Introduction
The first chapter of this dissertation will consider the justification of the study, formulate research questions and discuss the objectives and background of the problem, for instance, controversial issues, different type of violation of the copyright act, loopholes of the entire system, liabilities of the internet service providers to protect infringement of law by the subscribers, and so on. The next part of this paper will focus on the theoretical framework to describe internet service providers, need for ISPs liability, argument for and against imposing liability on ISPs for copyright violation by subscribers, limitations of the legal system, technical knowledge to detect a breach, International treaties like The Rome Convention, WIPO Copyright Treaty and Convention on Cyber Crime 2001. However, this chapter will also discuss the function of the ISPs in the limitation of liability, the exercise of freedom of expression, statutes relating to intermediaries, international disagreement over the issue, and so on.
Background of the problem
Matthew notes that the era of technology has introduced many challenges and unique problems in the legal framework in the United Kingdom, such as, adapting intellectual property in order to meet the challenges of international IT networks, introducing new laws to strengthen copyright act, sharing programs (particularly peer-to-peer file-sharing) and the liability on the intermediaries1. On the other hand, Popoola states that copyright protection seriously hampered because of technological changes and the lawmakers need to concentrate on the policies to impose liability on the ISPs particularly freedom of speech became the key concern in some extent2. At the same time, Song states that many issues have covered in law like trademark along with trade secrets, unfair competition, privacy, defamation, and copyright law; however, it is difficult to impose charges on the ISPs for the infringement of copyright acts, as it needs to investigate the extent infringement to which they are liable3. However, Lichtman states that it would not be rational to impose liability on the ISPs for each terrible activity of the subscribers and failing to warn them; in addition, it is not cost effective to the ISPs to monitor the performance of the users4.
Rationale for the Research
Many research articles have already addressed the liability of Internet Service Provider and compare among different countries in order to assess the actual position to face the challenges of adverse impact of technology and find out proper solution by changing or reforming legal framework. In addition, some other concentrated on the specific issues, for example, Olumuyiwa Oluwole deals with the protection of sound recordings in the DP2P file sharing among three countries and he identifies that ISPs have the capability to differentiate the works and protect illegal sharing of sound recordings, but they have induced the users and failed to comply existing regulation. However, the researchers further state that ISPs are liable for many consequences, but it is difficult to assess direct and indirect liability; as a result, treaties, regulation and laws of different countries based on some common features. The liability of ISPs has become a significant concern for the lawmakers of all nations and the policy makers eager to identify the loopholes and find out proper solutions considering global position; in this context, present research will compare between liability of the ISPs in the UK and India.
Objectives and Research Question
In the modern world, the Internet Service Providers are mostly immune from legal responsibility of safeguarding the users’ security and privacy; rather, the ISPs are stimulating the generation and circulation of worms, viruses, and malicious coding while this type of immunities are huskily incompatible with the prevailing tort law principles and hardly complex to secure on the policy ground. Thus, it is essential to investigate whether the liability of the ISPs has turned into negligence, or the statute and common law has responded timely to integrate the extents of ISPs liability that has been developed with gradual progression of the ISP industry and quick raising ICT integration among the private and public bodies. The aim of this research is to investigate recent trend of the court trials and legislative bodies to provide further indemnities to the ISPs that are continuously increasing security hazards; ISPs have the opportunity to assist to identify the hackers and burglars who instigate malicious code at the first instance, but there is a policy trend to provide greater immunity to them.
The main objectives of this research are to scrutinise the duties of care of the ISPs organised with multiparty complex value chain among the regional and international arena focusing on the facts and figure of the United Kingdom and India by providing some insight into the forms of duty of care of ISPs in both countries. This research would also enlighten on the role of policymakers, legislative bodies, academia, and governments of the two countries in order to identify the exact stands of ISPs in context of regulations accomplishment, degree of privacy, security level, and ethical standards by investigating with the following research questions
- To what extent the ISPs of India and the UK are providing their duty of care, what are the forms their liability;
- Harmonisation of regulations governing ISP liability: Institutions such as United Nations, WIPO, etc., to evolve with uniform set of regulations governing ISP liability
- What is the role of national government to imposing liability on the ISPs through legislative reformation?
- What are the outcomes and current stage of liability of ISPs that the countries are experiencing?
This study has indicated the Internet service providers (ISPs) who are active parties in the market to provide online services, offer network assess, operator of hosting and data storage facilities to the end-users has termed as ISPs; these parties are active in the market to sell their ICT product and services. The duties of care and the liability of ISPs are strongly accorded with the primary relationship among the government and Internet service providers and end user where the ISP and end-user are seller and buyer respectively, and the role if government is as a regulator. Consequently, the above research questions would be restructured into several sub- questions in order to represent a well-organised and easygoing research outcome.
Scope of the Study
This research area has a number of scopes to point out, such as
- The word limit or size of the dissertation was sufficient to analyze the research field because the topic “liability of Internet Service Provider: A comparative study between UK and India” is one of the prime important issues in the era of technology and globalization. Therefore, it is significant to discuss most of the aspects broadly to contribute for this sector;
- In addition, this dissertation will give the opportunity to the new researchers to get idea about the liability of the ISPs for the cyber crime occurred by the third parties;
- There are many journal articles, books, legislation and other secondary sources to cover all the aspects related with liability of the ISPs;
- On the other hand, this paper based on the secondary data, which gives the opportunity to observe the articles of different writers;
- At the same time, the dissertation will help the law makers to concentrate on some issues those have not been addressed yet;
Imitation of the Study
- The time limit to complete the research on ISPs liability was comparatively short;
- However, there are many secondary data sources on the liability ISPs in aspect of the UK and India, but no researcher has broadly compared the ISPs liability for these two countries. In this circumstance, it was hard for the researcher of this dissertation to compare the liability of the ISPs in aspect of the UK and India;
- This paper will not collect primary data and not concentrate on the view of the respondents due to considering technical issues;
- It is difficult to replicate due to use of case study approach;
- Researcher further states that subjective view of the writer may strongly influence the case study
Literature Review
Theoretical framework of the Internet Service Provider (ISP)
In the modern world, the Internet Service providers are the commercial entries generating profit by selling the Internet connectivity to the individuals and business organisations in different categories like dial up, broadband, and leased line depending on the speed of the connection and uses time, or quantity of data transfer, whatever the mode of service all are defined as ISPs. To get access to the Internet every user need to have a local ISP with a connection medium that facilitate the channel of information to receive and send from the user’s computer, through ware or wireless connectivity the ISPs offer different types of services to transmit data through the Internet including hosting, design and software support for different utilities. The US DMCA– 1998 pointed out that ‘service provider’ are the entities who operates and offers online digital communication facilities to the users for data transmission and routing among points selected by the user without any alteration to the contents while major concern is to network access by the user although they have technical opportunities to check the user contents. Under the Information Technology Act- 2000 of UK, the ISPs are the individuals or business entries that provide ‘information society service’ pointed to the all Information Technology integrated services through ‘electronic equipment’ without any obligation of border barrier to receive, send, compression and storage of digital contents in accordance with the request of the user. At the same time, it has also defined ISPs as the “network service provider” or intermediaries who handle the Information Technology enabled communication tools as a third party in order to facilitate the users whether they are professional or non-professional entry, but provide services to the user end in respect to the user defied way.
Necessity of the ISPs Liability
In the real life scenario, any wrong action would generate harm for someone and simultaneously may deliver positive outcomes for others, but the performer is always liable for his wrongdoing, from the viewpoint it is necessary to have specific liability for the ISPs for their mishaps committed over the Internet. Under the Information Technology enabled communication, there are enough possibilities to occur interference of the third parties where ISPs are the major third parties who can easily turn out such immoral action over the Internet with or without deliberate or accidental involvement hackers although they have facilities to prevent illegal communication. The basic idea of technology strongly argued that the happening of any wrong over the Internet is quite impossible to take place without the intended or involuntary participation of the ISP who provided the Internet connectivity; such awareness has generated the extensive debate regarding the liability of the ISPs for copyright violation occurred by the third parties.
The copyright holders strongly argued to impose liability on the ISPs for copyright violation with a the provision to impose penalty or to urge for compensation for any kind of reproduction or unauthorised commercial use of the digital commodities communicated or stored to their server, at the same time ISPs are passionately campaigning to such obligation of them5.
Direct Liability of the ISPs
Yen notes that the courts could seize an ISP accountable for its users for the performance that ultimately points to directly breach of IPR by the ISP that provides basic Internet service to the victim user while the outcome gives reasonable impression that the ISP intentionally or unintentionally reproduced or distributed copyrighted material without concern of the rights holder6. Tong reports that the users are capable to upload their digital commodities to their own websites by instructing the server of the ISP; while computer of ISP remains a copy of transmitted commodity, in each time, the user views this webpage and posts another copy to the desired beneficiary through Internet while such copying are not authorised by copyrights holder7. All these functions are the equitable evidence of infringing the Intellectual property right; there are huge cases where the court charged for violation of copyrights for instance Fox Film Corporation and others v BT is the landmark case where the evidence of imposing direct liability on the ISP has implicated. Bailli reports that it was established by the English court that the BT as an Internet Service Provider of Fox Film Corporation and other five studios has seriously occurred infringement of their copyrighted films the court ordered BT to put a stopple and seriously restrict its subscribers to access to the site with application of ‘Cleanfeed’ integrated software8.
In the mentioned case law and the observations identified that the properly disgraced by automatic copying, distribution as well as storage digital version of the film infringed the exclusive copyright rights of claimants, the Intention of BT to infringe is not necessary condition to prove the copyright infringement, unintentional event or lack of knowledge is not a defence. In the case ‘Fox Film Corporation and others v BT’, the verdict of the English court established that in general explanation the ISPs are directly liable for copyright infringement, but the depth analysis and more interpretation of law delivers problematic outcomes while the ISPs urged to take into account of intent and knowledge as an element of copyrights claim.
Research Design
Three main functions of legal research are exploration of a legal problem, critical description of facts, legislation, and explanation or interpretation of legal issues and concepts; however, this chapter aims organizes in order to describe the process by which the entire paper will formulate considering the topic “liability of internet service provider: A comparative study between the UK and India”. Kothari notes that methodology is a significant way to gain reliable and valid knowledge and to explore the relationship between theory and practice9; however, the researcher of this study selects case study approach since there is no exact rule about research design; though, it depends on the knowledge and training of the researcher and the nature of research questions.
Rationale to Use Case Study Method
- Kohn argues that it is useful method to clarify a complex phenomenon10;
- McLeod states that it gives insight for further research11;
- Yin states that it helps the researchers to coordinate the facts with theoretical framework because the findings and discussion chapter highlight the position of ISPs liability in terms of both hypothetical and practical viewpoint12;
- Tellis expresses that it is useful method for in-depth investigations13;
- Kohn argues that it should use this approach while the research based on description of different events those influence different parties14
Primary Sources
Tjalsma & Rombouts note that the primary sources of law are those authoritative records or authorized statements of law made by the law making bodies or governmental institutes 15. In general, Tjalsma & Rombouts state that primary data are mainly raw data those not published in articles or books; thus, it should require processing such data for using in the dissertation or research paper16. Cases, statutes, regulations, or decisions of administrative bodies and so on have treated as primary data for the legal research; moreover, some documents including the written opinions of courts, constitutions, legislation, rules of the court; the rules, regulations and opinions of administrative agencies are also be treated as primary data; however, There are following types of primary sources –
- Vibhute & Aynalem state that primary sources are the legally binding rule or the official pronouncement and pay special attention to the legal authority of the rules17;
- International soft and hard law instruments: While soft law refers to Declarations, Resolutions, Agenda, Programme of Actions and other documents, which are non-binding in nature; on the other hand, hard law implies conventions, treaties, protocols, Agreements, which have binding forces, for example, The Rome Convention, WIPO Copyright Treaty and Convention on Cyber Crime 2001;
- Statute or Legislation made by Parliament: A statute, sometimes referred to as legislation, is a positive statement of legal rules enacted by a legislature, for instance, the UK Digital Economy Act 2010, Copyright, Designs and Patents Act 1988 (UK), Trade Marks Act 1994 (UK); Indian Information Technology Act 2000 and 2008, Trade Marks Act 1994, and Copyright Amendment Act 2010 etc.
- The rules, regulations, orders and by laws of those to whom parliament has delegated authority; however, judicial decisions or case law assists the legal researcher in interpreting the statute;
- Ratio decidendi and obiter dictum are also treated as primary sources18
Secondary Research
In order to discuss the liability of internet service providers by comparing the position between the UK and India, the researcher of this study was concentrated on a number of secondary sources, for instance –
- Books: This dissertation will focus on many books of famous writers, for instance, Internet Law and Regulation, Information Technology Law, Digital Media: Contracts, Rights and Licensing, Sponsored Links and Trademark Infringement, Research Methodology: Methods and Techniques, Case Study Research: Design and Methods, Fundamentals of Business Law: Summarized Cases and so on;
- Online Reports: Holding Internet Service Providers Accountable, Liability of Network Service Providers, Liability of Internet Providers for Copyright infringement-legal Dimensions of Cyberspace, ISP liability – UK in Computer Law & Security Report, Copyright: Internet Service Provider Rights and Responsibilities, Copyright Protection – Current Indian & International Perspective, A rear view of the YouTube case, and many others;
- Journal Articles: This study will use many articles from renowned journal, such as, Journal of International Commercial Law and Technology, The Journal of Information, Law and Technology (JILT), Journal of Intellectual Property Rights, Emerald Group Publishing Limited, The Georgetown Law Journal, Legal Information Service, Harvard Journal of Law & Technology, etc. However, the figure no 1 of appendix illustrates the secondary data collection method broadly-
Analysis and Interpretation of Data
Analysis and Interpretation of Data is next stage after gathering both primary and secondary data; however, interpretation is search for the broader meaning of research findings and it refers to the generalization, and results; on the other hand, analysis of data is to be made with reference to the purpose of the study. In this stuffy, data should be analyzed in the light of research questions and as the research approach based on case study, it would be descriptive in nature to analyze the liability of the Internet Service Providers: A comparative study between the UK and India.
Findings and Discussion
Harmonisation of Regulations Governing ISP liability
Farano argued that a continuous debate has been flourishing with the definition of the ‘Internet Service Providers’ pointing to the question whether the Internet Intermediaries would be considered as pure ISP or traced as UGC platform who would be legally responsible for third party content hosting at their server or website and elevated the most vigorous debates with IP address19. Simultaneously, the entrepreneurs of the ISP business have been suffering from huge losses from their online operation and such entrepreneurs are arguing that ISPs along with the UGC platforms would be liable for the plagiarized contents presented on their server or website, as they are familiar with similar plagiarised contents and keep their effort to be liability free. Fiscor notes that they have already claimed that penalising them for plagiarised contents would be considered as a hindrance to the free flow of information and undermine the right and freedom of the ISPs, with a huge investment, they just introduced to publicise the Information Technology both in the public and in private sector with emergence to the digital economy20.
The policymakers and legislators of the EU and the USA have engaged their hard efforts to resolve the crisis among the right owners and the internet intermediaries through endorsing few fundamentally reliable regulations with objectives to encouragement of the expansion strong digital economy without hampering the security of IP rights with first attempt to regulate WIPO Copyright treaty in 1996. It was the initial attempt to facilitate the Online Service Providers (OSPs) to provide electronic communication opportunities to the third parties without keeping direct liability on the account of Internet Service Providers, the European e-commerce directives and the DMCA uphold the similar sense to limit the liability of the OSPs handling the third party content. Thus, Kalisch notes that it was emergence to harmonising the interpretation of the DMCA and European e-commerce Directive while the EU and US Courts have interpreted the comparable doorstep requirements with diverse approach pointing to the inconsistent outcomes for analogous business within their own existing law to qualifying the Internet service providers for not to direct liable for copy rights21. To harmonising the regulations governing ISP liability, it is essential to remove the conceptual gaps through the respective interpretations of the existing law and regulations guided as follows
- To conceptualise the eligibility for hosting the safe harbour that provides service would be technically eligible to ensure secured hosting harbours whether it may be a clean hosting providers or even UGC platform;
- The minimum standard of know how and concerned degree of knowledge including awareness regarding the plagiarised contents should generate the response of the Internet Service Provider by means of expressed notification commencing the right holder where exact information would be obtainable from any other information resources regarding the infringing activity;
- Lloyd notes that it is essential to provide standard form of adequate response by the ISPs taking into account of the reaction at the user level that what kinds of reaction they are expecting from the service provider in context of complain logged regarding the infringing activity; engaging different monitoring tools could assist to keep away from the publication of plagiarised contents22;
- Quick response to deliver the reaction is an obligatory condition for the ISPs; it is a considerable issue that how long time do the service provider takes to remove complained contents;
- Another vital consideration is that to what extents the service providers has control over the infringing activity, are they capable to prevent unauthorised interference of the infringing users by monitoring the displayed contents and keep a stopple to their further logon;
- Assessing the standards of financial benefits is another disposition to take into account to justify the qualification of the ISPs and impose liability upon them, if they are directly involved to get financial benefits infringing activities and repeatedly do so, they must be charged with entire liabilities
Issues pointed out on above are the general presumption to harmonising the existing EU and US law, further initiatives to harmonise the systems may require to having few small legal adjustments for instance keeping provision for simplified and coordinated notice and keeping those records in the system could relief ISPs from infringe copyright.
Development of Global Convention of UN for ISP Liability
Polanski pointed out that the General Assembly of the United Nations has successfully implicated the convention in 2005 to ratify the treaty concerned with electronic contracting among users, business communities, and governments particularly designed for global B2B model of electronic commerce while other international treaties like European convention for Cybercrime has intended to enforcing law to protect online crimes23. Moreover, the convention has provided new dimension to the law of contracts for sales of goods covered by the provision of Vienna Convention – 1980 that integrated faxes and telegrams, it included the technological development of the Information Technology as vital resource for communication for business contract and transaction upon a legal base by resolving regulatory gap. The convention has also integrated the core contents of UNCITRAL particularly the provisions of CISG along with the prevailing law of electronic commerce while the previous two principles of transaction both paper-based and electronic have adopted similarly importance without any favour or disfavour to the technologies with the aim to ascertain potential rules on contract establishment in the business. The Convention consists of twenty five articles with four chapters while first two chapters presented the right application of the instrument with common provisions together with definitions as well as terms of use, the next two chapters explored the application of electronic communications in business contracts including proviso of legal gratitude, requirements to organise offers and its time and place.
UNCTAD adds that the most of the businesses connect to the Internet through different type of ISP with different subscriptions packages; there are huge liabilities of the Internet Service Providers to ensure safety of the business and all users by ensuring the compliance with the International contracts and local and international legislation for ecommerce, e-transactions, information security and consumer protection24.
ISPs are strongly liable to ensure their compliance with data protection acts, intellectual property rights, privacy policy, dispute resolution among the users as well as e-contracting including the law on electronic signatures some countries have already established their own legislation and others have ratified the European Directive on ecommerce or US e-commerce law in to their own legislation25. The main purpose of the UN Convention is to identify a realistic solution for the dilemmas of using electronic communication for international contracts to establish by the way of concerned negotiation and performance by removing the legal obstacles to generate electronic commerce those were implemented before the Internet era and pointed out under the instruments of UNCITRAL in 2004. The UN convention on electronic contracting has set out the provision to provide complete recognition for electronic for electronic contracts as required to integrate core values of previous conventions just to accommodate the companies dealing with online sale of goods is accordance with the older rules of Vienna Convention in 1980. Through this convention, the global e-commerce has gained a legal reorganisation with a dynamic strategy easier than older conventions to establish offer and acceptance and to commence online transactions with widen scope to avoid traditional hard copies of contract complying with exceptionally narrow legal framework where security issues are raising day by day26.
The Berne Convention
Sterling notes that the Berne Convention was the most primitive statutory framework to safeguard the literary and artistic works that had introduced in 1886 and gone through several amendments until March 1989 while the USA first entered into this convention, the mainstream spirit of it was to globalise the copyright protection by integrating signatory countries to uphold copyright protection for the other signatories27. WIPO notes that the Convention also kept provision each signatory country to allow similar rights for the foreign authors that awarded to the native biographers with a minimum period of copyright protection, it resulted the equal treatment for all authors of the member states to the other Berne qualifying countries without any hazards by removing additional paper work or formalities28. It also urged for removal of most formalities for copyright protection and after a certain period withdrawal of copyrights of that work, although USA was away from this convention, but the controversial norms of US local legislation made the country bound to join to the Berne Convention by negotiating with the World Intellectual Property Organization like all other signatory nations. The most remarkable point of the convention is the ‘automatic protection of copyright’, under the provision of the convention there is no requirement of huge formalities or precondition to providing legal notice for protection, but essential to using the symbol © as a mandatory terms where the independent existence of the protection would be afforded by the works originating countries. In this connection, the domestic law would administer the protection and the member country guarantee to enact laws to implicating the objectives of the convention although it is not a self-executing treaty while the Article 2 of the Convention clearly mentioned the categories of works to be protected with this multilateral treaty.
The Rome Convention
Popoola added that in 1964 the Rome Convention has started the journey to protect intellectual property rights by pursuing the safeguard of the performers, producers of phonograms as well as broadcasting companies that generated a harmonised system to protect rights innovators and individual contributors; it secured the innovators and the contributors from any unauthorised commercial use. Under the article – 10 of the Rome Convention it has clearly mentioned that strictly prohibited the reproduction of sound recordings without prior concern of the right holder, the right holder is authorised to allow anyone for reproduction, but there is no indication regarding the exclusive authorisation for reproduction of the sound recordings. At the same time, Williams, Calow & Higham notes that the Article – 12 of the Rome Convention clearly mentioned that phonograms published with the aim to commence business or to broadcast to the public through any media, the user must pay a reasonable remuneration to the performer or publisher who is the right holder even to the both29. If there no indication in the national legislation regarding the non-existence of agreement among the parties under this Article the remuneration would be equitably shared among the involved parties, even if the producer of the sound recording is consequently approved to have a roundabout right to communicate, but not a granted right to distribute those recordings to the outlets. On the other hand, Article – 22 of the Rome Convention provided special provision to accommodate the member states to settle the right to commence special agreements among the broadcasting company, performer, and producer with more explanation of the rights and duty of the involved parties, but not contrary to the core essence of this Convention.30 The Article–11, of the Rome Convention dealt with the right to communicate literary works including music to the public, it explored that the authors of literary works especially books have exclusive right to give permission to circulate them to the public or market where the author have facilitated with exclusive rights to authorising anyone for republishing their works. Although the scope of the rights allowed under the Rome convention is very narrow to accommodate the copyrights protection for treaties in the Internet era, but it is the background regulation and analogue forms of communication to generate appropriate measures for the digital economy and content management.
The Universal Copyright Convention
Due to the inadequacies of the Rome Convention, the Berne Convention come into practice a foundation of international copyright law, but few of the super powers like US an former USSR were uncooperative to comply wit it, to harmonise the copyright legislation the Universal Copyright Convention commenced in 1952 to convey practice of an acceptable copyright law for all parties. Later in 1971, the UCC was amended that explored the integration of less developed countries with the core essence of the convention and those countries were allowed to achieve obligatory licences under particular terms and conditions to translate the copyrighted works into local languages for the reason of teaching as well as research purpose. The convention has expended the area of copyrighted materials and pointed out that all literary, scientific and artistic works books, journal, newspaper, reports, conference papers, writings, including computer software, music, drama and cinematographic materials, along with paintings, and sculpture would be considered as intellectual property that demands protection from plagiarism or any unauthorised application without the author’s prior concern.
WIPO Copyright Treaty
Dinwoodie notes that the WIPO Copyright Treaty has explored a new era in the global practice of copyright protection due to two reasons as the issue of copyright bought into discussion at diplomatic conference in 1996 and the second reason is that the convention was a break point at the instant while two other internet treaties were in conclusion stage31. Idris notes that rather than WCT, this international body passed another regulation ‘WIPO Performances and Phonograms Treaty’ in the same year in Geneva, both the two treaties have same core essence while WCT ensures to protect the rights of the authors of writers, artists, programmers, and databases designers while WPPT has aimed to protect rights of performer, producer of phonograms along with broadcaster32. To ensure appropriate implication of the WCT and in the WPPT obligations, the member states were directed to integrate the concerned provisions of copyrights into the national legislation while the global treaties connect a variety of national regulations as well as necessitate the countries to join into the treaties to award definite rights those would be specified at non-discriminatory basis.33 It has established by the WPPT and the WCT treaties that the copyrights of intellectual creation would be protected by the national legislation of each individual countries, the basic intention of the treaties were to update the mainstream spirit of the Berne Convention to protect literary and artistic works, which was introduced about half of a century back from now. The technological development and introduction of the Information Technology have generated new paradigm to address the challenges pretence concurrent digitalisation in at specific distribution of the soft copies of the copyrighted material through the Internet and this is why the treaties are pointed as the ‘Internet treaties’.
More than hundred of the countries have already provided their consensus on the both the WCT and the WPPT that indicates a wider global agreement on how the copyright protection drives would be implemented under the present environment of the Information technology era in context of digital economy. This is most significant issue for all users and stakeholders due to the complex procedure of the technology that occur a lot of compromises at some stage in the negotiation process among the stronger rights seeking countries beside the countries looking for hard protection under existing the WPPT and the WCT34. Reed notes that as a conduct of the diplomatic conference, the convention kept provision for the contracting states to put into practice in the national peripheral, depending on the excremental outcomes the countries may decide to join in the treaty to protect intellectual property from the unauthorised commercial use in accordance with the features and process that the WCT presented.
Convention on Cyber Crime 2001
Hopkins pointed out that due to the revolutionary implication of the Information Technology, people all over the globe has been experiencing different computer crimes in their regular life, for instance credit card fraud is a most common evidence where the criminals are hacking the victim’s personal information from the concerned website of his bank account35. Using those confidential information the computer criminal are transferring thousands of dollars from the victims credit card account, after commencing such offence they are destroying the records from the database, so the tradition way of trailing criminal offence fails to prove such theft and the criminal kept out of judgement without considering any geographical border barrier. Prior to the US Electronic Theft Act – 1997 the county was unable to respond rapidly to the rapid changing nature of crimes occurred through the Internet Technology, so the Congress endorsed a statute to encounter with the cyber-crimes generated from the adoption of new technology with the aim to avoid the critical aspect of the crime that hinders investigations. On the other hand, the existing legislation was unable to prosecute the individuals who hosted their websites to download software and copyrighted publications by anyone without any cost, as there is no evidence to prove the financial gain from illegitimate copying; thus, it is emergence to introduce appropriate legal framework to frame criminal charge against them36.
To overcome such dilemmas to prosecuting cyber crimes, it is essential to have international cooperation to identifying the individuals aligned with offences, where the Council of Europe has attempted to design a global treaty to protect cyber-crime through a multinational cooperation in this regards and capable to respond quickly to the changing nature of crimes and the Cyber-Crime Convention-2001 appeared. The prime objective of the convention is to correspondence to the domestic criminal law by harmonising the nature of offences and the way out of investigation procedures with two major concerns, firstly it aimed to make certain that the definition of crime is enough flexible to frame charges for any new nature of crimes whatever the process of committing crimes. Secondly, the policymakers were adamant for not to hindering the investigation process for geographical border barriers with due respect to the national legislation and guided the convention to hang about sensitiveness of the legal frameworks of involved countries. Cunha, Marin & Sartor notes that due to the socioeconomic and cultural differences along with the human rights factors in different countries, it was extremely challenging to unify the outlook of the global populace to the convention; for instance, European citizens are always eager to superior level of privacy protection while the US citizens have superior level of speech protection that may hamper investigative procedure37. Thus, the convention has attempted to balance these dilemmas by means of local legislation providing definition of crime and the necessary local law for investigation without hampering human rights and prevailed privacy policy guaranteed by the local framework. The major organisations involved to designing the global cyber crime policy are the CoE, the EU, and the G-8, at the same time, there are some contribution to this convention were kept by OECD and the UN, the Ministerial Committee of CoE kept vital role putting their recommendations to the member states to establishing harmonised procedures for implication.
Legal Framework for ISP Liability
The innovation of the Internet is the major contribution of this century that has provided the human race huge opportunity to communicate each other within few moments though out the globe by using online connectivity through the local ISPs and communication by e-mail, file sharing, file transfer protocol or online chat with a minimum cost than other traditional communication tools. The Internet has identified as a network of networks, which is an assortment of packet computer networks, attached collectively with the help of some software protocols TCP or IP those allow the computer networks to trace and identify the desired computer that he would like to communicate the digital form of information that like to share. Beside the opportunities that the Internet provided, it has generated massive threats of violating of IPR, while the people provide their digital products to sell online, any hacker could collect them and simultaneously able to sell them through online without the prior permission of the publisher or creator that ultimately hamper the interest of the copyrights holder. Due to raising demand of digital contents for the real world research, the distribution of unauthorized publication and plagiarism has tremendously increased by violating IPR that made the legislators, business communities, and academia to rethink for strict protection of the intellectual properties and transmission of digital data in the virtual world. Without any doubt, the Internet has facilitated the copyrights holder with the opportunity to enjoy an extremely wider market than ever to sell their digital commodities online, but the backside of the same coin it has generated the intellectual properties defenceless to illegitimate occupancy and allocation without any border barriers through out the globe where some liabilities adopt on ISPs38.
To protect the amplified social and commercial utilisation of the Internet and to rescue the confidence of the stakeholders, it is emergence to identify the extents of the ISP liability from different legal aspects linking with intellectual property; this research has engaged its efforts to identifying dilemmas from the legal framework of India and the United Kingdom. In context of both countries, there is remarkable advancement to digital tools to identifying the copyrighted materials directly copied in the concurrent research and digital contents, but the factor is to what extent the counties have developed their legislative framework to panelise such illegal actions while imposing the liability on the ISPs is much debated issue in the global practice.
Anti-Counterfeiting Trade Agreement
GIPC point outs that the Anti-Counterfeiting Trade Agreement – 2008 got its foundation by the multilateral negotiation among forty countries with the aim to carry out the enhanced cooperation for intellectual property (IP) protection in a harmonised way and to combat the rapidly increasing online businesses those are threaten for copyrights and piracy violation at a global scale. To complete the negotiation among the member states it takes three years with nine rounds of discussion and explored their joint statement in 2011 arguing that the fundamental goal of ACTA are to boost global cooperation by promoting legal infrastructure for dynamic enforcement and practice of the IP rights and urged to establish similar standard of WTO connecting the TRIPS.39 There are some myths that the legislation has turned the civil offence into criminal liability, but to fight against counterfeiting and piracy, ACTA clearly mentioned that only the wilful violation of privacy and copyrights for economic or commercial benefits would be considered as a criminal offence and there no requirement to have prior approval for prosecution for minor infringements. ACTA explored its viewpoint on the freedom of speeches arguing that during the enforcement of this legislation the primary principles of the freedom of expression with fair process to ensure privacy would be integrated while the member states would take care to ensure suitable balance among the intellectual property right protection and local public interests that ultimately increase IP investment.
Rather than a closed-door negotiation, ACTA explored through an open discussion among public and it strongly pointed ISPs liable for copyright infringement that may not be overburden for ISPs and make those ISPs bound to employ close observation of justifiable communications by ensuring transparency, compliance of law connecting the national law of the operating country. At this instance, ACTA does not imposed any new liability on ISPs, but particularly allowed the counties to limit the prevailing liability that was ISPs in practice before, just it is clear obligation that stolen copies of digital commodities and its distribution or illegally file sharing would be accountable as a criminal offence. In such case of violation of copyrights or privacy, ACTA kept the provision to seizure the equipments such as PC, laptops or MP3 players from the suspects under its Article 14, encouraged to put into practice of an elevated standard law enforcement process complying with the domestic legislation, and mandated the signatory countries to publish the relevant procedures.
Global Provision and Practice of ISP Liability
ISPs in the limitation of liability
Popoola states that it is difficult for the victims to establish liability in aspect of the UK law, which is one of the most important factors in order to proceed and impose liability for breach of duty by the perpetrators40; however, Communication Act41 amplified the scope for the victims to impose duty on the ISPs for the online violation of copyright, but there are many other factors influence in this sector, for instance, article 15 of the ECD42 prohibits the member States to adopt obligation on ISPs. According to the provision of the ECD, the ISPs are not bound to monitor the information transmitted or stored; however, the UK is the prominent member of the European Union and this country is bound to incorporate the regulation of the EU, so, the sections of Communication Act also reflect the provisions of the treaties and regulations. Popoola points out that ECD imposed no obligation to the ISPs to seek facts or circumstances demonstrating unlawful actions, but it provides the opportunity to the public authorities to monitor clear and unambiguous cases to take effective technical measures; thus, the Communication Act does not force ISPs to monitor while the concept of technical measures can violate freedom of speech43. In case of Promusicae v Telefónica44 the ECJ held that article 13(1)45 creates an exception to the general rule46 of ECD, for instance, member States may disclose confidential communication when it is essential, appropriate and proportionate considering the issue of national security; at the same time, Communication Act included some sections47 in order to identify the perpetrators. On the other hand, there is no exact law for explaining the extent to which ISPs are bound to take liability or the machinery of actual knowledge, but the ECR48 provided a general direction in this regard, for instance, constructive knowledge49 is the level of measurement mere conduit though notice is a significant factor of consideration in such conditions50.
Legislator and other administrative bodies of India had considered the international regulation and conventions to impose liability on the ISPs, but this country was not bound to comply all the provisions of international regulations; thus, India has more scope to pass a strict law to assist the victims and captured the culprits who use internet for unethical and wrongful purposes. However, some limitations of the Indian law to adopt liability on the ISPs are –
- Some provisions of the Information Technology Act (2000) are vague to understand, for example, section 79 of this act directly limiting the liability of internet service providers and provide enough opportunity to adopt such provision for unusual purposes, such as, irritating ISPs;
- On the other hand, the ISPs can escape the liability if they can ensure that they exercised all due diligence; thus, the term “due diligence” is a significant factor to determine liability as this term has not defined in this act, which creates hindrance to interpret the term for the different situations;
- This section has not specified who bears the liability for the violation of copyright;
- Rowland & MacDonald note that there is no act to classify or define ISPs, which creates uncertainty to impose liability on the appropriate culprits51;
The exercise of freedom of expression
Rizk notes that Internet service providers play an important function in facilitating Internet subscribers to adopt their right to freedom of expression and gather knowledge; however, most of the countries have imposed legal burden on the ISPs in order to control illegal contents and prevent access of the users who involved with cyber crime or other related offence 52. At the same time, it becomes a legal demand to the ISPs to eliminate, filter, delete and block illegal contents to save the victims though it is a grey and unsettled area of cyber law that whether ISPs’ would be responsible for the act of third parties or not. In developing countries like India, Internet usage is quickly rising but the legislator have just started to concentrated on these issues to specify the liability of the ISPs; therefore, Rizk notes that India has to local law enforcement authorities should have strict power, which will encourage the ISPs to take immediate action or monitor the activities of the users. In this context, the government of India has taken initiatives to change the provision, for instance, considering the EU E-Commerce Directive, Information Technology Act 2008 concentrated more on the ISPs for user content; however, the government provided very short time to evaluate the draft regulation, which encouraged the civil lawyers to protest the new law. However, Rizk further argues that India upheld the concept of freedom of expression with high priority, but illegal content increased number of cases, so, the government should consider impose liability to remove illegal content within 36 hours of notification to avoid flood of cases in this issue.
On the other hand, the government of the UK need to comply the articles and other provisions of the ACTA53, TRIPs54, WIPO Copyright Treaty, ECR, ECHR, and so on; therefore, it is difficult for the legislature to introduce new acts imposing such provision, which is arbitrary and incompatible with the EU regulation and the concept of freedom of expression.
Argument for Imposing Liability on ISPs
- Mishra & Dutta notes that it is hard to locate the genuine offender because the Internet permits customers or others to stay on unspecified making it impossible to locate the definite wrongdoers; however, the ISP is identifiable as well as locatable as they placed them in the same jurisdiction in most of the cases55. In this context, it would be easier to impose liability on the ISPs to identify the original culprits;
- Furthermore, Mishra & Dutta states that the perpetrators have not capacity to provide sufficient remedy in the cases, but the internet service provides have enough financial strengths to ensure justice; as a result, the legislator and other bodies would consider such kind of economical and social aspects;
- Smith notes that it is easy task for the internet service providers to monitor the performance of the users because law enforcement agencies do not have enough technical support along with knowledge to scrutinise the users with low efforts56;
- At the same time, the ISPs have the opportunity to protect the users by closing down the home page or site, blocking accounts of all potential originators, removing an e-mail account, creating new system for the perpetrators, and stopping further breach; therefore, it is rationale to impose some liability on the ISPs to minimise cyber crime in some extent;
- The legislator and other policy makers would like to impose liability on the ISPs in order to overcome the problems related with jurisdiction;
- It is important to ensure legal certainty, finding a balance, and so on;
Argument against Imposing Liability on ISPs
There are many issues for which it should not be feasible to impose liability of the ISPs; however, the following points illustrates these factors more elaborately
- ISPs considered themselves as a passive carriers, messengers of publishers or mere conduits of data;
- It is not possible for the ISPs to control or monitor all the content of the site, so, it would be impracticable to impose liability on the ISPs and in crease of Netcom 57, the court supported this point;
- It can create hindrance to expand of the development of technology in the country like India;
Comparison of ISP Liability in India and the UK
Mohanty argues that two issues in India and the US have increased concerns regarding the mediator-liability law in India, which is now deemed as defective; the first was the ruling of court in America regarding quite popular Youtube-Viacom copyright violation lawsuit, whilst the second was requests from MPs for cancellation of Intermediary-Guidelines with a writ-petition in Kerala-High-Court challenging it58. Whilst US regulation for mediators ensures their protection, the regulation of India at this issue is stuffed with uncertainties; it requires direct standard-setting-exercise – ISPs in India are not even convinced if someone could assert protection as a mediator for copyright-breach claims; even in 2012, this law is uncertain on whether it should endow protection to mediators for such claims. According to Vij, a number of problems exist in India that arise because of the rules; although a few of these were stated in detail earlier, a snapshot of some more problems are included in the table below 59 –
Table 1: Problems of IT (Intermediaries Guidelines). Source: Self generated
In contrast, Workman notes that several directives and regulation have issued from the EU on the cyber crime related aspects, but it introduced the responsibility for the ISPs in 2000 in the Directive 2000/31/EC and Directive 98/34/EC; however, ISPs can exclude accountability if they serve as a mere conduit or temporary caching (Article 12-13)60. The government of the UK took initiative from 2008 to enact legislation to adopt filtering measures to take concrete steps against unlawful downloads; on the other hand, the measures became controversial while larger ISPs have taken action against such legislation considering incompatibility.
Extent of liability of internet service provider in the UK and India
The Information Technology Act in India (2000, 2008)
Mishra & Dutta noted that in India, the copyright legislation does not necessarily take care of internet service providers explicitly; nevertheless, stipulations regarding this have been particularly considered in the Information Technology Act 2000; as a resultant effect, such intermediaries are now subject to strict regulation and any breach of proper conduct from their part may result in lawsuits61. According to Dara, online service providers are extensively acknowledged as the vital mediums for implementing freedom of expression all over internet; additionally, many jurisdictions throughout the globe have already established laws to restrict mediator-liability with intention of ascertaining continuous and uninterrupted internet services; however, fury flowed in India for a case where a mediator was impeached for hosting user-generated-content62. Dara further added that the country has modified s794 of the Act in 2008 and tied with countries that restrict intermediary-liability; later, in 2011, in applying its command under s79(2), the governmental cabinet stipulated IT (Intermediaries-Guidelines) Rules 2011; in this context, this sets down a privately directed ‘detect and record system’ for restricting mediators’ legal responsibility throughout the country63. WordPress suggests that the administration of the country recognized the necessity of new-regulation and for creating apposite modifications to current regulations to provide legal-recognition to electronic-records or digital-signatures; the lawful acknowledgment to e-records and digital-signatures would assist termination of agreements and formation of lawful rights and compulsions during the e-communication like internet; this has originated the Information Technology Bill 199964
According to WordPress, both the chambers of the legislative body of the country passed the Bill in May 2000, which got the acquiesce of the president in August 2000; it is important to note that this IT Act wants to afford an authorized network for e-commerce in the country, which in turn will present a great effect for online businesses65. In addition, the Act plans to grant a lawful structure on which an authorized inviolability can be attached to every e-records and other actions conducted via internet; furthermore, it is particularly notable that according to the this groundbreaking law, unless otherwise settled, a recognition of agreement could be articulated via internet announcement and this will possess lawful authority or obligation. For making certain modifications in accordance with the changing demands of the online communities, the Act was decided to be amended further; as a result, the modifications were brought about by the IT Amendment Bill 2006, which was approved in Loksabha and Rajyasbha in 2008; it would avert computer-based offences and ascertain safety-practices in perspective of broadest-possible application of IT-worldwide.
The Information Technology (Amended) Act 2008 has a number of essential objectives, which has been designed by the asking and opinions of the online communities, electronic business owners, e- commerce sites, information technology enabled service providers, and other internet users. WordPress has further suggested that the key aims of the Information Technology (Amended) Act 2008 are quite inclusive; this has been included in the following table in more details to show the features of the law comprehensively66 –
Table 2: The main objectives of IT Act. Source: Self generated
Liability of Intermediaries under the IT Amendment Act 2008
Katoch suggests that the ITAA 2008 was ultimately enforced on October 2009; according to ITAA 2008, the term “intermediary” would particularly comprise internet-service-providers, telecom-services-providers, network-providers, web-hosting-service providers etc; however, it is important to note that s 79 of the IT Act 2000 was indistinctly outlined and was deemed cruel on intermediaries; an illustration of this is the case of Baazee.com67. As a result, even through strict liabilities were imposed on the internet service providers in the 2000 Act; these liabilities were loosened up to a great extent by the changes brought about by the 2008 amended act. According to 2000 Act, ISPs were excused merely if they established that they were not engaged with breaches or if ISPs did everything necessary to avert crimes; Gupta stated that this made ISPs legally responsible if constructive-knowledge was established or deficiency was observed to take actions against breaches; nonetheless, it was unfeasible for ISPs with medium-traffic to watch its contents68. ISPs will not get this exemption, if they planned, assisted, or persuaded (through pressures or assurance) the completion of the crime; s79 additionally initiated the notion of notice-and-take-down specifications as ubiquitous on a lot of international legal systems; this means ISPs would lose indemnity after getting aware that any user-information is exploited for performing-crimes and fails to disable-access to that.
Although ISPs are indemnified in s79, liability will remain in s72(A) for revealing any personal-information without permission or with malicious intention; penalty of these actions is detention for a maximum of three years or fine of five hundred thousand Indian-rupees or both; a controversial portion of ITAA-2008 is the specification of s81 that the law will possess an overriding-effect. Katoch stated that as per s81, this law could not confine individuals from practicing rights bestowed in Copyright Act 1957 or Patents Act 1970; however, this stipulation has formed a great deal of perplexity regarding the degree of indemnity in s79; s79 of ITAA is supposed to be a protected port criterion replica on the European Union Directive 2000/3169. Rizk stated that this legislation seems to be a great danger for the users of internet in terms of freedom of expression; different states of India are applying more and more restrain on ISPs to keep ISPs legally responsible in case of failures to stop admittance of illicit contents; after Baazee-case, the Parliament curtailed liability of ISPs for user content70. Jaitly notes that this could have been scientifically impracticable for ISPs to monitor all user-content at their sites, particularly because of huge number of data that enter raises gradually; most significantly, inflicting this onerous-criterion could compress originality, strangle Indian-competitiveness, or avert owners from installing new-services; this was considered to be a hurdle for the growth of the country’s IT industry71.
IT (Intermediaries Guidelines) Rules 2011 and the Issues that Need to Change
According to PRS, the ITA 2000 had initiated four-sets of rules, as modified by the ITAA 2008; the Security-Practices Rules needed bodies with perceptive individual data of online-users for preserving some particular safety benchmarks; the Intermediary Guidelines Rules will exclude content of definite type from online; so, an intermediary, such as website-hosts or ISPs, are required to obstruct such content72. Under the Information Technology (Intermediaries Guidelines) Rules 2011, the guidelines regarding the operational principles for the internet service providers are stipulated; in order to understand the rules in a comprehensive manner, it is important to assess and identify the most important aspects of these guidelines. In the table below, a detailed analysis of the main issues of the guidelines are outlined –
Table 3: The key facts of the IT (Intermediaries Guidelines). Source: Self generated
T-Series v Myspace
Saikia notes that the verdict of Delhi HC in the case of T-Series v Myspace and Another was the first-verdict in India handling the issue of mediator accountability; the fact of the case is that users can upload music on MySpace; so, they tried to upload music belonging to T-Series, but T-Series was not keen regarding this without its consent74. My Space stated that T-Series would take advantage of its rights-management-tool to avert breaching song from being added; T-Series declined this submission – addition of song by users was not prohibited on entrance, so T-Series litigated for the breach of the copyright in its works; later, it seemed to enquire an injunction in opposition to encouragement to carry out copyright violation. However, Saikia added that injunction is not usually accepted in the kingdom of copyright regulation in India, and this was bizarre in itself; at this stage, the court clarified that Myspace could be responsible in s 51 (a) (i) for straight breach; but this must be proved that Myspace had unlawfully sanctioned the violation of T-series ownerships75. In addition, Saikia pointed out that two other things were needed to be proven – these included proof of an obvious and participative role in such an encroachment and use of certain extent of restrain over any such action representing encroachment; finally it was held by the court that MySpace had undeniably perpetrated violation of copyrights76.
JK Rowling v Vinay Varma (Baazee.com Case)77
Datta pointed out that the writer of Harry-Potter books-series initiated litigation on 2004 because of copyright-breaches as well as trademark-contravention in opposition to five-defendants in the Delhi HC; defendant number five was auction-portal of India, Baazee.com; they (indicted for adverts proffering the books for sell) were restricted from promoting or backing the material; moreover, warnings were given to Baazee78
In 2007, the Delhi-HC originated a direction for expanding eBay’s declaration that it will not exhibit any aberrant announcements of the four individual-defendants unless the lawsuit is at least set out; however, afterwards, information showed that e Bay filed a contempt-petition against claimants’ suspected press news and publications, asserting that these declarations resulted in a distortion of the genuine conclusion.
SMC Pneumatics (India) v Jogesh Kwatra79
According to Helplinelaw, in this landmark case, a worker was libellous about the status of a business by giving offensive electronic- mails to owners as well as diverse subordinate firms around the globe for vilifying MD – as a result, the judge of the Delhi-HC approved an ex-prate ad interim restriction noting that the claimant conducted a prima facie case80
Subsequently, the Delhi-HC controlled the defendant from giving offensive electronic- mails to the claimants as well as to its subordinate firms around the globe, the MD, or the different divisions; complementarily, the court also controlled the defendant from issuing or broadcasting any data in virtual planet as well as in cyber place which is insulting, libellous or obnoxious to claimants81.
Trade Marks Act 1999 (India)
According to Altacit Global, the description of trademark is extended to include any mark able to differentiate the goods and services; renowned sketches could now give shield in this regulation; moreover, one of the most important accompaniments in this law is the stipulation of Service-mark-registrations, and this is a result of the intensification of description of trademark to comprise services82. Many corporate bodies or persons proffering any sort of service can register their mark; in addition, collective mark (a mark utilised by the affiliates of an organization) is a latest idea conveyed in the law that makes it likely for any organization for acquiring registration of its mark; conversely, renowned-trademark concept will be utilised over goods or services with adequate-recognition. Moreover, it is extremely important to note that the period of shield of trademarks is increased from seven-years to ten years; additionally, regeneration would be possible prior to finishing point of ten years in infinity; conversely, penalty would be at least of six-months and could extend to three-years together with a fine of fifty thousand to three hundred thousand Indian-rupees.
The Copyright (Amendment) Act 2012 (India)
DNA notes that the country has long waited for this act to be modified in accordance to international standards so that users in India can finally protect their works efficiently; for expanding shelter of copyright-material over online, books, theatres, songs, creative workings, movies, and soundtracks, the modified act corresponds with international treaties; the modification will begin a method of statutory-licensing83. However, the changes were carried out in compliance with the World Intellectual Property Organisation (WIPO) Internet Treaties; in fact, the act also possess a section that gives special arrangements for bodily handicapped people to acquire copyright-materials; the copyrights will be appropriate for the most part of search engines, together with different types of internet-services, whether or not enclosed on interpretation.
Trade Marks Act 1994 and ISPs Liability
According to the view of Smith, internet is the a shop window and place if advertising in aspect of business as it gives the opportunity to the companies and individuals to reach global customers, but this scope has crated legal barriers in terms of jurisdiction; trade marks are national by nature and they can be registered or unregistered84. The UK government has passed this law in light of the EU Directive No. 89/104/EEC containing both civil and criminal law sanctions for the infringement of the sections of this act, for instance, it provided legal framework for saving the companies from Anti-counterfeiting efforts; however, this act has not focused on the liability of the internet service providers. In addition, this act helps the registered companies (covering some goods and services) to protect their brand all over the world, but the protection varies for the unregistered marks; however, the companies had faced many problems due to different legal framework in different nations and it was also uncertain what would be the remedy for the breach. However, Diane & Elizabeth report that this act includes sections for effects of registered trademark (section 9 to 13), infringement of registered trademark (section 10), infringement proceedings (section 14 to 21), and application for registered trademark (section 32 to 34), registration procedure (section 37 to 41), powers and duties of the registrar (section 66 to 70), certification marks and so on85.
Smith argues that trademark holders and infringers fight in the internet and the following points illustrate trademark clashes on the Internet
- Genuine clashes: there were two types of dilemmas with some difficult characteristics and both parties have legitimate claim to proceed; however, the following table gives more information in this regard
Table 1: Genuine Clashes. Source: Self generated from Smith
In Create & Barrel case, the court also held that use of trademark in the internet is the violation of the act because trademark is registered for a specific jurisdiction; therefore, it is rational to impose burden to protect use of trademark for the online advertisement.
- Cyber squatters: On the other hand, it is different type of clash and it starts generally when a company sale its intend to expand its business operation in the international market
Copyright, Designs and Patents Act 1988 (UK)
Fox v Newzbin87 was a case for online copyright infringement where the association applied for the injunction to the British Telecommunication to protect piracy as the defendant helped the users to search unlawful copies; however, the Applicants were six eminent film production firms or distributors (members of the Motion Picture Association) and the defendant was a British Usenet indexing website88. However, the respondent of this case was British Telecommunication; here, Dalton notes that the defendant argued that it was content agnostic, provided a file system and only a search engine like Yahoo and it offers hyperlinks with the result to the users; at the same time, the subscribers can upload and download the content by paying a monthly subscription fee89. In this case, the applicant claimed that the defendant misused their service line and gave unlawful opportunity to the subscribers to search for and download copyright protected works, which was prime source of income of this site and the company generated 99.7% profits using such unethical and unlawful business strategies; in addition, it introduced many software to serve this purposes. As a result, Dalton point outs that the claimant seeks two remedies (injunctions against the defendant to cease offering access and cease indexing all copyright-infringing material) and makes three specific claims against the company, such as
- Infringement of copyright works: the court had analysed more than 50000 reports and identified about 98% were valid links to the IMDb site, and only 0.3% were non-copyright works; therefore, majority of the content were illegal in nature and text content was highly misleading and wholly inconsistent with the Newzbin user interface;
- Encourage or enter into a common design to copy the films of the claimants:
- Communicate with the subscribers to promote its services
The applicants claimed under section 97A of the CDPA 198890 as this section 97A permits the right holders to seek an injunction against the ISPs if they have actual knowledge about the infringement copyright by the users or subscribers; however, it was the first case where copyright owners sought remedies under this act. However, the defendant argued that they had no function in this regard and they were not a part of such infringement, but the court took into account all the evidence and held that Newzbin could not exclude liability for the three claims because the company authorised the copying of the claimants’ films and content. Moreover, the court granted the first of the injunctions to cease offering access to copyright protected works because they had actual knowledge about infringement and they were liable to pay the Studios’ costs though this company filed for bankruptcy, so, the respondent took no action for damages; however, the judge stated that this injunction was too wide to be justifiable.
UK Digital Economy Act 2010
This is one of the most significant acts to the administration as it included the ways to strengthen industrial policies to develop national economy by creating new opportunities for the business sectors to overcome from recessionary impact; in addition, it will help the industrialists to face intense competition in the global market particularly with India and China. At the same time, the developing countries are carrying on business with superior skilled and value added economic activities; therefore, the government of the UK focused on some aspects, such as, encourage innovation, in new digital and broadband technologies, telecommunications infrastructure, and the content and creative industries. BIS notes that the aim of this act was to concentrate on the development of digital infrastructure, set out the right framework to promote further investment; in addition, this act placed an obligation on the ISPs to inform users of their illegal activities, and to maintain records of the most frequent perpetrators91; however, figure no 2 of appendix gives more information–
McLaughlin notes that there are seven giant ISPs92 those give internet connections to more than 96%, which influence OFCOM to impose rights and liabilities on them93; however, the figure no 3 of appendix gives more information about implementation process.
According to the report of Crown Copyright, there are more than 450 fixed ISPs in the UK, which aggregately make profits above £3 billion per year, and six giant hold about 90 percent market share; on the other hand, there are minimum 6.5 million illegal file-sharers, which involved in unlawful activities94. However, the purpose of this act is to decrease unlawful downloading by 55% (around £200 million), and stop infringement by 70% as this act made provisions for the infringers that they will stop they unlawful activities as soon as they notified by the ISPs, which will increase the costs of the ISPs by £20 million to £65 million. At the same time, ISPs will send letter to the infringers to mitigate the issue for which ISPs need to expend additional funds; in this context, the requirements of this act to protect copyright infringement became controversial to the ISPs and the made several claim in this issue stating that this act is incompatible with the EU law. OFCOM reported that impose burden on the ISPs will create a new ex-judicial procedure to handle appeals as ISPs are responsible to take technical measures and to provide copyright infringement report to appropriate IP addresses; in addition, ISPs asked to the users about the violation and if they fail to adduce evident for them, then ISPs can remove the content. However, few provisions of this act are
Table 4: Important Sections of DEA 2010. Source: Generated from96
In BT Application Case97 British Telecommunications and TalkTalk (two of the UK’s greatest ISPs) made an application for judicial review on the ground that the provisions of DEA 2010 and Copyright order 2011 were incompatible with the EU law; however, these companies argued the following points
- Miller states that DEA imposed liability on the ISPs (Section 15 introduced a new section 124A to 124M of the CA 2003) to notify the customers or users of their services if copyright owners complained against them for the violation of the acts98;
- In addition, ISPs would be responsible if the ISPs fail to comply the “technical obligations, for instance, ISPs can limit internet access”
- The companies also mentioned that the legislators have not notified the European Commission;
- Palmer states that the provisions are incompatible with the EU Telecoms Directives, the PEC Directive99, EU law and the ECHR, which adversely impact on the ISPs100;
- Mansell & Steinmueller state that this act is disproportionate in terms of free movement of services101;
The Court rejected the application, but considered one point of view, which related not to the Act; in addition, the court held that the Government is free to press ahead with implementing the DEA, but it has to be adjusted Ofcom’s costs of administering the scheme; therefore, the ISPs are bound to follow the provisions of the DEA 2010. The court rejected the case for various reasons, such as, Parliament significantly addressed the main dilemmas related with social and economic policy, initial obligations of ISPs sections 124A and 124B were conditional, and no breach of Article 8 of the Data Protection Directive, Article 15 of the Directive permits member states to pass law to protect copyright, and so on102. However, Gardner reports that it was a disappointment for digital rights campaigners because sections 3 to 18 amend the CA 2003 and gives the right to the copyright holders to send copyright infringement reports, and then the ISPs must notify the subscribers regarding the violation and take all technical measures in order to limit or suspend subscription103.
Loopholes of DEA 2010
According to the report of BIS, Smaller ISPs are not responsible to notify the users (though they must inform manually in some extent) regarding infringement or unlawful behaviour in accordance with this act considering the economic condition of the small service providers; however, the five greatest ISPs must notify the scribers using automatic process. It is important to mention that smaller ISPs offer different service, such as, P2P networking services, which also give the chance to the users to download digital products with a higher legal security; therefore, a large number of copyright infringers would be influenced to switch off the company to use service of the smaller ISPs to escape any legal barriers. This legislation could adversely affect on the legal and business operation, for instance, a significant number of infringers with general users will use service from small ISPs in the UK, which will demand to change the provisions of the act to protect copyright holders; moreover, small ISPs have not sufficient bandwidth and technical support in order to provide upgrade services. At the same time, the government of the UK imposed no liability for notification or expenditure for this purpose because it would be disproportionate to adopt costs on the small ISPs in a per unit basis as they earned below £1 million, so, if the charge remain same for all ISPs, then small ISPs will collapse or bankrupt.
ISPs Liability for Defamation in the UK law
JISC Legal reports that publishers are legally accountable for their own published contents while they make sure that they are not violating the rights of others; however, the issue became controversial when intermediaries have charged for a defamatory statement (possession of unlawful as well as illegal content) as a third party104. The ISPs are not responsible to monitor the content of the users, but if they have actual knowledge and take no reasonable action (take care of the notice of the victim seriously and inspect the issue without delay), then they cannot exclude liability; however, Section 1(1) and 1(3) of the Defamation Act 1996 provides defence for the defendant.
Godfrey v Demon105
In this milestone case, the court first impose liability on the ISPs for online defamation; in this case, the plaintiff was physics lecturer who received message to the Usenet discussion group from an unidentified source, so, the plaintiff contacted Demon Internet to remove such message and ISP deleted after ten days but ISP failed to take action in time. In this context, the plaintiff sued for libel stating that ISP had taken no initiative at early stage and the defendant intended to take the advantage of the defence of innocent dissemination; however, the court held the plaintiff provided notice to the ISP, which indicates that ISP had actual knowledge regarding the issue and the court imposed liability106. However, the court held that the defence of Innocent Dissemination (as ISP was not author, editor, or publisher and it took reasonable care) was no longer available for Demon and then the defendant settled the case by providing £265,000 to the plaintiff, but the Media lawyers stated that it was violation of human rights in terms of freedom of expression.
Bunt v Tilley and others107
In this case, the claimant alleged defamation against three internet service providers who were responsible to provide hosting services; however, the court held that ISPs perform as passive facilitators and they are not actively procuring the commission, so, it would not be rationale to impose liability on them until and unless the claimant makes proper notice about the breach. the court held that legal responsibility lies on the ISPs if they permit the perpetrators or fail to take reasonable care after knowing about the defamatory content of the sites; however, the court held that imposition of liability in case of Godfrey was acceptable considering the sections of defamation act, but the ISPs have right under the e-Commerce Regulations.
Keith-Smith v Williams108
Gibson notes that this is an important case in the area of online defamation and the claimant asked for claim for injunctive relief; in this case, the claimant was a politician of Conservative party, but he had participitaed in the election as a member of the UK Independence party and he signed up to an internet discussion group in Yahoo109. The claimant had involved in the debate (controversial issues) with many individuals like Tracey (defendant) and the defendant had published some defamatory statement and some content were available in the news board of Yahoo; therefore, the court held that Tracey liable to pay £10000 in damages along with legal costs £7200 costs and the court warned the defendant as well.
Tamiz v Google110
Rea reports that the claimant complained against Google instead of the original blogger In this case; however, Google relied on the defence of innocent dissemination (it was not publisher) and Regulation 19 of the ECR; however, the court held that the company failed to convince the judge as the statement constituted a real and substantial tort111. However, the court held in that most of the ISPs rely on the above mentioned defence or said that they have not actual knowledge regarding the issue; in this case, the court held the Google took very short period to remove the illegal content, so, the defence is available to this company; thus, ISPs are not considered liable for online defamatory posts.
Conclusion and Recommendations
Recommendations
- DEA 2010 has imposed no burden of notification to the smaller ISPs, so, it is easy for the infringers to use smaller to violate copyright act; therefore, the government should impose some burden on the smaller ISPs considering economic and legal aspects in this regard;
- On the other hand, the developing country like India has not differentiated between the smaller ISPs and the larger ISPs; therefore, it becomes difficult for the smaller ISPs in India to minimise costs to notify the subscribers or users if they infringe acts related with copyrights;
- At the same time, it was important to the legislator to consider for whose the rights need to be protected, nature of infringing behaviour, enforceability of legal sanctions, and the process to handle the problem related with this issue to impose liability on the ISPs;
- The government of India concentrated more on the issue of freedom of expression and can modify national legislation considering international convention, acts, and journal reports and so on; however, India is not bound to comply the directives of European Union and if this country makes any law, which is incompatible with EU directives, then there is no problem. But the government of the UK needs to focus on the directives of European Union, otherwise, it has to face legal barriers for incompatibility in the ECJ; therefore, the policy makers should introduce new provision for the ISPs concentrating the fact of freedom of expression and European Convention of Human rights;
- It is important both for the UK and India to concentrate more on the research work to reduce such problems;
- From the above discussion, it can be said that ISPs are not directly liable for infringement in the UK; as a result, it should essential to reduce the limitations of the existing laws
- There are available software in the Internet those can use for both infringing and non-infringing reasons and it is easy to identify transmission of sound recordings without scrutinizing or interrupting communications; however, ISPs should reject such an recognized account holder access to their networks by using technical protection measures, such as, anti-copy devices, access control, proprietary viewer software, and so on;
- At the same time, ISPs can slowdown brandwith time-to tome to protect illegal download or impose other severe punishment to the infringers to protect the rights of the copyright holders;
- In the era of globalisation, it is essential to have unified code for all countries;
Conclusion
From the above discussion, it can be argued that the legislature of the UK and India are highly interested to address the issues related with online infringement of copyright to save creative industries and help investors to get full returns on their investment by reducing unlawful downloading, introducing and implementing new legal provisions. the government of the UK passed many legislation complying EU regulation, such as, CDPA 1988, TA 1994, DPA 1998, DEA 2010 and so on; however, DEA 2010 imposed liability on the ISPs to notify, list and remove access of the infringers in order to reduce copyright infringement by 70%; in addition, larger ISPs are mainly bound to bear legal obligation. At the same time, Indian Government enacted several acts considering demand of the copyright holders, ISPs, and users, for instance, CRA 1957, TA 1999, IT Act 2000, and IT (Amendment) Act 2008; however, most of the provisions of these laws imposed over burden on the ISPs in terms of monitoring, which became controversial in some extent. Due to the strictness of the Indian law regarding the ISPs, users and service providers face increasing troubles of privacy and freedom of expression; experts have suggested that the country could lose its IT industry if it does not amend the rules because there are certain South Asian neighbours with low labour costs that possess moderate intermediary laws. In order to sustain in the competitive market, therefore, it is highly recommended that the MPs should take steps to amend the rules as early as possible.
Appendices
Appendix 1 – Figures
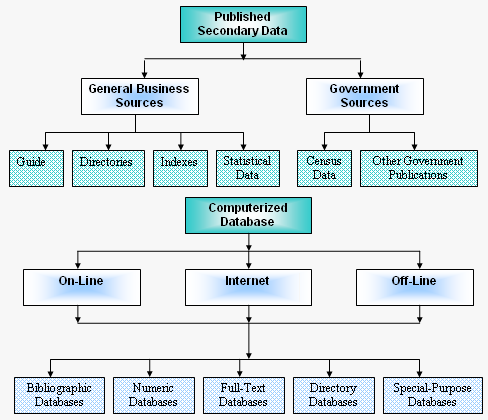
Appendix 2 – Abbreviations
Anti-Counterfeiting Trade Agreement = ACTA
Communications Act 2003 = CA 2003
Copyright, Designs and Patents Act 1988 = CDPA 1988
Council of Europe = CoE
Decentralized peer-to-peer = DP2P
Digital Economy Act 2010 = DEA 2010
Digital Millennium Copyright Act, 1998 = DMCA
Electronic Commerce Regulation = ECR
European Union = EU
Intellectual Property Rights = IPR
Internet Protocol = IP
Internet Service Providers = ISPs
Online Service Providers = OSPs
Organization for Economic Cooperation and Development = OECD
Peer-to-peer = P2P
Trade-Related Aspects of Intellectual Property Rights = TRIPS
Transmission Control Protocol = TCP
User Generated Content = UGC
United Nations = UN
WIPO Copyright Treaty = WCT
WIPO Performances and Phonograms Treaty = WPPT
World Trade Organization = WTO
References
Altacit Global, The salient features of the Indian Trademarks Act 1999, 2003. Web.
Bailli, England and Wales High Court (Chancery Division) Decisions, 2010. Web.
BIS, Impact Assessment for the Digital Economy Act 2010, 2010. Web.
Crown Copyright, Digital Economy Act 2010. Web.
Cunha, MV, L Marin & G Sartor, ‘Peer-to-peer privacy violations and ISP liability: data protection in the user-generated web’, International Data Privacy Law, 2012, Vol. 2, No. 2. Web.
Dalton, P, Intellectual Property and the Internet, 2012. Web.
Dara, R, Intermediary Liability in India: Chilling Effects on Free Expression on the Internet, 2011. Web.
Datta, A, ISP Liability In India: Fact Or Fiction, 2007. Web.
Diane, R & M Elizabeth, Information Technology Law, 3rd edn, Cavendish Publishing, London, 2005.
Dinwoodie, GB. ‘The WIPO Copyright Treaty: A Transition to the Future of International Copyright Lawmaking?’ Case Western Reserve Law Review, Vol. 57, No. 4, 2007. Web.
DNA, Amendments to Copyright Act introduced: Authors to get royalty, 2010. Web.
Farano, B, Are ISPs liable for IP wrongs? 2012. Web.
Fiscor, M, The Law of Copyright and the Internet, Oxford University Press, Oxford 2002.
Gardner, C, BT/TalkTalk: Always an Unappealing Appeal, 2012. Web.
Gibson, O, Warning to chatroom users after libel award for man labelled a Nazi, 2006. Web.
GIPC, The Anti-Counterfeiting Trade Agreement (ACTA), 2012. Web.
Gupta, A, The Scope of Online Service Providers’ Liability for Copyright Infringing Third Party Content under the Indian Laws – The Road Ahead, 2009. Web.
Helplinelaw, Judicial response to offence of cyber defamation, 2013. Web.
Hopkins, SL, ‘Cyber Crime Convention: A Positive Beginning to a Long Road Ahead’, Journal of High Technology Law, Vol. 2, No. 1, 2013, pp. 1-22. Web.
Idris, K, Intellectual Property: A Power Tool for Economic Growth WIPO, 2001. Web.
Jaitly, R, Intermediary liability and the future of the Internet in India, 2007. Web.
JISC Legal, ISP Liability – Overview, 2007. Web.
Kalisch, D, Sponsored Links and Trademark Infringement: Primary Liability of the ISP under the EU Trademark Directive, Sweet & Maxwell, London, 2011.
Katoch, PS, Liability of Intermediaries under the IT Amendment Act 2008, 2010. Web.
Kohn, LT, Methods in Case Study Analysis, 1997. Web.
Kothari, CR, Research Methodology: Methods and Techniques, Wishwa Prakashan, New Delhi, 1990.
Lichtman, D, Holding Internet Service Providers Accountable, 2005. Web.
Lloyd, IJ, Information technology law, Butterworths, London, 2000.
Mansell, R & WE Steinmueller, Copyright infringement online: the case of the Digital Economy Act judicial review in the United Kingdom, 2011. Web.
Matthew, RJ, ‘Internet File-Sharing and the Liability of Intermediaries for Copyright Infringement: A Need for International Consensus’, The Journal of Information, Law and Technology (JILT), vol. 1, 2003, pp. 1–30. Web.
McLaughlin, K, The Digital Economy Act 2010 – Implications for UK Colleges and Universities, 2010. Web.
McLeod, S, Case Study Method in Psychology, 2008. Web.
Miller, LR, Fundamentals of Business Law: Summarized Cases, Sweet & Maxwell, London, 2012.
Mishra, P & A Dutta, ‘Striking a Balance between Liability of Internet Service Providers and Protection of Copyright over the Internet: A Need of the Hour’, Journal of Intellectual Property Rights, Vol. 14, 2009, pp. 321-329. Web.
Mohanty, A, Indian Intermediary Liability Law Requires a Thorough Makeover, 2012. Web.
Nagpal, R, Liability of Network Service Providers, 2012. Web.
Palmer, R, BT v Secretary of State for Business, Innovation and Skills [2011] EWHC 1021 (Admin), 2011. Web.
Polanski, PP, ‘International electronic contracting in the newest UN Convention’, Journal of International Commercial Law and Technology Vol. 2, Issue 3, 2007. Web.
Popoola, OO, Statutory Limitation of Liability of Internet Service Providers in Decentralized Peer to Peer File Sharing, 2012. Web.
PRS, Rules & Regulations Review, 2011. Web.
Rea, A, Tamiz v Google, 2012. Web.
Reed, C, Internet Law: Text and Materials, 2nd edn, Cambridge University Press, Cambridge, 2004.
Rizk, D, New Indian Internet Intermediary Regulations Pose Serious Threats to Net Users’ Freedom of Expression, 2011. Web.
Rowland, D, & E, MacDonald, Information Technology Law, Routledge, London, 2000
Saikia, N, T-Series v. MySpace: First Reactions, 2011. Web.
Smith, GH, Internet Law and Regulation, Sweet & Maxwell, London, 2007.
Song, SH, A Comparative Copyright Analysis of ISP Liability in China Versus the United States and Europe, 2010. Web.
Sterling, JAL, World Copyright Law, 2nd edn, Sweet & Maxwell, London, 2003)
Tellis, W, ‘Application of a Case Study Methodology’, The Qualitative Report, vol. 3, no. 3, 1997. Web.
Tjalsma, H, & J Rombouts, Selection of Research Data, 2010. Web.
Tong, CM, Copyrighted works being infringed on the Internet, 2006. Web.
UNCTAD, Information Economy Report 2007-2008: United Nations Conference on Trade and Development, New York, and Geneva, 2007. Web.
Vibhute, K & F Aynalem, Legal Research Methods, 2009. Web.
Vij, S, How India made it easy for everyone to play internet censor: A primer from SFLC.in, 2012. Web.
Williams, AP, D Calow, & N Higham, Digital Media: Contracts, Rights and Licensing, Sweet & Maxwell, London, 1998.
WIPO, Berne Convention for the Protection of Literary and Artistic Works. n.d. Web.
WordPress, Information Technology (Amended) Act 2008, 2008. Web.
Workman, S, Internet Law – Developments in ISP Liability in Europe, 2013. Web.
Yen, AC, Internet Service Provider Liability for Subscriber Copyright Infringement, Enterprise Liability, and the First Amendment. n.d. Web.
Yin, RK, Case Study Research: Design and Methods, 3rd edn, Sage Publication, London, 2003.
Summary
As the Internet services have spread its tentacles all over the world with both advantages (development of communication system and knowledge) and disadvantages (increased threat of IPR violation), the purpose of this dissertation is to research on the liability of Internet Service Providers by comparing between the UK and India. In context of UK and India, this paper has engaged to identify a uniform approach to impose burden on the ISPs in regards to data protection, privacy and copyrights violation on various grounds for legislative materials while the content and personal data directly published by the user may generate conflict on the ‘freedom of expression’ for privacy and data protection. The Treaties, Acts and Legislation discussed over the paper identified that the ISPs may emerge to be co-responsible for violation of privacy and benefit them by facilitating the information accessible and searchable without any difficulties where the ISPs encourage illicit circulation of its business an enabler to the unauthorised access to the server that generated increasing civil and political debates. The provisions of the legislations have honestly engaged to impose liability on ISPs, but amalgamated the concepts of ISPs and hosting providers at the hosting server for user generated contents, ISPs have limited responsibility; thus, the future data protection Acts should clearly clarify that who controls the user-generated contents so that the imposed liability would be exempted or relaxed. However, this dissertation will concentrate on the UK Digital Economy Act 2010, Copyright, Designs and Patents Act 1988 (UK), and Trade Marks Act 1994 (UK); in addition, it will explain the provisions of Indian law, such as, Information Technology Act 2000, Information Technology Amendment Act 2008, Trade Marks Act 1994, and Copyright Amendment Act 2010, etc.
Footnotes
- RJ Matthew, ‘Internet File-Sharing and the Liability of Intermediaries for Copyright Infringement: A Need for International Consensus’, The Journal of Information, Law and Technology (JILT), vol. 1, 2003, pp. 1–30.
- OO Popoola, Statutory Limitation of Liability of Internet Service Providers in Decentralized Peer to Peer File Sharing, 2012. Web.
- SH Song, A Comparative Copyright Analysis of ISP Liability in China Versus the United States and Europe, 2010. Web.
- D Lichtman, Holding Internet Service Providers Accountable, 2005. Web.
- Cunha, MVdA. Marin, L. and Sartor, G. Peer-to-peer privacy violations and ISP liability: data protection in the user-generated web, International Data Privacy Law, 2012, Vol. 2, No. 2. Web.
- AC Yen, Internet Service Provider Liability for Subscriber Copyright Infringement, Enterprise Liability, and the First Amendment. Web.
- CM Tong, Copyrighted works being infringed on the Internet, 2006. Web.
- Bailli, England and Wales High Court (Chancery Division) Decisions, 2010. Web.
- CR Kothari, Research Methodology: Methods and Techniques, Wishwa Prakashan, New Delhi, 1990.
- LT Kohn, Methods in Case Study Analysis, 1997. Web.
- S McLeod, Case Study Method in Psychology, 2008. Web.
- RK Yin, Case Study Research: Design and Methods, 3rd edn, Sage Publication, London, 2003.
- W Tellis, ‘Application of a Case Study Methodology’, The Qualitative Report, vol. 3, no. 3, 1997. Web.
- Kohn, p.4.
- H Tjalsma & J Rombouts, Selection of Research Data, 2010. Web.
- Tjalsma & Rombouts, p.13
- Vibhute, K, & F, Aynalem, Legal Research Methods, 2009. Web.
- Kothari, CR, Research Methodology: Methods and Techniques, Wishwa Prakashan, New Delhi, 1990.
- B Farano, Are ISPs liable for IP wrongs? 2012. Web.
- M Fiscor, The Law of Copyright and the Internet, Oxford University Press, Oxford 2002.
- Kalisch, D, Sponsored Links and Trademark Infringement: Primary Liability of the ISP under the EU Trademark Directive, Sweet & Maxwell, London, 2011.
- IJ Lloyd, Information technology law, Butterworths, London, 2000.
- PP Polanski, ‘International electronic contracting in the newest UN Convention’, Journal of International Commercial Law and Technology Vol. 2, Issue 3, 2007. Web.
- UNCTAD, ‘Information Economy Report 2007-2008’, United Nations Conference on Trade and Development, New York, and Geneva, 2007, pp. 1–386. Web.
- ibid
- PP. Polanski, p. 2
- JAL Sterling, World Copyright Law, 2nd edn, Sweet & Maxwell, London, 2003.
- WIPO, Berne Convention for the Protection of Literary and Artistic Works. Web.
- AP Williams, D Calow & N Higham, Digital Media: Contracts, Rights and Licensing, Sweet & Maxwell, London, 1998.
- Popoola, p. 45
- Dinwoodie, GB. The WIPO Copyright Treaty: A Transition to the Future of International Copyright Lawmaking? Case Western Reserve Law Review, Vol. 57, No. 4, 2007, pp. 1-67
- K Idris, Intellectual Property: A Power Tool for Economic Growth WIPO, 2001. Web.
- WIPO, The Advantages of Adherence to the WIPO Copyright Treaty (WCT) And the WIPO Performances and Phonograms TREATY (WPPT). Web.
- C Reed, Internet Law: Text and Materials, 2nd edn, Cambridge University Press, Cambridge, 2004.
- Hopkins, SL, ‘Cyber Crime Convention: A Positive Beginning to a Long Road Ahead’, Journal of High Technology Law, Vol. 2, No. 1, 2013, pp. 1-22. Web.
- Hopkins, p.20.
- MV Cunha, L Marin & G Sartor, ‘Peer-to-peer privacy violations and ISP liability: data protection in the user-generated web’, International Data Privacy Law, 2012, Vol. 2, No. 2. Web.
- Mishra and Dutta, p.3
- GIPC, The Anti-Counterfeiting Trade Agreement (ACTA), 2012. Web.
- Popoola, p. 154
- section 124A(6)(g)
- Electronic Commerce (EC Directive) Regulations 2002;
- ibid
- Productores de Música de España (Promusicae) v Telefónica de España SAU (Telefónica) (C-275/06)
- Data Protection Directive 95/46
- The confidentiality of communications transmitted via public communications networks and publicly available electronic communication services and should prohibit the storage of such data by anyone other than the user unless consent is obtained
- Section 124A(8)(c)
- Electronic Commerce Regulation
- Regulation 22 of ECR 2002
- Smith, GH, Internet Law and Regulation, Sweet & Maxwell, London, 2007.
- D Rowland & E MacDonald, Information Technology Law, Routledge, London, 2000
- D Rizk, New Indian Internet Intermediary Regulations Pose Serious Threats to Net Users’ Freedom of Expression, 2011. Web.
- Anti-Counterfeiting Trade Agreement
- Agreement on Trade-Related Aspects of Intellectual Property Rights
- P Mishra, & A Dutta, ‘Striking a Balance between Liability of Internet Service Providers and Protection of Copyright over the Internet: A Need of the Hour’, Journal of Intellectual Property Rights, vol. 14, 2009, pp. 321-329. Web.
- Smith, p.165
- Religious technology Service Centre h Netcom
- A Mohanty, Indian Intermediary Liability Law Requires a Thorough Makeover, 2012. Web.
- S Vij, How India made it easy for everyone to play internet censor: A primer from SFLC.in, 2012. Web.
- S Workman, Internet Law – Developments in ISP Liability in Europe, 2013. Web.
- Mishra & Dutta, p.2
- R Dara, Intermediary Liability in India: Chilling Effects on Free Expression on the Internet, 2011. Web.
- Dara, p.3
- WordPress, Information Technology (Amended) Act 2008, 2008. Web.
- ibid
- WordPress, p.3
- PS, Katoch, Liability of Intermediaries under the IT Amendment Act 2008, 2010. Web.
- A Gupta, The Scope of Online Service Providers’ Liability for Copyright Infringing Third Party Content under the Indian Laws – The Road Ahead, 2009. Web.
- Katoch, p.3
- D, Rizk, New Indian Internet Intermediary Regulations Pose Serious Threats to Net Users’ Freedom of Expression, 2011. Web.
- R Jaitly, Intermediary liability and the future of the Internet in India, 2007. Web.
- PRS, Rules & Regulations Review, 2011. Web.
- Nagpal, R, Liability of Network Service Providers, 2012. Web.
- N Saikia, T-Series v. MySpace: First Reactions, 2011. Web.
- Saikia, p.1
- Saikia, p.1
- JK Rowling and Anr vs. Mr. Vinay Varma and Ors; CS (OS) No. 1242 of 2004
- A Datta, ISP Liability in India: Fact or Fiction, 2007. Web.
- SMC Pneumatics (India) Pvt. Ltd. v. Jogesh Kwatra; No. 1279/2001 Delhi HC
- Helplinelaw, Judicial response to offence of cyber defamation, 2013. Web.
- Helplinelaw, p.1
- Altacit Global, The salient features of the Indian Trademarks Act 1999, 2003. Web.
- DNA, Amendments to Copyright Act introduced: Authors to get royalty, 2010. Web.
- Smith, p.140.
- R Diane & M Elizabeth, Information Technology Law, 3rd edn, Cavendish Publishing, London, 2005.
- Euromarket Designs Inc v Peters
- Twentieth Century Fox Film Corp v Newzbin Ltd [2010] EWHC 608 (Ch), [2010] FSR 21
- Bailli, England and Wales High Court (Chancery Division) Decisions, 2010. Web.
- Dalton, P, Intellectual Property and the Internet, 2012. Web.
- Copyright, Designs and Patents Act 1988
- BIS, Impact Assessment for the Digital Economy Act 2010, 2010. Web.
- BT, TalkTalk, Virgin Media, Sky, Orange, O2 and Post Office
- K McLaughlin, The Digital Economy Act 2010 – Implications for UK Colleges and Universities, 2010. Web.
- Crown Copyright, Digital Economy Act 2010. Web.
- the Communications Act 2003
- Crown Copyright
- British Telecommunications Plc & Anor, R v The Secretary of State for Business, innovation and Skills
- LR Miller, Fundamentals of Business Law: Summarized Cases, Sweet & Maxwell, London, 2012.
- Privacy and Electronic Communications Directive
- R Palmer, BT v Secretary of State for Business, Innovation and Skills [2011] EWHC 1021 (Admin), 2011. Web.
- R Mansell & WE Steinmueller, Copyright infringement online: the case of the Digital Economy Act judicial review in the United Kingdom, 2011. Web.
- C Gardner, BT/TalkTalk: Always an Unappealing Appeal, 2012. Web.
- Gardner, p.1
- JISC Legal, ISP Liability – Overview, 2007. Web.
- Laurence Godfrey v Demon Internet Limited [(1999) QBD, [1999] 4 All ER 342]
- JISC Legal, p.2
- [2006] EWHC 407
- [2006] All ER (D) 297
- O Gibson, Warning to chatroom users after libel award for man labelled a Nazi, 2006. Web.
- Payam Tamiz v Google Inc and another [2012] EWHC 449
- Rea, A, Tamiz v Google, 2012. Web.
- BIS, p.43
- McLaughlin, p.6