smart card and with a finger touch or looking at a camera his authentication will be fulfilled. Loss of smart card, IDs, keys, password etc. can happen and biometric recognition can solve such problems. It is user friendly and cost effective, and also guarantees fastness, accuracy, reliance etc. (Biometrics, 2007).
Since the 11 September terrorists attacks, both the US and UK are exploring the feasibilities of biometric security to increase the security at airports, army and governmental establishments, and this caused stocks in biometrics companies to increase up to 130% in 2002 (Anderson, K. 2002). Though the biometric systems have advantages, equally there are disadvantages. Effective engineering principles should be sought to enhance the security level. As the influence of biometric technology increases there will be corresponding rise in the potential threats to the privacy. These risks can be regulated only through proper and effective legislation. Most of the employees who handle the biometric equipment discard the ethics relating to it (Encyclopedia.jrank.org).
Biometrics is not something that we may become accustomed to or confronted with as a sci-fi futuristic system of technology. It is not at all new, for the basic principles of biometry was practiced thousands of years ago by the people of Egypt who lived on the banks of the river Nile, to identify the individuals through their physiological parameters like scars, complexion, eyes and height. Thereafter, the researchers who were engaged in developing criminology correlated the physical traits with the criminal tendencies of the individuals.
This resulted in the invention of several tools to measure the data, and later on settled with the development of fingerprint techniques as the international methodology for identity verification of persons, especially among the police forces and military. Subsequently, when microchips and electronics snatched the fascination of the world, military as well as commercial institutions went forth to integrate them in the biometric system, which flourished enough through the last decade to become the most coveted and feasible global industry involving billions of dollars turnover (Anderson, 2007) & (Jain, 2004).
Prior to the 1970s, the responsibility to protect network and all other information security was left on the shoulders of the national government, and the intelligence agencies were fully engaged in surveillance against hostile countries.
They constantly penetrated the traffic of the rival nations in order to sabotage their malicious moves to intrude into the national network. Since then and up to the year 2004, the information security was focused on to the companies than the governmental organizations as most of the firms in the private sector showed more inclination to the computer networks for transacting business and this dependency increased the chances of frauds and failures, which in turn paved the way for intensified research and development in the security sector to overcome the adverse situations.
The volume of internet crime was beyond all imagination and the hackers and criminals were on thrift with credit card thefts and unauthenticated access to electronic banking systems. Within no time hacking has achieved an unlawful business status and the market was flooded with hacking software and tools. The development of crime-ware has streamlined their methods of crime and there emerged a parallel criminal economy that challenged every social structure in most of the countries (Anderson, 2007).
. Thus, while Europe advanced, the need to implement effective and accurate information security was also increasing. The public are now more concerned about security so that both the private and public organizations shall be protected from all fraudulent activities. Since information security encompasses all the fields from law to psychology to mathematics, many of the biometric tools shall come out of economics (Anderson et al. 2007).The biometric security systems are conceived to have a legal output. For example Digital signatures are marketed with a claim that the courts will accept only the electronic documents. Most of the errors in the devices are invariably the results of mismanagement and blunders at the production stage. Therefore, the present situation calls for adoption of new cryptographic algorithm (Anderson, n.d.).
If seen from a new perspective biometric security and the privacy problems are inseparable and a valid and eternal solution is not feasible under current social set up. Since humans do recognize people accurately, biometrics is kept aside as an irrelevant issue (Jain et al., 2004).
Biometric can go beyond the realm of Homeland security and shine through the enterprise based network security, electronic banking, financial transaction sector, law enforcement, retail sales, health services, insurance, social services. New prospects are there in amusement parks, credit organizations, governmental networks, driving licenses, passports, schools and colleges etc. (About Biometrics, 2002). Biometric recognition technologies such as face, hand and voice are in common use and the cost effectiveness attracts the end users widely. Biometric solutions provide increased accountability and accuracy at a low cost, and therefore its position in the identity recognition is enviable (Podio & Dunn, n.d.).
The current scenario shows that the system of biometrics has graduated itself from the status of an information provider to the elite position of decision making facilitator. However, it confronts so many problems such as data thefts, malicious code attacks, service denial etc. Access control devices and database entries through computer logins facilitate solutions to the dilemma of password thefts and hacking (Obaidat & Sadoun, 1997).
The information security is now a business issue rather than technological issues. But thanks for the global networking; it is now a value creator and opportunity provider. The risks and carelessness can harm the results reputation and financial loss. To safeguard these, the data should be protected and confidentiality and integrity should be maintained, and thus it has become the key element of IT Governance. The stake holders are much concerned about the security because of data theft and hacking (Nagarajan, n.d.).
Digital identities are required for any transactions, and it is a necessity that the responses of the end users are given due consideration while applying them (Jones et al., 2007). Lately, user perceptions have influenced their own approach to biometric banking and this is because of the efficacy maintained by the system (Tassabehji & Kamala, 2010). As in the case of biometric banking, the mobile devices need increased security provisions to protect them from unauthorized access. The existing PINs must be replaced by biometric security system to safeguard the authentication after the initial entry point (Karatzouni et al., 2007).
The introduction of 3G technologies has facilitated several data centered services, and at present more than one million subscribers is switching over to it everyday (Best, 2006a). This situation poses serious security problems as there are more chances for unauthorized access to person and corporate information (Vance, 2006). A recent survey conducted in the UK revealed that mobile phone theft has shared 45% of the total thefts (Leyden, 2005).
The development of biometrics, overtaking the traditional applications, is based on financial motivation derived out of the alarming situation of credit card frauds that encumber a loss of $500 million and the ATM frauds snatched away $3 billions each year. Biometric systems can ward off such impostors as it is more individual centric than other systems of security. Though it was mainly designed for big companies, it can now accommodate small networks and applications that are stand-alone. Now one can get digital face identification software for $100 and a finger print scanner PC compatible with $150.
The increased availability of video conferencing and cheap price of multimedia based video capture equipment, the audio visual authentication and access modes are feasible as well as cost effective. The new generation of biometric devices will win over all other industrial products if careful evaluation of algorithms and protocols are performed with motivation (Green, 2001). With procurement of more contracts from government and large corporations, the biometric security systems can look forward to have the major share of the tempting market (Simpson, 2006).
Biometric authentication process is the basis of single sign on, workstation and network logging, security transactions, accessing remote resources, web security etc., and by executing effective personal authentication processes e-commerce as well as e-governance can be optimized. Other areas where biometric authentication is mainly used are electronic banking network, investment and financial transaction sector, trading, enforcement of law, defense, aviation and other transporting systems, health care and social service sectors and space research. The system will play an important role in the authentication of digital content and its related applications. By integrating other technologies, biometric security systems will exhibit its presence in every aspect of our daily lives (Biometrics, 2007).
Evaluating Biometric Technologies
During the one-on-one interviews when the questions relating to the evaluation of biometric technologies were put forward it was revealed that only six of the thirty-five participants were familiar with biometrics. This focuses on the necessity to redefine biometrics to make it more understandable and familiar to the public. According to Ashbourn (2000),
A biometric authentication system is essentially a pattern recognition system that establishes a person’s identity by comparing the binary code of a uniquely specific biological (physical) or behavioral characteristic (trait) to the binary code of a stored characteristic. This is accomplished by acquiring a live sample (the characteristic) from a petitioner (individual who is requesting access). The system then applies a complex and specialized algorithm to the live sample; it is then converted into a binary code. Once the live sample has been converted into a binary code, it is compared to the reference sample (previously stored binary code) to determine the petitioner’s access or not (Ashbourn, 2000).
Biometrics is the measurement of biological patterns to recognize the behavioural traits such as voice, eyes, fingerprints, and signature or keyboard dynamics. The biological characteristic and behavioural traits should tally with the individual’s unique biometric information acquired by the use of electronic devices (Ashbourn, 2000).
Contrasting Methods of Authentication
In order to recognize a person’s identity the system adopts three stages of processing. The first one is known as verification which confirms or rejects the claim of the person regarding the identity, that is to say, ‘Am I whom I claim to be?’ This verification is done by using any of the verification of signature, fingerprints, keyboard dynamics, iris, thermo graphics, and vein recognition. The next stage is identification that establishes the identity of the person, which can be put as ‘Who am I?’ Towards this the biometrics that are 100% sound in real life such as fingerprint, palm print, retina, iris scan etc. are leaned to as identifiers. Due to the complexity in the technology sometimes it may happen that the identification biometric may become vague and at other times it may surpass the boundaries. To overcome this dilemma, multimodal
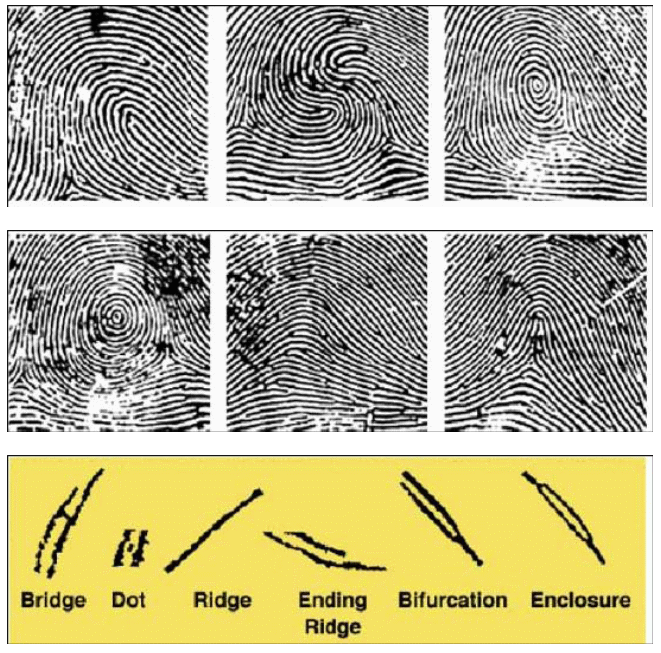
hybrid identification mode is sought to establish the identity of the person (Nanavati et al, 2002). The multi modal fusion schema will help defeating the limitations of finger print and face recognition systems by improving and integrating the multiple cues having different mathematical algorithms (International Journal of Biometrics, 2009). The figure -5 below depicts the fingerprint patterns & minutiae. Top row from left to right gives the picture of loop, double loop, and shell whorl of finger prints. The middle row shows the target whorl, tented arch and the bottom row provides the minutiae (Lawson, 2003).
In facial thermography, an infrared camera is used to capture the heat patterns generated by the face of the individual Figure-6. The aura is then converted to the data for comparing to the stored aura of the individual for authentication (Lawson, 2003).
At present there is no standardized ‘liveness’ test in the market as the manufactures of biometric devices keep these details confidential. If such details are made available it would enhance the accuracy and security of the biometrics. Ashbourn (2000) hold the view that “In a business-to-business scenario, the biometric authentication system can be linked to the business processes of a company to increase accountability of financial systems, vendors, and supplier transactions; the results can be extremely beneficial”. The biometric authentication techniques can be used in areas that demand physical access such as buildings, safe etc. (Nanavati et al., 2002).
Privacy and legal problems that face Biometrics applications
If the society needs to enjoy the full potential of the biometric system promulgation of proper laws is necessary to curb infringement of privacy. Various surveys and interviews held on the issues have revealed that the biometric technologies will face challenges if alternative authentication methods are not adopted to cope with the needs of variable group of people that require identification.
The opponents of the technologies demand improved designs and safeguard the well being and security of the humanity. For, the civilized people enjoy freedom and do appreciate new technologies only if it is compatible to their civil rights. Biometrics technology hence, has to attain more advancement in order to get the full support of the people. In spite of the adversities many governments, private companies and organizations look forward to biometric technologies as an effective method for the authentication of users who access to secured data. The major share of the biometrics market comprises of law enforcement, government, financial, healthcare, travel and immigration sectors.
The applicability of a biometric technology to a situation is determined by its characteristics, stability, acceptability and the level of accuracy together with the user friendly attributes and susceptibility rate against any attacks and interference. In the following zephyr analysis (Figure-7), the above factors are codified under two categories namely, technology and user criteria (Inman, 2000).
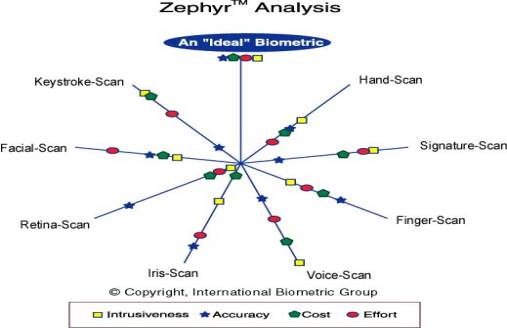
The Figure-7 above gives an idea about the strength and weakness of each technology with the eight primary ones around the border and the ranks of the technologies are depicted towards the centre.
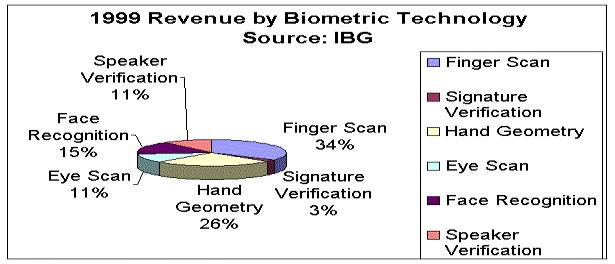
If the statement of International Biometric Group (IBG) can be taken into account the biometric market will experience tremendous progress within 2-3 years. The total revenue last year in lieu of the biometric products in the market was estimated to be $594 million in 2003. The chart (Figure-8) given below depicts the observations of IBG for the year 1999 taking it as the base (Inman, 2000).
Ever since the globalisation that originated between the 16th and 18th centuries there was a need to establish some sort of golden standard for the economic transactions. Likewise, the contemporary globalization which is based purely on electronic transactions for confirming identities, also needs some sort of golden standard and biometrics has now become that golden standard that decides the fate of the current global economic network, but the same golden standard if disregard ethics will cease to exist (Ethical and Social Implications of Biometric Identification Technology Workshop, 2005).
The Transportation Security Administration (TSA) of USA is optimistic that if someone hides something it could be disclosed through the system. But if someone hides something in the body cavity the TSA has to scratch their face. Immediately after the underwear bomber episode, the manufacturing company of the machines has revealed that if that person was subjected to the machines, there would be only remote chance of him caught in the machine. Bruce Schneier, who is an expert on computer security, feels that USA has dumping public money on security devices that makes security pretentions having no effect at all. There is no intelligence in the airports security leaving the passengers at their mercy placing their privacy at peril (Schneier, 2008).
Information security must ensure the privacy and integrity of the individual while allowing access to information. It is essential that a biometric security application should adhere to the principle of authentication without the involvement of identification. Authentication without the insistence of identification safeguard the privacy of the user and it can be provided by new technologies based on authentication combined with encryption. Biometrics is not at all secrets, states (Schneier, 1999). Since it is not possible to revoke any biometric information it should be given full protection against any malicious access to it and an act of compromising will jeopardize the interests of an individual (Fleming, 2010).
Conclusion and Recommendation
Conclusion
Biometrics recognition technology is used to identify a person from a large enrolled data of people by searching the database for the relevant characteristics belonging to that particular person. A user can enter an account with a proper user name or a smart card and with a finger touch or looking at a camera his authentication will be fulfilled. Such a system will bring out unique advantages. Loss of smart card, IDs, keys, password etc. can happen and biometric recognition can solve such problems. It is user friendly and cost effective, and guarantees fastness, accuracy, reliance etc.
Even though biometric technology heralds a revolution in the field of security and person recognition has become more convenient, the infringement of privacy and frauds are tarnishing its reliability. To combat the situation proper legislation is necessary. The market trend shows that the future of biometric technology, especially Iris recognition based devices, will become the most sought after security systems in the near future. The manufacturers are trying to make the devices more users friendly and cost effective. By the end of 2010 the industry will attain a turn over of 5,749.2 million USD, which is four times the turn over achieved in 2005.
In generic, there are concerns standing in the matter of adapting new technologies. The present study reveals that most people are reluctant to undergo biometrics identification process as if affects the privacy and safety of the individuals. They do not want to jeopardize the benefits of the system but they want a solution to the challenges to the freedom and privacy of their individuality.
It is evident that the people hold the opinion that the government must come forward to promulgate new laws to safeguard the privacies of the users. The manufacturers of the biometric devices should see that the liveness test details should be provided to the personnel who handle the equipment so that more accuracy will be bestowed to these devices. It is quite explicit that the future of biometric industry is progressive and prosperous which in turn will call for new methods to safeguard the interest of the public more than ever, considering the present annual growth rate of 35 percent in biometric sector.
From the literature and other data the researcher has found that among the various biometrics applied iris identification is the most effective system. It is less harmful than other systems, and as such it would be better if more and more iris scanning system devices are used to carry out the identification and authentication process. Whatever it is, the inherent ethical problem that is seen in these technologies are much severe as any technology that infringes the privacy and freedom of individual will face setbacks, and therefore, stringent measures should be adopted to check such infringements.
The study conducted through surveys and interviews pin point this aspect as many of the respondents have expressed their concern over this issue though they admit openly that there are benefits and convenience offered by the system. Additionally, the replies of the respondents have enabled the researcher to understand that though the biometrics sector is making tremendous progress the integration of the system facilities still run short of adequate security provisions.
Ultimately, this dissertation achieved the goals and carried enough potential in evaluating the biometric system at the root level and also assessed the market trend to get insights into the benefits of the various sections of the technologies that are ranging from finger prints to iris scan devices. The world today moves towards convenience and the customer’s mind is tuned to this basic instinct. Hence, biometrics while integrating the consumer interests into the business must see that the users should not be allowed to feel dread subsequent to the use of the techniques. No system will thrive if the privacy and freedom of an individual is put at peril.
Therefore, without underestimating the prosperous future of biometrics it is recommended that there is an overall necessity to safeguard the privacy of the individual at any cost without harming the advancement of biometric technologies (Robers & Patel, n.d.)
Recommendations
The security potential of the biometric systems needs more enhancement and the manufactures should put in maximum effort to make the devices user friendly and cost effective. Stringent measures should be adopted to safeguard the privacy of the individual. The ethical standard exhibited by the employees who handle the equipments need be trained and motivated so that they would stick to the ethics. If required stringent legislation should be formulated to overcome the privacy infringement so that they must know that privacy of a person is the most important feature of an individual and societal life.
The present research has ended in identifying different areas where continued researches are needed, especially in the field of iris biometrics. The drawbacks in the performance of the system should be removed entirely for the satisfaction of the users. Further analysis should be undertaken to deal with the interaction during the process of scanning and enrollment. There should be sincere steps on the part of the manufacturers to redesign their iris scanning devises to improve on the failures inherent.
New researches must be launched in all industrial sectors that are related to biometrics so as to streamline the training process and development of new technologies for enhancing the convenience of the users. The sensitive locations such as airports and other governmental institutions must install iris scanning security systems as it is found to be more effective than other systems. It is also recommended that considering the necessity to deal with variable user groups, multi modal hybrid identification system that are developed through integrating or combining the systems of iris, retina, face, fingerprints etc. should be made use of to combat the challenges of vague identification process.
Since iris scanning is resulted from the visual identification that concedes to digital identification, there is some sort of inconsistencies and concerns on the longevity of the system. Therefore, steps should be undertaken to redesign the technology to overcome the image capturing barriers (Stevenson, 2006)
If the applied biometric identification technology is managed well so as to reduce the cost of administration and the frauds, productivity will increase and the higher security provision will compensate the cost of initial installation of the biometric technology. While implementing the system the company managers should weigh the elements that are quickly identifiable as such elements are generally used heavily in the process.
The managers also should study the environment where the equipments are deployed so that maximum out put will be generated in terms of system integration, biometric trait, front and back end processing devices, security levels, user expertise, access, scalability and so on. A biometric solution that functions with minimum user effort would be very convenient for the user and the purchaser (Ashbourn, 2000). Implementing alternative methods for identification is a good practice as it will make the biometric system accepted by all people and such systems will reduce the error levels during the authentication process and enrollment. Additionally, proper auditing on a continual basis will enhance the functioning parameters of the biometric systems (Lawson, 2003).
References
About Biometrics, 2002. National Institute of Standards and Technology. Web.
Anderson, K., 2002. BBC NEWS, Eye scans unlock the future. Web.
Anderson, R.J., Bohme, R., Clayton, R. & Moore, T., 2007. Security Economics and European Policy. Web.
Anderson, R. J., n.d. Liability and Computer Security: Nine Principles. Cambridge University Computer Laboratory. Web.
Arnese, P., 2000. The mark of the beast. The Xcellent Files, Apocalypsesoon. Web.
Arvacheh, E. M., 2006. A Study of Segmentation and Normalization For Iris Recognition Systems, Waterloo, Canada.
Ashbourn, J., 2002. Introduction to biometrics, In: BANTAM User Guide: Biometric and Token Technology Application Modeling Language. London: Springer. p11-17.
Ashbourn, J., 2000. Biometrics: advanced identity verification: the complete guide. London: Springer. p45-66.
Best, J., 2006a. 3G reaches 50 million users worldwide. CNET. Web.
Biometrics, 2007. Web.
Bowyer, K.W., 2009. Iris Biometrics Research, Biometric technology for human identification. Web.
Ceyhan, A., 2008. Surveillance Studies Network. Technologization of Security: Management of Uncertainty and Risk in the Age of Biometrics 5(2): 102-12. Web.
Chu, V. & Rajendran, G., 2009. Use of Biometrics, TechCast LLC. Web.
Clarke, N.L., Furnell, S.M, Rodwell, P.M. & Reynolds, P.L., 2002. Acceptance of Subscriber Authentication Method for Mobile Telephony Devices. Computers & Security, 21, 3, pp. 220-228.
Cronje, J., 2005. Research Methods Online. Web.
Dale, M. P., Munde, K.H., Bodade, R.M. & Kapoor, N., 2006. Management of Innovation and Technology. IEEE International Conference, Volume: 2 P: 960 – 964, Singapore, China. Web.
Davison, R.M. & Vogel, D.R., 2006. Group Support Systems in Hong Kong: An Action Research Project, in Galliers, R.D., Markus, M.J. and Newell, S. Exploring Information Systems Research Approaches: Readings and Reflections, Routledge, 33-46.
Daymon, C., 2002. Qualitative Research Methods in Public Relations and Marketing Communications, Routledge.
Elizabeth, M., 2005. Biometrics for the masses. Newsfactor Magazine Online. Web.
Encyclopedia.jrank. n.d. Types of Biometric Devices. Web.
Encyclopedia.jrank. Web.
Eric, B., 2000. Everything You Need To Know About Biometrics. Identix Corporation. Web.
Ethical and Social Implications of Biometric Identification Technology Workshop, 2005 Towards an International Approach. European Commission – Science and Society, Brussels. Web.
European Commission, 2005. Ethical and Social Implications of Biometric Identification Technology Workshop.Towards an International Approach. European Commission – Science and Society, Brussels. Web.
Evaluating the Capability of Biometric Technology, 2009. Web.
Fleming, S.T., 2010. Biometrics Security Net Industries and its Licensors, University of Otago, New Zealand.
Fons, F. & Fons, M., 2010. Making biometrics the killer app of FPGA dynamic partial reconfiguration. Web.
Frucci, A., 2010. Is It This Easy to Pull Straight Nude Pics From Airport Scanners? [NSFW]. Gizmodo. Web.
GlobalSecurity. 2009. Homeland Security. Web.
Greene, T., 2001. Biometric Security – Practical and Affordable! Web.
Habermas, J., 1972. Knowledge and Human Interests. Heinemann, London.
Hobbing, P. & Koslowski, R., 2009. A Comparison of Border Security Systems in the EU and in the US, Ad hoc Briefing Paper, Justice and Home Affairs Section of the Centre for European Policy Studies (CEPS). Web.
Holmes, C. & Walmsley, S., 2005, Biometric Security in Today’s Market: An introduction to fingerprint, retinal, and iris scanning technologies, COP4910 – Frontiers in Information Technology. Web.
Homeland Security, 2009. GlobalSecurity. Web.
Homeland Security, 2009a. Web.
Home office Identity and passport service, 2010. New passport design unveiled. Web.
Hudson, K., 2010. Use of Iris Recognition technology in the Biometric ATM. Web.
Inman, H. M., 2000. The Emergence of Biometrics. Indiana State University, MIS 476. Web.
International Journal of Biometrics, 2009. Optel Ultasonic Technology/Fingerprint recognition. Web.
Implementing Recommendations of the 9/11 Commission Act of 2007, Public Law 109- 367.
Jain, A.K., Pankanti,S., Prabhakar, S., Hong, L., Ross, A. & Wayman, J. L., 2004. Biometrics: A Grand Challenge. Proceedings of International Conference on Pattern Recognition, Michigan State University, Cambridge, UK 0-7695-2128-2/04 IEEE. Web.
Jarvinen, E.M. & Hiltunen, J., 1999. Home security-children’s innovations in action. Mottier, I. & M. J. de Vries (Eds.), Impacts of Technology Education. Proceedings of PATT-9 Conference in Indianapolis. Eindhoven: PATT- Foundation.
Johnson, J., 2010. One Hundred Naked Citizens: One Hundred Leaked Body Scans. Gizmodo Investigation. Web.
Jones, L. A., Anton, A.I. & Earp, J. B., 2007. Towards understanding user perceptions of authentication technologies. Proceedings of the 2007 ACM workshop on Privacy in electronic society. ACM Digital Library. Web.
Karatzouni, S., Clarke, N.L. & Furnell, S.M., 2007. Device- versus Network-Centric Authentication Paradigms for Mobile Devices. Proceedings of 5th Australian Information Security Management Conference. Edith Cowan University Research Online, Perth Western Australia. Web.
Kevin, M., 2003. High tech enhances old con. The Cincinnati Post.
Knox, R., 2010. Scientists Question Safety Of New Airport Scanners. Web.
Lawson,W. J., 2003. Enhancing assistive technologies: Through the theoretical adaptation of biometric technologies to people of variable abilities. Web.
Leyden, J., 2005. Londoners Top World in Leaving Laptops in Taxis. The Register. Web.
Liu, Y., 2008. Identifying Legal Concerns in the Biometric Context. Journal of International Commercial Law and Technology Vol. 3, Issue1.
Manchester Airport, 2010. Body scanners introduced at Manchester airport. Web.
Mercury News, 2003. Editorial. Web.
Meyers, D., R. Koslowski, R. & Ginsburg, S., 2007. Room for progress. Reinventing Euro-atlantic Borders for a New Strategic Environment. MPI. Web.
Miller, G., 1998. Handbook of Research Methods in Public Administration. Marcel Dekker Incorporated. New York, NY, USA.
Nagarajan, N., n.d. Information Security Governance: What, How and Why of IS Security. Web.
Nanavati, S., Thieme, M. & Nanavati, R., 2002. Biometrics: Identity Verification in a Networked World. John Wiley & Sons, New York, USA.
Neil, R., 1999. Biometric Basics. ZDNet PC Magazine. Web.
New passport design unveiled, 2010. Home office Identity and passport service. Web.
Obaidat, M.S., Sadoun, B., 1997. Verification of computer users using keystroke dynamics. IEEE Transactions on Systems, Man and Cybernetics 27 (1997) 261269.
Paul, F., 2007. Europäische IT-GroBsysteme: SISII und VIS, 10. Europäischer Polizeikongress. Web.
Pavone, V., 2010. Public assessment of new surveillance-oriented security technologies: beyond the trade-off between privacy and security. Public Understanding of Science. SAGE Publications, Washington DC. Web.
Patrick, A.S., n.d. Usability and Acceptability of Biometric Security Systems. Information Security Group: Institute for Information Technology, National Research Council, IST-044-RWS-007. Web.
Podio, F. L. & Jeffrey S. Dunn, J. S., n.d. Biometric Authentication Technology: From the Movies to Your Desktop. National Institute of Standards and Technology. Web.
Pointsec, 2005. IT professionals turn blind eye to mobile security as mobile survey reveals sloppy handheld Habits. Web.
Questbiometrics.com, n.d. Types of biometric devices. Web.
Research Methodology, 2010. Dissertation India. Web.
Robers, J. & Patel, S., n.d. Biometrics: Does Convenience Outweigh Privacy?. Web.
Rosenzweig, P., 2004. Biometric Technologies: Security, Legal, and Policy Implications. Legal Memorandum, the Heritage Foundation, No.12.
Schneier, B., 2008. Schneier on Security. Wiley, John & Sons, Inc. Web.
Sim, P., 2010. How the War on Terror has Affected British Policy-Making. Counter- Terrorism Legislation in the UK. Web.
Simpson, I., 2006. BIOMETRICS: ISSUES AND APPLICATIONS. Electronics and Computer Science, University of Southampton. Web.
Sirvan, O., Karlik, B. & Ugur, A., 2005. An Efficient Iris Recognition for Security Purposes. GVIP 05 Conference, CICC, Cairo, Egypt. Web.
Stefan Brobeck, S. & Folkman, T., 2005. Biometrics- Attitudes and factors influencing a breakthrough in Sweden. Master’s Thesis in Informatics. Web.
Stevenson, B. R., 2006. Analysis of near infrared phase effects on biometric iris data. Web.
STORRE, 2002-2006. Stirling Online Research Repository (STORRE), Chapter 4: Theoretical Framework (online), University of Stirling. Web.
Tassabehji, R. & Kamala, M.A., 2009. Improving E-Banking Security with Biometrics: Modelling User Attitudes and Acceptance. Mobility and Security (NTMS) 3rd International Conference, IEEEXplore Digital Library. Web.
TechCast LLC, 2009. Use of Biometrics. Techcast. Web.
The Solutions: Cost-Effectiveness, n.d. The Problems: Corporate Security, The Solutions: Cost Effectiveness. Web.
The EU and the Fight against Terrorism, 2006. Euromove, European Movement, London. Web.
Towards an International Approach, European Commission, Brussels. Web.
UK Passport Service page. Web.
Vance, A., 2006. Lost Ernst & Young laptop exposes IBM staff. The Register. Web.
Wildes, R., 1997. Iris Recognition: an Emerging Biometric Technology. Proceeding of the IEEE, Vol. 85, No. 9. Web.
Yin, R., 1994. Case study research: Design and methods (2nd ed.). Beverly Hills, CA: Sage Publishing.
Zalman, A., n.d. History of Biometrics from fingerprints to facial recognition software. Web.
Zephyr Analysis. International Biometric Group. Web.