Abstract
This experiment aimed to conduct an assessment on firewall security, based on the experiments conducted on a firewall utility of Kaspersky Internet Security. This entailed undertaking a series of tests on the firewall utility to ascertain the security capabilities of a firewall on a network. The experimental environment was conducted in the laboratory using the VMware Workstation, which offers the safest way to test a security application program without posing any potential threats to the entire network. The VMware workstation serves as virtual software for computer systems from VMware that facilitates the setting up of virtual computers with the hosting system software. It was established that the firewall restricted network activities such as remote access and applications that relied on network functionalities such as web browsers if the application rules were well set. This implies that the Firewall is an important security tool that can be used to enhance system security through the restriction of threats that can be initiated on applications that rely on network resources. However, there are potential security enhancements provided by the use of firewalls in computers and computer networks. Firewalls also enhanced privacy, making it difficult to collect data and information concerning the network. However, firewalls cannot eliminate attacks that are initiated within a protected network, attacks associated with malicious access and attacks that initiated through the open ports that are under the packet and application rules. In addition, firewalls do not help prevent attacks that bypass the firewall. It was established firewall is vulnerable to attacks initiated through trace routing via an open port, mapping the network behind the firewall and the loopholes associated with firewalls of allowing data packets to port 80. Therefore, port scanning can be helpful in the assessment of ports that are open during firewall implementation.
Introduction
The practical aspect of this report focuses on the assessment of firewall security concerning the identified research aims. This will primarily entail running a series of tests to ascertain firewall security and offer viable solutions that can be deployed to enhance firewall security (Abhishek & Cantrell, 2006). The purpose of the practice tests is to develop a test environment where one can assess the security of the firewall and to be able to identify whether it is configured properly and if it serves what it is intended to do i.e. close ports. To provide a viable solution based on the weakness identified. The significant limitation of firewall security is that it does not offer protection from attacks that are bypass the firewall (Bagad, 2009). This means that for firewalls to be effective, they have to be implemented in all the aspects of the organization’s network and security architecture. Another potential loophole identified in the report is that a firewall does not offer any form of protection to internal threats, which refers to threats that are from within the network (Bansal, 2004). Even though an industrial spy can be used in the exportation of data through the firewall, they do not offer protection against attacks associated with social engineering (RAD University, 2011). A common misconception that organizations and computer users embark on is that firewalls are helpful in the identification and blocking of attacks. The functionality of firewalls serves to shut everything down, after which it only allows the allowed items.
In an ideal scenario, computer systems would be secure and be in lockdown mode, implying that there would be no need to deploy firewalls as a parameter for enhancing computers and network security (Earle, 2005). The underlying reason behind the reliance on a firewall for security is that vulnerabilities are accidental. Therefore, during the installation of a firewall, whether hardware or software, the initial step is that it serves to stop all forms of communication, after which the rules are added to allow specified traffic to pass via the installed firewall (Bates, 2007). For instance, a usual firewall deployed by a corporate organization used for accessing the internet will function by stopping all the traffic associated with UDP and ICMP datagram, it will also stop all incoming communications that use TCP but allow outgoing TCP communications. This helps stop all forms of incoming internet connections such as hackers, while at the same time allowing users within the network to have access to the internet through the outgoing connection. This implies that a firewall simply serves as a perimeter fence for a computer network having specified gates (Bates, 2007).
As a result, it has limited functionality for identifying break-in attacks that are involved with bypassing the fence. In addition, the firewall is not intelligent enough to know whether the person that is using the gate has the required permissions. To meet the purpose of this experiment, an assessment will be conducted through the installation of self-managed firewall application software that can configure itself. Additionally, it is important to make use of the optimal security policy that is available to evaluate whether the configurations options that have been provided meet the business requirements. This will help in the recognition of the potential loopholes during the experiment. The assessment of Firewall security of this report will be based on Firewall utility found on Kaspersky Internet Security. The basic observation from this is that firewalls offer restrictions to designated points (Gollman, 2011). The findings from this report are that firewalls do not serve as a dynamic defensive security system, and therefore should be implemented together with other security measures such as the Intrusion Detection Systems that are more proactive to enhance computer network security for the organization (Ferhat & Rachida 2005).
The experiments
Numerous firewall applications can be used in experimenting with the assessment of firewall security. The choice of the firewall application will be determined by the configuration properties, firewall management policies and the cost of the application. Each of the alternatives has significant benefits and constraints associated with this research project. For instance, the cost factor for off-the-shelve applications for firewall hardware devices (Hunt, 2002). This research project focuses mainly on the assessment of firewall application software because the firewall hardware devices are beyond the scope of this project due to financial constraints. In addition, they offer a limited number of configuration options for the firewall hardware products to assess firewall security. However, firewall hardware devices are easy to implement because they are just placed in between the computer and the network to enhance computer security (Hunt, 2002).
Another possible alternative that can be deployed in this project is the use of stand-alone firewall hardware devices, which are dedicated computer systems that serve as firewalls. These systems have the capability of offering protection to an entire network. They are most appropriate because the application software offers various configuration options. Another potential benefit of standalone firewall devices is that a user in operating systems such as Linux can download and make use of open source applications for free. The only constraint associated with these systems is that users must have more knowledge concerning the configuration scripts deployed in the configuration of the firewall (Jackson, 2010).
The last viable alternative for this research project, which is considered appropriate for this research, is the installation of self-managed firewall application software that can configure itself (Ferhat & Rachida, 2005). Additionally, it is important to make use of the optimal security policy that is available to evaluate whether the configurations options that have been provided meet the business requirements. This will help in the recognition of the potential loopholes during the experiment. The assessment of Firewall security of this report will be based on Firewall utility found on Kaspersky Internet Security (Ferhat & Rachida, 2005).
Overview of Kaspersky Internet Security
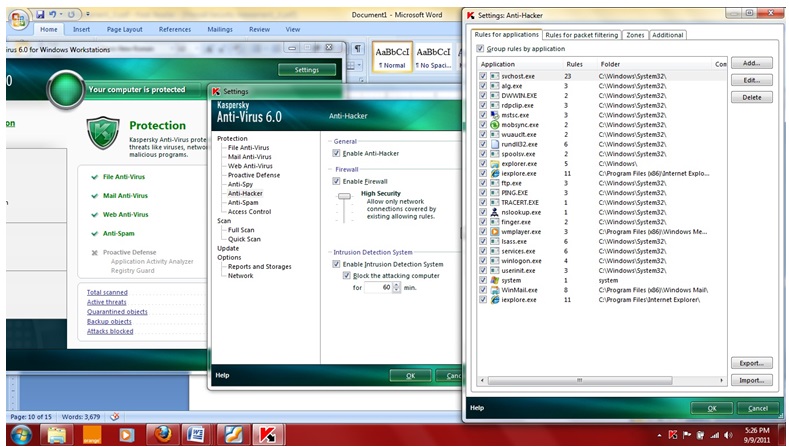
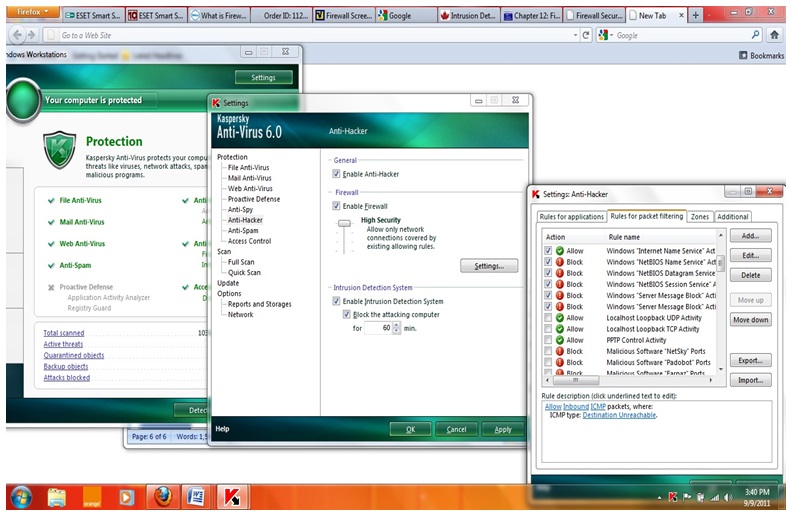
Kaspersky Internet security suite offers diverse product features that are aimed at enhancing computer security. Some of the features include real time protection from web-based attacks. This helps improve security within the home network, public and wireless networks (Randall, 2002). The primary concern of this report focuses on the assessment of the firewall utility of the Kaspersky Internet Security, which will be used for the evaluation of firewall security. The firewall profiles make use of the automatic learning mode because the creation of the firewall rules is self-managed depending on the network usage (Larry & Bruce, 2007). The firewall utility has a base configuration that plays a significant role in learning the approaches that the user deploys to configure the firewall. In addition, there is an added option that helps users to configure their firewall regarding the programs that use network resources such as the internet, shared files and network printers. The configuration of the firewall rules is simple, which is found within the advanced setup tree section (Larry & Bruce, 2007). A basic interface of the Kaspersky Internet security and the personal firewall option is found in figure 1 below.
General layout
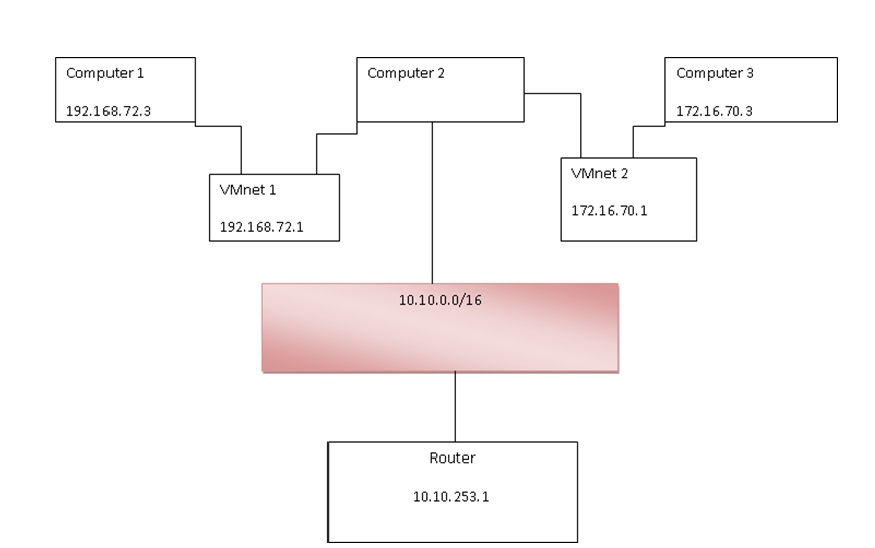
This part describes the test environment that the practical experiment will be done. The layout of the test environment is described, the principles underlying the operation of virtual machines is introduced, its configuration and the functionality of virtual networks. The general experimental layout is shown in the following figure.
Experimental procedures
Computer 1 and computer 3 serve as the hosts for testing that denote the computer networks identified by 192.168.72.0/24 and 172.16.70.0/24 in that order. This is to say that all packets that have been forwarded to 192.168.72.0/24 are handled by computer 1while all packets that have a destination of 172.16.70.0/24 are handled by computer 3. Computer 2 serve as the firewall, which has two network interfaces connecting all the networks, and another adapter that serves as the access point marked by 10.10.0.0/16. VMnet 1 and VMnet 2 serves as network switches that link the interfaces of the hosts to the interface of the firewall (Pathan, 2010).
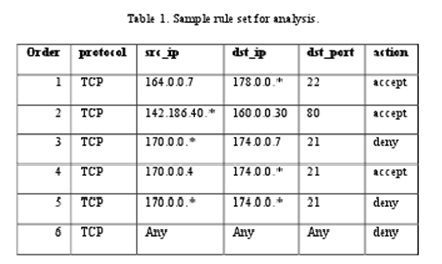
After enabling the firewall, it is important to define the set of rules that the firewall has to use to control the network traffic. The assessment of firewall security will then be done using the established firewall rules (Merritt, 2002). Experimental tests need the connection of a personal computer to a network and attempt to access the PC using features like remote access. Other experiments for evaluating firewall security require the use of shared documents that have no permission. The firewall rules form the basis of ascertaining whether firewalls are effective in enhancing computer and network security (Ferhat & Rachida 2005). It is also important that redundant rules be avoided to eliminate any potential problems during the experiment (Meghanathan, 2010).
The following are the policy statements taken into consideration during this experiment. The policy statements are categorized into low-risk environmental policies that are designated for the user and the manager (Tanenbaum, 2003).
Low-Risk Environment policies for the user
- All users that need internet connectivity must the approved internet gateways and applications for the organization
- A firewall has been installed between the private networks and the internet in order to protect the computer systems. Therefore, individuals in the organization should not bypass the firewall by the use of modems and other tunnelling application software to gain connectivity to the internet.
- Some of the protocols have been blocked while some have been redirected. In case of needs for a specific business requirement, employees are required to contact the network manager.
Low-Risk environmental policies for the manager
- A firewall should be implemented between the network of the organization and the internet with the main objective of preventing unauthorized access by untrusted networks. In addition, the selection and maintenance of the firewall is to be conducted by the network administrator
- Connecting to the internet by use of other forms such as dial-up connections and dial-out models from internet sites that are linked to the WAN of the organization is not allowed.
- Users that need internet connectivity must rely on the approved gateways and application software.
Evaluation of firewall security
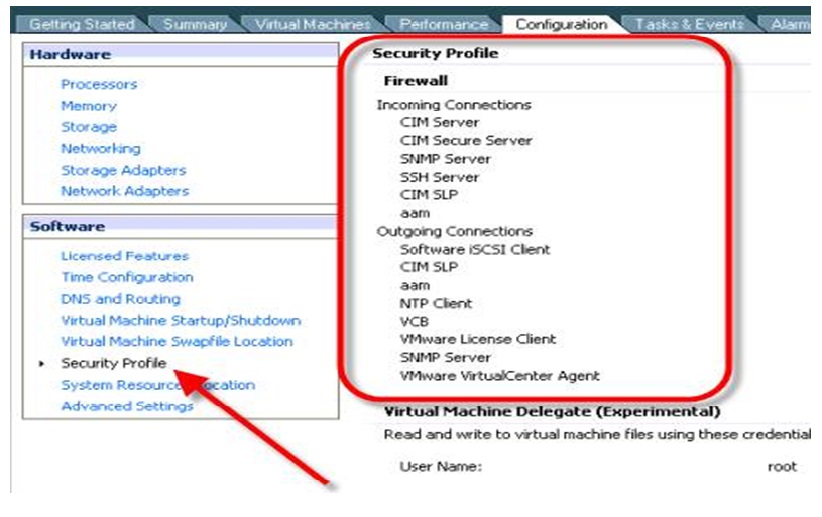
VMware
The practical experiment was conducted in the laboratory using the VMware Workstation, which is the safest way to test a security application program without posing any potential threats to the entire network. The VMware workstation serves as virtual software for computer systems from VMware that facilitates the setting up of virtual computers with the hosting system software (Scarfone, 2010). Each of the instances of the virtual machines can execute its guest system software such as Windows, Linux and variants of the BSD. Simply stated, the VMware workstation facilitates the multiple running of various operating systems simultaneously in one physical machine. In addition, the VMware workstation facilitates the bridging of the existing network adapters in the hosts, hard disks, USB devices and facilitates the simulation of other hardware (Abhishek & Cantrell, 2006). The VMware workstation also facilitates the process of testing live compact discs without the need of having to record them in the physical discs or setting the PC to reboot. Snapshots of the various operating systems that are running under the VMware workstation application can be taken, making it an essential tool for the secure running of the assessment tests without jeopardizing the functionality of the entire network (Bagad, 2009). The following Figure 2 represents a simulation of a PC in the Linux operating system under windows in the VMware workstation application software.
The experiment will assess the security of firewalls using emulated nodes to represent firewalls on the Virtual Machines that are running on various types of operating systems and applications (Bagad, 2009). In the experiment, the emulated were used together with application software that relies on network resources or network functionalities such as remote desktop access. In most scenarios, making use of a standalone experimental network using actual devices to assess the security of firewalls is constrained by factors such as cost. Therefore, the capability for the network to be represented using modelling and simulation is the best approach towards assessing the security levels of firewalls (Abhishek & Cantrell, 2006). A major requirement in the analysis of firewall security is the availability of the models of the network devices.
This requirement will be met using the OPNET Modeler network, which facilitates the understanding of how the various network algorithms perform under the diverse amounts of traffic loads and the configuration of the devices. This implies that network security analysts can make use of the algorithms on the network of the devices that have been simulated to trace the data packets and messages and collect statistics that can help analyze the security of firewalls. An added advantage of the network modelling and simulating tools such as OPNET Modeler is that they can be interfaced with actual devices and traffic. It is important to take into account the limitations associated with using network modelling and simulation tools (Ferhat & Rachida, 2005). Notable limitations include their inability to model the operating system and the vulnerabilities of the application; this makes it difficult to gather precise data that can be used in assessing the security capabilities of firewalls. This is since modelling and simulation tools do not represent the vulnerability of the actual device under certain operating system conditions.
To have a representation of the authentic network services, Virtual Machines functioned as the substitute systems that replaced the hosts and servers in the network. In the experiment to assess the security of a firewall, physical hardware solutions like emails, proxies and Domain Name Servers (DNS) were used. Using Virtual Machines presented numerous advantages when analyzing the security of firewalls. For instance, it offers an opportunity through which a significant portion of the analysis experiment can be virtualized, which implies that diverse services and network components can be integrated into one computing source (Meghanathan, 2010). This is a cost effective option when compared to using real hardware components. Such an experimental methodology offers the ability to set up the actual data traffic for the numerous network systems without having to acquire the actual network hardware devices. Irrespective of this, there are potential trade-offs during the experiment in the sense that the actual behaviour of the network hardware component is not attained. The experiment was based on the assumption that the potential benefits are more when compared to the constraints, based on the fact that virtualization implies that the experiment can be conducted on a single powerful computer (Ferhat & Rachida, 2005).
This experiment included the identification and assessment of firewall security, which is normally placed as an interface the serves to separate trusted networks within an organization from the untrusted ones. The firewall is initially assumed to be an effective security tool that can be used in averting network attacks using filtering. The firewall comprises a firewall application with its specified set of rules that dictate the nature of network activity (Ferhat & Rachida, 2005). The basis of the experiment was based on an understanding of the firewall security policies and how they can be used to enhance network security policies. The firewall security policies were then implemented in the virtual devices and the real firewall applications in the virtual environment. Instances of real systems for this experiment were implemented on the Virtual Machines. The nodes of the various network devices were simulated under the OPNET network modeller (Bansal, 2004). Under the demonstration systems, the nodes of the network devices were represented using simulation that attempted to denote similar behaviours of real network devices and the firewall applications. Owing to the fact the experiment heavily relied on the implementation of Access Control Lists, the experiment set up the models of the actual devices and applications using a direct importation of the authentic configuration files and the application rules. Therefore, the demonstration system consisted of many configuration files and the firewall application (Abhishek & Cantrell, 2006).
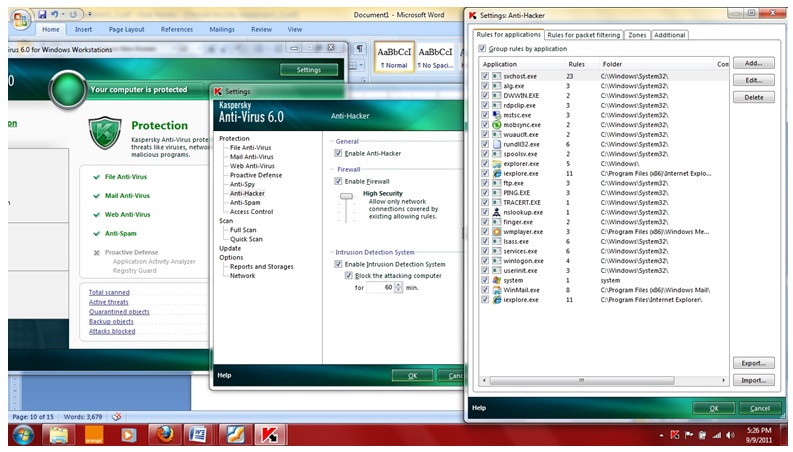
In order to assess the effectiveness of firewall security, the Firewall utility of the Kaspersky Anti-virus was turned on and set to the various security levels as shown in the following diagrams. The tests using remote access were conducted based on the existing rules. The high-security level allows network connections that are covered by the existing allowing rules (Vacca, 2010). The training mode allows the appearance of a training prompt if a network connection is being established. The chosen action is added to the list of the existing rules. Low-security blocks only network connections that are covered by the existing blocking rules, while the “allow all” profile all network activities. This experiment was focused on High-Security mode (Ferhat & Rachida, 2005).
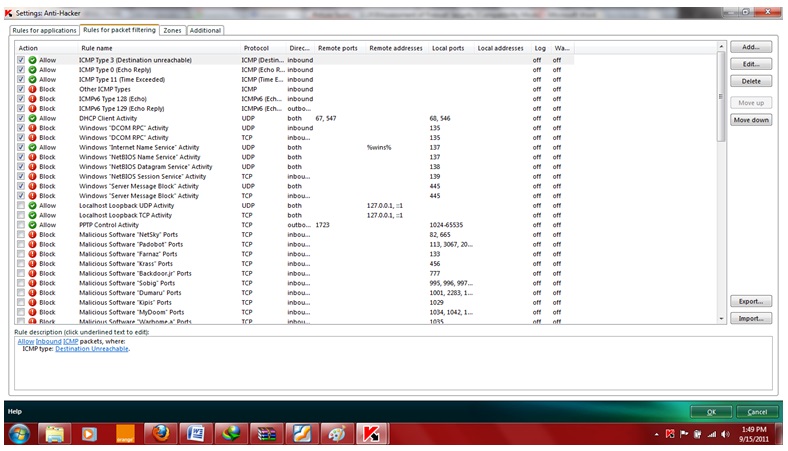
The firewall utility in Kaspersky aims at enhancing the level of security in local networks and attacks initiated using the internet. The rules adopted in the firewall utility apply to all network activities and connections that the computer has. A firewall rule can be defined as an action for blocking or allowing an attempt to establish a connection once the firewall detects such actions (Vacca, 2009). The firewall security in Kaspersky is implemented on two levels, mainly involving networks and applications that attempt to use the network resources. Security at the network level is implemented using rules that are based on global packet filtration. This mainly involves the blockage or allowing of network activity depending on the direction of the packet, the protocols deployed in data transfer and the port for the outbound packet. The security at the application level is implemented using the rules that determine the usage of network resources by the supplication software on the system (Ferhat & Rachida, 2005).
The rules at the application level depending on the analysis of the direction of the data packets, the protocols for transferring data and their respective ports. The use of application-level security helps in facilitating the process of configuration that is more specific concerning the applications that rely on the network resources such as browsers. There are two types of firewall rules, which depend on firewall protection levels. They include the packet rules, which are generally used in the creation of restrictions on activities on the network, irrespective of the application software on the computer system (Larry & Bruce, 2007). For instance, if a user sets up a packet rule that restricts inbound connections found on port 21, then not all the application software that uses port 21 such as the FTP server will be accessible by external users. The application rules are used for setting up restrictions of activities on the network for particular applications. For instance, if a user sets up a rule that blocks the connections for port 80 for all the applications, then an exception rule for that port can be created that allows only a specific application such as Firefox to use that port (Ferhat & Rachida, 2005). The following figure shows the application rules that were deployed during this experiment.
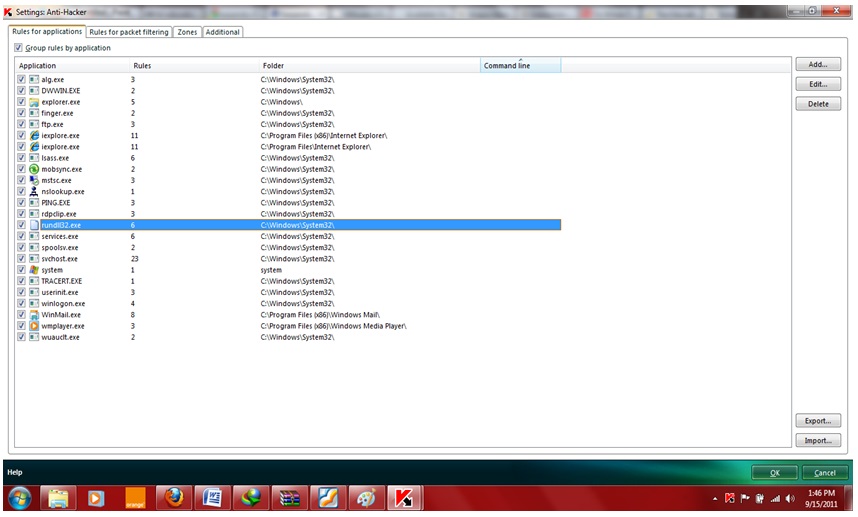
The rules for packet filtering are shown in the following diagram.
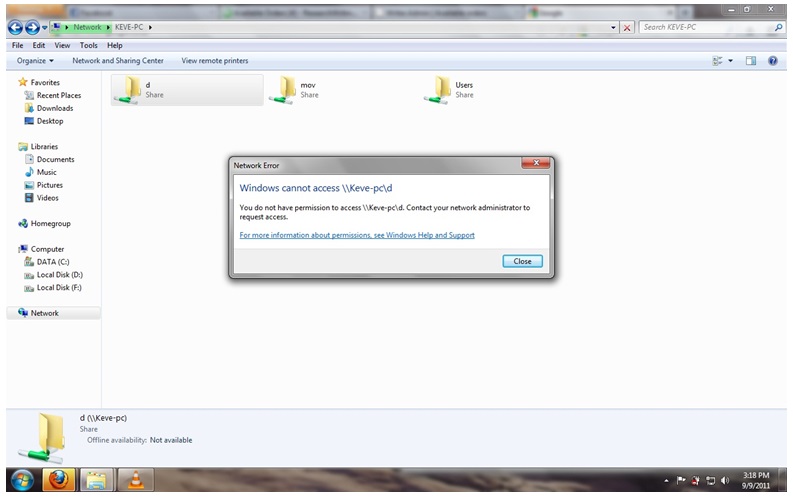
Remote access was deployed to access the network resources such as shared files that had no permissions with the firewall using the rules of high security (Pathan, 2010). The security assessment was also evaluated on programs that attempt to use the internet or establish a network connection that mainly involved data transfer between the various computers. Remote access is mainly deployed to access and control a personal computer remotely. It is a potential security loophole that attackers can rely on initiate their attacks. Remote access to the computer understudy was done using the local IP address of the computer and its corresponding computer name. In addition, the Remote Desktop Connection utility was also deployed in the experiments (Abhishek & Cantrell, 2006). In order to ensure reliability and validity of the information gathered, experiments were done repeatedly and made use of other methods such as Remote Desktop Web Connection. The Kaspersky Firewall utility was evaluated in terms of its efficiency in monitoring the network activity of the computer ranging from dial-up connections, remote access and control, network connection establishment and usage (Ferhat & Rachida, 2005).
Assessment of firewall security was also conducted using Network penetration testing tools. The main objective behind the implementation of network penetration tools is to evaluate the vulnerability of the computer network. Network penetration testing involved making attempts to break the rules laid down in the firewall policy. The results generated after completion of the procedure can be compared against expected results to provide insight into whether the firewall is operating within the required parameters (Ferhat & Rachida, 2005). If the firewall is capable of generating and monitoring the traffic for the network as required, it might be assumed that the firewall is operating properly. Problems concerning network security can be categorized into four basic areas: issues involving authentication, secrecy, and issues dealing with no repudiation and primarily controlling integrity (Ferhat & Rachida, 2005). The above network concepts are imperative in determining the effectiveness of a computer network in handling the various computer network threats. In its broadest sense, authentication involves determining who has access to a computer network and the associated network resources. Network penetration entails simulation of the potential attack by malicious software or attacker which may be based on either hardware or software oriented (Jackson, 2010).
The results of the experiments
With the firewall enabled, remote access to the computer was impossible, provided the application and its corresponding port was not allowed in the firewall rules. For example, restricting Mozilla Firefox on port 80 implied that the application could not be used to access the internet. This means that incoming communications by particular applications can be restricted under the firewall policy (Hunt, 2002). The remote access and control of the desktop returned a warning error as shown in the figure below. This is because the Windows Explorer HTTP activity, FTP activity and FTP data activity are not allowed under the firewall application rules. It is arguably evident that the Firewall is an important security tool that can be used in enhancing system security through the restriction of threats that can be initiated on applications that rely on network resources (Ferhat & Rachida, 2005).
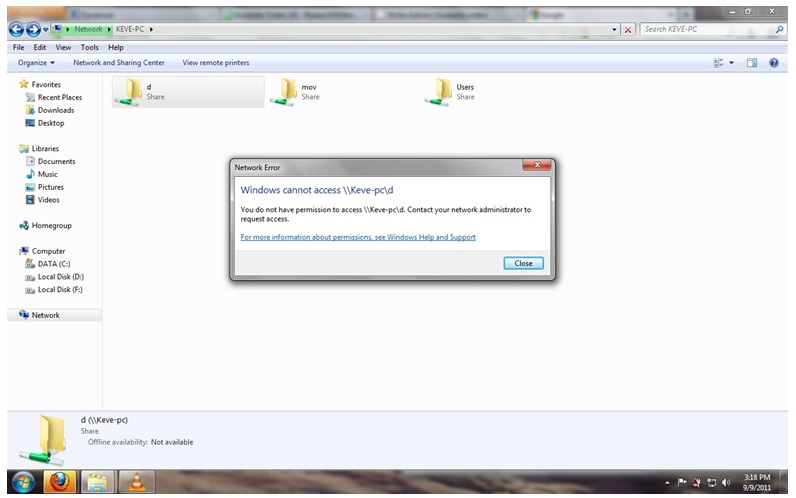
There are potential security enhancements provided by the use of firewalls in computers and computer networks (Tanenbaum, 2003). One of such benefits is that it reduces the risk by enhancing protection from the attacker’s attempt to make use of the potential security vulnerabilities (Ferhat & Rachida, 2005). Firewalls also enhanced privacy, making it difficult to collect data and information concerning the network. An added advantage is that firewalls enhance the security policy deployed by an organization. However, firewalls cannot eliminate attacks that are initiated within a protected network, attacks associated with malicious access and attacks that initiated through the open ports that are under the packet and application rules (Earle, 2005). In addition, firewalls do not help prevent attacks that bypass the firewall. Such attacks usually involve fire walking, which involves trace routing via an open port, mapping the network behind the firewall and the loopholes associated with firewalls of allowing data packets to port 80 (Vacca, 2009). Therefore, port scanning can be helpful in the assessment of ports that are open during firewall implementation (Larry & Bruce, 2007).
Conclusions and Recommendations
In this experiment, a capable firewall security assessment and the experimental environment was developed to facilitate the assessment of the effectiveness of firewalls in reinforcing network security. The experiments were based on an integration of simulations and emulations of real network hardware components that denoted the true capabilities of the firewall applications as much as possible. The virtualization aspect of the experiment facilitated accurate representations of the actual devices of the firewall applications and network hardware components while still ensuring scalability advantages and cost-effectiveness of the network simulation tools for the experiment. The outcome of the experimental setup was a large and low-cost representation of the network that facilitated the assessment of firewall security. In this experiment, firewalls were used based on an implementation of access control lists, the configuration files were used to set up an accurate representation of the network devices. The experiment also assessed the security issues relating to real time performance issues relating to the models of firewall applications. In addition, simulation facilitated higher traffic loads compared to actual devices. Further research should be conducted on actual devices on a large scale to increase the accuracy of the experiment by assessing their true behaviour.
References
Abhishek, S. & Cantrell, C., 2006. Firewall policies and VPN configurations. New York: Syngress.
Bagad, D., 2009. Computer Networks. New York: Technical Publications.
Bansal, K., 2004. A Text Book Of Information Technology. New York: APH Publishing.
Bates, D., 2007. Voice & data communications handbook. New York: McGraw-Hill Professional.
Dutcher, B., 2000. Managing IP addresses: how to number your network for growth and change. New York: Wiley.
Earle, A., 2005. Wireless security handbook. New York: Auerbach.
Ferhat, K. & Rachida, D., 2005. Testing of communicating systems: 17th IFIP TC6/WG 6.1 International Conference, TestCom 2005, Montreal, Canada, May 31-June 2, 2005: proceedings. New York: Springer.
Gollman, D., 2011. Computer Security. New York: John Wiley and Sons.
Hunt, C., 2002. TCP/IP network administration. New York: O’Reilly Media, Inc.
Jackson, C., 2010. Network Security Auditing. New York: Cisco Press.
Larry, P. & Bruce, D., 2007. Computer networks: a systems approach. New York: Morgan Kaufmann.
Meghanathan, N., 2010. Recent Trends in Network Security and Applications: Third International Conference, CNSA 2010, Chennai, India, July 23-25, New York: Springer.
Merritt, M., 2002. Wireless security. New York: McGraw-Hill Professional.
Pathan, A.-S., 2010. Security of Self-Organizing Networks: MANET, WSN, WMN, VANET. New York: Taylor and Francis.
RAD university, 2011. Tutorials for Telecommunications, Data Communications and Computer Networking. Web.
Randall, N., 2002. Wireless security: models, threats, and solutions. New York: McGraw-Hill Professional.
Scarfone, K., 2010. Guidelines on Firewalls and Firewall Policy: Revision 1. New York: DIANE Publishing.
Tanenbaum, A., 2003. Computer networks. Upper saddle River, NJ: Prentice Hall Professional.
Vacca, J., 2009. Computer and information security handbook. Upper Saddle River, NJ: Morgan Kaufmann.
Vacca, J., 2010. Managing Information Security. New York: Syngress.
Appendix A: Table of Figures
- Figure 2: general layout of experiment 9.
- Figure 3: VMware workstation 13.
- Figure 4: High-Security mode for Kaspersky firewall utility 14.
- Figure 5: firewall application rules deployed in experiment 16.
- Figure 6: rules for packet filtering 17.
- Figure 7: outcome of remote access 19.
Appendix B: screenshots